Strategy And Risk Management With CSAM
Cybersecurity risk management isn’t a one-time audit. It’s an ongoing cycle of identifying what you have, figuring out how it’s exposed, and putting controls in place before a breach forces your hand through a structured risk assessment process.
That cycle starts with your assets. Risk assessment means looking at your network and data assets against your current threat landscape and whatever regulatory requirements apply to your organization, forming the foundation of a quantitative risk assessment approach.
The results tell you which controls to deploy based on the assets, vulnerabilities, and attack techniques you’re actually dealing with. And the stakes are high — the average cost of a data breach is $4.44 million globally.
Cybersecurity asset management (CSAM) gives your team a structured way to identify, classify, assess, and manage every IT asset tied to your security posture. When your asset inventory is accurate and current, your risk decisions reflect what’s actually in your environment, not what someone documented six months ago.
This article breaks down what CSAM involves, why skipping it creates real operational risk, and how to build a practice that manages cyber risks effectively.
What is cybersecurity asset management?
Cybersecurity asset management (CSAM) is the process of identifying, classifying, and managing IT assets with a security lens. It’s a focused subset of IT Asset Management, where ITAM tracks the full lifecycle of assets for cost and compliance purposes, CSAM zeroes in on the security implications.
Think of CSAM as the security layer of your broader IT risk management framework. It ensures every device, software instance, and cloud resource is accounted for from a threat and vulnerability standpoint.
The goal: maintain a complete, current inventory of every device and software instance in your environment so your team can perform risk assessment, spot vulnerabilities, manage assets effectively, and strengthen security posture over time.
Without that inventory, you’re reacting to threats blindly.
How does CSAM differ from IT asset management (ITAM)?
ITAM tracks the full lifecycle of IT assets, including procurement, deployment, maintenance, and retirement, with a focus on cost optimization, license compliance, and supporting risk assessment tools. CSAM narrows that scope to security. It asks which assets exist, what vulnerabilities they carry, who has access, and how they connect to critical services.
In practice, the two overlap heavily. An asset that’s untracked in your ITAM system is also invisible to your security team. Tools like Virima handle both: IT discovery feeds asset data into your CMDB and your security workflows, so your ITAM and CSAM programs share a single source of truth. ITAM plays a direct role in risk management by ensuring every asset is accounted for before security controls are applied.
What happens when you don’t prioritize cybersecurity asset management?
The biggest risk is simple: you don’t know what you don’t know. Organizations without a CSAM practice often can’t answer basic questions. Where do our assets sit? How are they connected? Who has access, and at what permission levels? Without those answers, your security team is working with incomplete information.
Poor CSAM creates real consequences and limits your ability to implement effective risk reduction strategies. In fact, organizations take an average of 241 days to identify and contain a breach. A breach that takes down essential data or systems can halt operations entirely. Beyond the immediate disruption, you’re looking at reputational damage, regulatory fines, and recovery costs that compound fast.
The risks extend to endpoints your team doesn’t control, introducing concerns similar to health and safety risks in physical environments. Malware from a workplace network can follow an employee’s personal device home.
That infection can lead to identity theft, and the liability often lands back on the employer. Proactive asset discovery reduces breach exposure by surfacing those blind spots before attackers find them.
Without a clear asset inventory, you can’t prioritize your defenses or apply the right control measures where it matters most. You’re guessing which devices need protection, which servers carry the most risk, and where to deploy your security budget. That guesswork wastes money and leaves gaps that attackers can exploit.
Why cybersecurity asset management matters for risk assessment
CSAM matters because you can’t protect what you haven’t inventoried or assign an accurate risk rating to your assets. Understanding your assets, where they sit, and how they’re used, lets you assess their value and focus your IT risk assessment on what actually moves the needle.
It starts with mapping your digital footprint: hardware, software, applications, data, and cloud resources, often visualized using a risk matrix. From there, CSAM helps you identify risks specific to each asset and determine where security investments will deliver the most protection per dollar. Keeping that asset inventory secure is a continuous effort, not a project with an end date.
What role does a CMDB play in cybersecurity asset management?
Your CMDB is central to any CSAM practice, especially in managing every information system component and its dependencies. It stores every configuration item (CI) in your environment along with the relationships between them: which servers support which applications, which applications support which business services, and which dependencies create single points of failure.
When a vulnerability is disclosed, a well-maintained CMDB tells your team exactly which assets are affected and what downstream services are at risk. Without it, your incident response team is manually tracing dependencies during an active threat.
That’s the worst time to be discovering your own infrastructure. Virima’s CMDB, fed by recurring scheduled scans, keeps this data current so your risk assessment is based on what’s actually deployed, not what was there months ago.
The quality of your risk assessment depends on the quality of your CMDB data. Virima’s discovery uses machine-learned relationship mapping to build dependency data automatically, which means the CMDB reflects actual infrastructure relationships rather than manually documented assumptions that go stale the moment something changes.
What constitutes cybersecurity asset management?
CSAM requires a mix of processes, tools, and people working together within a structured management plan. The specifics vary by organization, but every effective CSAM practice covers these core areas.
1. Discovery and protection of devices
Proactive discovery is the foundation for identifying potentially harmful effects of vulnerabilities across your network. You need to know every device on your network before you can secure it. That means running regular IT asset discovery scans, assessing each device for vulnerabilities, and securing exposed endpoints with segmentation, quarantine, or firewall rules to block unauthorized access.
2. Cloud security
Cloud environments add complexity because assets spin up and down constantly. CSAM requires visibility into every cloud-based service, application, and workload, including those running with insecure configurations or inadequate access controls.
Virima’s cloud environment management tracks cloud assets across AWS and Azure alongside your on-prem inventory, so your security team sees one unified view instead of toggling between consoles.
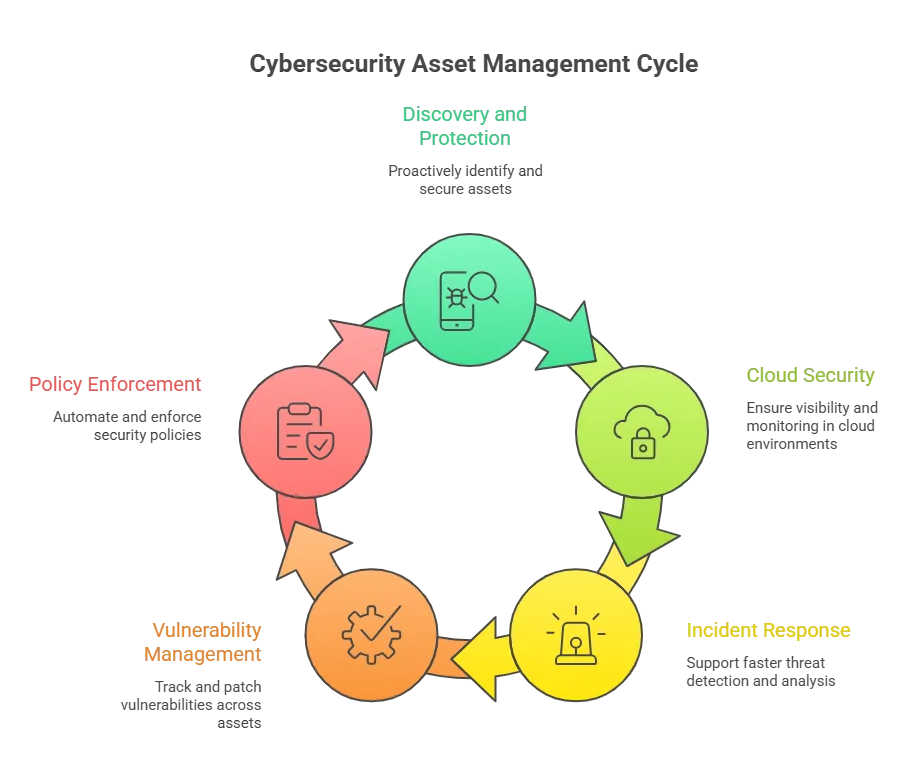
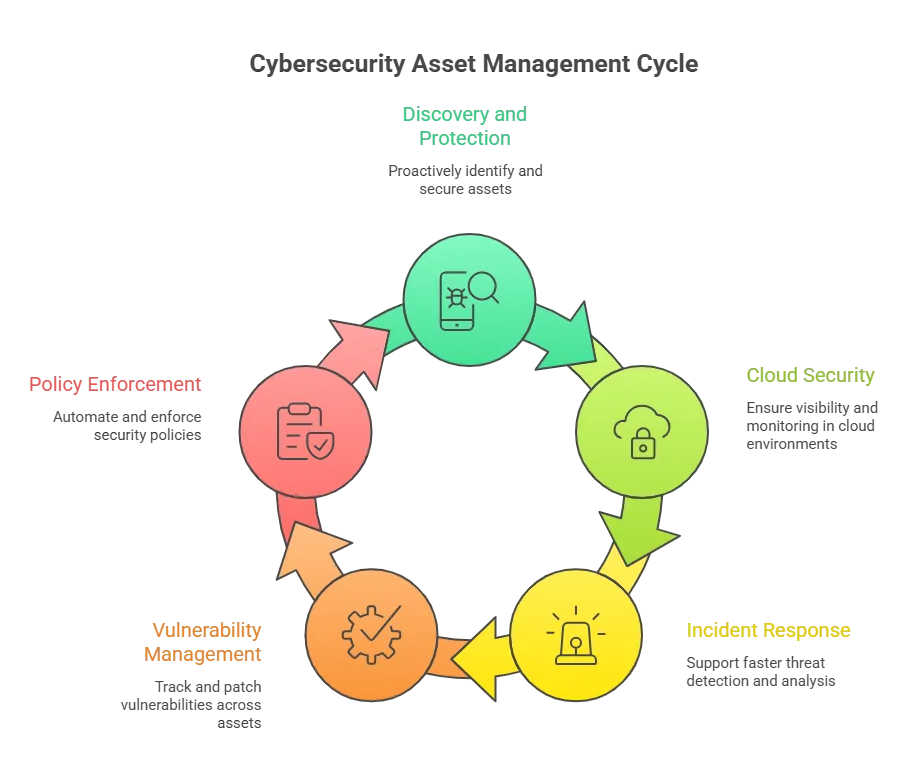
3. Incident response
CSAM feeds directly into threat detection and incident response, enabling faster conducting risk evaluations during active threats. When your asset inventory includes dependency data, your IR team can quickly identify which systems are affected by a threat, assess the blast radius, and quarantine suspicious activity before it spreads.
Service mapping combined with ViVID™ makes this faster. ViVID overlays active incidents and vulnerability data onto your dependency maps, so instead of manually tracing connections during an incident, your team can see which business services depend on the compromised asset, whether related vulnerabilities exist on connected systems, and prioritize response based on risk assessment.
4. Vulnerability management
Vulnerability management depends on knowing what’s running where and supports managing risk across all assets. Unpatched software on a device you didn’t know existed is exactly the kind of gap that attackers exploit. CSAM ensures every asset is tracked so your patching process has full coverage and the right people get notified when new vulnerabilities surface.
Virima supports this through NVD-based vulnerability lookups on discovered assets, flagging known vulnerabilities tied to the software and firmware your discovery scans have identified, at no additional cost.
5. Continuous policy enforcement
When a new device joins your network and matches an active policy profile, it should be protected automatically. Effective CSAM gives you visibility into every resource regardless of when or how it was added, and tracks how security policies were applied and enforced across the asset lifecycle.
How often should you update your cybersecurity asset inventory?
Your asset inventory should be updated continuously, not quarterly or annually, to maintain an accurate level of risk at all times. Environments change constantly with new devices, cloud instances, software deployments, and configuration changes. A quarterly scan means three months of blind spots.
Virima’s recurring scheduled scans run on configurable intervals per subnet, keeping your CMDB current without manual effort. The goal is a living inventory that reflects your actual environment at any given time, so your security risk assessment is never based on stale data.
Why automated discovery alone isn’t enough for risk assessment
Automated scans catch hardware, software, configurations, and network relationships. But they can’t tell you who owns an asset, how critical it is to the business, what SLAs apply to it, or whether it’s scheduled for decommissioning. That context matters for risk assessment because two servers with the same vulnerability carry very different risk profiles if one supports a customer-facing payment service and the other runs an internal test environment.
Virima’s Autonomic Social Discovery (ASD) fills that gap. ASD automates the process of gathering human knowledge that discovery probes can’t reach, including asset lifecycle status, ownership, business criticality, and policy assignments. It assigns a Service Value Rating (SVR) to each asset, which helps your team set remediation priorities, attribute the right policies, and define SLAs based on actual business impact rather than guesswork.
Virima is independently certified for AICPA SOC 2 Type 2 audited controls, which means its own data handling processes around security, availability, confidentiality, integrity, and privacy have been evaluated by an independent auditor. For teams building a CSAM practice that needs to satisfy compliance requirements, that certification removes a layer of vendor due diligence.
Strengthening risk assessment with cybersecurity asset management
A cybersecurity risk management strategy without asset management is incomplete. If your team can’t identify and track every asset, vulnerabilities go unnoticed, and incident response slows down. Building a CSAM strategy into your broader cybersecurity program closes those gaps.
Here’s what a mature CSAM practice delivers:
1. Improve security posture
Start by building an inventory of your critical systems and mapping the dependencies between them. This baseline reveals gaps where automation alone isn’t enough and where human oversight is needed.
Once you have that inventory, prioritize by risk. Focus on the assets that, if compromised, would cause the most operational damage. Virima’s ViVID™ (Visual Impact Display) goes beyond standard service dependency maps. It overlays ITSM incidents, pending changes, and NVD vulnerability data directly onto your service maps, so your team can see which assets carry open vulnerabilities, which have active incidents, and how those assets connect to upstream and downstream business services. Risk prioritization becomes visual and context-rich instead of spreadsheet-based.
2. Reduce the risk of a breach
Breach prevention comes from staying current on threats, on your own asset inventory, and on the controls you have in place. Use continuous discovery to detect new assets as they appear, monitor for configuration drift, and respond quickly when something looks wrong.
3. Improve business continuity and disaster recovery
CSAM provides the asset and dependency data your business continuity and disaster recovery plans depend on. A thorough risk assessment should include your asset inventory with dependency mapping, data classification tied to specific assets, gap analysis between your controls and your exposure, and ongoing testing to verify that those controls hold up.
4. Create a more secure environment
Threats span everything from commodity phishing to advanced persistent threats deployed by organized groups. CSAM helps your team identify and address security risks across every connected device, application, and service. Ongoing visibility into your network and data environment is what turns a reactive security risk assessment into a proactive one.
How Virima supports cybersecurity risk assessment
CSAM is only as effective as the data it runs on. If your asset inventory is incomplete or stale, every downstream security decision, from risk assessment to incident response, starts on shaky ground.
Virima gives your team an asset inventory built by agentless and agent-based discovery that spans on-prem, cloud, and hybrid environments. Cloud assets like AWS EC2 instances and Azure virtual machines sit alongside physical infrastructure in your CMDB, giving your security team a single consolidated view. Virima runs within cloud environments for application discovery and dependency mapping, and ViVID™ layers NVD vulnerability data and ITSM incident records onto those dependency maps so your team can assess cybersecurity risk in the context of actual business service impact.
On the operational side, Virima ties incidents and problems back to the specific assets involved through its ITSM integration, giving your IR team immediate asset context when responding to threats. Change management workflows backed by ViVID™ service maps help your team identify stakeholders and assess potential risks before applying changes, and configuration management capabilities help ensure systems stay aligned with your internal security policies and compliance requirements.
Schedule a demo to see how Virima’s IT discovery, automated CMDB, ViVID™ service mapping, and NVD integration work together to strengthen your cybersecurity risk assessment.