What is Vulnerability Management?
A vulnerability is a weakness in a system that can expose it to attacks or damage. Open ports, unsafe settings, and software flaws often create easy entry points. As a result, risks can quickly grow across your IT environment.
Unlike viruses, vulnerabilities are harder to eliminate. They often come from old code, human errors, or evolving threats. Because of this, they require continuous monitoring rather than a one-time fix.
After running vulnerability scans, IT teams review and document the findings. Then, stakeholders assess the risks and decide whether to fix, reduce, or accept them based on business needs.
Vulnerability management is a continuous cycle. It starts with discovering IT assets and identifying risks. Next, teams analyse and prioritise vulnerabilities based on impact, helping them manage security more effectively.
By treating vulnerability management as an ongoing process, organisations can stay prepared, reduce risks, and strengthen their overall security posture.
Types of vulnerabilities and their causes
Understanding vulnerabilities is essential for building secure systems. Let’s break down the common types and what causes them.
1. Hardware
Hardware vulnerabilities often come from the surrounding environment. For example, humidity, dust, and poor physical protection can damage equipment. In addition, old hardware and overheating can create serious problems. Over time, these issues can weaken devices and cause system failures.
2. Software
Software vulnerabilities usually come from faulty code. Because of this, attackers search for buggy software to break into systems. In fact, research shows that over 33% of known vulnerabilities are high or critical. So, many of these flaws can seriously affect your operations if you ignore them.
Common causes include poor testing and unsafe coding practices. In addition, missing audit trails can hide important activity. Design flaws can also create hidden security gaps.
3. Network
Network vulnerabilities often come from weak security controls. For example, unprotected communication lines can expose your data. In addition, weak cryptography and poor network design create more risks.
Because of this, security professionals check many layers of the network. Then they look for weak points that attackers could use. This helps you fix problems before they cause damage.
4. Personnel
IT staff and cybersecurity teams can sometimes create risks by mistake. For example, weak authentication or poor authorization controls can open security gaps. Because of this, you need strong monitoring and alerting systems. These systems should detect unusual activity and report it in real time.
Weak access controls and poor passwords also increase risk. In addition, a lack of security training can create serious problems. Sometimes, insider threats also appear because teams miss key checks. Most of these issues happen due to weak checklists or training gaps.
5. Physical site
Physical vulnerabilities often come from natural disasters. For example, floods and earthquakes can damage buildings and IT equipment. Because of this, your systems may stop working suddenly.
Power interruptions can also create serious risks. Battery backup systems usually run only for a few minutes. So, without proper protection, your systems may shut down quickly.
6. Organizational
A lack of vulnerability management awareness is a serious risk for any organization. If you skip regular audits, problems can grow quickly. In addition, weak planning can make your systems harder to protect.
Without clear priorities, teams may not fix the most critical risks first. A weak security posture also makes attacks more likely. Because of this, every other type of vulnerability becomes harder to control.
What is the difference between a vulnerability and a threat?
A vulnerability is a weak point in your infrastructure. On the other hand, a threat is an attacker or an event that tries to exploit it. In simple terms, a vulnerability is a weakness, and the threat is the danger that targets it.
Because of this, security teams use threat intelligence to study attacker behavior. This helps you understand how attackers exploit weaknesses in real situations. So, while they are related, they are not the same.
| Vulnerability | Threat |
| A known weakness in an asset that one or more attackers can exploit. | A new or newly discovered incident with the potential to harm a system or organization. |
| An unprotected or unmonitored point in a system. | The actor or event that exploits a system through its vulnerabilities. |
| Can be known or unknown. An effective vulnerability management program covers all possible vulnerabilities and their business impact. | Often uncontrollable and difficult to identify in advance. |
| Example: A former employee’s access to external accounts, logins, or company credit cards is not revoked after they leave. | Example: Malware that causes harm through automated attacks rather than direct human action. |
Vulnerability assessment
Before you start vulnerability management, you first run vulnerability assessments. These assessments help you find weaknesses in your IT systems early. Because of this, you can understand your risks more clearly.
Then you use these findings to plan your next steps. This helps you treat and reduce risks more effectively.
A vulnerability assessment typically includes tracking and documentation of:
- Business operations and personnel
- Technologies and updates
- Policies and compliance requirements
- Efforts to reduce new vulnerability risks
Modern vulnerability management tools use technology to find weaknesses in your systems. They also help you send quick alerts to IT teams. As a result, your team can act faster and fix problems sooner.
A prioritized checklist helps your IT team plan their work better. It shows how much effort each fix may require. Because of this, your team can focus on the most serious vulnerabilities first.
In this way, you reduce the chance of attackers exploiting them. As a result, your security efforts become more effective.
What is the difference between a vulnerability assessment and penetration testing?
A vulnerability assessment scans your systems to find known weaknesses. Then it ranks them based on severity. Because of this, you can clearly see which issues need attention first.
Penetration testing goes one step further. In this case, security experts try to exploit the weaknesses. This helps you understand their real-world impact.
Most organizations use both methods. They run assessments regularly for broad coverage. In addition, they perform ad hoc penetration tests to check critical systems.
What role does IT asset discovery play in vulnerability management?
You cannot protect assets you do not know exist. So, IT discovery becomes the first step in vulnerability management. It helps you build a full list of every device, application, and service on your network.
Without proper asset discovery, vulnerability scans can miss many systems. For example, unmanaged devices, shadow IT, and unknown endpoints may stay hidden. Because of this, your security risks increase.
In fact, research shows that about 45% of discovered vulnerabilities stay unresolved for over a year. This often happens because teams cannot clearly see all affected assets.
These blind spots are often where attackers find entry points. Because of this, discovery is very important. It also shows the relationships and dependencies between assets. This helps you understand how far a vulnerability could spread.
When discovery data feeds into a Configuration Management Database (CMDB), things become much clearer. Each vulnerability links to the exact asset it affects. You can also see its configuration, owner, and the business service it supports.
As a result, the data becomes more useful. Your team can understand the risk faster. Then they can take the right action to fix it.
How Vulnerability Management Lifecycle Works
A vulnerability management program follows several stages. These stages form a continuous process. Each step builds on the previous one.
Because of this, you can track and manage vulnerabilities more effectively. As a result, the issues you discover receive the attention they need.
1. Discover
First, you inventory all assets across your network. You also collect host details like operating systems and open services. This step helps you understand what exists in your environment.
Next, you create a baseline for the network. Then you automate discovery with scheduled scans. Because of this, you can keep your asset list accurate over time.
2. Prioritize assets
Categorize assets into risk groups or by business function. Assign a business value to each asset based on how critical it is to operations.
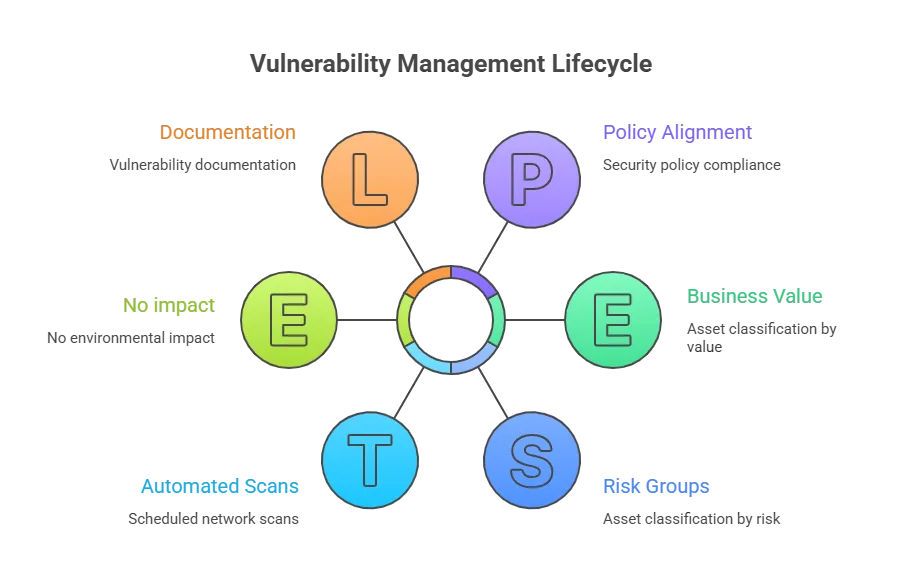
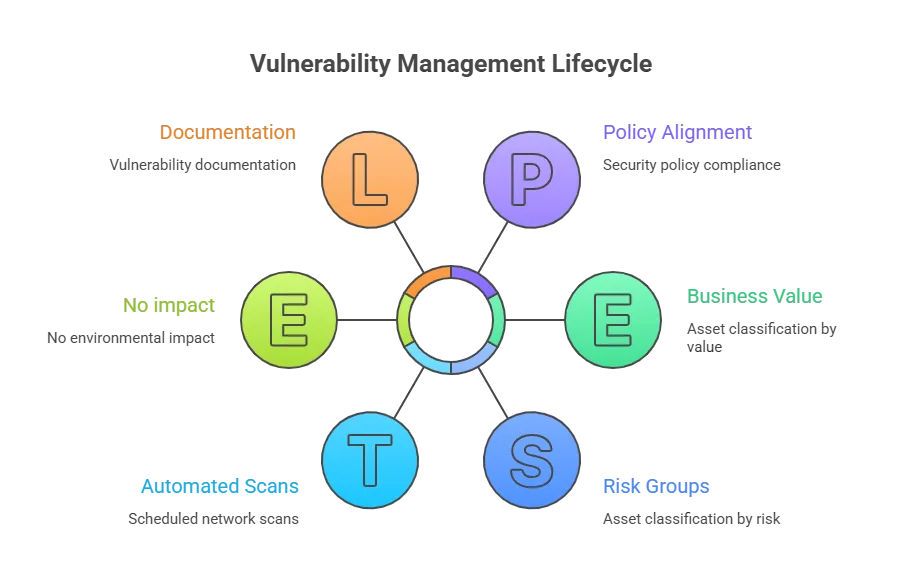
3. Assess
Build a baseline risk profile. Eliminate risks based on asset criticality, vulnerability severity, and asset classification.
4. Report
Measure the level of business risk for each discovered vulnerability against the organization’s security policies. Document a security plan that covers monitoring for suspicious activity and describes known vulnerabilities.
5. Remediate
Fix vulnerabilities in order of the business risk they pose. Address the highest-risk items first.
6. Verify
Run follow-up audits to confirm that vulnerabilities have been resolved. Close the loop before moving to the next cycle.
| How often should vulnerability scans be run? Most industry standards and security frameworks suggest running vulnerability scans at least every three months. This schedule helps you check your systems regularly. As a result, you can find problems before they grow. However, high-risk environments may need more frequent scans. Many organizations scan monthly or even weekly. This helps you detect new vulnerabilities faster. Critical infrastructure and internet-facing systems need even closer monitoring. In many cases, teams use continuous or near-continuous scanning. The right schedule depends on your IT size, risk level, and how often your environment changes. |
What is the difference between vulnerability management and patch management?
Vulnerability management and patch management are related, but they are not the same. Vulnerability management is the larger process. It helps you find, prioritize, and fix many types of security weaknesses.
These weaknesses may include misconfigurations, weak access controls, or missing encryption. So, vulnerability management looks at the full security picture. Because of this, it covers more than just software fixes.
Patch management is only one part of this process. It focuses on installing software updates that fix known vulnerabilities. These updates help close specific security gaps.
Not every vulnerability has a patch. In many cases, you must make configuration changes to reduce the risk. Sometimes you also need network segmentation to limit the damage.
You may also add compensating controls to protect the system. Because of this, patching alone is not always enough. A strong vulnerability management program uses patch management as just one tool among many.
What is a CVE in vulnerability management?
CVE stands for Common Vulnerabilities and Exposures. It is a standard ID given to publicly known security vulnerabilities. The program is maintained by the MITRE Corporation. Each CVE entry includes a short description of the issue and links to related security advisories.
Security teams use CVEs to track which vulnerabilities affect their assets. This helps you prioritize which problems to fix first. In addition, the National Institute of Standards and Technology runs the National Vulnerability Database (NVD), which builds on CVE records.
The NVD adds extra details such as severity ratings, affected products, and fix guidance. For example, it uses the Common Vulnerability Scoring System (CVSS) to rate how serious a vulnerability is. Because of this, your team can understand the risk level more easily.
Many security tools connect directly to the NVD. As a result, they can automatically flag assets that run vulnerable software. This saves you from manually checking scan results against public vulnerability databases.
Risk mitigation in vulnerability management
Risk mitigation means reducing your exposure to risky situations. It also lowers the chance of security incidents. Because of this, IT teams must keep addressing the most important risks.
To stay protected, your organization needs strong security controls. These controls help stop risks before they turn into real problems. As a result, your systems remain safer.
You can achieve this through clear policies and procedures. These preventive steps guide how your team manages security risks. This process is what IT professionals call risk mitigation.
Who is responsible for vulnerabilities?
Responsibility for vulnerabilities primarily lies with IT security teams, as they identify, assess, and manage risks across systems. However, it is a shared effort, where developers, IT operations, and end users also play a role in preventing and reducing vulnerabilities.
IT security
The IT security team handles cyber intelligence, incident response, incident handling, and threat management alongside vulnerability management. They help the organization make informed security decisions and gather the information needed to adopt adequate protections.
IT security teams run vulnerability assessments to find weaknesses in systems. They also perform penetration tests to check how attackers might exploit them. These activities help you identify security issues across networks, infrastructure, and applications.
After that, teams work to fix the problems. They apply patches whenever updates are available. However, if a patch is not ready, they create mitigation plans to reduce the risk.
IT Ops
After vulnerability analysis and risk assessment, the IT Ops team applies most mitigation actions. They work to reduce risks and keep systems stable. Because of this, their role is very important.
IT Ops also maintains a complete and updated inventory of all IT components and applications. This list helps you track everything in your environment. Most organizations store this information in a Configuration Management Database (CMDB).
Clear communication between IT security and IT Ops is very important. It helps teams respond faster to security issues. In addition, it improves investigations and gives better visibility through shared data.
However, the biggest challenge is timing. SecOps and IT Ops must receive vulnerability data quickly. Then they must fix the problem without delay. Decision-makers can close this gap only when they have the right insights.
How does a CMDB help with vulnerability management?
A Configuration Management Database (CMDB) stores records of every configuration item in your IT environment. This includes hardware, software, network devices, and their relationships. Because of this, you can clearly see how systems connect.
When vulnerability data feeds into the CMDB, your security team gains better visibility. You can see which assets are affected, who owns them, and which services depend on them. As a result, you can prioritize risks more accurately.
For example, a vulnerability on a test server is very different from one on a production database. The CMDB provides the business context needed to make that decision.
Tools like Virima improve this visibility further. Its Virima Visual Impact Display (ViVID) overlays vulnerability data, incidents, and alerts on service maps. This helps teams assess impact and prioritize fixes quickly.
Why is having a vulnerability management program important?
Every organization has vulnerabilities. These are weaknesses that attackers can exploit. As a result, they may cause cyberattacks, service outages, or data theft. In many cases, attackers do not need advanced skills to exploit them.
In fact, a survey reported by Infosecurity Magazine found that nearly 60% of breaches involved an unpatched vulnerability. This shows how risky unresolved flaws can be.
Because of this, a strong vulnerability management program is essential. It helps you find and fix weaknesses early. As a result, you can prevent many security incidents before they happen.
How can IT security and Ops work together?
The security team focuses on protecting the organization. The operations team focuses on uptime and business growth. Because of this, their priorities can sometimes clash.
This difference creates what many call the SecOps gap. As a result, vulnerabilities may stay open for too long. It can also cause downtime, higher labor costs, and problems meeting compliance rules.
Effective vulnerability management helps close this gap. Modern vulnerability management solutions give both teams shared visibility. Because of this, security and operations teams can see the same risks.
A clear dashboard also helps you focus on what matters most. It shows which vulnerabilities attackers are likely to exploit. As a result, your team can fix the most urgent issues first.
Strengthening vulnerability management with Virima
Virima’s IT discovery provides the foundation for vulnerability management by building a complete, accurate inventory of your IT estate. Agentless IP-based scanning with hundreds of extendable probes covers on-premise data centers and edge devices, while API-based integrations pull in cloud assets from AWS and Azure.
ViVID™ (Virima Visual Impact Display) then overlays that vulnerability data alongside ITSM incidents, pending changes, and event management alerts onto your service dependency maps, so IT security and IT Ops teams can see exactly which business services are at risk and set remediation priorities based on real impact.
Virima also integrates with ITSM platforms, including ServiceNow, Jira Service Management, Ivanti, HaloITSM, Cherwell, Xurrent, and Hornbill, syncing asset data, configuration details, and service dependency context into your existing incident and change workflows.
Cybersecurity Asset Management rounds out the picture by identifying rogue and unmanaged devices, flagging unpatched devices and unauthorized software versions, and tracking compliance against security policies.
Paired with IT Asset Management, Virima helps you prioritize remediation based on asset criticality and business service impact rather than vulnerability severity scores alone.
Schedule a demo to see how Virima’s discovery, CMDB, and ViVID service maps work together to identify and prioritize vulnerabilities across your IT estate.






