Active vs. passive IT asset discovery: which one works better?
Shadow IT, IoT devices, and lab gear slip under the radar more often than most teams want to admit. If you don’t know a device is sitting on your network, you can’t patch it, monitor it, or lock it down. That’s the gap IT asset discovery is designed to close.
There are two core approaches: active and passive. Each tackles a different part of the problem, and most environments need both. This post walks through how active vs passive IT asset discovery works, where each method fits, and how to combine them for full coverage.
What is IT asset discovery?
IT asset discovery is the process of finding every device, application, and cloud resource connected to your network. That includes hardware like servers, laptops, routers, switches, and IoT sensors. It also includes software: installed applications, licenses, SaaS subscriptions. Cloud resources like virtual machines, containers, and storage buckets fall under its scope too, along with network components such as firewalls, load balancers, and access points.
The goal is simple: know what exists, where it sits, and what state it’s in. Without that baseline, security patches go undelivered, compliance gaps stay hidden, and incident response starts with guesswork instead of data.
Consider a scenario that plays out constantly: your organization adds a batch of remote laptops for a hybrid workforce. Without a discovery process, some of those laptops never get security updates. Each unpatched device becomes a potential entry point.
What is active IT asset discovery?
Active discovery sends probes across the network to identify devices and pull data from them directly. Think of it as knocking on every door in a building to find out who’s home and what they’ve got inside.
Common active discovery methods include:
- Ping sweeps, which send ICMP echo requests to a range of IP addresses
- Port scanning to check open ports and identify running services
- SNMP polling, which queries devices using Simple Network Management Protocol
- Credentialed scans that log into devices with valid credentials for a full hardware and software inspection
- WMI queries that pull configuration data from Windows environments
Active scanning gives you detailed, real-time data on each device. It catches dormant and idle assets that aren’t generating any traffic on their own. It can also double as a vulnerability scan, surfacing exposed services and outdated software alongside the asset inventory.
The trade-off is network impact. Active scans generate traffic, and on congested networks that matters. Credentialed scans need secure credential management. In sensitive environments like OT/ICS, active probes can disrupt industrial control systems if they’re not scheduled during planned maintenance windows.
Real-world example: A financial institution runs credentialed active scans after market hours to inventory all trading floor workstations without touching operations during the trading day.
What is passive IT asset discovery?
Passive discovery takes the opposite approach. Instead of sending probes, it monitors the traffic devices that are already generating. That includes syslogs, DHCP requests, ARP broadcasts, and DNS queries. Over time, it builds an inventory from that data. The difference between active and passive is essentially knocking on doors versus listening from the hallway.
The big advantage is zero additional network load. That makes passive discovery safe for fragile or sensitive environments where active scanning could cause problems. It aligns with CIS Control 1 (inventory and control of enterprise assets) by providing continuous visibility without any scanning risk.
Passive discovery also catches assets that active scans sometimes miss. Devices that rarely respond to probes, or machines that only appear on the network at odd hours, eventually get picked up as their traffic accumulates. Historical data helps too. Assets missed in earlier windows surface later.
The limitation is depth. Passive monitoring collects less detail per device than a credentialed active scan. Any device that isn’t generating traffic stays invisible. A dormant backup server that hasn’t been powered on in months won’t show up until someone plugs it back in.
Real-world example: In a manufacturing plant, passive discovery captures syslogs from PLCs and HMIs without disrupting production lines. But a test server sitting offline in a rack won’t appear until it reconnects.
Active vs. passive IT asset discovery: key differences
| Dimension | Active discovery | Passive discovery |
| How it works | Sends probes and queries to devices | Monitors existing network traffic |
| Network impact | Generates additional traffic | Zero additional load |
| Detail per device | Deep — full hardware/software inventory | Lighter — traffic metadata only |
| Speed | Fast, on-demand results | Gradual, builds over time |
| Dormant devices | Detects idle and offline assets | Misses devices not generating traffic |
| Sensitive environments | Can disrupt OT/ICS systems | Safe for fragile environments |
| Credentials | Requires secure credential management | No credentials needed |
| Best for | Scheduled deep scans, vulnerability auditing | Continuous baseline monitoring, OT environments |
Why you need both: the hybrid discovery approach
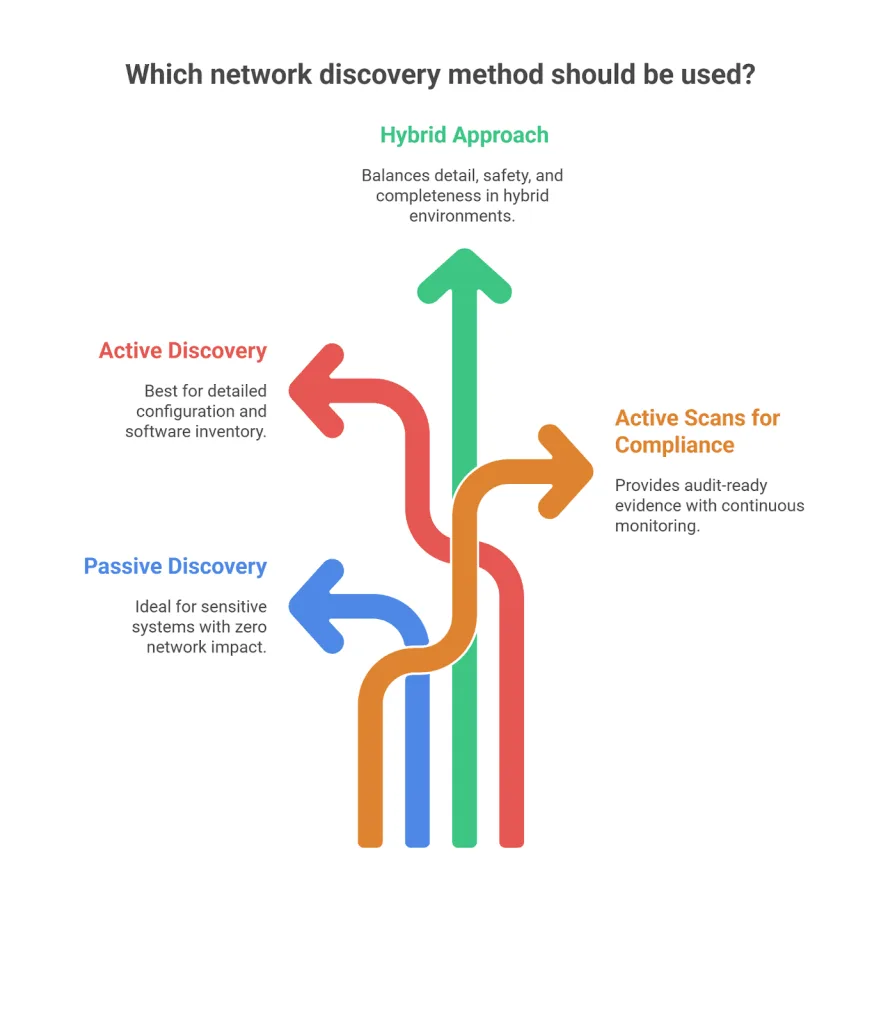
Neither active nor passive IT asset discovery covers everything on its own. Active scans catch dormant assets, forgotten servers, decommissioned endpoints still drawing power, lab gear nobody’s touched in months. Passive monitoring catches live devices the moment they connect, IoT sensors, contractor laptops, rogue access points.
The hybrid approach works in layers:
- Passive monitoring runs continuously, capturing every device that generates traffic and building a real-time baseline of your environment.
- Active scans run on a schedule (daily for servers, weekly for endpoints, quarterly for OT), filling in the gaps by probing devices that passive monitoring can’t see.
- Agent-based discovery extends the reach to remote endpoints and work-from-home devices that aren’t sitting on the corporate network.
What you get is full visibility: what’s running right now, what exists but isn’t active, and what just appeared for the first time.
What is agentless vs. agent-based discovery?
Active and passive describe what a scan listens for. Agentless and agent-based describe how it connects to devices. They’re separate axes, and the distinction matters.
Agentless discovery scans devices remotely over the network using protocols like SNMP, WMI, and SSH. Nothing gets installed on endpoints. It’s fast to deploy and low-maintenance, but it needs network line-of-sight to the target.
Agent-based discovery puts a lightweight agent on each device. That agent reports back regularly, even over the internet, tracking daily configuration changes, even when the device is off the corporate network. Deeper data, better for remote or WFH endpoints, but it means deploying and maintaining agents.
Virima supports both. Agentless scanning handles on-network assets. Agents cover Windows, macOS, and Linux endpoints that don’t routinely connect to the corporate network.
How often should you run IT asset discovery scans?
There’s no single right answer — scan frequency depends on the environment and the risk profile of what you’re scanning.
| Environment | Active scan frequency | Passive monitoring | Why |
| Core infrastructure (servers, network gear) | Daily or weekly | Continuous | High-value assets with frequent config changes |
| Virtual and cloud assets | Weekly active + cloud API sync | Continuous | Cloud footprints grow fast; APIs catch provisioning in real time |
| Remote workforce endpoints | Periodic off-hours scans | On arrival (passive) | Minimizes user disruption while catching new devices |
| OT/ICS environments | Quarterly or event-driven | Continuous (passive only) | Active scans risk disrupting production systems |
The key is layering. Passive monitoring provides the baseline. Active scans fill the gaps. Both feed the CMDB so your asset records stay current instead of drifting.
Credential management for active scans
Active credentialed scans pull the deepest asset data, but credentials need careful handling:
- Use read-only access with the minimum permissions needed
- Grant elevated credentials only for devices that require deeper inspection — patch audits, configuration checks
- Store credentials in a secure vault with access logging and automatic rotation
- Rotate scan credentials on a schedule so they don’t become a standing security liability
Getting this active scanning vs passive scanning right means your scans stay thorough without opening new attack vectors.
How Virima handles IT asset discovery across hybrid environments
Virima combines agentless active scanning and agent-based discovery in one platform, giving teams a unified view without stitching together separate IT asset discovery tools.
IT Discovery — Agentless, IP-based scanning with hundreds of out-of-the-box, extendable probes. Covers on-prem and cloud environments across Windows, Linux, Unix, and macOS. The scan engine avoids disruption with intelligent scheduling that prevents scan storms and performance hits on target devices.
Discovery Agent — Lightweight agents for Windows, macOS, and Linux. Built for remote workers, WFH setups, and assets that don’t routinely sit on the corporate network. Agents report back on a recurring schedule, even when endpoints are communicating over the internet rather than the corporate network.
CMDB — Discovery data flows directly into Virima’s CMDB, automatically creating and updating CI records with hardware specs, installed software, and relationship data. For assets and data outside discovery’s reach, Virima also supports structured CSV imports and manual entry to keep the CMDB complete.
ViVID™ — Once assets are discovered and mapped, ViVID visualizes the dependencies between them with dynamic, filterable service maps. Open incidents, pending changes, and known NVD vulnerabilities overlay directly on the maps, so change managers and incident responders see full context before touching a change request.
Service Mapping — Uses machine-learning techniques from Virima Discovery to map connections between applications, infrastructure, and business services automatically. Change managers and incident responders get a dynamic dependency view instead of a static diagram.
ITAM — Tracks the full lifecycle of discovered hardware and software, from procurement through disposal. Covers license compliance, ownership records, lifecycle status, and financial governance.
What sets Virima apart: the agentless-first approach. Many discovery tools require agents on every endpoint, which adds security and credentialing overhead. Virima scans without agents by default and only deploys them where they are genuinely needed, such as remote endpoints, persistent monitoring, or devices behind strict firewall rules.
Want to see it in action? Request a demo to explore how Virima’s hybrid discovery gives you complete visibility across on-prem, cloud, and remote environments.
FAQs
- How does IT asset discovery feed your CMDB?
Discovery’s main output is CMDB data. Every asset that gets discovered — with its configuration, relationships, and software inventory — flows into the CMDB to form a single source of truth for IT operations.
Without automated discovery, the CMDB decays fast. Manual updates can’t keep up with cloud provisioning, device turnover, and daily configuration drift. Virima’s discovery feeds directly into the Virima CMDB, keeping CI records accurate so that change management, incident response, and compliance audits run on real data rather than last quarter’s spreadsheet.
- How does IT asset discovery detect shadow IT?
Shadow IT is any device, app, or cloud service employees use without IT’s approval. Active scans find unknown devices by probing IP ranges. Passive monitoring picks up traffic from devices that weren’t supposed to be there. Between the two, most shadow IT surfaces within a few scan cycles.
- How does IT asset discovery improve security and compliance?
Discovery shows security teams what’s exposed: unpatched servers, outdated software, unauthorized devices. Frameworks like CIS Controls, NIST, and ISO 27001 all require an accurate asset inventory. Automated discovery satisfies that requirement continuously instead of relying on a quarterly spreadsheet that’s stale by the time it’s done.
- What’s the difference between IT asset discovery and IT asset management?
Discovery answers “what do we have?” — it finds devices, software, and cloud resources. IT Asset Management answers “how do we track it?” — covering lifecycle, ownership, contracts, and license compliance. Discovery feeds asset management. Without it, ITAM records go stale because manual updates can’t keep pace.
- How do you choose the right IT asset discovery tool?
Look for coverage across hardware, software, cloud, and network devices. Check whether it supports both agentless and agent-based scanning for hybrid environments. Make sure discovery data flows into your CMDB and ITSM tools without manual exports. Favor tools that scan agentlessly by default and only add agents where truly needed.