Everything You Must Know About National Vulnerability Database Integration
Keeping your IT infrastructure secure starts with knowing where the risks are. According to IBM, the global average cost of a data breach reached $4.45 million in 2023. Importing data from the NIST National Vulnerability Database (NVD) into your CMDB gives your team a direct line to the latest vulnerability intelligence.
The NVD recorded over 28,000 vulnerabilities in 2023 alone, matched to the assets you actually manage. For teams juggling patching, compliance, and uptime, this connection removes the guesswork from vulnerability tracking.
The NVD provides detailed information about security vulnerabilities, including severity ratings, Common Vulnerability Scoring System, affected systems, and links to vendor patches. Pulling this data into your IT Asset Management workflow supports security measurement and compliance, keeps your environment current with the latest fixes, and reduces your exposure to known threats.
Here is what the National Vulnerability Database is, how integration works in practice, and how to use it to strengthen your vulnerability management program.
What is the National Vulnerability Database (NVD)?
The National Vulnerability Database (NVD) is a publicly available repository of standards-based known software vulnerabilities. The National Institute of Standards and Technology (NIST) maintains it, and new entries are added daily.
The NVD assigns each vulnerability a Common Vulnerabilities and Exposures (CVE) identifier. CVE IDs have been the standard reference for vulnerability tracking since 1999. Each CVE entry describes a specific flaw in a software product, lists affected versions, and links to available patches.
NIST manages the database, while MITRE acts as the primary CVE Numbering Authority (CNA). Other vendors, researchers, and third-party coordinators also contribute to CVE assignments. The database only includes vulnerabilities that have been publicly disclosed, similar to other databases of security intelligence, so it does not track every possible flaw in every product.
What is Common Platform Enumeration (CPE)?
CPE is a standardized naming scheme for IT products, maintained alongside the NVD. Each CPE identifier maps to a specific software product, version, and platform. When the NVD publishes a CVE, it includes CPE data that tells you exactly which products and versions are affected.
That CPE mapping helps enable automated vulnerability matching work: your asset inventory records products as CPE entries, and incoming CVEs match against them without manual effort.
How NVD integration supports vulnerability programs
Vulnerability management means finding and fixing security flaws across your IT environment through a standards-based vulnerability management approach before attackers exploit them.
Effective vulnerability management and vulnerability management security measurement depend on two things: a complete picture of what assets you have, and a reliable feed of current threat data. NVD integration handles the second part by connecting your asset records to the vulnerability management data and vulnerability disclosures as they are published.
How does IT asset discovery help with vulnerability management?
You cannot protect assets you do not know about. IT discovery uses over 140 extendable probes to scan your network through agentless IP-based scanning or optional agents for Windows, macOS, and Linux. The result is a complete inventory of hardware, software, operating systems, and their configurations. Without that foundation, vulnerability data from the NVD has nothing to match against.
Automated discovery closes visibility gaps that manual inventories miss, catching devices that fall outside routine inventory processes, endpoints with outdated configurations, and assets in remote or edge locations. Those are the spots where unpatched vulnerabilities tend to sit unnoticed. Running discovery alongside NVD integration means every asset gets checked against the latest threat data as soon as it appears.
What are the benefits of automating NVD vulnerability scanning?
Manual vulnerability tracking does not scale. New CVEs come out daily, and matching each one against your asset inventory by hand is slow and riddled with errors.
Automated NVD scanning fixes this problem:
- New CVEs and CPE identifiers are pulled as soon as they are published
- Each one is matched against your asset inventory without manual lookup
- Affected assets are flagged immediately
- Vulnerability data stays current without tying up staff time
The shift moves your team from running periodic audits to maintaining continuous vulnerability awareness. Staff time goes to fixing issues, not hunting for them.
What does NVD integration mean for your IT assets?
The threat landscape shifts fast. New vulnerability types emerge constantly, and your exposure to flaws in open-source components may not be visible to your developers, particularly through transitive dependencies they never chose directly.
NVD integration gives you a reliable way to track these risks. You search your own asset records for known vulnerabilities, where this data enables results matched to your specific software versions to your specific software versions, rather than checking the NVD website yourself.
Connecting your IT assets to the National Vulnerability Database lets you:
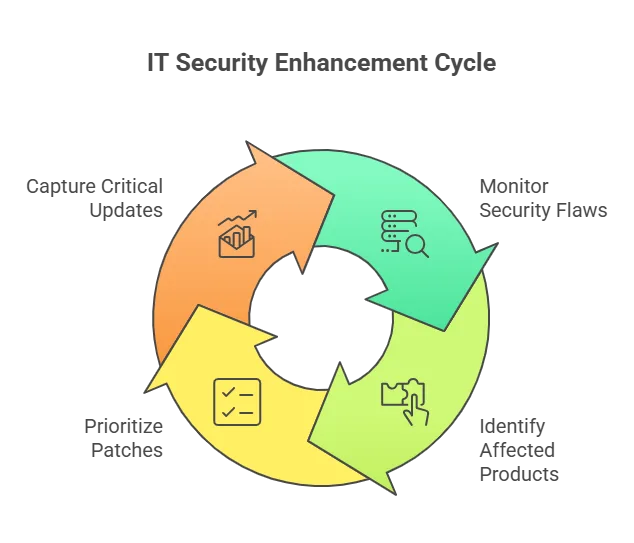
- Monitor security flaws mapped to your actual environment
- See which products and versions are affected by each CVE
- Rank patches based on severity and business impact
- Catch updates that would otherwise fall through the cracks
How does NVD integration work with a CMDB?
A CMDB stores configuration items (CIs) that represent your IT assets, including the software they run. When NVD data feeds into your CMDB, each new CVE is matched against the CPE records attached to your CIs.
The result is a vulnerability-aware asset register. Asset management and vulnerability management run through the same system rather than as separate workflows. Your team sees which CIs are affected, checks upstream and downstream dependencies between configuration items, and decides where to patch first, all in one place. For teams responsible for both change management and security, that single view cuts the coordination overhead significantly.
That CMDB-to-ITSM connection matters because Virima integrates with platforms like ServiceNow, Jira Service Management, HaloITSM, Ivanti, Cherwell, Xurrent, and Hornbill. When a vulnerability is flagged on a critical CI, the next step is often a change ticket or an incident record. With automatic two-way syncing to leading ITSM platforms, vulnerability findings move straight into your existing remediation workflows without switching tools.
How Virima connects National Vulnerability Database data to your workflow
Virima’s IT discovery solution includes NVD integration at no additional cost. Once connected, your NVD feed automatically checks for newly published CVEs and CPE identifiers against your asset inventory. No manual updates needed.
This integration sits within Virima’s broader IT Asset Management framework, which tracks each asset’s lifecycle status, ownership, and license compliance alongside its vulnerability exposure. Discovered assets carry CPE data from the start, so every new CVE is matched against your inventory on the next scheduled scan. Combined with Virima’s CMDB, you get a single view of which configuration items carry known vulnerabilities and how they connect to everything else in your environment.
How does service mapping help with vulnerability prioritization?
Not every vulnerability carries the same business risk. A critical CVE on an isolated test server matters far less than a moderate one sitting on a database that feeds your customer-facing application.
Virima Visual Impact Display (ViVID™) uses Application Dependency Mapping (ADM) to map dependencies between services, applications, and infrastructure components. When a vulnerability hits a specific asset, ViVID™ shows you which business services depend on it. Each asset carries a Service Value Rating (SVR) based on its role in supporting business services, so your team can rank remediation by actual business impact rather than relying on CVSS scores alone.
Service mapping added to your vulnerability workflow turns severity ratings into real priorities. You see the downstream impact of each vulnerability, and ViVID™ overlays open incidents and pending changes onto those same maps so your team can coordinate remediation across a single view. You address the highest-risk issues first with full context on what is already in progress.
Ready to see how Virima ties National Vulnerability Database integration, IT discovery, and service mapping into a single workflow? Request a demo today.