ServiceNow configuration items (CIs) and configuration management in ServiceNow CMDB: A step-by-step guide
In 2025, misconfigurations remained the top cause of enterprise security and service failures.
The Cloud Security Alliance’s 2025 SaaS Security Survey found that 43% of organizations experienced a SaaS breach caused by misconfigured settings. Not zero-days. Not advanced attacks. Basic configuration drift that went unnoticed.
This isn’t just a security problem.
It’s a configuration management problem rooted in poor visibility across service management processes.
When configuration items (CIs) are outdated, duplicated, or poorly related, the CMDB stops being a system of record. Impact analysis becomes guesswork. Incident management and change management slow down. Incident response relies on tribal knowledge instead of data — making it harder to support IT services effectively.
Configuration management exists to prevent this exact failure mode. It helps organizations reduce risk through better control over what exists in their environment and how it connects.
At the center of configuration management are CIs and the relationships between them. If that foundation is weak, no amount of process or tooling on top will fix it.
Understanding the ServiceNow CMDB and configuration items
What is the ServiceNow CMDB?
The ServiceNow CMDB (Configuration Management Database) is a centralized system that stores configuration items and the relationships between them. It gives teams a shared view of how IT components connect, so they can assess impact, resolve incidents faster, and manage change with confidence.
That definition sounds straightforward. In practice, this is where many organizations struggle. The CMDB only works when its data is accurate, current, and trusted. Otherwise, teams stop using it, and its value drops quickly across service delivery workflows.
What are configuration items (CIs)?
A configuration item is anything you need to manage and track to deliver an IT service.
That can include:
- Physical infrastructure like servers and network components
- Software such as applications, databases, and middleware
- Cloud resources from AWS, Azure, or SaaS platforms
- Logical components like users, groups, and service accounts
- Higher-level constructs such as business or technical services
In ServiceNow, CIs are sometimes called objects. The name varies, but the intent stays the same.
A CI represents something that:
- Exists in your environment
- Changes over time
- Has an operational impact when it fails or is modified
Not everything tracked in IT qualifies as a CI. The distinction matters because it shapes what belongs in your CMDB and what doesn’t.
Want to know more? Read here: What is a configuration item?
CI vs asset: understanding the difference
Assets belong to IT Asset Management, focusing on financial and ownership tracking — purchase cost, depreciation, and lifecycle value. CIs focus on operational impact: dependencies, changes, and outages.
A laptop, for example, may exist as an asset for financial reporting and as a CI because it supports a user or application. Both records matter. They serve different purposes.
The lifecycle of a CI in ServiceNow
Unlike assets, CIs follow an operational lifecycle. Most CIs move through stages such as:
- Create – The CI is discovered or manually added
- Deploy – It becomes active in the environment
- Operate – It supports one or more services
- Change – It is patched, upgraded, or reconfigured
- Retire – It is decommissioned and no longer in use
When lifecycle states are unclear, CI data quickly becomes stale. A server decommissioned three months ago still shows as active. A change advisory board reviews impact analysis against CIs that no longer exist. Consistent lifecycle management — tracking each CI from creation through retirement — prevents this drift and makes audit preparation faster.
Why CIs matter in day-to-day operations
CIs play a direct role in incident triage and root cause analysis, change impact assessments, problem investigations, service mapping and dependency analysis, and security and risk assessments.
When CI data is accurate, teams move faster and with more confidence. When it isn’t, they fall back on spreadsheets, screenshots, and tribal knowledge.
Analyst research consistently shows that CMDBs with poor data quality are underused in incident and change processes. Teams end up running manual validation instead of trusting automated impact analysis. If teams don’t trust the CMDB, they stop using it. That’s why defining and managing CIs correctly is foundational — not optional.
Where CMDBs deliver value and where they struggle
When the CMDB works
At a basic level, the ServiceNow CMDB stores CI records and their attributes, maintains relationships between CIs, and shows how components depend on one another.
But storing data isn’t enough. The CMDB becomes valuable only when CI records are continuously updated, relationships reflect reality, ownership and standards are clearly defined, and data is actively used in ITSM or ITOM workflows. When those conditions aren’t met, the CMDB goes stale quickly and teams lose trust.
Where implementations break down
Most organizations don’t fail at creating a CMDB. They fail at maintaining it. Common issues include duplicate CIs, stale records that no longer exist, misclassified CI types, and missing or broken relationships.
These problems don’t appear overnight. They build up slowly until the CMDB is no longer reliable. Gartner has reported that only 25% of organizations get meaningful value from their CMDBs, citing manual maintenance, unidentified assets driving security incidents, and rapidly outdated inventory data as the main culprits.
The good news: these issues are fixable. But before fixing them, you need to understand how CIs are defined, normalized, and related inside ServiceNow.
Defining and managing CIs in ServiceNow CMDB
Once you understand what a CI is, the next challenge is managing it properly. This is where many CMDB initiatives start to drift. Not because teams don’t add CIs — but because they add them without clear structure, standards, or ownership.
Defining a CI in ServiceNow
Every CI in ServiceNow is represented by a record. That record describes what the CI is, how it behaves, and how it connects to other components in your environment.
At a minimum, a CI definition includes:
- A CI class (for example, server, application, database)
- Core attributes such as name, status, and environment
- Lifecycle information
- Relationships to other CIs
The goal isn’t to capture everything. It’s to capture what matters operationally. If a field isn’t used for decision-making, reporting, or automation, it probably doesn’t belong in your CI model.
Choosing the right CI class
ServiceNow provides a rich CI class hierarchy out of the box. While this flexibility is helpful, it can also lead to inconsistency if left unchecked. For example, the same application might be created as an application CI by one team, a software CI by another, and a custom CI class by a third party.
Over time, this makes reporting, impact analysis, and automation unreliable.
To avoid this:
- Use standard CI classes wherever possible
- Align CI classes to your service model
- Document when and why custom classes are allowed
CI attributes and normalization
Attributes describe the characteristics of a CI: identification details (name, serial number, hostname), operational data (status, environment, owner), and technical details (OS version, IP address, cloud region).
Focus on attributes required for reconciliation, used in workflows or reports, and needed for compliance or audit. Fewer, well-governed attributes are far more valuable than dozens of unused fields.
CI data comes from multiple sources — manual entry, IT discovery tools, integrations. Naming and formatting inconsistencies are inevitable. Normalization ensures CI names follow consistent patterns, manufacturers and versions are standardized, and duplicate records are easier to spot. Without normalization, the CMDB slowly fills with near-duplicates that erode trust.
Managing CI relationships
If CIs are the building blocks, relationships are what give the CMDB its real value. Relationships show how one CI depends on another. An application runs on a server. A database supports that application. A business service depends on all of them.
ServiceNow supports many-to-many relationships, allowing complex dependency modeling. However, more relationships aren’t always better. What matters is accuracy over volume, relationships that support impact analysis, and clear directionality — what depends on what.
Missing or incorrect relationships are one of the most common reasons CMDBs fail during change and incident reviews. When a network switch goes down at 2 AM, the team needs to know immediately which services sit downstream. If that relationship data doesn’t exist, they’re guessing.
Applications often rely on shared databases, middleware, or cloud services. These many-to-many relationships are critical for understanding blast radius during incidents or changes. The key is to model relationships based on how failures propagate, not just how systems are built.
Relationships can be created manually (through the CI record), automatically (through discovery tools), via integrations and imports, or through service mapping. Manual relationships don’t scale. Automated relationships are more reliable, but only when discovery is accurate.
Common mistakes when defining CIs
A few patterns that cause long-term issues: creating too many CI classes too early, treating CI attributes as optional, ignoring normalization rules, focusing on CI count instead of relationship quality, and relying heavily on manual updates.
These problems surface months later when teams start questioning CMDB accuracy. And once trust is lost, it’s hard to regain.
Case: Building CMDB trust with quick wins (Wesleyan University)
Wesleyan University built a functioning CMDB without dedicated CMDB staff by focusing on quick wins and steady adoption. The CMDB gained traction once they automated repetitive entry and made dependency information accessible in one place. They also added asset refresh and replacement timelines, feeding directly into budget projections. Over time, their CMDB became an operational backbone powering their service catalog.
CMDB capabilities, CSDM, and ITIL alignment
Relationship and dependency mapping
The CMDB doesn’t just store CIs — it connects them. Relationships show how components depend on one another: which servers host an application, which databases support it, and which services rely on those components.
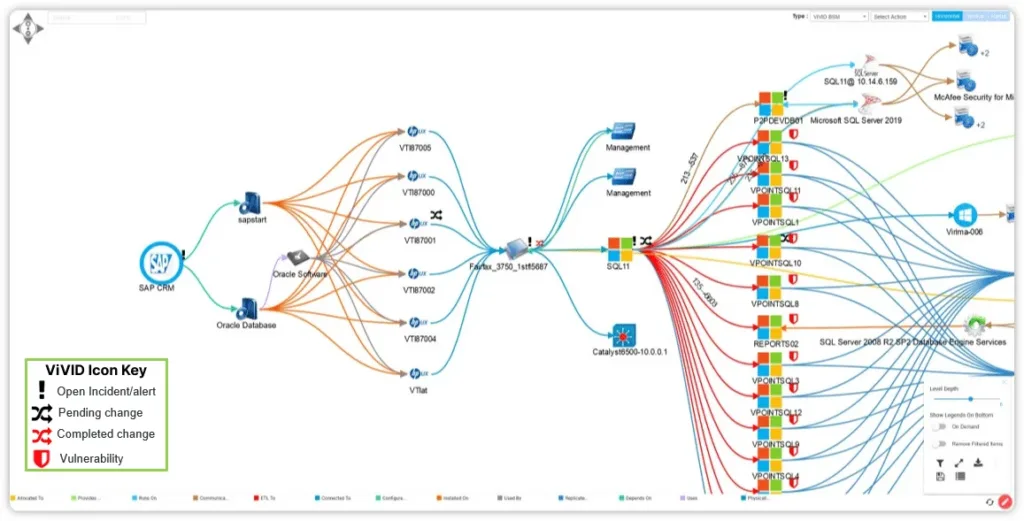
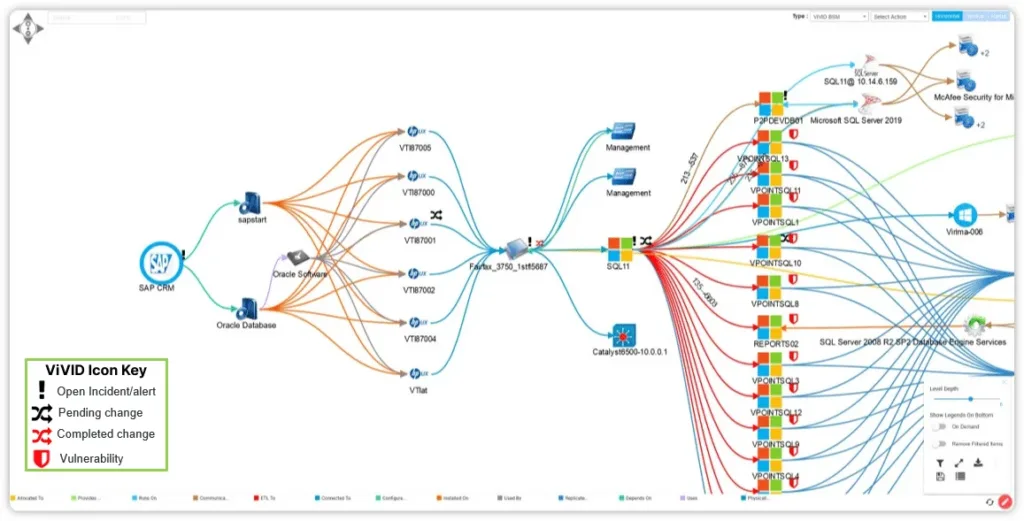
Virima’s ViVID™ service mapping takes this further by visualizing these relationships with real-time overlays for open incidents, recent changes, and pending changes — so teams see operational context on top of the dependency map, not just a static diagram.
This relationship data powers change impact analysis, faster incident resolution, and more accurate root cause analysis. Without relationships, the CMDB becomes little more than an inventory list.
Impact analysis and ITSM workflows
When a change is proposed or an incident occurs, teams need to answer one key question quickly: What else could this affect?
With accurate CI and relationship data, ServiceNow can highlight upstream and downstream dependencies, surface affected services and users, and reduce guesswork during CAB reviews. When this data is missing or outdated, teams fall back on manual checks — which slows everything down.
Accurate CI data also improves incident management and prioritization, change management risk scoring, problem investigations, and service mapping health dashboards. CMDB quality directly influences the quality of your ITSM outcomes. If incidents take too long to resolve or changes fail unexpectedly, the CMDB is often a root cause.
CMDB health and data quality
ServiceNow includes built-in tools to assess CMDB health — monitoring completeness of CI records, correctness of CI attributes, and compliance with modeling standards. Health dashboards don’t fix problems on their own, but they make issues visible.
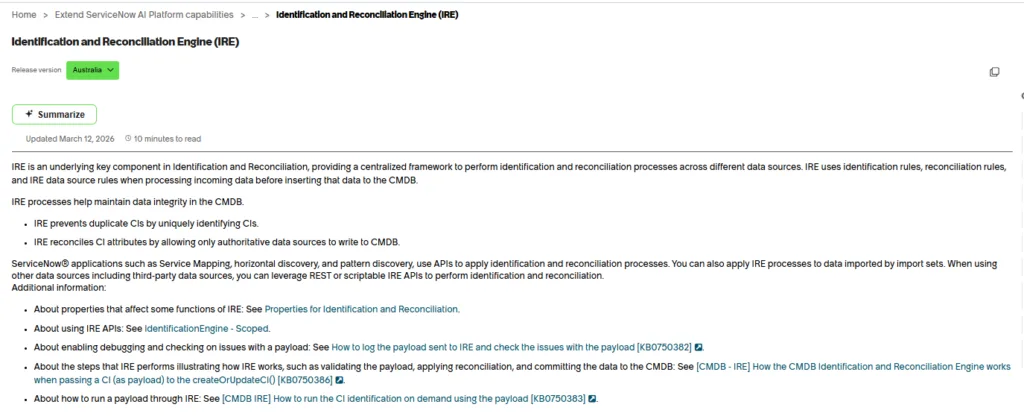
CMDB data quality isn’t a one-time cleanup — it’s an ongoing discipline. Teams that maintain high-quality CMDB data follow a repeatable cycle: discover, normalize, reconcile, validate, and govern. Automate discovery so CI records update continuously. Enforce normalization rules so data from different sources lands consistently. Use ServiceNow’s Identification and Reconciliation Engine (IRE) to catch duplicates before they take root. Schedule regular validation reviews — comparing what the CMDB says against what actually exists.
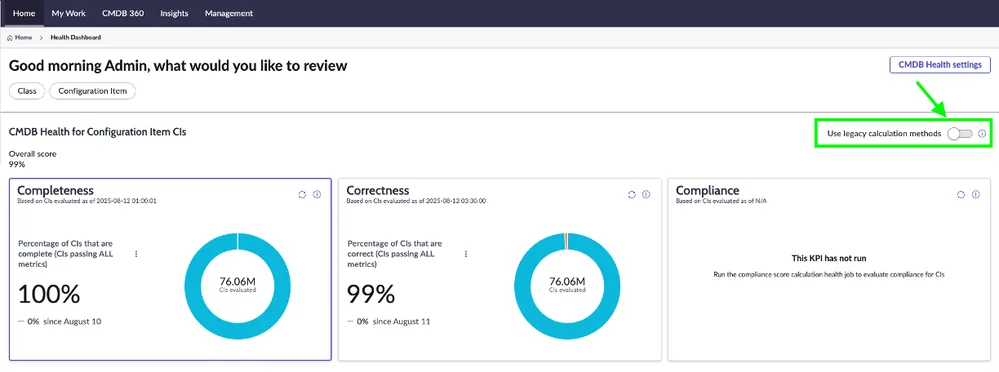
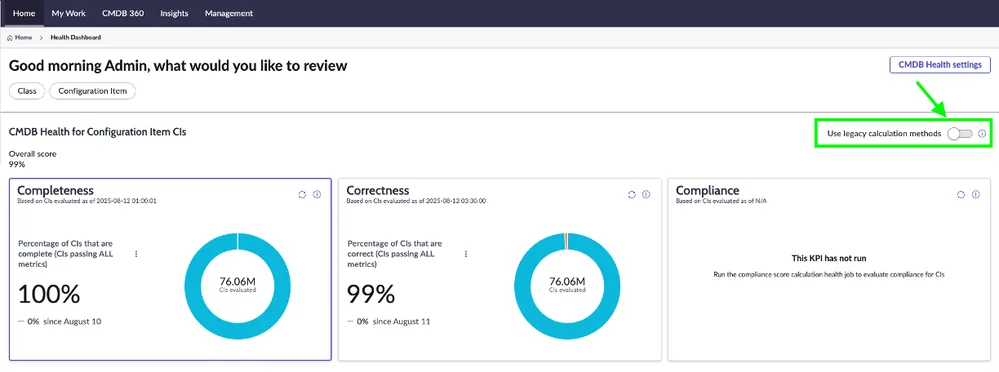
The teams that do this well treat data quality as an operational metric, not a project milestone. They track completeness percentages, duplicate rates, and stale CI counts weekly — and they act on the numbers.
Aligning the CMDB with CSDM
CSDM, or the Common Service Data Model, is ServiceNow’s standard for modeling services in the CMDB. It defines what types of services should exist, how they relate to technical components, and how data should be structured across teams. CSDM provides the blueprint. The CMDB provides the data.
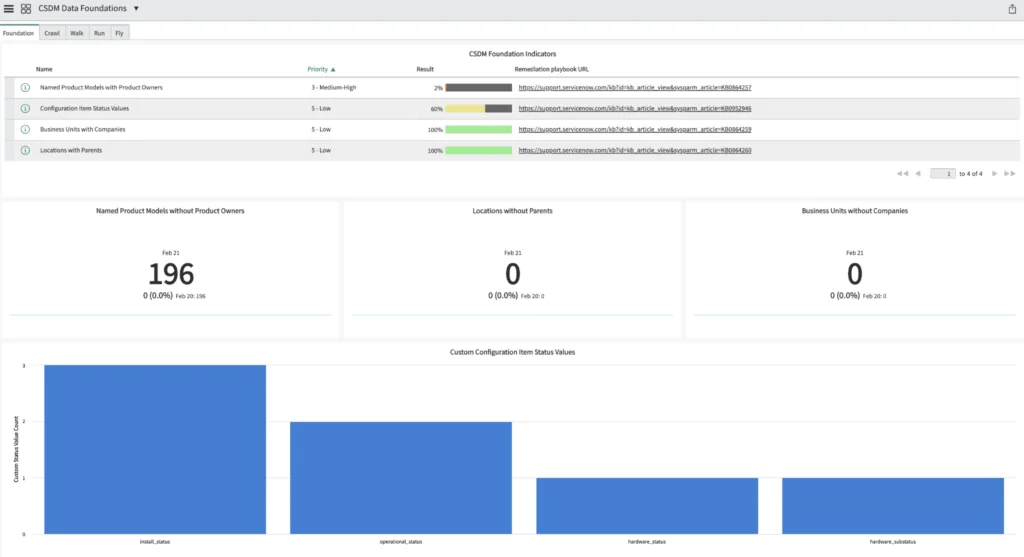
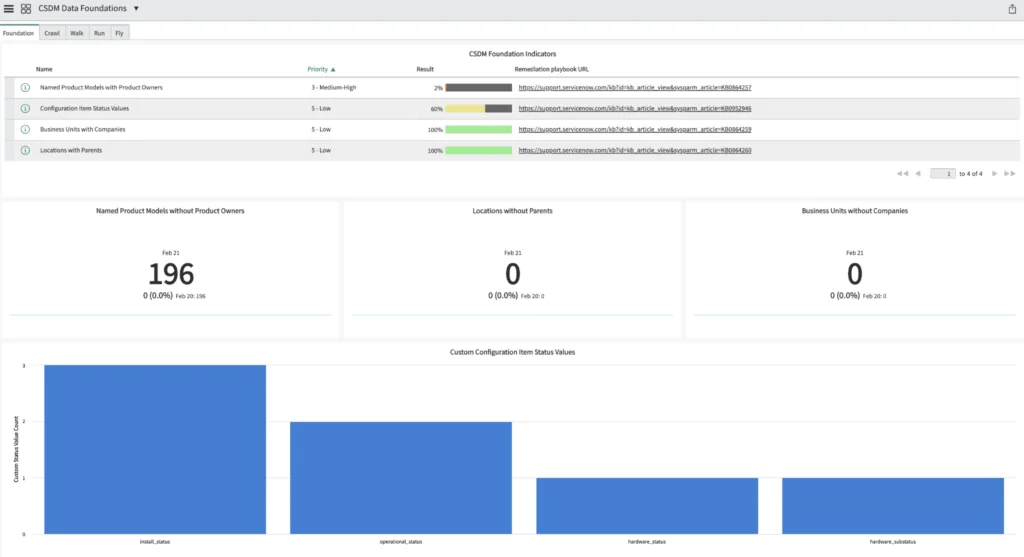
Without CSDM alignment, teams model services differently — making cross-team reporting and automation difficult.
Learn more: Why do Common Service Data Models (CSDM) matter for CMDB success?
Put simply: CMDB answers what exists. CSDM answers how it should be organized. Both are necessary for a scalable ServiceNow implementation.
How the CMDB supports ITIL practices
The CMDB plays a foundational role across multiple ITIL 4 practices. When CI and relationship data is accurate, it directly supports:
- Change enablement — by enabling impact analysis and risk assessment before changes are approved
- Incident management — by helping teams quickly identify affected components and services
- Problem management — by exposing recurring dependencies and failure points
- Service asset and configuration management — by maintaining reliable records of CIs and their relationships
- Service catalog management — by linking services to the underlying infrastructure that delivers them
These practices depend on trusted data. Without it, processes slow down and outcomes suffer.
The role of the configuration manager
The configuration manager owns the integrity of CI data in the CMDB. This role is responsible for defining CI standards, enforcing classification rules, running data quality audits, and coordinating across teams that create or modify CIs.
In practice, the configuration manager acts as the gatekeeper between discovery tools, ITSM processes, and the CMDB itself. When a new CI class is proposed, the configuration manager evaluates whether it fits the existing model or creates unnecessary fragmentation. When data quality drops, they investigate whether the cause is a discovery gap, a process gap, or a governance gap.
Organizations without a clearly defined configuration manager almost always see CMDB data quality decline over time. It’s one of the simplest governance changes that makes the biggest difference.
Discovery and integration options for ServiceNow CMDB
Even the best CMDB model won’t stay accurate on its own. IT environments change constantly. New servers appear. Cloud resources spin up and down. Applications are patched, moved, or retired.
Discovery approaches that work well in stable, on-prem environments often fall short in cloud and hybrid setups. Cloud resources change more frequently, credentials rotate, and dependencies shift. For these environments, continuous discovery, stronger normalization, and deeper relationship mapping are critical.
Why manual updates don’t scale
Many teams start by managing CIs manually. At first, this feels manageable. Over time, it becomes a bottleneck — delayed or missed CI changes, inconsistent data across teams, and higher risk during incidents and changes. As environments grow, manual CMDB maintenance can’t keep up.
How ServiceNow discovery populates the CMDB
ServiceNow’s native discovery scans your environment to identify devices and software, then automatically creates or updates CI records. It populates attributes like IP addresses, OS versions, installed software, and status.
The flow works like this: discovery runs a scheduled scan, identifies a device or application, checks the CMDB for an existing match using identification rules, and either creates a new CI or updates the existing record. ServiceNow’s IRE handles the matching logic — comparing discovered data against existing CI records to prevent duplicates.
For many organizations, this works well for traditional on-prem infrastructure, standard server and network discovery, and environments with stable credentials. However, as environments become more complex, teams often see gaps — particularly in cloud visibility, application-layer dependencies, and cross-platform relationship depth.
Native discovery can struggle when credentials are incomplete, cloud and SaaS environments change frequently, relationship depth is limited to infrastructure layers, or CI updates lag behind real-world changes. These limitations don’t mean native discovery is ineffective. They mean it may not cover everything on its own.
Virima discovery for ServiceNow CMDB
Virima’s IT discovery is designed to extend and strengthen CMDB data in dynamic, hybrid environments. It focuses on agentless discovery across on-prem and cloud, deeper visibility into applications and dependencies, and continuous CI updates to reduce data drift. Virima also emphasizes CI normalization, relationship accuracy, and integration with ServiceNow’s reconciliation process — so discovered data improves CMDB quality rather than adding noise.
Where native discovery typically maps infrastructure-level relationships, Virima builds service-aware dependency maps. Combined with ViVID™ service mapping, teams get visual dependency maps that overlay operational data — open incidents, pending changes, and vulnerabilities — directly on the service map. That means when an incident fires, the team sees not just the failed CI but everything upstream and downstream that’s affected.
A hybrid discovery approach
In practice, many organizations use a hybrid model: native ServiceNow discovery where it fits well, and Virima discovery to close coverage and relationship gaps. This lets teams maximize existing ServiceNow investments, improve CMDB completeness and trust, and reduce manual effort without overhauling tools.
Quick comparison: discovery options
| Capability | ServiceNow Discovery | Virima Discovery | Hybrid Approach |
| Infrastructure coverage | Good | Strong | Strongest |
| Cloud visibility | Limited | Strong | Strong |
| Relationship depth | Infrastructure-focused | Service-aware | Best |
| Manual effort | Medium | Low | Optimized |
| CMDB trust over time | Moderate | High | Highest |
Integrating discovery with the CMDB
Recent ServiceNow releases have expanded CMDB Health, Discovery, CMDB Data Manager, and Service Graph Connector capabilities. Regardless of the discovery method, discovered data must follow CI class standards, respect normalization rules, and reconcile cleanly using ServiceNow’s IRE.
Without this, discovery can actually create duplicates and inconsistencies. When discovery and reconciliation work together, the CMDB stays accurate with minimal manual work.
Discovery keeps CI data fresh, but it doesn’t define ownership, priorities, or standards. That requires governance.
CMDB failure modes, governance, and measuring success
Common failure modes and how to fix them
Most CMDB issues come from gradual drift. Small inconsistencies add up until the CMDB is no longer reliable.
Duplicate CIs occur when the same component is discovered or created multiple times under slightly different names or classes. Fix it by enforcing identification rules through ServiceNow’s IRE, normalizing CI naming, and reducing overlapping discovery sources.
Stale or outdated records represent components that no longer exist or no longer reflect reality. Fix it by automating CI updates through discovery, defining clear retirement rules, and reviewing inactive CIs on a scheduled basis.
Misaligned CI classes break reporting and automation when similar components are modeled using different classes. Fix it by standardizing CI class usage, aligning to CSDM guidance, and limiting custom classes.
Orphaned or missing relationships turn impact analysis into guesswork. Fix it by prioritizing relationship depth over CI count, using automated discovery for dependencies, and validating relationships through incident and change reviews.
Most CMDB recovery efforts follow the same pattern: normalize existing CI data, remove duplicates, rebuild critical relationships, automate discovery, and introduce governance and ownership. The key is consistency, not perfection.
Governance and ownership
CMDB health improves only when ownership is clear. Most successful teams define responsibility across roles:
- Configuration manager — Owns CI standards, quality, and audits
- Service owners — Accountable for services and related CIs
- IT operations teams — Ensure changes reflect real-world updates
- ServiceNow platform owner — Oversees tooling, integrations, and upgrades
Lightweight, consistent reviews beat large cleanups every time. Common cadences include weekly CMDB health checks, monthly reconciliation reviews, and quarterly model and class audits.
What CMDB success looks like by role
Configuration manager: CI classes are standardized, data quality issues are caught early, and audits are routine — not reactive.
IT operations manager: Faster incident resolution, fewer failed changes, and confidence that impact analysis reflects reality.
ServiceNow platform owner: The CMDB is trusted across teams, scales with new services, and continues to work after upgrades.
Measuring CMDB health and maturity
Counting CIs isn’t a success metric. What matters is how CMDB quality improves operational outcomes. Teams typically track mean time to resolution (MTTR), change failure rate, incident impact accuracy, and percentage of automated CI updates.
CMDB maturity isn’t a binary state — it’s a spectrum. Most organizations assess maturity across five dimensions:
| Dimension | What it measures | Weak (1) | Moderate (3) | Strong (5) |
| Coverage | Are all relevant components represented? | Major CI gaps; key services missing | Core infrastructure covered; apps partial | Infra, apps, cloud, and services fully represented |
| Correctness | Are CI attributes accurate and normalized? | Frequent duplicates, stale or incorrect data | Mostly accurate with periodic cleanup | Normalized, validated, and trusted CI data |
| Timeliness | How quickly are changes reflected? | CI updates lag weeks or months | Scheduled updates with some delay | Near real-time automated updates |
| Relationship depth | Do dependencies reflect real impact paths? | Few or no dependencies modeled | Partial service and application relationships | End-to-end service dependency mapping |
| Policy adherence | Are standards and rules being followed? | No enforced standards or audits | Informal standards, inconsistently applied | Documented, enforced, and regularly audited |
Score each dimension on a 1–5 scale. An organization scoring 2 on timeliness but 4 on coverage knows exactly where to invest next. Virima’s CMDB health framework uses these same dimensions to give teams a measurable baseline.
How Virima auto-populates and maintains ServiceNow CIs
For teams running ServiceNow, keeping CI data accurate is the difference between a CMDB that drives decisions and one that gathers dust.
Virima connects directly to your ServiceNow instance and continuously populates CI records through agentless discovery across your hybrid environment. As new assets appear, change, or retire, Virima updates the corresponding CIs in ServiceNow automatically — following your CI class standards and normalization rules.
The integration uses ServiceNow’s IRE for reconciliation, so discovered data maps cleanly to existing records without creating duplicates. Virima’s ViVID™ service mapping then layers operational context — open incidents, pending changes, and known vulnerabilities — on top of dependency maps, giving your teams a live picture of service health.
The result: a ServiceNow CMDB that stays current without manual upkeep, with relationships deep enough to support real impact analysis.
Schedule a demo to see how Virima keeps your ServiceNow CMDB accurate and actionable.
| A practical 90-day CMDB uplift plan CMDB improvement doesn’t require a multi-year program. Most teams see meaningful gains within 90 days. 1–30 days: baseline and alignment. Assess current CMDB health across the five dimensions above. Identify critical CI classes and the services they support. Define ownership: who is the configuration manager, who owns each service, and who reviews data quality. 31–60 days: discovery and normalization. Deploy or tune discovery to cover gaps — especially cloud and application-layer CIs. Enforce normalization rules so incoming data is consistent. Remove duplicate CIs using IRE identification rules. 61–90 days: relationships and optimization. Build and validate service relationships — start with your highest-impact services. Align CI classes and service models to CSDM. Start tracking operational KPIs (MTTR, change failure rate, stale CI percentage) to measure progress.By the end of 90 days, teams typically see higher trust and better adoption across incident and change workflows. |
Your ServiceNow CMDB is only as good as the data feeding it.
Virima discovers your entire hybrid environment on-prem, cloud, and SaaS — and auto-populates ServiceNow CIs with normalized, relationship-rich data. No manual entry. No stale records. No duplicate cleanup cycles.
Teams using Virima with ServiceNow see faster incident resolution, more confident change approvals, and a CMDB their operations teams actually trust.
See how Virima strengthens your ServiceNow CMDB → | Schedule a demo
FAQ
What is the difference between CMDB and CSDM in ServiceNow?
The CMDB is the database that stores CI records and their relationships. CSDM is ServiceNow’s data model framework that defines how services, applications, and infrastructure servicenow configuration management database should be organized within that database. You need both: the CMDB holds the data, and CSDM ensures it’s structured consistently across teams.
How often should CMDB data be updated?
For most organizations, continuous automated updates through discovery are the goal. At minimum, run discovery scans weekly for infrastructure CIs and daily for cloud resources that change frequently. Manual updates should be the exception, not the rule — reserved for CIs that can’t be reached by discovery tools.
What are the most common causes of CMDB failure?
The three most frequent causes are duplicate CIs from multiple uncoordinated discovery sources, stale records that aren’t retired when the underlying component is decommissioned, and missing relationships that prevent accurate impact analysis. All three stem from the same root issue: insufficient governance and ownership over CMDB data.