Guide for choosing the right network asset discovery tool
Introduction
As part of the IT team, how often are you asked what assets are present on your network? As somebody responsible for finding, tracking, and monitoring the usage of assets on your network, our guess? Far too often. A network asset discovery tool is an essential solution that helps organizations identify, map, and manage all IT assets across their network.
However, this can be a big and tiring job. This is especially true if you work in a large organization with many assets on its network. This is where the network asset discovery process comes into the picture.
This process also helps you identify and monitor all the assets within your network at all times—manually or automatically. In either case, it’s an essential aspect of IT infrastructure management.
Analysts expect the Global Software Asset Management Market to reach $5.4 billion by 2027. This shows a growth rate of 17.3% each year during this time.
Summary
A network asset discovery tool automates the process of IT asset discovery, generating a real-time inventory of devices, software, and services. Moreover, they play a critical role in:
- Network mapping
- CMDB automation
- Comprehensive asset inventory management
Without such a tool, manually tracking hundreds or thousands of endpoints becomes unsustainable, especially in remote or hybrid environments. In this article, we will talk about network asset discovery. We will also explain how it works and how businesses can benefit from it.
What is network asset discovery?
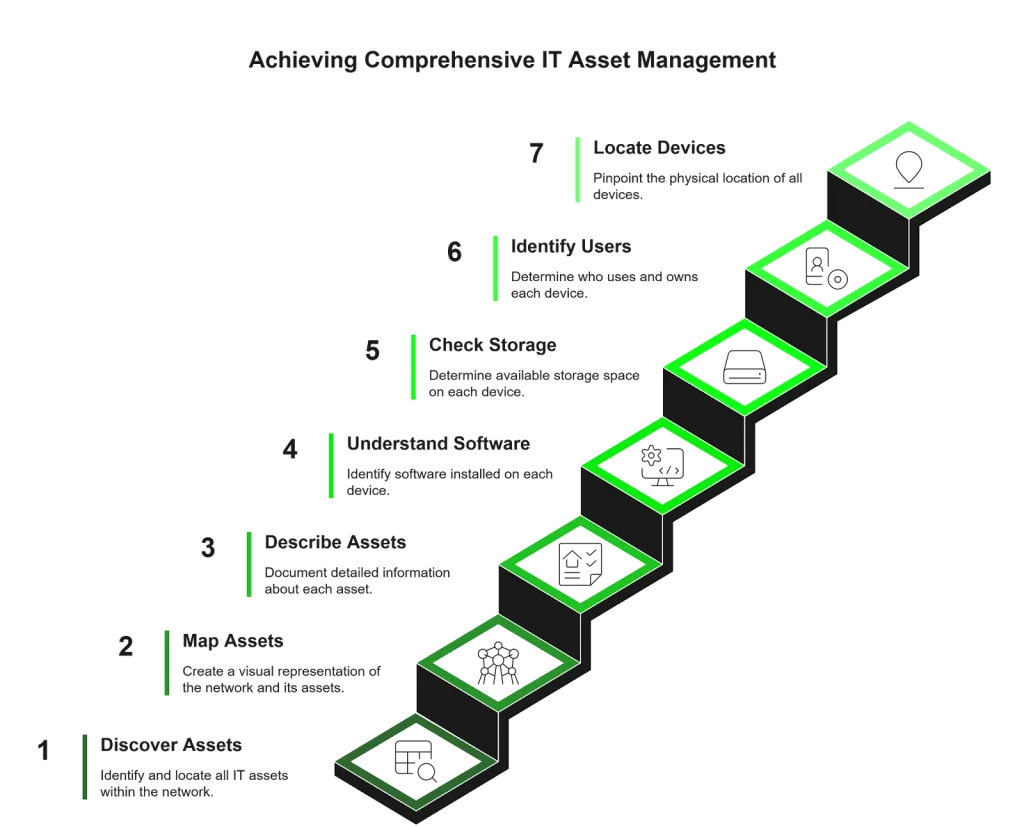
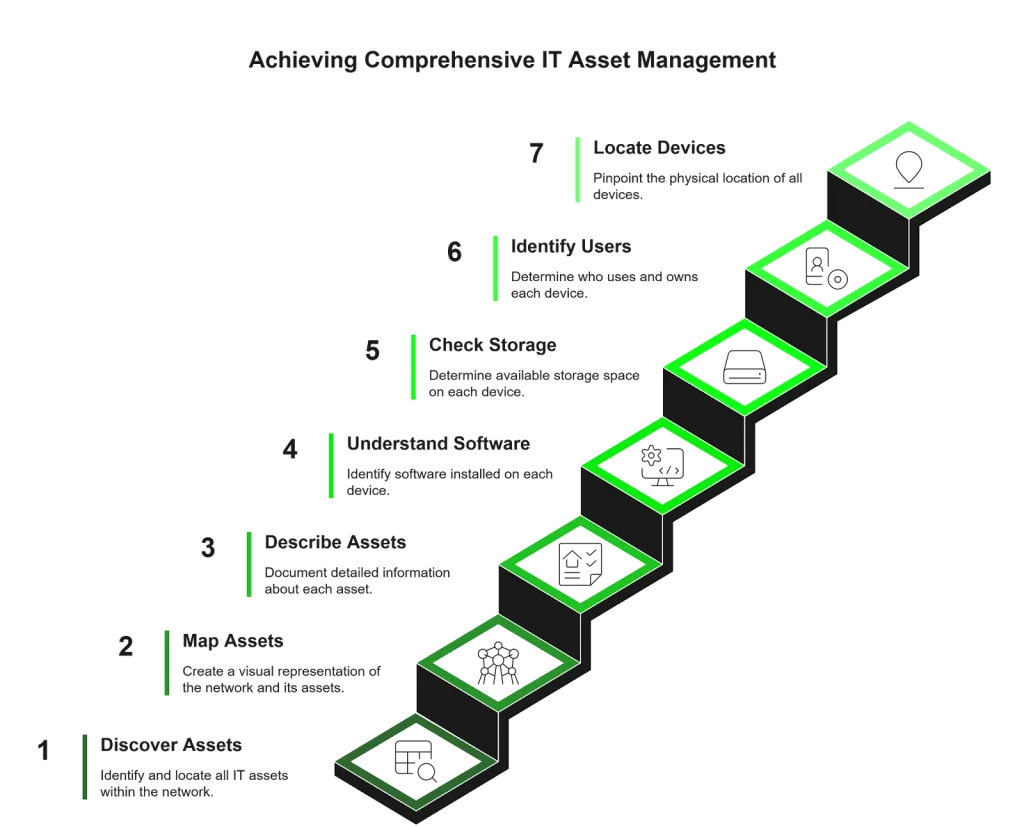
Network asset discovery is the process of discovering, mapping, and describing all of your IT assets.
It is a key part of any IT management plan. It also gives a clear list of all your assets. This process can often be conducted using an asset discovery tool.
Network asset discovery for ITAM
Asset discovery tools can also help you understand:
- What software is installed on each device
- How much storage space is available
- Who uses and owns each device
- Where all your devices are located
This information is valuable for identifying problems within your network environment. It can further help you make smart choices about future purchases or upgrades based on facts, not guesses.
You can also perform this process manually. It is often better to use an automated tool. This tool can quickly gather all important information and further show it in a clear format.
Why is network asset discovery needed?
Network asset discovery is foundational to managing a secure, compliant, and efficient IT infrastructure.
Here’s why your organization needs it:
- Visibility & control: Complete insight into all network-connected assets, including unauthorized or unknown mobile devices.
- Security & compliance: Identify vulnerabilities, detect shadow IT, and subsequently maintain software license compliance.
- Performance monitoring: Monitor device health and usage to proactively prevent downtime.
- Operational efficiency: Reduce manual tracking and keep your CMDB consistently accurate.
Challenges of managing software assets
Before we learn how network asset discovery works, let’s first understand why it is important.
Here is a list of challenges of tracking and managing software assets within your network:
Lack of visibility into the entire IT infrastructure
It helps IT teams see their whole infrastructure. They can understand what assets are on their network. Moreover, it will enable the team to preserve, protect, and identify devices critical to business operations.
For example, remote work is now common. Employees often connect multiple devices that may not belong to the company. It is also important to keep track of these assets. Ignoring them could lead to security and compliance problems later.
This process will show when someone last upgraded or replaced devices. This asset information is useful for keeping track of the asset inventory.
Also, this process will indicate when devices were last upgraded or changed out, which is helpful if you’re maintaining the asset inventory.
Regular asset failure leads to a longer downtime duration
It is easy to underestimate how complex network infrastructure is, especially when functioning correctly. When something goes wrong with even one operating system component, it can cause a chain reaction that affects the entire network. It is particularly true for highly distributed environments and spans multiple locations, such as cloud infrastructure or data centers.
In 2020, 25% of respondents worldwide reported that their servers’ average hourly downtime costs between $301,000 and $400,000. So, a longer downtime duration could result in a loss of millions of dollars.
Unnecessary disruptions to IT services
Managing a network with hundreds of devices can be a challenging process. There are several reasons why this can happen:
- Lack of processes to manage these assets
- No dedicated network asset discovery tools are in place
- No clear separation of monitoring duties
- Lack of a security structure
If you do not have a system in place, it can cause regular service disruptions. This leads to frustrating experiences for both employees and customers.
Applications and programs freeze often
The most common cause of system downtime is a malfunctioning component within a network infrastructure. The discovery of network issues often involves troubleshooting by IT personnel, which can be time-consuming and expensive.
No matter how well a company plans, one or more servers may fail. Subsequently, this can stop them from working properly. It can happen to any system regardless of whether it is an integral part of an organization’s operations. Plus, it’s unrealistic to physically visit each server to run tests every single time this happens.
Increasing costs of using and managing IT assets
In today’s businesses, computers and network devices run various processes. A failure in any of them can further lead to a loss of valuable data, irrecoverable documents, or incomplete work. Employees must deal with the issues and breakdowns if a computer is offline.
The same is true of faulty network equipment. Likewise, the number of working computers and other assets will affect the company’s employee productivity.
When something breaks down in a small office, it takes the IT staff quite some time to find out what failed and why it went wrong. Hardware issues are not always clear-cut. Sometimes an outdated device or software can malfunction or crash because of a virus. In some cases, users also need to restart it after not using it for too long.
How does a network asset discovery tool work?
Network asset discovery tools operate using either agent-based or agentless methods:
- Agent-based discovery: Deploys small agents on endpoints to collect detailed software and hardware data.
- Agentless discovery: Leverages SNMP, SSH, WMI, or APIs to remotely gather information without installation.
Network asset discovery methods
Most modern solutions offer hybrid capabilities, using both methods for broader visibility. Discovery processes often include:
- IP range and port scanning
- MAC address detection
- Credential-based authentication
Collected data is then centralized and visualized for real-time network mapping and CMDB updates.
Benefits of network asset discovery
There are several benefits of implementing network asset discovery processes within your organization.
A strong IT discovery tool delivers strategic advantages across security, compliance, and operations:
- Enhanced security
- Detects unauthorized devices and rogue applications
- Identifies outdated software and firmware
- Prevents malware from spreading across devices
- Regulatory compliance
- Tracks software licenses for audit readiness
- Highlights non-compliant or unapproved assets
- Supports HIPAA, GDPR, SOX, and other regulations
- Cost optimization
- Finds underused or redundant assets
- Reduces overspending on software or hardware
- Improves planning for future IT investments
- CMDB accuracy & automation
- Auto-updates the CMDB with asset changes
- Eliminates manual data entry errors
- Business continuity:
- Flags potential system failures before outages occur
- Enables rapid incident resolution with real-time data
- Informed decision-making
- Provides data to support procurement and lifecycle strategies
- Helps assess software utilization and ROI
Key takeaways: Benefits of network asset discovery
How to choose a network asset discovery tool
Follow this framework to evaluate the best-fit tool for your environment:
- Discovery scope:
- Supports on-premises, cloud based, hybrid, and virtual systems
- Detects BYOD, IoT, and remote devices
- Automation & CMDB integration:
- Offers automated syncing with CMDB
- Customizable workflows and scheduled reporting
- Security features:
- Encrypts credentials and enforces access control
- Protects sensitive data throughout the discovery process
- Agent-based/Agentless flexibility:
- Provides both options for different environments
- Suitable for regulated or high-latency settings
- Ease of use & reporting:
- Clean, intuitive dashboard with real-time visibility
- Automated as well as exportable report generation
- Scalability & cost:
- Can scale to enterprise-level infrastructures
- Transparent pricing with long-term value
Top features to look for in a network asset discovery tool
When comparing network asset discovery tools, prioritize these features:
- Real-time asset discovery
- Interactive network mapping
- CMDB integration and automation
- Software license tracking
- Unauthorized device detection
- Role-based access controls
- Multi-environment (cloud, edge, on-prem) support
- Customizable as well as exportable reports
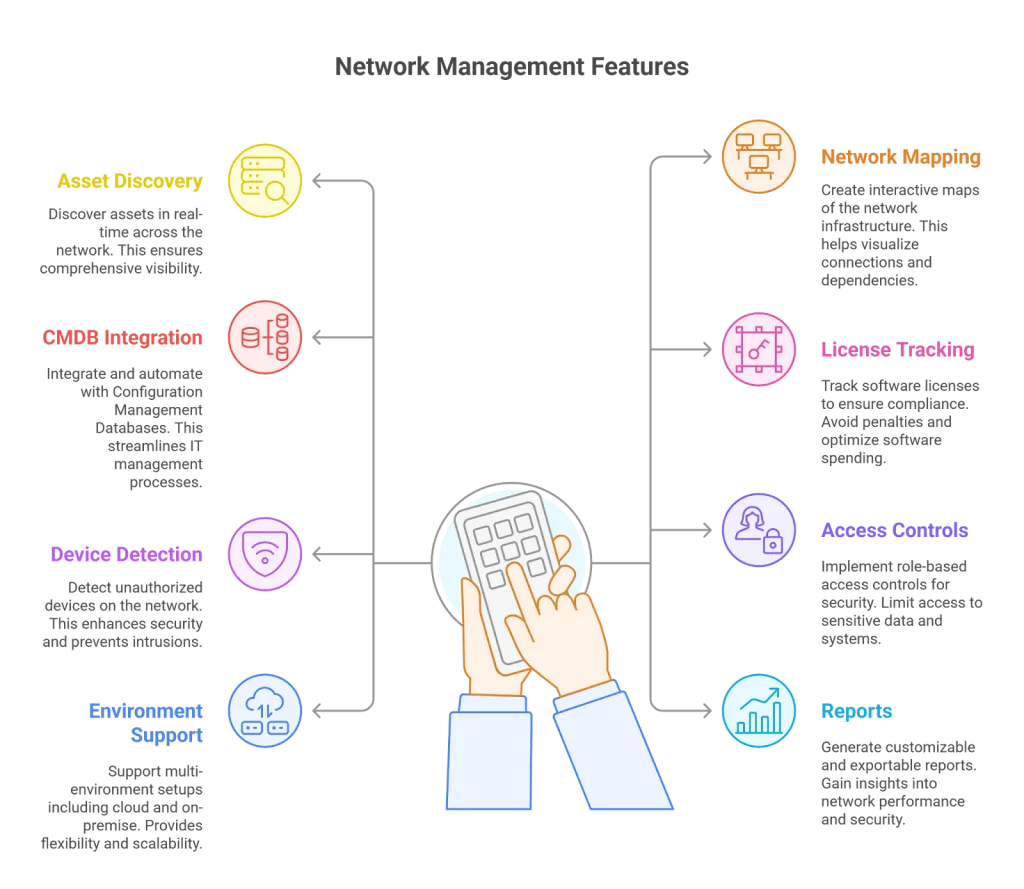
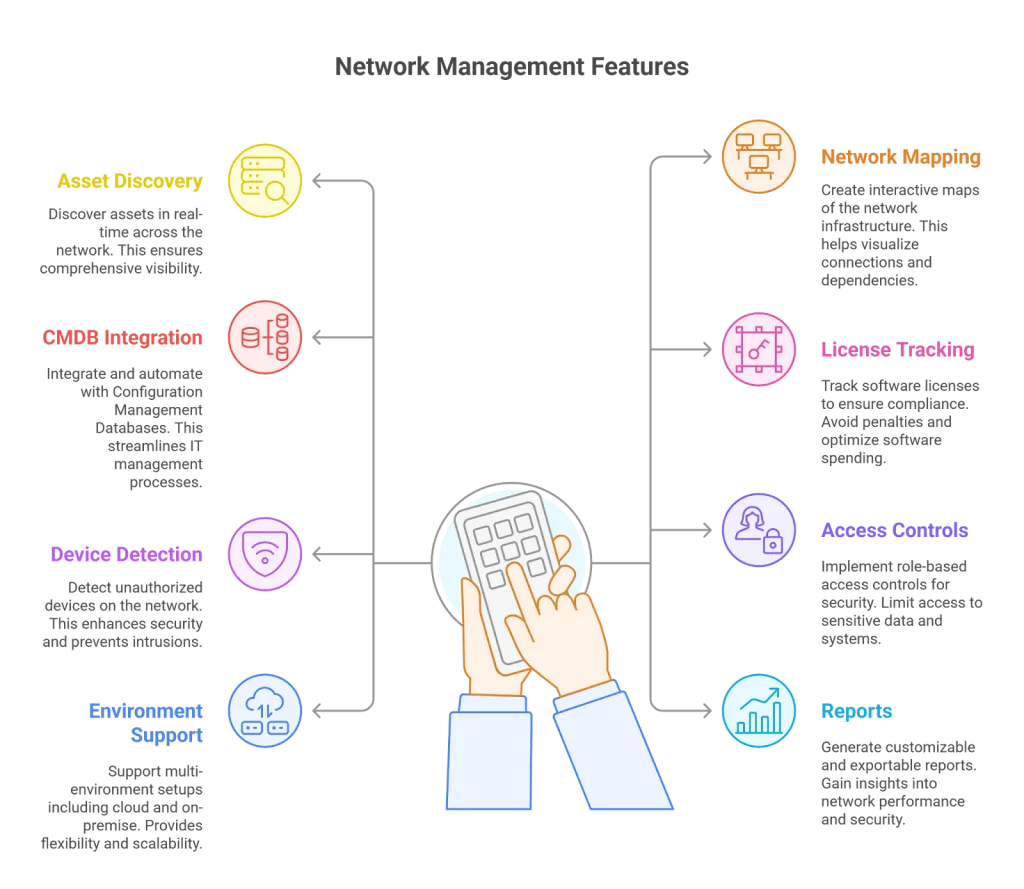
Network asset discovery tool features
Which network asset discovery tools are available?
Several tools dominate this space, each offering distinct capabilities:
- Virima: Offers a unified solution for both agent-based and agentless discovery. Moreover, with dynamic visualizations, secure scanning, and native CMDB synchronization, Virima excels in environments requiring strong governance and scalability. It’s especially suitable for hybrid infrastructures and supports detailed asset context, including vendor, model, and serial number.
- Lansweeper: Specializes in asset inventory and hardware/software discovery with minimal configuration. Its strength is in deep scanning and wide compatibility. Ultimately, this makes it a good choice for businesses that want quick deployment and a central view of discovered assets.
- ManageEngine AssetExplorer: An IT asset management (ITAM) platform that includes built-in network discovery. It also connects with service desks and purchase workflows. Overall, this makes it great for organizations that want asset discovery in their ITSM strategy.
- SolarWinds Network Performance Monitor: While primarily a network health monitoring tool, it includes robust discovery features. It further gives real-time alerts, performance metrics, and easy-to-use dashboards. Subsequently, this is perfect for teams that need visibility and uptime in large, complex networks.
Manage your network infrastructure with Virima
Managing a complex IT infrastructure without complete visibility can lead to downtime, compliance violations, and operational inefficiencies. That’s where Virima’s network asset discovery tool stands out.


Virima’s network asset discovery tool
Virima offers a strong, flexible, and safe discovery solution. It helps make your asset inventory process easier. It also keeps your network mapping current and automates CMDB updates.
Key capabilities include:
- Secure agent-based and agentless scanning: Adjust to any environment with flexible ways to find information. This also applies to endpoints, data centers, and the cloud.
- Near real-time asset visibility: Quickly find hardware and software on the network. Moreover, get useful details like who owns the device, how it is used, and its settings.
- End-to-end encryption and access control: Protect sensitive data and credentials throughout the discovery as well as the reporting lifecycle.
- Intelligent alerts and dashboards: Continuously monitor critical IT assets and flag anomalies to minimize downtime and further accelerate response times.
- Automatic synchronization with CMDB: Ensure your configuration database remains accurate without the burden of manual updates.
Virima works well with your current ITSM and infrastructure management systems. Plus, it helps IT teams manage risk, improve performance, and support business growth.
If you’re ready to enhance IT visibility, security, and efficiency, schedule a demo with Virima today.
Frequently Asked Questions (FAQs)
Do we really need a network asset discovery tool if we already have a CMDB?
Yes. A CMDB is only as accurate as the data fed into it. Without an automated discovery tool, your CMDB can quickly become outdated or incomplete. A network asset discovery tool further ensures that asset data remains fresh, accurate, and comprehensive by continuously scanning and updating the CMDB in real time.
How often should discovery scans be scheduled?
It depends on your environment, but most organizations benefit from running discovery scans at least daily or weekly. High-change environments (e.g., cloud-first organizations or enterprises with frequent deployments) may require real-time or near-real-time scanning to maintain accuracy and security.
Can network asset discovery tools detect shadow IT or rogue devices?
Absolutely. One of the key benefits of these tools is their ability to detect unauthorized or unknown devices on the network—providing the visibility needed to address security risks before they escalate.
Are these tools only for large enterprises?
Not at all. While enterprises benefit from scalability, small and mid-sized businesses can also gain immense value from automated discovery—especially in reducing manual tracking, ensuring license compliance, and preventing costly mistakes.
How do these tools support compliance efforts?
Discovery tools help identify and track licensed versus unlicensed software, detect unauthorized hardware, and log changes over time. These capabilities support audit readiness and help align with standards like HIPAA, GDPR, and SOX.
What’s the difference between agent-based and agentless discovery again?
Agent-based discovery installs software on endpoints for deep insights, while agentless discovery uses protocols like SNMP or WMI to scan devices remotely without software installation. Many tools, including Virima, offer both for flexible coverage.
Can asset discovery reduce IT costs?
Yes. By identifying redundant assets, underused licenses, and unnecessary purchases, these tools help cut operational costs and optimize IT spending.