What Are Configuration Items? A Practical Guide for IT Teams
A configuration item (CI) is any IT component tracked in your CMDB to deliver and manage IT services. This complete…
How a CMDB reduces risk in IT change management
Every IT change carries risk. A patch that takes down a dependent service, a network update that cascades into an…
Halo Integrations Offer The Full Power Of Virima IT Discovery
Without an IT discovery and service mapping solution, keeping full visibility over your IT environment is tough. Incomplete asset data,…
Guide for choosing the right network asset discovery tool
Introduction As part of the IT team, how often are you asked what assets are present on your network? As…
How to Make the Best Out of Your IT Discovery Tool
IT discovery allows businesses to stay on top of their game by providing them with an overview of the current…
Top 11 asset lifecycle management best practices
Managing IT assets goes beyond buying and using them. Effective asset lifecycle management best practices help you get the most…
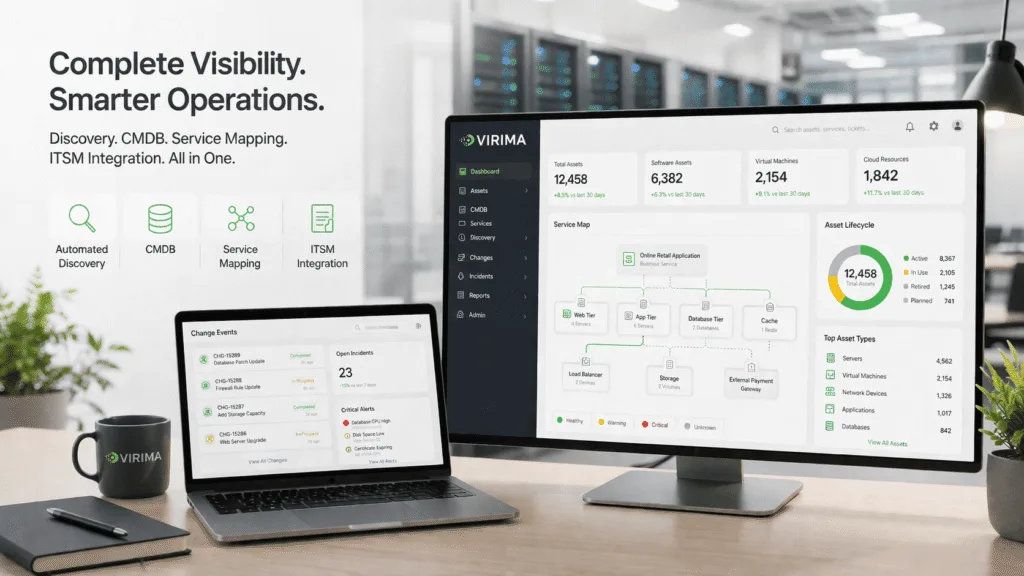
Virima 6.1: More Assets, Smarter CMDB, Faster Mapping
Switch stacks, modeled the right way Databases are no longer hidden dependencies Standalone ESXi hosts are finally visible Deeper cloud…
What is the best Active Directory monitoring tool for security?
Active Directory controls identity, authentication, and access. Therefore, when it changes unexpectedly, risk increases immediately. In today’s hybrid environments, that…
Virima vs. Native ServiceNow Discovery: What’s Different and When You Need Both
TLDR Introduction ServiceNow Discovery is one of the most widely deployed CMDB population tools in enterprise IT, forming a core part…
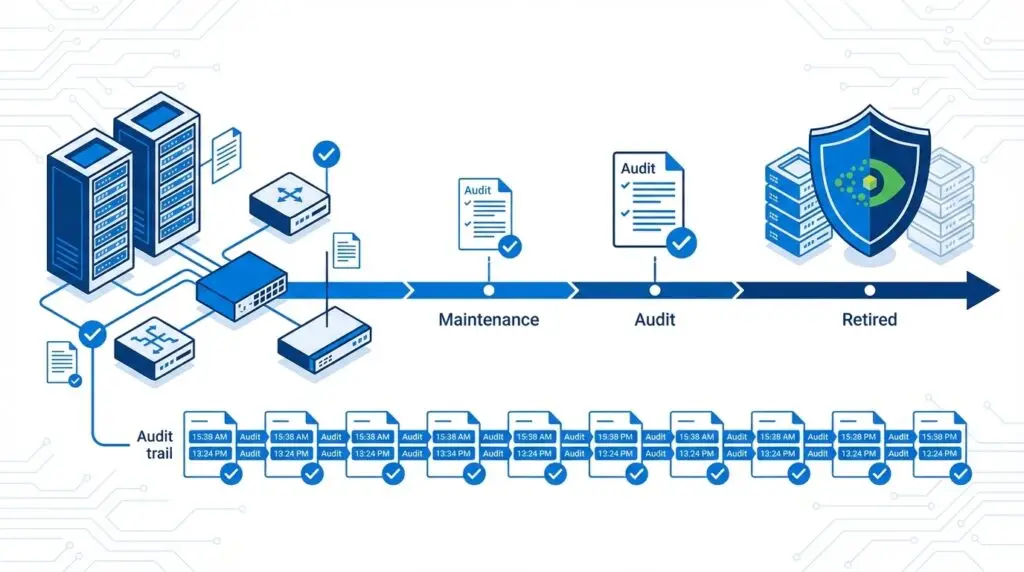
Virima’s comprehensive guide to IT asset lifecycle visibilityA comprehensive lifecycle management approachVirima’s comprehensive guide to IT asset lifecycle visibility
Navigating the intricate terrain of modern IT demands a clear view of assets at every stage of their journey. It’s…
Service Intelligence Starts With Your CMDB
Pink Elephant is a global provider of conference, consulting, and training focused on ITIL and CMDB. Jan-Willem Middelburg is the…
A comprehensive guide to managing CIs in ServiceNow CMDB
Are you tired of struggling to keep track of your organization’s IT assets? Do you find yourself constantly searching for…
ServiceNow CMDB Discovery: The Limitations, Real Costs, and Alternatives to Evaluate
If you work in IT as a leader or manager, like a CIO, CTO, IT Director, or Infrastructure Manager, this…
Best CMDB Software for ServiceNow Users in 2026A CMDB shouldn’t just tell you what existsBest CMDB Software for ServiceNow Users in 2026
A stale CMDB is one of the most common root causes of failed changes. This guide compares the best CMDB…
Virima’s guide to ITIL change management best practices
Navigating the complexities of IT landscapes can be daunting. Especially when it comes to implementing changes, it seems formidable. That’s…
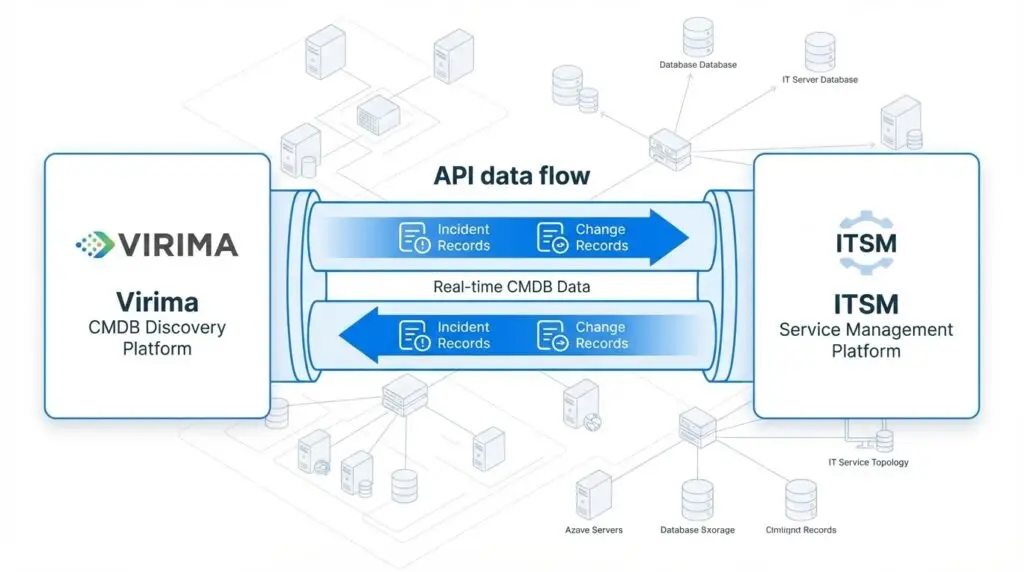
Virima + Xurrent Integration: Real-Time CMDB Data for Your ITSM Platform
Virima integrates with Xurrent to deliver automated CMDB discovery, ViVID service maps, and real-time CI context for faster incident resolution…
Faddom in 2026: Features, Pricing, Limitations & 5 Best Alternatives Compared
QUICK ANSWER What is Faddom? Faddom is an agentless application dependency mapping (ADM) tool that discovers servers, applications, and network…
Top 5 ITOM solutions to boost your business needs
Your IT setup is getting harder to manage. You have cloud systems, old servers, and new apps all running at…
ServiceNow Discovery vs Service Mapping: Key Differences (2026 Guide)
ServiceNow Discovery and ServiceNow Service Mapping are closely related — but they do very different things. One finds what exists…
Top 10 ITSM Change Management Best Practices
Technology moves fast. Keeping IT services stable during constant change sets strong teams apart from those stuck firefighting every Monday…
Understanding hybrid and multi-cloud network topologies
IT teams rarely run everything in one place. Instead, you spread workloads across on-prem systems and cloud platforms. As a…
How to streamline IT compliance audit with Virima
In this fast-evolving world, businesses encounter a multitude of challenges with IT compliance audits. Regulations are becoming stricter and more…
Understanding Risk Assessment vs Impact Analysis in IT Change Management
In the enterprise IT change management process, many people confuse risk assessment with impact assessment. This confusion is a common…
Application Dependency Mapping: How to Automatically Map IT Service Relationships in Your CMDB
Learn how automated application dependency mapping in Virima 6.1.1 uses Discovery scan data and ViVID Service Mapping to build always-accurate…
Top 10 IT inventory management software in 2026
Introduction Most automated IT operations, from incident resolution to AI-assisted change management start with one question: what exists in your…
AWS Lambda, App Runner, and Batch in CMDB: Why Serverless Assets Need Configuration Management Too
Learn why AWS Lambda, App Runner, and Batch workloads belong in your CMDB — and how Virima automatically discovers serverless…
Boost you ITSM strategy with application discovery and dependency mapping
With the expansion of technology assets—like the projected increase from 15.14 billion IoT devices in 2023 to 29.42 billion by…
What is ITOM and why it matters- Everything you need to know
Keeping a large IT setup running well can feel like a daily test. If you lead IT, you may worry…
ServiceNow CMDB Best Practices: Complete 2026 Guide
ServiceNow CMDB best practices is not just about loading data into ServiceNow. It creates a sustainable, well-governed system that IT…
Business service mapping in ServiceNow: Overview and alternatives
According to an InvGate survey, only 13% of ITSM professionals can pinpoint how their IT investments affect business outcomes. When…
Business Services Discovery and Mapping
DevOps Groups Get Incredible Insight Into the Web and Application Environment We’re announcing today the immediate availability of Services Topology…
Does Virima Include IP Address Management (IPAM)? How IPAM and CMDB Work Together
Virima 6.1.1 includes native IP Address Management inside the CMDB — no separate tool, no reconciliation required. IP records and…
Do Your Change Management Tools Alert You to Unplanned Changes?
Change Management is great – funneling changes through a common set of processes to ensure the proper reviews occur and…
Five reasons why cloud assets should be in configuration management database (CMDB)
Are you planning a move to the cloud, or have you already made the move and now want to make…
Device42 Competitors in 2026: Top Alternatives Compared by IT Teams
Device42 competitors include Virima, Faddom, Lansweeper, ServiceNow Discovery, BMC Helix, and Sunbird, and each takes a distinct approach to IT…
Best ServiceNow CMDB Alternatives in 2026: 10 Tools Evaluated on Discovery, Accuracy, and AI Readiness
ServiceNow CMDB alternatives are standalone configuration management platforms that deliver IT asset discovery, CI relationship mapping, and service dependency visualization…
How to Build an AI-Ready CMDB Checklist for 2026
Building an AI-ready CMDB checklist starts with an uncomfortable truth: most CMDBs were never designed for the job AI agents…
Asset lifecycle management best practices: The ultimate guide
Managing technology is more than keeping systems running. You also need to add new software and retire old hardware. Getting…
ITOM processes & Virima: Smarter automation for IT teams
Your IT services work best when everything hums along behind the scenes. That’s exactly where ITOM processes come in. They…
The role of a CMDB in IT management and what changes when it’s accurate
IBM’s 2024 Cost of a Data Breach Report found the global average breach cost reached $4.88 million, with incomplete infrastructure…
SSL Certificate Management: Complete Guide to Tools, Automation & Renewal Tracking
Imagine this: Just days before an important compliance audit, your team finds 300 SSL certificates about to expire. Panic sets…
Simplify your IT operations with Virima’s discovery and mapping
In the rapidly evolving landscape of IT, maintaining an efficient, secure, and reliable infrastructure is more complex than ever. Virima…
Automatic network mapping guide: Benefits & best practices
“Your phone buzzes. It’s the third alert tonight. The network is down again. You open your laptop, hoping the old…
What Is a Service Dependency Map? Types, Benefits, and Tools for IT Teams
As IT setups grow more complex with both cloud and on-prem systems, managing them gets harder. You need better tools…
Strengthen IT Governance with Virima and Ivanti
Without IT governance and risk management, you get security breaches, data loss, regulatory penalties, and direct financial damage. Leave those…
BMC Helix CMDB Alternatives in 2026: What to Evaluate Before You Commit
Managing IT assets can be tough, especially when working with an untrustworthy Configuration Management Database (CMDB) solution. Many companies struggle…
Automated CMDB discovery tools compared: which ones actually keep your CMDB accurate?
Most CMDB discovery tools scan your environment and report what they find. Fewer actually maintain the CI records, relationships, and…
ITOM vs. ITSM: A complete guide to IT operations & service management
ITOM and ITSM get used all the time interchangeably. They shouldn’t be. Both fall under IT management, but they serve…
Top ITSM Software Platforms Compared [2026 Buyer’s Guide]
This guide compares the top ITSM software platforms of 2026 — ServiceNow, Jira Service Management, Ivanti, HaloITSM, Xurrent, Hornbill, and…
The 7 best software asset management solutions in 2024
In today’s complex IT environment, managing software assets efficiently is crucial. Best software asset management solutions help organizations optimize software…
CMDB Best Practices: How companies can get it right
A configuration management database that worked in 2023 does not meet the demands of 2026. Back then, a quarterly spreadsheet…
Is Your CMDB Really a Source of Truth?
Most IT teams rely on the CMDB as their source of truth. Here’s why that’s insufficient for modern IT operations…
Virima Database Discovery: Oracle, MySQL, Apache, Tomcat, IIS & More
Direct answers to every question about Virima’s database and application server discovery capabilities — Oracle, MySQL, Apache, Tomcat, IIS, and…
Apache, Tomcat, and IIS in Your CMDB
Apache, Tomcat, and IIS instances are the invisible middle tier in most enterprise CMDBs. This guide explains why application server…
Best IT Asset Management Tools in 2026: Compared for Hybrid IT Teams
The 10 best IT asset management (ITAM) tools for 2026 are: 1. Virima — Best for unified ITAM, CMDB, and…
Your essential guide to cybersecurity asset management platform
Cybersecurity asset management (CSAM) is a process for identifying, assessing, and prioritizing IT infrastructure for protection. The goal of CSAM…
6 ways your ITAM is key to your organization’s cybersecurity
Cyberattacks have increased over the years. If your organization is to be successful globally, you need to support your IT…
Cybersecurity asset management: 10 things you must know
Cybersecurity asset management has become a crucial part of IT security, but there are still many organizations that have yet…
ITAM vs CSAM: which is better for your business?
Every organization needs a good asset management program. This is true whether the organization is a small business, an education…
Virima vs Axonius: Cybersecurity Asset Management vs IT Asset Management
The Virima vs Axonius comparison comes down to one question: Should asset visibility live with your security team or your…
Medical Device Management: Challenges and Opportunities
Connected medical devices represent one of the largest and fastest-growing segments of the Internet of Things (IoT). Healthcare devices, like…
How IT Can Be Used to Support Healthcare and Medical Devices
An information technology(IT) system outage in most companies is frustrating and it may be disruptive. At healthcare companies, however, where…
The Complete Guide to Healthcare IT Asset Management
Healthcare IT asset management carries stakes that most enterprise environments never face. Between life-critical medical devices, strict regulatory requirements, and…
Elevating IT service impact with Virima’s change management solutions
Change management can feel overwhelming. You need to know what’s connected to what before you make any changes. One wrong…
How to simplify IT compliance management with Virima
IT compliance management is getting harder. Regulations change constantly, asset inventories sprawl across cloud and on-prem environments, and auditors expect…
IT Asset Management for Financial Services: Compliance and Risk Management in 2026
IT asset management for financial services has become a regulatory problem, not just an operational one. When auditors arrive, they…
CMDB Audit Essentials: Ensuring Data Accuracy and Compliance
A well-maintained Configuration Management Database (CMDB) is the backbone of effective IT Asset Management. It stores data on hardware, software,…
Your CMDB: Your ITSM-ITOM Connection
A previous post, “ITSM and ITOM: How They Align, How They Differ, and Why They Matter,” defined IT Service Management…
Complete guide to enterprise IT asset management
Managing IT assets at a large company is not just about tracking serial numbers. You also need to manage how…
Manufacturing IT Asset Management: Managing OT and IT Infrastructure Convergence
Why standard asset management falls short in manufacturing, and how to build the discovery-driven asset record a converged IT/OT environment…
Servicenow Cmdb Governance: Best Practices For Maintaining A Healthy And Accurate Cmdb
ServiceNow CMDB governance in 2026 goes beyond clean data. This guide covers the best practices for establishing ownership, enforcing data…
Top 5 Application Dependency Mapping Tools for IT Teams in 2026
Picture this: your billing app crashes 20 minutes before a board demo. The on-call engineer can see the app is…
Free IT Asset Management Software: Are the Savings Worth The Compromises?
Keeping track of hardware, software licenses, and cloud resources matters for daily operations and security. Free IT asset management software…
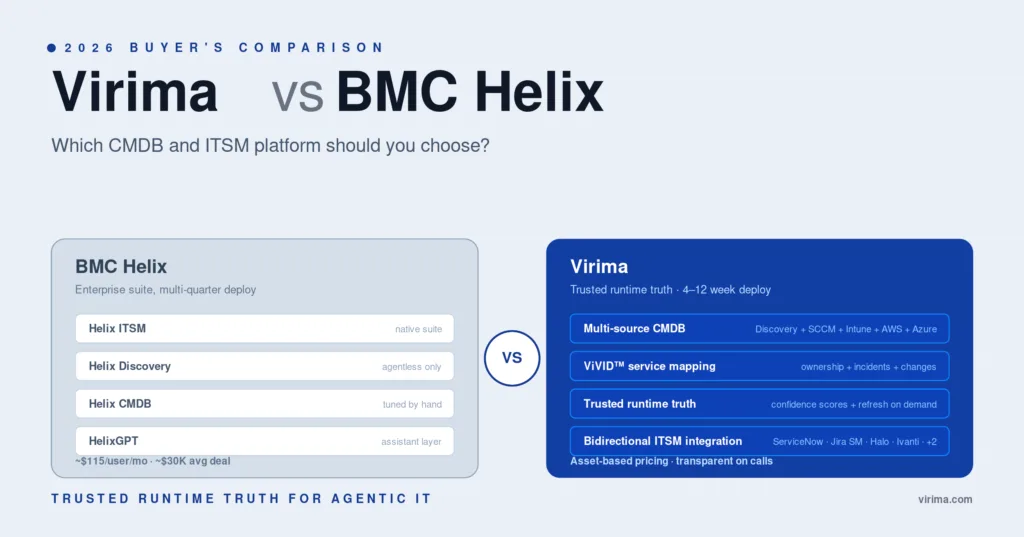
Virima vs BMC Helix 2026: which CMDB and ITSM platform should you choose?
A 2026 side-by-side of Virima vs BMC Helix on CMDB accuracy, ViVID™ service mapping, pricing, deployment time, ITSM integration, and…
Virima vs Freshservice 2026: CMDB and ITSM compared
If you’re searching Virima vs Freshservice, something specific is usually broken. Probably this: Freshservice runs your service desk fine, but…
Virima vs ManageEngine ServiceDesk Plus 2026: What to know before you buy
A side-by-side look at Virima vs ManageEngine ServiceDesk Plus on the decisions that matter in 2026: CMDB freshness, hybrid cloud…
How to optimize IT asset lifecycle management with Virima
Managing IT assets sounds easy at first. But then you end up with thousands of devices and dozens of software…
Virima vs SolarWinds Service Desk 2026: What to know before you buy
Virima vs SolarWinds Service Desk 2026 buyer’s guide: G2 ratings, pricing tiers,
features, and real user sentiment to help you pick…
How Good is Your IT Change Management Process?
In change management, “pretty good” can get you in big trouble. You have an established IT change management process, but…
MSP IT Asset Management: Managing Multiple Client Environments at Scale
Running ITAM for 20+ client environments breaks tools built for single-tenant IT teams. Learn how MSP IT asset management…
Turbocharge Halo Software with Virima’s Visual Impact Display (ViVID™)
Halo Software is a powerful ITSM platform. But Halo ITSM has one limitation: it doesn’t show you how your infrastructure…
Why Virima Leads Xurrent Integrations for Discovery & CMDB
Xurrent is an ITSM platform built around integrations. Its leadership has made that clear — modularity and ecosystem partners sit…
How to streamline your IT operations with Virima ITSM solution
Your IT team juggles dozens of incidents, change requests, and service tickets every week. Without a structured system, those pile…
6 Network Topology Types (with Diagrams) and How to Map Yours
It’s Monday morning. You’ve just settled in with your coffee when the complaints start rolling in, “The Wi-Fi’s slow!” “My…
Best Software License Management Tools in 2026 (Reviewed & Ranked)
Most IT teams don’t discover how much they’re bleeding on software licenses until a vendor forces an audit. I’ve seen…
Network topology explained: Key concepts and importance
In today’s connected world, understanding how our digital systems link together is crucial. Network topology, which maps out these connections,…
How Virima Service Mapping Jira Service Management ITSM processes
Jira Service Management (JSM) handles incidents, changes, and service requests well. But it doesn’t include native service mapping — the…
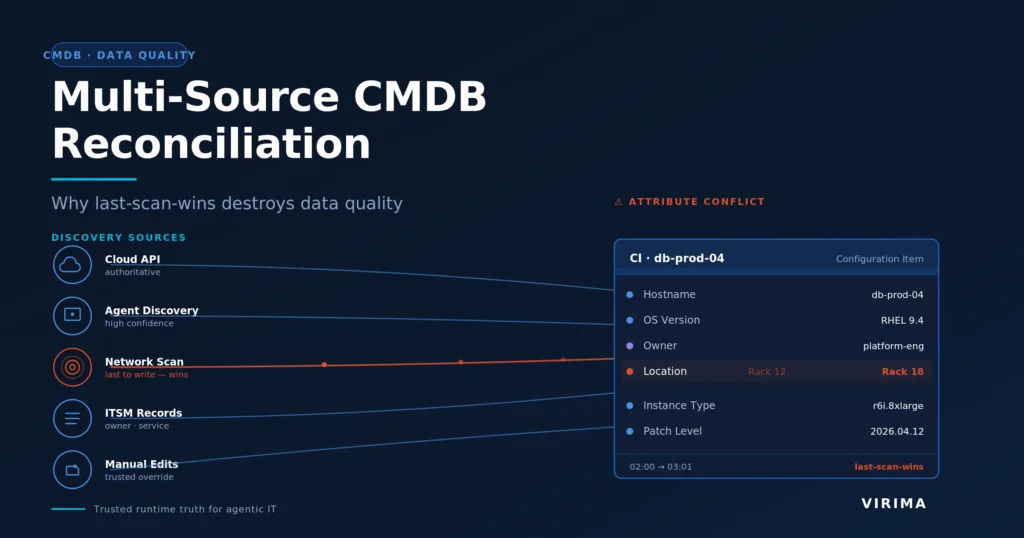
Multi-Source CMDB Reconciliation: Why Last-Scan-Wins Destroys Data Quality
Last-scan-wins is the quiet default behind most CMDB data quality failures. This guide breaks down the four ways it destroys…
Network Device Discovery: What It Is, How It Works, and Why Your CMDB Depends on It
Network device discovery is the unglamorous layer that decides whether your CMDB tells the truth. Here is how it works,…
Top 7 Open Source IT Asset Management Software (2026)
The seven strongest open source IT asset management software tools in 2026 are Snipe-IT, GLPI, Ralph, OCS Inventory NG, i-doit,…
IT infrastructure modernization: How Virima and Ivanti accelerate the transition from legacy to advanced IT infrastructure
Outdated IT infrastructure slows teams down. Compatibility issues, rising maintenance costs, security gaps, and limited scalability make day-to-day operations harder…
Data integrity redefined: Jira service management CMDB and Virima integration in action
Picture an IT infrastructure where every component is accounted for, accurately documented, and connected to the services it supports. That’s…
The role of IT device management in boosting security and productivity
Picture a workplace where every device runs smoothly, data stays secure, and your team stays focused. That sounds great on…
Revolutionizing IT operations: The intersection of Virima and ServiceNow™ AIOps
When your IT operations team runs ServiceNow for ITSM and ITOM, the quality of every workflow depends on the data…
Oracle Database CMDB Discovery Guide: MySQL, Relationships & ViVID
Virima 6.1 introduces Oracle database discovery via Deep Host Scan and MySQL discovery via agents, automatically creating CMDB Runs On…
7 Best Lansweeper Alternatives in 2026: Honest Comparison for Enterprise IT Teams
Lansweeper does network discovery well. It finds devices on your network, builds an inventory, and gives you a starting point….
CMDB Health Score: What It Is, How to Measure It
Most IT teams have a general sense that their CMDB is degraded. 70–80% of organizations fail to build a proper…
Virima vs BMC Helix Discovery: The 2026 Comparison IT Leaders Need Before They Buy
A 2026 head-to-head comparison of Virima and BMC Helix Discovery across discovery methods, CMDB data quality, service mapping, ITAM, deployment…
Introducing ViVID Service Maps
CMDB service maps are visual depictions of hierarchical relationships among business services (sometimes also major applications) and their supporting Configuration Items…
You’ve Decided You Need an ITAM Tool. Now What? (part 1 of 2)
IT Asset Management (ITAM) is critical to effective delivery and management of the IT-powered services that drive your business. But despite…
How IoT Will Impact IT Service Management (ITSM)?
More Devices, More Connections, More User Demands, More Complexity The mobile, social web has grown to include millions of users,…
ITOM governance with automated discovery tools
Effective ITOM governance is critical for maintaining control over today’s complex IT environments. However, manual methods of IT operations management…
Master network configuration change management with Virima
In today’s rapidly evolving digital landscape, managing network operations requires agility, foresight, and a structured approach. Network configuration change management…
Integrating SecOps With Your ITSM: How to Get Started (Part 2)
Integrating SecOps With Your ITSM: How to Get IT Service Management (ITSM) and Security Operations (SecOps) are equally critical to survival…
Maximizing IT Asset value with Virima IT Asset Management
IT asset management is crucial for organizations to effectively track, monitor, and optimize their IT assets. Virima IT Asset Management…
ITAM In A Hybrid Workplace: Remote Asset Monitoring To Secure Your Assets
Organizations with hybrid work setups have a visibility problem. IT assets are scattered across offices, home networks, and cloud environments,…
Integrating SecOps With Your ITSM: How to Get Started (Part 1)
IT Service Management (ITSM) and Security Operations (SecOps) are equally critical to survival and success for many businesses. The need to…
IT operations management functions: Mastering every aspect
Are you struggling to keep your organization’s workstations and assets running smoothly? Do you worry about fixing issues quickly, especially…
Improve customer IT service delivery with Virima IT discovery
Your business is only as good as the experiences it offers its customers. Despite that, many organizations need help to…
Why Virima and ServiceNow are the perfect match for IT Operations
The smooth functioning of regular IT operations plays a crucial role for organizations of all sizes. As per the latest…
How Virima simplifies IT asset management audits
The IT asset management audit plays a key role in maintaining operational efficiency and regulatory compliance. They ensure your organization’s…
IT asset management service for enterprises: How Virima ITAM shines
Effectively managing IT assets is essential for every enterprise, yet it comes with challenges. Disorganized inventory data can lead to…
Differences Between Patch Management and IT Asset Management
In this era of heightened focus on cyber security, patch management is an increasingly popular and urgent subject of discussion…
Future-proofing IT: ServiceNow CMDB integration with Virima
With the accelerating shift toward hybrid infrastructure and automation, future-ready IT operations demand a new level of control and insight….
A comprehensive guide to application dependency mapping
When you look after IT systems, you need to see how apps connect. Today, systems use cloud computing tools, microservices,…
Multi-cloud Deployments: How to Pierce the Fog
Multiple Clouds, Multiple Challenges What is even more challenging than deploying an application on a cloud computing platform? Deploying multiple…
IT Discovery: A Complete Guide for IT Teams
Let’s begin with the three major concerns plaguing IT organizations today The concerns aren’t exclusive to any single IT organization,…
The Importance of IT Service Management Foundations for a Growing Business
In the world of business expansion, the absence of a robust IT service management foundation, encompassing IT discovery and CMDB,…
Top 9 Enterprise Software Asset Management Solutions in 2026
Enterprise software asset management (SAM) is the practice of tracking, managing, and optimizing the software an organization buys, deploys, and…
Leveraging Virima CMDB for change management excellence in IT organizations
The role of change management in IT organizations has become increasingly important. As the rate of changes being made in…
IT Asset Management Tools vs CMDB: Do You Need Both?
The confusion is understandable — but costly Ask ten IT teams how they use their CMDB and their ITAM tool….
ITIL asset management best practices: Your top 10 guide
As an IT asset manager, you already have a lot going on. You’re expected to track devices, licenses, and systems….
IT Asset Management Best Practices 2022
A Brief Overview of IT Asset Management IT asset management is commonly classified as a subset of IT service management…
UVexplorer Review: Features, Limitations & Best Alternatives
Table of Contents What Is UVexplorer? Key features of UVexplorer Strengths of UVexplorer Limitations and constraints Where UVexplorer fits best…
5 Common IT Operations Challenges: Strategies To Overcome Them For Modern Enterprises
IT operations covers a lot of ground: managing infrastructure, responding to incidents, tackling problems, handling change, and releasing. The scope…
Maximizing ITSM efficiency: Atlassian Jira Service Management integration with Virima
Delivering fast and reliable IT service management has never been more important. Atlassian’s Jira Service Management (JSM) helps many teams—from…
What Is an IT Risk Register and How Does Virima Connect Risk to Change Management and Projects?
Virima’s IT risk register provides a centralized, structured record of all technology risks — integrated with change management and project…
IT Risk Register: How to Identify, Track, and Mitigate Technology Risks Across Your Organization
An IT risk register provides a centralized, structured record of every technology risk — with probability scores, impact levels, mitigation…
ServiceNow configuration items (CIs) and configuration management in ServiceNow CMDB: A step-by-step guide
In 2025, misconfigurations remained the top cause of enterprise security and service failures. The Cloud Security Alliance’s 2025 SaaS Security…
Effective service mapping implementation for your business
How often have you struggled to identify how each of your applications, servers, and hosts are interconnected? How many times…
Best CMDB Software in 2026: Top Tools Compared for Enterprise IT Teams
You know that feeling when something breaks in your IT stack, and no one knows who owns it, what it…
ITIL CMDB Best Practices: How to Build a Configuration Database That Stays Accurate
ITIL recommends a CMDB. It doesn’t tell you how to keep it accurate. That’s the gap where most ITIL CMDB…
Top ServiceNow competitors in 2026: alternatives compared
ServiceNow is more powerful and more expensive than ever in 2026. Compare Virima, Device42, BMC Helix, Freshservice, Jira Service Management,…
CMDB for AI Agents: What Your Automation Stack Needs
Nine seconds. That is how long it took an AI coding agent to delete an entire production database, including all…
How to navigate change risk assessment with Virima
Change risk assessment is the process of identifying, evaluating, and mitigating potential problems before you modify your IT environment. Get…
Change risk assessment in IT: How to know your blast radius before you approve
Over 80% of IT-related outages stem from planned changes, not cyberattacks, not hardware failures, but changes that someone on your…
VMware ESXi Discovery FAQ: Supported Versions, Data Captured, CI Relationships
Direct answers to every question about Virima’s VMware vCenter and ESXi discovery capabilities — what gets captured, how relationships are…
CMDB Business Rules: End Manual CI Maintenance
Most CMDB projects fail not at implementation but at maintenance. Manual CI updates create data drift that makes the CMDB…
CMDB Business Rules: Automate IT Operations
CMDB business rules automate CI promotion decisions, downstream sync actions, and ITSM event responses in Virima 6.1.1 — eliminating manual…
Why Is Your ServiceNow CMDB Always Inaccurate?
After every ServiceNow Knowledge Forum, the conversations about CMDB accuracy follow a predictable pattern. IT teams return from sessions on…
Certificate Lifecycle Management: Best Practices to Prevent Outages and Automate Renewals
Certificate lifecycle management is how IT teams track, renew, and govern SSL/TLS certificates before they expire and cause outages. This…
Application Dependency Mapping vs Service Mapping: What’s the Difference?
Why these two terms keep getting confused Ask five IT operations professionals to define application dependency mapping and service mapping,…
Virima: A Powerful Alternative to Jira Asset Discovery for IT Asset and Configuration Management
Change management controls how IT changes move from proposal to production. Done well, it keeps services running and teams aligned….
How Virima’s change management tools can transform your change processes
Change management controls how IT changes move from proposal to production. Done well, it keeps services running and teams aligned….
Transform your IT Operations: Integrating Jira Service Desk with Virima
In fast-paced IT environments, having the right tools isn’t just an advantage; it’s table stakes. Jira Service Desk (now Jira…
Unified IT platform: The future of IT asset visibility with Virima and Ivanti
Managing complex IT environments means dealing with hundreds of tools, applications, and device types spread across on-prem and cloud infrastructure….
Jira integration (JSM): Turbocharge ITSM process efficiency with Virima
IT operations teams using Jira Service Management often face the same problem. Your CMDB feels incomplete, and asset data quickly…
Top Asset Lifecycle Management Software for Businesses
Your IT assets do more than sit on a spreadsheet. They power every service your organization delivers. But without the…
What ITIL4 means for ITIL IT Operations Management?
ITIL4 moved past the old process-by-process thinking. Instead of treating each practice separately, it focuses on how IT delivers value…
Benefits of network asset management software for IT teams
Your network runs on hardware: routers, switches, firewalls, servers, and wireless controllers. But how well do you actually know what’s…
How to build an AWS configuration management database
Managing configurations in large AWS setups affects every team that uses asset data. You need accurate and up-to-date information to…
The CMDB capabilities your ITSM team can’t operate without
The systems we build to simplify operations often need simplifying themselves. Tasks once tracked with pen and paper now depend…
Virima and Ivanti Neurons for ITSM: A path to ITSM efficiency and operational excellence
IT teams deal with two things every day: keeping operations stable and keeping every asset compliant with security standards. According…
How Virima’s automated IT asset management boosts your ITAM processes
Most IT teams know exactly how many servers they bought last quarter. Fewer can tell you how many are still…
CMDB meaning: What does CMDB stand for and why does it matter?
CMDB stands for Configuration Management Database — but understanding the acronym only scratches the surface. The meaning behind each word…
The real CMDB benefits for ITSM and why most teams aren’t seeing them yet
ITSM teams with accurate CMDB data resolve incidents faster, approve changes more confidently, and spend significantly less time in post-incident…
Why CMDBs Keep Failing (And What CMDB Governance Actually Fixes)
CMDB drift is almost always a governance problem. This guide covers what CMDB governance means, why CMDBs lose accuracy, and…
Application dependency mapping: What it is, why it matters, and how to do it right
Application dependency mapping discovers how apps connect to servers, databases, and services. This guide covers what ADM is, how it…
How Virima Complements ORDR: Trusted Runtime Truth for IoT and OT Security
ORDR sees every connected device on your network. Virima tells you what each device does, what service it supports, and…
What Is a CMDB? Complete Guide to Configuration Management Databases
Introduction A Configuration Management Database (CMDB) is no longer a theoretical concept from the ITIL playbook. It has become a…
Top 5 Enterprise IT Asset Management Software Solutions
Enterprise IT asset management software plays a pivotal role in optimizing asset utilization, reducing costs, and ensuring compliance. With numerous…
Automated Incident Response and Management with Virima
It’s 2:13 a.m., and an alert wakes you up. Then many more alerts follow fast. Soon, your cloud, devices, and…
The top 8 asset inventory management software in 2026
Most IT teams don’t lose control of their assets all at once. It happens gradually. A device gets deployed without…
A CMDB Without Discovery Is Just a Database
Discovery gives CMDB database users two things that matter most: trustworthy data and faster time to value. Without it, your…
Digital Transformation in Businesses Requires a Better Understanding of Your IT Environment
Digital transformation has become a defining priority across IT departments. Companies are finding new ways to put technology to work…
What Is SACM? A Practical Guide for IT Teams
SACM (Service Asset and Configuration Management) is one of the most foundational ITIL v4 practices. This FAQ answers the most…
Agent-based vs. agentless discovery: which is best for your business?
Agent-based, agentless, and API-based, how each IT discovery method works, when to use each, and how Virima supports all three…
What Is Blast Radius in IT Change Management?
TLDR: Blast radius in IT is the breadth of impact a failed or misconfigured change can produce. The larger the…
What Is Agentic IT? A Plain-English Guide for IT Leaders
TLDR: Agentic IT is the discipline of deploying AI agents that can perceive, reason, and act across enterprise IT environments…
ServiceNow CMDB Accuracy: Why Native Discovery Falls Short at Scale
ServiceNow is built on the assumption that your CMDB is accurate. But native Discovery has structural limits that cause CMDB…
Strategy And Risk Management With CSAM
Cybersecurity risk management isn’t a one-time audit. It’s an ongoing cycle of identifying what you have, figuring out how it’s…
Discovering Security Gaps: Enhance IT Systems With ITAM & ITSM Automation
Unpatched servers, shadow IT, and unknown dependencies — these are the gaps that show up in IT audit findings and…
Enhanced Jira incident management: Virima’s ViVID™ for Jira Service Management
No matter what incident management workflow your organization follows, three needs stay constant: a clear view of the infrastructure, effective…
Complex IT environment: The Challenges Of Achieving IT Visibility
In a complex IT environment, IT visibility is what separates teams that react from teams that stay ahead. It gives…
Why Virima is the best CMDB integration for your ITSM processes
A reliable Configuration Management Database (CMDB) can reshape how your organization handles IT Service Management (ITSM), forming the foundation of…
Halo CMDB: How Virima enhances it?
Halo CMDB gives your team a central place within a configuration management database CMDB to store and track configuration items…
Beyond service mapping plus: Discover a superior alternative
If your team relies on ServiceNow service mapping plus to visualize service dependencies, you already know it works. You’ve also…
Best practices for IT infrastructure and operations management in 2026
Six proven IT infrastructure management best practices for 2026, refreshed for hybrid cloud complexity, agentic AI, and trusted runtime truth…
Alternative to ServiceNow application dependency mapping: Exploring Virima
ServiceNow is a go-to platform for application dependency mapping. It maps how applications, servers, databases, and network components connect and…
The role of CMDB compliance in IT security and risk management
Managing IT security without a CMDB compliance strategy means operating with blind spots across your entire infrastructure, and 57% of…
Simplify IT discovery and gain full visibility with Virima’s automated tools
IT environments don’t stand still. A developer spins up a cloud instance on Friday. An employee installs unapproved software on…
Visualize and optimize: Unleash the power of dependency mapping with Virima
Dependency mapping gives your IT team a clear picture of how applications, infrastructure, and services connect. When something breaks, you…
Asset lifecycle management process: Optimizing your strategy
The asset lifecycle management process is the sequence of steps an IT organization runs every asset through, from the moment…
The Zero-Touch Service Desk Needs a Zero-Doubt CMDB
Zero-touch service desk automation only works when the CMDB it queries is accurate. Here’s what breaks when it isn’t, and…
5 K26 Takeaways for IT Directors Who Couldn’t Make It to Vegas
Couldn’t make it to K26 2026 in Las Vegas? Here are the 5 takeaways IT directors need to act on…
What K26 Told Us About the Future of Agentic IT (And What It Didn’t Say)
K26 2026 confirmed agentic IT as enterprise IT’s near future. Here’s what ServiceNow’s conference revealed and the critical gaps the…
Trusted Source of Runtime Truth for Agentic IT: Why Virima Delivers What Other Platforms Only Promise
Agentic IT is on every technology roadmap. Vendors are racing to launch AI agents, “command towers,” and self‑optimizing workflows that promise…
CMDB with Automated Discovery for Hybrid and Cloud Environments
Monday, 9:07 a.m. Your CEO messages: “Is that finance server still under warranty? And why is payroll so slow?” You…
Halo Discovery And Virima: A Powerful IT Discovery Duo
Gaps in asset visibility, outdated configuration data, and manual tracking create inefficiencies, security risks, and compliance failures. According to IBM’s…
What K26 Is Really Telling IT Leaders About Their CMDB
ServiceNow Knowledge 2026 announced the Agentic Era. But the more urgent message was hidden in the CMDB foundation sessions. Here’s…
Device42 vs Virima: Head-to-head Comparison For ITSM Success
ITSM is the backbone of service management ITSM. It helps you run IT in a smooth and simple way. It…
How Mapping Applications Enhance ITSM Processes
Picture your entire IT infrastructure on a single screen: every server, application, database, and network link visible with its connections….
How Does IT Visibility Improve IT Operational Efficiency in a Business?
Your IT environment is growing faster than you can track. New servers spin up, and cloud systems keep increasing. Also,…
Device42 Application Dependency Mapping vs Virima: Which Offers Better Value?
Application dependency mapping (ADM) maps the connections between applications, services, and infrastructure in your IT environment, giving complete visibility into…
The Most Impactful Jira Service Manager Tool Examples: Virima
Jira Service Management (JSM) is a solid service management itsm platform for service delivery, supporting teams that manage customer requests,…
Maximizing IT Service Performance With Integrated ServiceNow ITSM and CMDB Solutions
ServiceNow offers two core solutions for managing IT services and infrastructure: the Configuration Management Database (CMDB) and the IT Service…
Top 5 IT Asset Management Solutions Compared
Every IT team juggles hardware, software licenses, and cloud resources across environments that keep growing. Without a clear system to…
CSDM 5.0 Audit: The Hardest Work No One Talks About at K26
K26 2026 showcased CSDM 5.0 in polished demos. Here’s what the actual audit work looks like and why most organizations…
Network Topology Mapping: Benefits & Types
What is network topology mapping? Network topology mapping gives IT teams a visual picture of every device, connection, and path…
Application Change Management: Reduce Failed Changes
Picture this: the IT team of a 500-bed hospital is working late to deploy an EHR upgrade. The goal is…
Top CMDB Tools For Turbocharging Your ITSM Efforts
Your IT environment changes daily. New servers spin up, software gets patched, and network configurations shift. Without a reliable Configuration…
Asset Management In IT: A Complete Guide
Managing IT assets is vital for smooth business operations and resource optimization. According to the 2025 Flexera State of ITAM…
Active vs. passive IT asset discovery: which one works better?
Shadow IT, IoT devices, and lab gear slip under the radar more often than most teams want to admit. If…
10 types of CMDB discovery techniques you must know
A CMDB stores every detail about your IT assets, services, and devices. However, cloud environments bring unique discovery needs. To…
Spiceworks IT Asset Management Features Limitations And Alternative
When managing IT assets, the right tools directly affect how fast your team resolves incidents, tracks license spend, and plans…
BMC Remedy CMDB: Features, Benefits, and Alternatives
BMC Remedy CMDB has been around for over two decades. However, BMC is now shifting toward its cloud-based Helix platform….
Before You Run AI Agents on ServiceNow, Answer These 5 Questions About Your CMDB
Before your agentic AI deployment goes live on ServiceNow, five CMDB readiness questions determine whether it succeeds or fails in…
Everything You Must Know About National Vulnerability Database Integration
Keeping your IT infrastructure secure starts with knowing where the risks are. According to IBM, the global average cost of…
Device42 Asset Management: Pros, Cons & Alternatives
Device42 asset management gives you a suite of features for IT asset tracking and management. It helps organizations control their…
IT Change Management and Configuration Management: How They Work Together
Change management and configuration management get mixed up constantly, and it’s easy to see why. Both involve controlling changes to…
ITIL Types of Changes: Standard, Normal & Emergency With Real Examples
Change is one of the few things you can always expect in the world of IT. New business requirements appear,…
Device42 auto discovery: Features, Process, and Alternative
Managing your IT infrastructure gets harder as new devices show up and others slip off the radar. Device42 auto-discovery handles…
SolarWinds IT Asset Management: Features & Limits
Managing hardware, software, and cloud resources across a growing network can feel overwhelming. As your environment grows, it becomes harder…
Agentic AI in the Enterprise: What IT Leaders Must Get Right
Agentic AI moves from assisting to acting. But acting safely in enterprise IT requires more than a capable model. It…
What is Vulnerability Management?
A vulnerability is a weakness in a system that can expose it to attacks or damage. Open ports, unsafe settings,…
AI Agents in ITSM: Why the Data Layer Determines Whether They Work
AI agents in ITSM promise faster resolution and zero-touch workflows. But they only act as well as the data underneath…
How Virima Augments the ServiceNow Context Engine with Trusted Runtime Truth
Workflow context tells AI agents what happened. Trusted Runtime Truth tells them what exists, how it’s connected, and what could…
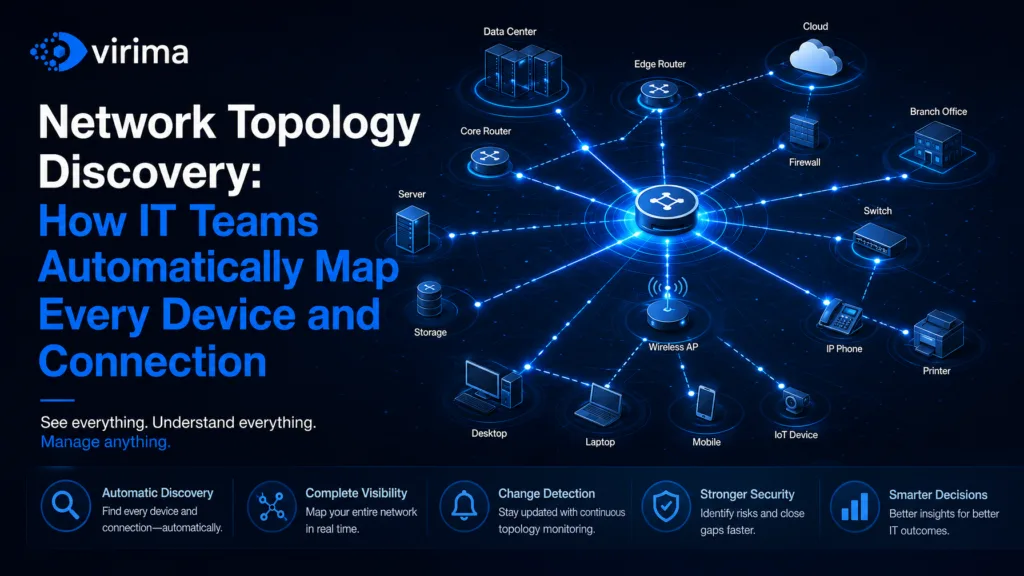
Network Topology Discovery: How IT Teams Automatically Map Every Device and Connection
The Problem With Manual Network Maps Your network diagram was accurate the day someone drew it. That was probably six…
Configuration Item lifecycle: From discovery to decommission in a modern CMDB
The problem with treating CIs as static records Most CMDB projects start with momentum. Teams run a discovery sweep, populate…
ITIL Change Management and CMDB Accuracy: Why One Depends on the Other
The change that should have gone fine The CAB approved it. The change window opened on schedule. Forty minutes in,…
CMDB Alone Is Not AI Governance
When I speak with fellow large and medium enterprise CIOs and CTOs about making their environment AI-ready, the conversation almost…
Why AI agents need trusted runtime truth, not just good data
The promise of agentic IT is real. AI agents that can triage incidents, assess change risk, prioritize vulnerabilities, and recommend…
CMDB TCO Analysis: The Real Cost of Inaccurate Data
Stale CMDB data drives hidden costs in downtime, license waste, and audit risk. Learn how to quantify the gap and…
Cisco & Juniper Switch Stack Discovery in the CMDB | Virima
Virima 6.1 introduces Beta storage and HCI topology discovery for Nutanix, NetApp ONTAP, and HP MSA. Populate CMDB and service…
Storage and HCI Topology Discovery in Virima 6.1
Storage underpins everything, yet without proper storage and HCI Topology Discovery, it remains the most opaque layer in modern infrastructure….
How to Prioritize Vulnerability Remediation Using CMDB Asset Criticality and Service Maps
Learn how to use CMDB asset criticality and ViVID service maps to build a vulnerability remediation priority queue that targets…
Does Virima Include Vulnerability Management? How NIST NVD Integration Works with CMDB
Answers to the most common questions about Virima 6.1.1 vulnerability management — how NIST NVD integration works, how CVEs link…
CMDB and Vulnerability Management: How to Automatically Link CVEs to Affected IT Assets
Discover how Virima 6.1.1 integrates CMDB with vulnerability management to automatically link CVEs to configuration items — enabling risk-based remediation…
CMDB-Backed Incident Management: How Real-Time CI Data Reduces MTTR and Speeds Up Root Cause Analysis
Long MTTR is a data problem. Virima 6.1.1 connects every incident to its CMDB CI, overlays impact on ViVID service…
NetApp, Arista, and Aruba Discovery: Auto-Populate Your CMDB from Network and Storage Infrastructure
Discover how Virima 6.1.1 auto-populates your CMDB from NetApp ONTAP, Arista EOS, and Aruba switches using SNMP and SSH discovery…
Does Virima Support Pure Storage, NetApp, Arista, and Aruba Discovery?
Structured FAQ answering whether Virima supports Pure Storage, NetApp, Arista, and Aruba discovery. Covers supported vendors, discovery protocols, and CI…
How to Automatically Import and Discover AWS, Azure, and Intune Assets into Your CMDB
Cloud assets don’t appear in your CMDB automatically. This step-by-step guide covers AWS Assume Role, Azure service principals, and Intune…
AWS Assume Role for CMDB Discovery: Why Cross-Account Access Control Matters for Security
Learn why static AWS access keys for CMDB discovery create persistent security risks, and how AWS Assume Role with STS…
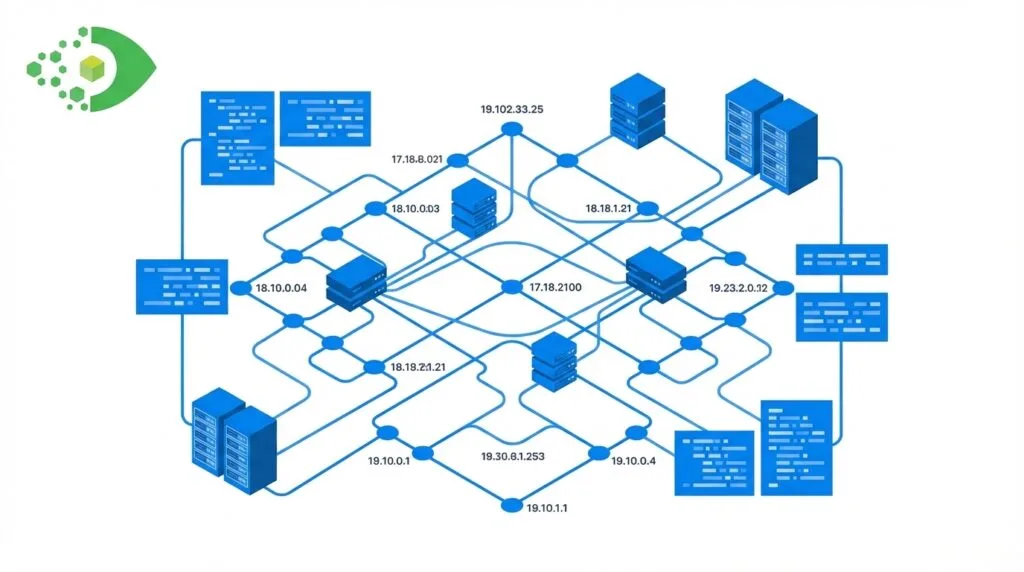
What Is CI-to-Hardware Asset Auto-Linking and Why Does It Matter for ITAM Accuracy?
CI-to-hardware asset auto-linking is the automated process of matching CMDB configuration items to ITAM hardware asset records by serial number…
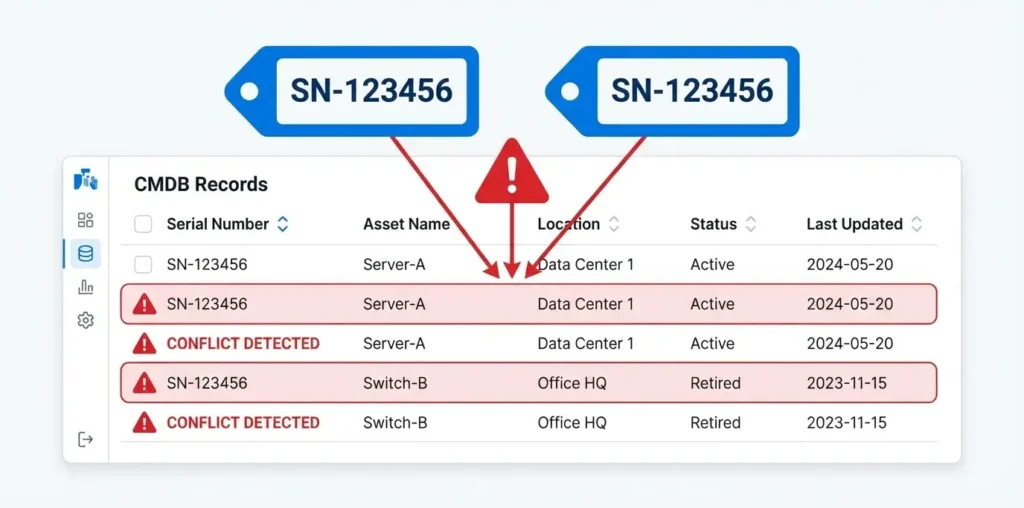
Serial Number Conflicts in CMDB: What They Are and How to Resolve Them
A serial number conflict in a CMDB occurs when two asset records share the same serial number, blocking auto-linking and…
What Happens to CIs When IT Assets Are Decommissioned? A CMDB Best Practices Guide
When IT assets retire, their CMDB CIs must follow a defined decommission process — not deletion. This guide covers best…
Change Impact Analysis with CMDB: How to Assess Risk Before Every IT Change
Change-related incidents remain the leading cause of IT outages. The gap between change intent and change outcome closes when CMDB…
How to Use CMDB Service Maps to Identify Stakeholders and Approval Paths for IT Changes
Missing the right stakeholder in a change approval workflow is one of the most common causes of post-change escalations. CMDB…
How Does Virima Support ITIL Change Management? CMDB, Impact Analysis, and ViVID Explained
Virima 6.1.1 delivers full ITIL v4 change management backed by live CMDB data, ViVID Service Maps for impact visualization, Discovery-based…
IT Runbook Automation in ITSM: Automating Repetitive Tasks from Password Resets to Server Reboots
IT teams spend an estimated 2-3 months per year on repetitive manual tasks that should be automated. Runbook automation in…
How Does Virima Handle Software License Tracking and Compliance? A Complete ITAM Guide
Virima 6.1.1 tracks software license keys in ITAM, links them to CIs via component-of relationships, and exports compliance reports for…
IPAM and CMDB Together: Why Managing IP Addresses Inside Your Configuration Database Changes Everything
Managing IP addresses in a standalone IPAM tool creates a persistent reconciliation gap with your CMDB. Virima 6.1.1 includes native…
CMDB vs. SACM: Understanding the Difference and Why Both Matter in ITIL v4
The CMDB is the tool. SACM is the discipline that keeps it accurate. Organizations that deploy one without the other…
ITIL v4 SACM Explained: What Service Asset and Configuration Management Means for Your CMDB and Service Delivery
SACM is the ITIL v4 practice that governs how service assets and CIs are identified, controlled, and verified. Learn the…
CMDB Implementation: A Step-by-Step Guide
Most CMDB implementations fail not because of the tool, but because foundational decisions were wrong before the first scan ran…
What Is a CMDB? A Complete Guide for IT Teams
A CMDB is the single source of truth for your IT environment. This guide explains what a CMDB is, how…
Does Virima Discover macOS, Linux, and Windows Devices? A Complete OS Support Guide
A structured FAQ covering Virima’s endpoint discovery support for macOS, Linux, and Windows — what data each OS returns, how…
6 steps to create an effective IT business continuity plan
Picture your organization facing an unexpected disruption, whether from a cyberattack, natural disaster, or technical failure. Without a well-structured IT…
CMDB vs ITAM: Auto-Link CIs to Hardware Assets
Table of Contents What Is a CMDB and What Is ITAM? The CMDB-ITAM Gap Problem How Serial Number-Based Auto-Linking Works…
The business impact of choosing the right software licensing model
Every software licensing decision hits your bottom line. Pick the wrong model and you overpay for seats nobody uses. You…
Top 10 features that make an SSL management solution stand out
Certificate lifespans are collapsing. In April 2025, the CA/Browser Forum unanimously voted to reduce maximum TLS certificate validity from 398…
What Is ViVID Service Mapping? How Virima Visualizes IT Service Dependencies
ViVID Service Mapping in Virima 6.1.1 is a dynamic visualization layer built on the Virima CMDB that automatically maps IT…
How to Overlay ITSM Incidents and Vulnerabilities onto Your IT Service Map for Faster Root Cause Analysis
Learn how Virima 6.1.1 ViVID overlays ITSM incidents and NIST NVD vulnerabilities onto your IT service map to accelerate root…
Does Virima Discover Kubernetes, Lambda, and Serverless Cloud Services? A Complete Cloud Coverage Guide
Find out exactly which cloud services Virima discovers — Kubernetes, Lambda, EKS, AKS, and ECS — with a complete multi-cloud…
The Real Cost of CMDB Inaccuracy: A TCO Analysis
Stale CMDB data drives hidden costs in downtime, license waste, and audit risk. Learn how to quantify the gap and…
VMware and ESXi CMDB Discovery: How to Get Complete Visibility into Your Virtualized Infrastructure
VMware ESXi and vCenter discovery for enterprise CMDBs requires capturing physical hosts, hypervisors, VMs, cluster membership, and all CI relationships…
AWS and Azure CMDB Discovery: A Complete Guide to Cloud Asset Visibility with Virima
A complete guide to AWS and Azure CMDB discovery with Virima, covering EC2, S3, Lambda, ECR, NAT Gateways, Azure VMs,…
Communication Views in CMDB: How to See Host-to-Host Traffic Flows, Ghost Machines, and Open Ports
Discover how Virima 6.1.1 ViVID Communication View surfaces host-to-host traffic flows, open ports, and ghost machines — undocumented devices that…
Linux CMDB Discovery: Disk Capacity, Last Login, Process Data, and Non-Sudo Scanning
Linux runs enterprise servers, containers, and developer workstations — but CMDB discovery often fails in locked-down environments that prohibit sudo…
How to Discover and Map Pure Storage FlashArray in Your CMDB
TLDR Pure Storage FlashArray arrays rarely appear in CMDBs because most discovery tools treat storage as out-of-scope. Automated SSH or…
How to Discover Oracle and MySQL Databases in Your CMDB: A Complete Guide
Most CMDBs track the server but miss what runs on it — leaving Oracle and MySQL databases invisible and change…
Virima Self-Service Portal: Features & Capabilities
Virima’s self-service portal gives employees direct access to IT services, incident tracking, knowledge articles, and automated request fulfillment — all…
Stop Buying ITSM Blind: A CPO–CFO Playbook for Maximizing ITSM Value with Discovery, CMDB, and Service Maps
Most organizations don’t have an ITSM problem. They have a data problem. CPOs and CFOs approve large investments in ITSM…
How to Reduce IT Help Desk Tickets with a Self-Service Portal, Service Catalog, and Knowledge Base
An IT self-service portal reduces help desk ticket volume by giving employees direct access to services, knowledge articles, and incident…
Which Network Device Vendors Does Virima Discover? Cisco, Juniper, Aruba, Fortinet, APC, and More
A structured FAQ covering Virima’s network device discovery support: which vendors, which protocols, what data, and how switch stack relationships…
Kubernetes CMDB Discovery: How to Track EKS, ECS, AKS, and Containerized Workloads in Your CMDB
Discover how Virima auto-discovers EKS, ECS, and AKS Kubernetes workloads as CIs in your CMDB for complete cloud-native infrastructure visibility.
Azure Cosmos DB, Functions, and Key Vault in CMDB: Closing the PaaS Discovery Gap
Azure PaaS resources — Cosmos DB, Azure Functions, Key Vault, and Storage Accounts — are invisible to traditional CMDB discovery…
Fortinet, Aruba, and APC UPS Discovery: Closing the Network Device CMDB Gap
Fortinet firewalls, Aruba access points, and APC UPS devices run in almost every enterprise — but rarely appear in the…
Optimized Halo Asset Management With Virima IT discovery
Effective IT asset management starts when you clearly see all your hardware and software. First, you need correct and up-to-date…
How Does Virima’s ServiceNow CMDB Sync Work? A Step-by-Step Guide
TLDR Overview: How Virima Connects to ServiceNow Virima functions as a discovery and CMDB enrichment layer that feeds CI data…
Does Virima Integrate with Xurrent? How Incident and Change Data Flows Between Systems
Virima integrates with Xurrent to deliver automated CMDB discovery, ViVID service mapping, and ITSM data overlays. This FAQ covers incident…
The Real Reason Your CMDB Keeps Failing (And How to Fix It)
If you’ve invested in CMDB software and still feel like you’re operating blind, you’re not alone — even with what…
You Don’t Have a Certificate Management Strategy. You Have a Spreadsheet and a Prayer.
SSL/TLS certificate lifetimes just dropped to 200 days. They’re heading to 47. And the way most enterprises manage certificates won’t survive what’s coming. By Salil Kulkarni, Chief Strategy and Information Officer, Virima….
How to Discover Cisco and Juniper Switch Stacks in Your CMDB
Switch stacks present a unique CMDB challenge: a single management IP masks multiple physical devices. Learn how to discover Cisco…
How Does Virima Connect ITSM Incident Management to CMDB? A Practical Guide
A practical FAQ on how Virima 6.1.1 connects ITSM incident management to CMDB — covering CI linkage, automated incident creation,…
How to Track, Report, and Audit Decommissioned IT Assets in Your CMDB
TLDR Ghost assets, devices, and software no longer in service but still in asset records, inflate licensing counts, distort audits,…
How to Prevent Duplicate CIs and Sync Errors in ServiceNow CMDB Integration
TLDR Duplicate CIs in ServiceNow CMDB, often referred to as ServiceNow CMDB duplicate CIs, originate from multiple discovery sources, uncontrolled…
macOS Discovery in CMDB: Why Apple Devices Are a Blind Spot and How to Fix It
Macs are standard equipment for enterprise IT, finance, design, and executive teams — yet most CMDBs have no macOS CI…
Software License Management in ITAM: How to Track, Audit, and Stay Compliant with Your Software Assets
TL DR: Software license management in ITAM connects license keys to installed software instances and the CIs they run on,…
Hybrid cloud strategy: Best practices, frameworks & Virima’s edge
A hybrid cloud strategy is no longer optional for most enterprises. You now manage workloads across on-premises systems, private clouds,…
How to Create an Effective Asset Management Report
IT asset management (ITAM) reports turn raw asset data into decisions. They show you what you own, how it performs,…
ServiceNow CMDB Workspace: Complete Setup & Best Practices Guide [2026]
If you are setting up the ServiceNow CMDB Workspace for the first time, trying to get more out of it,…
How to Implement Business Continuity Planning with ITAM and Service Mapping
Preparing for a disaster is often not as simple as it seems. When you’re thinking about how to protect your…
Mastering audit management and compliance tools
Regulatory expectations continue to rise. At the same time, enterprise IT environments are expanding across hybrid cloud, SaaS, and distributed…
Choosing Between Autotask and Modern ITSM Tools for Mid-Sized Enterprises
Last year, an IT Ops team believed their service desk was running smoothly. Tickets flowed efficiently. SLAs appeared green across…
How does ManageEngine AssetExplorer compare to other asset management tools?
It usually starts with a win. An IT team rolls out ManageEngine AssetExplorer, finally centralizes inventory, and gets software licensing…
AI in ITSM: What Works, Risks, and the Virima Advantage
Enterprise IT teams are not short on AI promises. They are short on clarity. AI is already embedded in many…
Asset Request and Form Management for Better Control and Visibility
An employee’s laptop request should not feel like sending a message into a black hole. Yet across many enterprises, that…
A Practical Guide to Enterprise AI Monitoring and Observability
Enterprise AI does not fail like normal software. When a server breaks, you see alerts fast. However, AI can look…
Unified Network and Application Monitoring: Best Practices for Modern IT Operations
At 9:07 a.m., your dashboard turns yellow. Latency starts to rise. Soon, remote offices complain. Transactions slow down, and the…
Understanding MTBF vs Service Availability in IT Operations
Service availability is no longer a reliable indicator of reliability.Most reliability metrics come from small failures repeated at scale: a…
Open Infrastructure Mapping Tools for Smarter Enterprise IT Management
Picture an outage bridge where the only “map” is a Visio diagram last updated two quarters ago. The network team…
Audit-Ready Asset Management Dashboards With Continuous Discovery
At 9:12 a.m., you get an audit email. It asks for proof that your asset list is current. In regulated…
ServiceNow ITOM service mapping: Is it the right fit for you?
Key takeaways (TL;DR) ServiceNow ITOM Service Mapping can produce strong service maps but only when discovery coverage and CMDB hygiene…
The top five insights from Gartner IOCS 2025
Gartner’s IT Infrastructure, Operations & Cloud Strategies (IOCS) Conference has always been a useful barometer for where IT operations priorities…
Reduce MTTR with Xurrent Ticketing & Virima Service Mapping
Incident pressure builds quickly inside the Xurrent ticketing system. Alerts arrive in waves, tickets pile up, and multiple teams are…
Top ManageEngine Alternatives & Competitors (2026 Guide)
ManageEngine may have worked well at the start. It gave your IT team visibility, faster control, and quick setup wins….
From blind spots to full visibility: How Virima powers Xurrent discovery
Today’s IT environments span data centers, cloud platforms, distributed applications, and remote endpoints. Managing this scale requires ITSM platforms that…
From Discovery to Regulatory Audit: How Automation Keeps You Audit-Ready All Year
Keeping up with compliance can feel like an endless race. Between changing regulations, expanding digital environments, and constant security risks,…
Closing the gaps: How Virima strengthens Xurrent’s CMDB with a robust discovery
The Xurrent CMDB is a core system that supports accurate configuration data, reliable operations, and confident IT decision-making. As environments…



























































































































































































![ServiceNow CMDB Workspace: Complete Setup & Best Practices Guide [2026]](https://virima.com/wp-content/uploads/2026/03/CMDB-WITH-AUTOMATED-DISCOVERY-30-1024x576.png.webp)