ITAM In A Hybrid Workplace: Remote Asset Monitoring To Secure Your Assets
Organizations with hybrid work setups have a visibility problem. IT assets are scattered across offices, home networks, and cloud environments, and most teams can’t track what’s where. When your workforce operates from multiple locations on a mix of company-issued and personal devices, standard IT Asset Management processes break down quickly.
Remote work isn’t going away. The infrastructure behind it, though, has outgrown the asset management practices most organizations still rely on. Your team needs real-time visibility into hardware, software, and cloud resources, regardless of where those assets sit. Without that visibility, you lose control over compliance, security, and cost.
ITAM tools close this gap by pulling every asset into a single view across on-premises, cloud, and remote environments, effectively acting as a remote asset monitoring solution for distributed teams. The result: accurate inventories, audit readiness, smoother lifecycle management, and tighter software license control.
This post covers the challenges of managing IT assets in hybrid environments and how remote asset monitoring helps you stay ahead of them.
Remote asset monitoring challenges in a hybrid environment
These are the challenges asset managers deal with when their workforce splits between office and remote:
Security gaps from unmanaged remote devices
Hybrid work widens your attack surface 57% of IT managers report an increase in cybersecurity threats due to remote work, showing how distributed environments expand risk exposure. Employees connect from home networks on personal laptops, tablets, and phones that your IT team may never have cataloged. Those devices slip past your security controls and create blind spots you can’t monitor, making remote asset management significantly more difficult.
The math is simple: devices you can’t see are devices you can’t protect. Unmanaged endpoints might carry malware, run outdated operating systems, or rely on weak credentials. This aligns with findings that 45% of IT employees report stricter cybersecurity policies due to remote work risks, often driven by unmanaged endpoints. Any one of those gives an attacker a foothold.
Data privacy complicates this further. Remote employees sit outside the physical controls of your corporate network. If you don’t have visibility into what devices access your systems, enforcing consistent security protocols becomes almost impossible.
Cloud adoption adds to the challenge. Data stored in AWS, Azure, or GCP environments needs the same governance you apply to on-premises assets. Your security posture has to extend across every environment your team uses.
Compliance risks without full asset visibility
Without a complete picture of every asset on your network, audit compliance turns into guesswork. Auditors want a full, accurate inventory of IT assets and their security posture. No remote asset monitoring means you can’t provide that.
Remote work stacks the odds against you. Your team can’t physically verify what’s running on home networks. Personal devices accessing company systems may carry unpatched vulnerabilities or unauthorized software, and that’s exactly the kind of gap auditors flag.
Keeping remote machines patched, passwords rotated, and configurations current demands automation. Manual processes don’t scale across a distributed workforce, and every missed update or unpatched device is a compliance violation waiting to happen.
Productivity losses from poor asset tracking
When you don’t know what assets exist, where they are, or who’s using them, incident resolution drags. A remote employee reports a connectivity issue, and your team can’t see the device’s configuration or dependencies. What should be a quick fix becomes a multi-hour troubleshooting session.
Weak asset tracking also drives wasted spend. Licenses slip through the cracks, hardware gets over-provisioned, and decommission dates pass unnoticed. Across a hybrid environment with assets spread over multiple locations and cloud platforms, those costs compound.
Priorities for IT teams managing a hybrid work environment
Managing a hybrid setup requires IT teams to balance flexibility with consistent visibility and control.
Build full visibility across your entire IT network
Asset management software gives hybrid teams the cross-environment visibility they need. A capable tool discovers hardware, software, applications, licenses, and contractual details across on-premises data centers, cloud infrastructure, and SaaS platforms in real time.
This visibility does two things. It keeps data secure and accessible only to authorized users. And it catches changes as they happen, so records stay current without manual intervention. Reliable asset data also feeds utilization reports that help you cut waste and right-size spending.
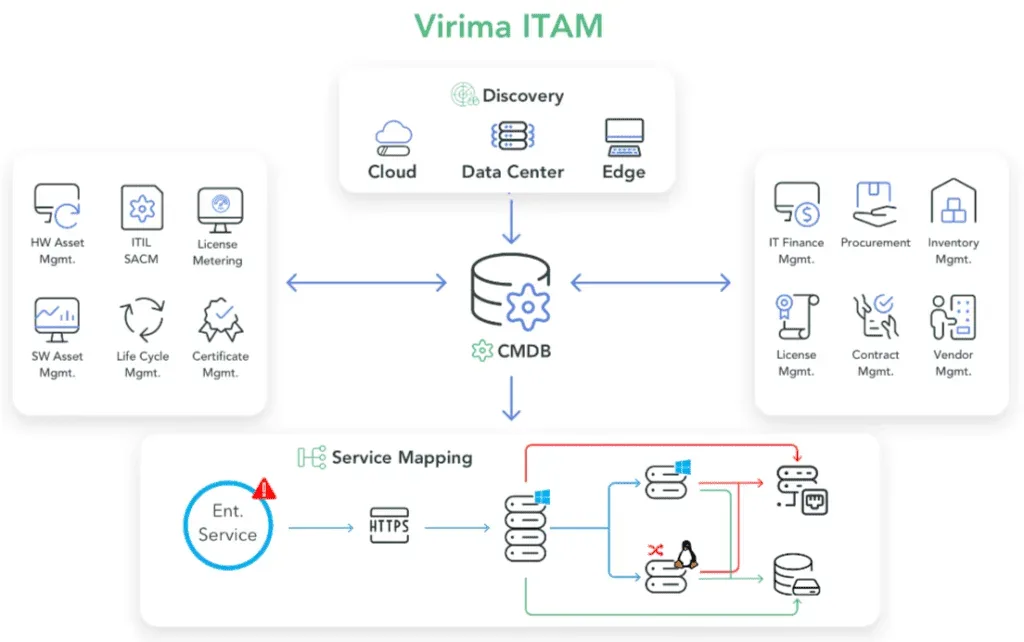
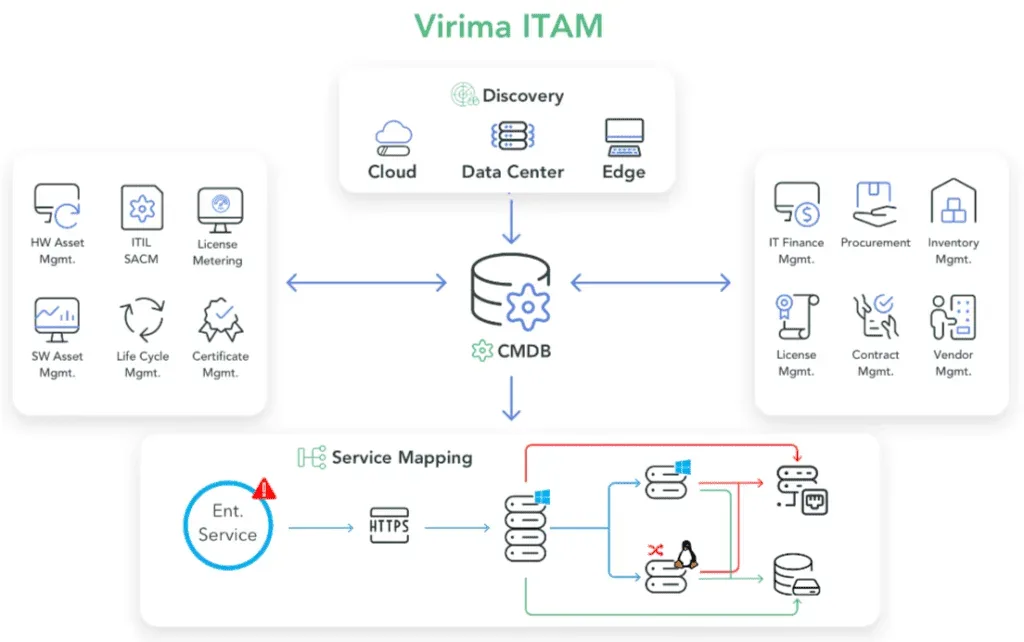
Virima’s IT discovery scans your entire network using agentless and agent-based probes across on-premises, cloud, and edge environments. Every asset is identified with its location and role in your infrastructure. Scheduled discovery scans run on your cadence, so new devices get picked up on the next scan cycle without manual effort.
For remote and hybrid employees who aren’t always connected to the corporate network, Virima’s Discovery Agent includes a Work from Anywhere (WFA) solution. WFA tracks daily configuration changes and software usage on remote PCs over the Internet, without requiring a VPN or direct network connection. That means your team gets visibility into remote endpoints even when those devices are off-network, allowing you to remotely monitor them and closing one of the biggest gaps in hybrid asset monitoring.
Secure your network with strong BYOD policies
Hybrid work demands clear bring-your-own-device (BYOD) policies backed by enforcement. ITAM tools let you set granular controls: which devices can access company data, what applications they can run, and who gets access to sensitive systems.
Monitoring BYOD devices in real time helps you catch risks before they escalate. A personal device connects to your network running outdated antivirus software or carrying a known vulnerability, and your team flags it before it becomes an incident. Standard reporting policies for device usage keep your asset inventory accurate across both company-owned and personal hardware.
Asset tracking capabilities maintain a clear record of every device with network access. You know who connects, what they can reach, and whether their device meets your security baseline.
Some asset attributes can’t be learned through scanning alone. Who owns a personal device? What’s its lifecycle status? Is it approved for production use? Virima’s Autonomic Social Discovery™ (ASD) automates human intelligence gathering by routing these questions to the right people in your organization. ASD fills the data gaps that discovery probes can’t reach, so your CMDB has complete, reliable records for every asset, including the ones that walked in the door with your employees.
Use ITAM to drive operational efficiency
A solid ITAM tool breaks down the information silos that slow hybrid operations. When hardware inventories, software licenses, and configuration data live in disconnected systems, your team burns time reconciling records instead of resolving issues.
Pulling asset data into one place gives you actionable intelligence. You spot underused licenses, flag hardware approaching end-of-life, and base purchasing decisions on actual usage data. Automated tracking keeps assets current with licensing obligations and regulatory requirements.
Virima’s ITAM platform produces detailed reports spanning your full asset landscape. The reporting engine combines hardware inventory, software license records, and discovery results into dashboards designed for your team. You track utilization trends, catch anomalies, and monitor infrastructure and asset health from one place.
Integrate security and governance without disrupting workflows
ITAM tools give you visibility into every asset connected to your corporate network across on-premises and cloud environments. Your IT team can track inventory, enforce security policies, and stay on top of compliance requirements without piling on manual work.
Automated discovery surfaces unauthorized devices and unexpected software installations across your network. Your ITSM change management workflows enforce approval gates before changes go live, reducing the risk of unplanned modifications that could create security gaps or compliance violations. Because identity is often the first target in a distributed environment, pairing asset discovery with active directory monitoring strengthens your ability to detect unauthorized access changes, stale accounts, and privilege escalations before they become incidents.
Virima’s discovery maintains an accurate, continuously updated inventory of hardware and software assets. Built-in NIST NVD vulnerability lookup cross-references your discovered assets against known vulnerabilities, so your team can prioritize remediation based on both vulnerability severity and business service impact. Pair that with ViVID service maps, and you can pinpoint an issue, trace which services it impacts, and route it to the right team from a single interface. This approach cuts MTTR and gives incident response teams full context from the start.
Why remote asset monitoring with Virima secures your hybrid infrastructure
Managing IT assets in a hybrid work environment takes more than basic inventory tracking. It takes a full IT operations management approach: continuous discovery across every environment, a CMDB that maps how assets relate, service maps that trace impact chains, and reporting that keeps your team ahead on compliance and cost.
Virima packages all of this in one platform. IT discovery catalogs assets automatically across on-premises, cloud, and edge environments. The CMDB maintains accurate relationship data that’s always audit-ready.ViVID™ service maps display real-time dependencies so your team resolves incidents faster.
And codeless integrations with ITSM platforms like ServiceNow and Jira Service Management sync discovered assets to your CMDB using configurable blueprints and business rules, so your ITSM workflows always have current data.
For hybrid IT teams, this translates to fewer blind spots, faster incident resolution, and confidence that your asset data is both complete and current.
Book a demo with Virima to see how our platform helps you manage and secure IT assets across your hybrid workplace.
FAQ
1. What is the role of CMDB in hybrid remote asset monitoring?
A CMDB ties your asset data together. In a hybrid environment, isolated asset records fall short. You need to understand how assets relate to each other: which servers support which applications, which cloud instances connect to which databases, and which services rely on which infrastructure components.
Without a CMDB mapping these relationships, your team responds to incidents without context. A server goes down, and nobody knows which business services are affected until users start reporting problems. An accurate CMDB fed by continuous discovery gives your team the relationship data they need. Pair it with ViVID™ service maps, and you see the blast radius of any change or failure immediately, not after four hours of manual investigation.
How does service mapping help with hybrid infrastructure visibility?
When your infrastructure spans offices, cloud providers, and home networks, understanding how services connect matters more than ever. Service mapping automatically discovers dependencies between applications, databases, network devices, and cloud resources.
Virima’s ViVID™ (Virima Visual Impact Display) builds on this with dynamic, real-time visualizations of your service dependencies. When an incident hits, your team sees which services are affected without guessing. ViVID maps the impact chain visually so you can prioritize response and communicate status to stakeholders immediately. For IT ops teams running hybrid infrastructure, this cuts mean time to resolution (MTTR) because you see the problem and its downstream effects in a single view.
How does remote asset monitoring improve security in a hybrid workplace?
Remote asset monitoring gives IT teams continuous visibility into every device, whether it’s on-premises, in the cloud, or used remotely. This visibility helps identify unmanaged endpoints, detect vulnerabilities early, and enforce security policies consistently across all environments. As a result, teams can reduce blind spots, respond to threats faster, and maintain a stronger security posture across distributed infrastructure.






