Discovering Security Gaps: Enhance IT Systems With ITAM & ITSM Automation
Unpatched servers, shadow IT, and unknown dependencies — these are the gaps that show up in IT audit findings and post-incident reviews. As attack surfaces grow more complex, identifying where your IT environment is exposed is a core operational requirement, not just a security team checkbox.
This blog breaks down how IT Asset Management and ITSM automation help you find and close security gaps. We’ll also cover how Virima’s discovery and service management platform fits into this process.
Why IT asset and service management automation matters for security
Manual asset tracking breaks down fast. In fact, 78%of enterprises now use IT asset management solutions, reflecting how organizations are moving away from manual tracking to automated visibility. Spreadsheets go stale, shadow IT grows unchecked, and your team can’t protect what it doesn’t know exists. ITAM and ITSM automation solve this by giving your operations team consistent, up-to-date visibility across the infrastructure.
In practice:
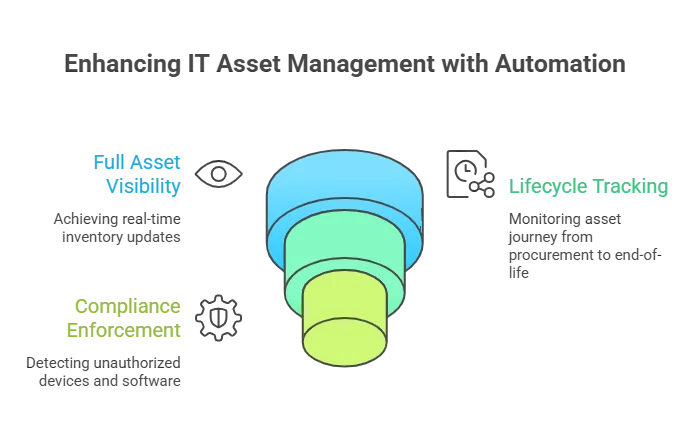
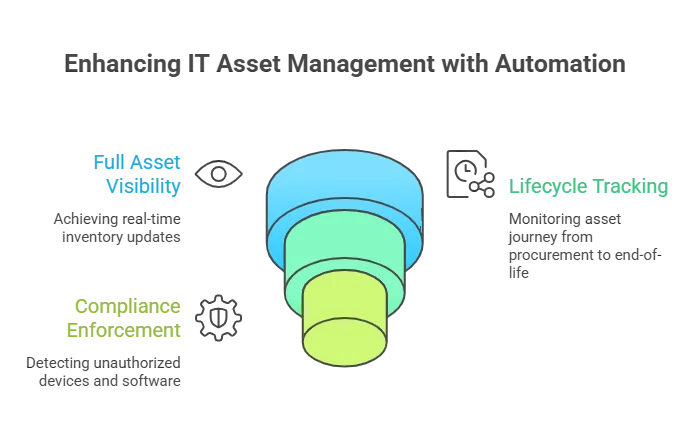
- Full asset visibility — Automated IT discovery scans your network on recurring schedules, covering on-prem, cloud, and remote endpoints, so your asset inventory stays current without manual effort.
- Lifecycle tracking — Every asset is tracked from procurement through decommissioning. When a device hits end-of-life, your team knows before it becomes a security liability.
- Compliance enforcement — Automated workflows flag unauthorized devices and unlicensed software. Recurring scans also surface configuration changes between scan cycles, so your team catches the gaps that auditors look for and attackers exploit.
What are the most common IT security gaps?
Most IT security gaps fall into a few predictable categories(Supporting this, 45%of organizations report security risks due to poor configurations, one of the most common and preventable gaps.): unknown or unmanaged assets, outdated software missing critical patches, misconfigured devices, orphaned user accounts with active permissions, and undocumented dependencies between services. The common thread is visibility. If your team doesn’t know an asset exists or how it connects to other systems, it can’t be secured. A strong cybersecurity asset management practice paired with automated discovery and a well-maintained CMDB eliminates the biggest category of gaps — the ones you didn’t know you had.
[ Read also: Cybersecurity asset management: 10 things you must know ]
How IT asset management identifies security gaps
The first step in closing IT security gaps is knowing exactly what’s in your environment. IT Asset Management gives your team a complete inventory of hardware, software, and configurations across the infrastructure.
Virima’s discovery engine automatically identifies and categorizes assets. It captures device specifications, software versions, installed patches, and configurations. By cross-referencing discovered assets against the NIST National Vulnerability Database (This is increasingly important as cybersecurity incidents are growing by 22% year-over-year, putting more pressure on teams to identify vulnerabilities faster.), your team can flag software with known CVEs automatically. This adds an extra layer of protection to your existing vulnerability management tools, and the NVD integration is included at no additional cost.
How end-of-life assets create security gaps
ITAM also supports risk assessment by tracking end-of-life dates. Hardware and software past their support window don’t receive security patches, making them prime targets. When your ITAM system flags an asset approaching end-of-life, your ops team can plan replacements before the gap opens.
Agentless and agent-based discovery for full coverage
What makes Virima’s approach effective is flexibility in how discovery runs:
- Agentless discovery scans your network without installing software on each device, which means faster deployment, lower overhead, and no endpoint maintenance.
- Agent-based discovery via the Discovery Agent installs lightweight agents on Windows, macOS, and Linux devices. These agents report asset data on recurring scheduled scans, giving deeper visibility into configuration changes and software inventory.
- Work from Anywhere (WFA) support — The Windows Discovery Agent tracks configurations on remote endpoints, so assets remain visible regardless of where employees connect from.
[ Read also: Agent-based vs. agentless discovery: which is best for your business? ]
How do you identify unauthorized devices on a network?
Unauthorized devices typically appear when someone connects personal hardware, spins up an unapproved cloud instance, or plugs in networking equipment without IT knowledge. Automated discovery catches these by scanning subnets on a recurring schedule and comparing results against your known asset inventory in the CMDB. Any device that shows up in a scan but doesn’t match a known configuration item (CI) gets flagged for review. Agentless scanning is particularly effective here because it finds devices that were never registered, precisely because no agent was installed on them.
What role does a CMDB play in security gap analysis?
A CMDB is the single source of truth for your IT environment — every asset, relationship, and configuration attribute in one place. Without it, security analysis relies on incomplete spreadsheets and tribal knowledge.
For security gap analysis, the CMDB answers three questions that matter:
- What do we have? Every discovered asset is recorded as a configuration item with its attributes: OS version, installed patches, owner, and location.
- What depends on what? Dependency relationships show how a vulnerability in one system can cascade. A compromised database server isn’t just one risk — it’s every application that depends on it.
- What’s changed? Every CI update is versioned with a full audit history. When a configuration changes between scans, your team can see exactly what shifted — and whether that change was authorized.
Virima’s CMDB is populated directly by its discovery engine. CI data reflects the actual infrastructure state from the most recent scan, not what someone entered manually six months ago. This attribute authority is what makes security gap analysis reliable. Virima is also SOC 2 Type II certified, which means the platform itself meets the same audit standards your team is working toward.
How dependency mapping strengthens incident response
When a security incident hits, your team needs to know the blast radius immediately. Which services are affected? Which teams own those services? What’s the downstream impact?
Service mapping and ViVID™ (Virima Visual Impact Display) provide this context. ViVID™ renders dependency relationships visually, so when a compromised asset is identified, your team can see every connected service, application, and infrastructure component without digging through spreadsheets or Visio diagrams.
This turns incident response from a guessing game into a structured process. Instead of manually tracing connections during an outage, your team already has the dependency map and can isolate the threat, assess impact, and communicate scope to stakeholders within minutes.
Enhancing system security through ITSM automation
While ITAM identifies what’s vulnerable, ITSM automation handles what happens next. Virima integrates with ITSM platforms like ServiceNow, Jira Service Management, Ivanti, and HaloITSM, so incident management, change management, and problem resolution workflows are all connected to your discovery and CMDB data. Virima’s ITSM holds PinkVERIFY ITIL 4 certification across six processes — SACM, change, incident, problem, request fulfillment, and knowledge management — which means these aren’t loosely defined workflows. They follow the same ITIL framework your team is already measured against. That connection is what closes security gaps before they’re exploited.
An automated ITSM system ensures that every incident, security-related or not, is recorded, tracked, and resolved with a consistent workflow. Patterns emerge: repeated alerts from the same subnet, recurring configuration changes on a specific server, or escalations tied to a particular application. These patterns are early indicators of security gaps your team can address proactively.
How does change management reduce security risk?
Unauthorized or poorly managed changes are one of the most common causes of security incidents. A developer modifies a firewall rule without approval. A sysadmin updates a production server configuration outside the change window. These uncontrolled changes introduce vulnerabilities.
Whether you’re running Virima’s native ITSM or integrating with platforms like ServiceNow or Jira Service Management, the workflow stays the same: every change request is logged, reviewed, and tied to the affected CIs in the CMDB. If a proposed change impacts a critical service — visible through ViVID™ dependency maps — the change advisory board sees that risk before approving. This process doesn’t just prevent unauthorized changes. Every CI update is versioned in the CMDB, and every change request is logged in ITSM — together, that’s the audit trail your compliance team needs when auditors ask “who changed what, when, and why.”
Close your security gaps before auditors find them
Security gaps don’t announce themselves. They hide in forgotten assets, stale CMDB records, undocumented dependencies, and uncontrolled changes. The organizations that close these gaps consistently are the ones with automated discovery feeding an accurate CMDB, dependency visibility through service mapping, and structured ITSM workflows enforcing change control.
Virima ties discovery, CMDB, asset management, service mapping, and ITSM workflows into one platform so your team doesn’t have to stitch together five different tools to get from “what’s exposed” to “it’s been fixed.”
Find out more about how Virima can help by requesting a demo right away.






