Mastering The IT asset Discovery Process: Strategies For Overcoming Risks
Most IT teams still use manual methods or basic tools to track assets. However, these methods often miss important details. As a result, you get gaps and blind spots over time. In fact, IBM says 40% of data breaches involve data across many environments. So, it becomes harder for you to see all your assets clearly.
The IT asset discovery process helps you find and list every asset on your network. It checks both hardware and software in your system. Then, it finds devices, maps where they are, and collects key details. For example, it gathers OS versions, IP addresses, and installed software. However, even this process can create risks if you do not manage it well.
So, this guide will help you understand those risks step by step. Next, it will show you simple ways to reduce them. Finally, you will learn what to look for in a tool that truly keeps your system safe.
How the IT asset discovery process supports vulnerability management
If your asset list is not complete, your security plan has gaps. As a result, you miss important risks. The average cost of a data breach reached $4.44 million in 2025. So, poor visibility can cost you a lot of money. Every missed device is one you cannot patch or protect.
IT discovery tools help you scan your network and find every asset. They build a full list of devices, apps, and settings. Then, this list goes into your CMDB. So, your security team gets a clear and updated map. You can see what you have, where it runs, and how it connects.
Next, you compare these assets with known risk databases. For example, the National Institute of Standards and Technology offers the NVD for known vulnerabilities. Tools like Virima IT Discovery check assets for known risks automatically. They also use maps like ViVID™ to show which assets affect key services. So, you can fix the most critical issues first.
However, without automated discovery, your data quickly becomes outdated. As a result, hidden devices stay unpatched. Your compliance gaps grow over time. Also, your response slows down during an attack. This happens because you cannot see the full impact clearly.
Risks associated with the IT asset discovery process
The IT asset discovery process makes your security stronger. However, it also brings some risks. So, you need to understand them clearly. Here are the four most common risks you should know.
Data privacy risks
Discovery scans collect sensitive details about your devices. For example, they gather IP addresses, device names, and software versions. They also capture system settings and configurations. So, this data is very important and needs protection.
However, if this data gets exposed, it becomes a guide for attackers. As a result, they can plan targeted attacks more easily. This can also lead to privacy issues for your business. Therefore, you must keep all discovery data safe.
You should always encrypt this data and control who can access it. In addition, store it in a secure place. This way, you reduce the risk and protect your systems better.
Network performance risks
Scanning large networks with thousands of devices puts strain on bandwidth and processing. Poorly timed or overly aggressive scans can cause:
- Network congestion and slow performance
- Dropped connections for end users
- In extreme cases, network downtime
First, plan your discovery scans during off-peak hours. This helps reduce pressure on your network. As a result, your systems can run smoothly without slowdowns.
Next, use tools that prevent scan storms. These tools control how many requests run at once. For example, the Virima Discovery App uses smart scan pacing. So, it spreads out requests and avoids flooding your network.
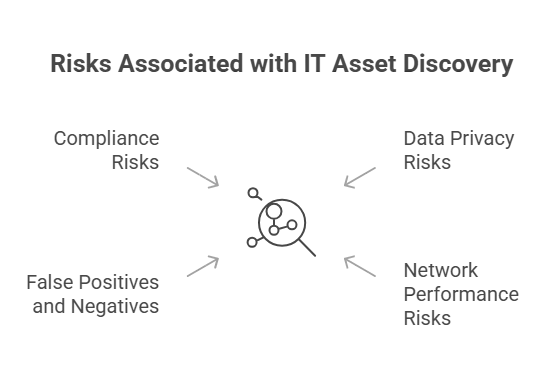
False positives and negatives
No discovery tool is perfect. Sometimes, it shows a device that is not really there. This is called a false positive. Other times, it misses a real device on your network. This is called a false negative.
Both issues can confuse your asset list. For example, false positives waste your time on devices that do not exist. On the other hand, false negatives leave real devices unprotected. So, you should run regular audits and do physical checks. This helps you catch these problems early.
However, some details cannot come from scans alone. For example, ownership, business value, and SLAs need human input. So, tools like Virima Autonomic Social Discovery help fill these gaps. It asks the right people for missing details. As a result, your CMDB stays complete and accurate.
Compliance risks
Regulatory frameworks like HIPAA, PCI DSS, and GDPR require accurate inventories of hardware and software assets. An incomplete or inaccurate inventory can result in:
- Audit failures and remediation orders
- Fines and penalties
- Loss of certifications
Discovery must be complete and repeatable to meet compliance needs. So, you should run scans on a fixed schedule. This helps you avoid gaps between audits. As a result, your data stays fresh and reliable.
Also, using trusted tools can make audits easier. For example, Virima ITSM has PinkVERIFY ITIL certification. It supports key processes like asset, change, and incident management. So, auditors can see clear proof that your workflows follow best practices.
What is the difference between agentless and agent-based discovery?
Agentless discovery scans devices from a distance. It uses simple network methods like SSH, WMI, and SNMP. So, you do not need to install any software on devices. As a result, it is quick to set up and easy to scale.
On the other hand, agent-based discovery works differently. It installs a small program on each device. Then, it tracks changes, monitors software use, and sends updates back. Even better, it works when the device is off the network.
So, most teams use a mix of both methods. First, use agentless scans to cover your whole network. Then, add agents to important systems like servers and remote devices. Tools like Virima IT Discovery support both methods. This way, you get wide coverage and deeper insights at the same time.
How often should you run IT asset discovery scans?
Scan frequency depends on the size and volatility of your environment.
- Large, dynamic environments (cloud workloads, DevOps pipelines): Daily or more frequent scans
- Stable on-premises networks: Weekly scans with event-triggered updates
- Compliance-driven environments: At a minimum, scan before each audit period
Virima Discovery App lets you schedule scans based on your needs. So, you can run them as often as your environment changes. In addition, its agent option tracks daily changes and software use. This helps you monitor important assets more closely. As a result, your CMDB stays updated, and no device goes unnoticed.
Also, discovery supports your IT Asset Management (ITAM) process. When a new device appears, it can trigger the next steps automatically. For example, it can start validation, track allocation, and plan device removal later. However, without this automation, you must rely on manual work. So, teams often end up matching spreadsheets with outdated scan data.
Best practices for mitigating IT discovery risks
Now, let’s explore the best practices for mitigating IT discovery risks and maintaining accurate, secure visibility across your environment.
Secure discovery data from day one
Protect the data your scans collect with:
- Encryption for data in transit and at rest
- Role-based access controls so only authorized personnel can view discovery results
- Data masking for sensitive fields in reports shared outside IT
Virima Discovery App keeps your asset credentials safe. It encrypts them directly within the app. So, your sensitive data stays protected at all times.
Also, the app runs on servers that you own and control. Because of this, your credentials never leave your environment. This gives you more control and reduces risk.
In addition, discovery data is encrypted before it is sent out. Then, it is securely transmitted to the Amazon Web Services platform. As a result, your data stays safe both in transit and at rest.
Optimize scan scheduling and scope
Avoid network disruptions by:
- Running scans during off-peak hours
- Segmenting your network to reduce the scan scope per job
- Using discovery tools with built-in scan pacing
These steps keep discovery from competing with production traffic for bandwidth.
Pick discovery tools that stay current
Reduce false positives and negatives by choosing a discovery tool that:
- Updates its probe library regularly
- Supports both agentless and agent-based scanning for broader coverage
- Integrates with your ITSM platform for automatic inventory reconciliation
Virima integrates with ServiceNow, Jira Service Management, Ivanti, HaloITSM, Cherwell, Xurrent, and Hornbill, so discovered assets sync directly into your service management workflows.
Maintain compliance-ready inventory
Keep your asset records audit-ready by:
- Scheduling automated asset discovery process scans on a regular cadence
- Running compliance assessments between audit periods to catch gaps early
- Documenting your discovery scope and methodology for auditors
ViVID™ service maps also help you manage changes better. They show both planned and recent changes on one view. So, you can clearly see what is happening in your system.
Before you approve a change, you can check its impact. For example, you can see which connected services may be affected. This includes both upstream and downstream systems. As a result, you reduce the risk of unexpected issues after changes.
Train your team
Staff should understand:
- Why the asset discovery process matters and what risks it carries
- How to configure and operate your discovery tools correctly
- How to handle data privacy concerns if sensitive information surfaces during scans
Training reduces human error, which accounts for the majority of discovery-related incidents.
How to choose the right IT asset discovery tool
When evaluating discovery tools, ask these five questions:
- Does it scan on-premises, cloud (AWS, Azure), and hybrid environments?
- How many configuration attributes does it collect per asset?
- Does it sync with your ITSM and CMDB platforms?
- How does it handle credentials and discovery data?
- Can it handle your full environment without scan storms?
A tool that performs well in all five areas helps you reduce risk at every step. So, you can manage your asset discovery process with more confidence. As a result, your systems stay safer and more stable.
For example, Virima IT Discovery supports cloud and on-premises environments. It currently covers Amazon Web Services and Microsoft Azure. So, you can track assets across different setups in one place.
However, if you use other cloud providers, you should check support first. This helps you avoid gaps later. So, always confirm coverage before choosing any tool.
How Virima Discovery reduces IT asset discovery risk
Here is how Virima’s design helps reduce risk across each stage. It runs on AWS with strong data separation. Also, it encrypts credentials on your servers, so they never leave your control. In addition, discovery data is encrypted before it is sent. So, your data stays safe at all times.
On the network side, the Discovery App uses smart scan pacing. As a result, it avoids network slowdowns and scan storms. You can also control scan timing and scope easily. For accuracy, it supports AWS and Azure environments with wide asset coverage.
Autonomic Social Discovery™ fills gaps by collecting missing details from people. Also, it maps asset links and feeds data into your CMDB. It integrates with ServiceNow, Jira Service Management, Ivanti, and more. So, your data stays connected and useful.
Request a demo to see how it works in your setup.