Asset management vs. configuration management
Asset management and configuration management look like separate disciplines from the outside. Different teams run them, different processes govern them, and the people who specialize in each often speak different languages. But Configuration Items (CIs) are still assets, and assets still get configured.
Asset management vs. configuration management: Is it really one versus the other? Masters of asset and configuration management appear to travel in different circles, with different processes to manage their practice, even speaking different languages. But Configuration Items (CI) are still assets and assets are thus configured. In many cases, yes. The distinction becomes especially clear in cloud environments, where building an AWS configuration management database requires tracking not just asset inventories but also the constantly changing configurations, security groups, and service relationships that define cloud infrastructure.
So what actually separates these two practices, and why do organizations treat them like they have nothing in common?
This guide covers both, shows where they overlap, and makes the case that modern IT teams can’t afford to run one without the other. In fact, the need for alignment is becoming more urgent as environments grow more complex. According to over 80% of IT leaders, visibility across assets and configurations is critical to reducing operational risk.
What is IT asset management?
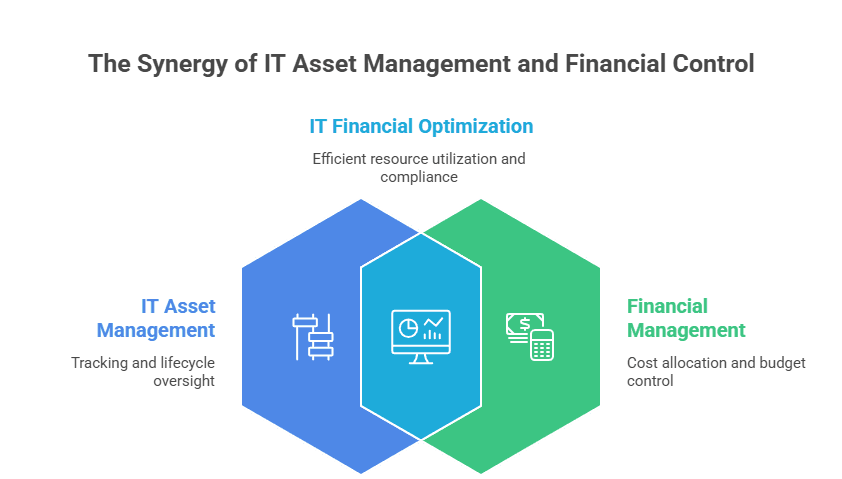
IT Asset Management, as a practice, takes responsibility for managing IT-related assets or service assets in IT Service Management (ITSM) terms. Structuring IT asset management roles and responsibilities across the ITAM practice ensures that financial tracking, lifecycle management, and compliance are owned explicitly rather than assumed.
In IT asset management, include all infrastructure, personal computing, and software assets, focusing on understanding IT’s investment in contract and financial aspects. Teams running bundled PSA platforms like Autotask asset management often handle the financial tracking side well but lack the configuration-level depth that a standalone ITAM and CMDB combination delivers.
IT Asset Management (ITAM), as a practice, takes responsibility for managing IT-related assets or service assets in IT Service Management (ITSM) terms. In IT asset management, include all infrastructure, personal computing, and software assets, focusing on understanding IT’s investment in contract and financial aspects. Legacy vendors like IBM IT asset management address the financial and inventory side of ITAM effectively, though bridging into configuration management typically requires a dedicated CMDB with automated discovery and relationship mapping that IBM’s platform does not natively provide at the depth modern IT demands.
A centralized group within IT, like the help desk or technology services group, typically manages software licenses as they impact all users in the organization. The goal is to ensure that every employee has access to only those programs he needs while avoiding any over-allocation of licenses that would result in unnecessary costs. HaloITSM customers handling license management through their service desk can extend this capability with discovery-backed Halo asset management from Virima, which automatically detects installed software across the estate and reconciles usage against entitlements within the Halo workflow.
ITAM sits on the business side of IT ownership. It answers the money questions:
- How much did we spend on this infrastructure?
- Are our software licenses properly allocated?
- When does this equipment need to be replaced?
Organizations typically handle IT financial management in one of two ways:
- Silo-based financial management: Tracking costs by infrastructure type (servers, networking, software)
- Service-based financial management: Grouping total asset costs by the services they support
ITIL asset and configuration management principles cover the entire asset lifecycle, from procurement or lease through assignment, ongoing operations, and eventual retirement. ITAM tracks each asset’s location and usage throughout, and it manages proper depreciation of capital assets along the way.
Why asset management matters
ITAM keeps your hardware and software inventory honest. It makes sure your business holds only the licenses it actually needs, cutting waste and avoiding compliance risk. Here are the core activities involved.
Tracking asset locations and states through an asset register
A good asset register tracks where each piece of equipment is located and what its state is. For example, it can indicate whether an employee or department still uses a computer or if it has been decommissioned. The register also tracks software licenses allocated to specific computers or user accounts. Building that register systematically starts with an IT asset management checklist that defines what to track, how to tag, and when to audit, ensuring the register remains accurate and complete as the environment evolves.
The register also tracks software licenses allocated to specific computers or user accounts. Some organizations build their initial register using SharePoint IT asset management lists and custom columns, which handles basic location and state tracking but lacks the automated discovery, relationship mapping, and configuration-level depth needed to bridge into true configuration management.
Managing software licenses
A centralized IT group, typically the help desk or technology services team, owns software license management. Their job is making sure every employee can access the tools they need without over-allocating licenses that quietly inflate costs.
Managing end-user devices
IT departments need to manage their organization’s PC and mobile device inventory. This includes making sure that employees are using the right equipment for their roles and ensuring that devices are secure, backed up, and properly maintained by employees. Some IT teams rely on IT Glue asset management for centralized device documentation and credential storage, though the distinction between documentation and true configuration management becomes critical as environments scale and compliance requirements tighten.
Open-source tools likeSnipe asset management handle physical asset and device inventory effectively, but the gap between asset tracking and configuration management becomes apparent when teams need CI-level detail, relationship mapping, and ITSM integration that purpose-built CMDB platforms deliver.
Some IT teams rely on IT Glue asset management for centralized device documentation and credential storage, though the distinction between documentation and true configuration management becomes critical as environments scale and compliance requirements tighten.
Handling decommissioned assets
ITAM also governs what happens when equipment reaches end-of-life. Proper disposal processes handle data security, environmental compliance, and financial write-offs so nothing falls through the cracks.
Platforms like Maximo IT Asset Management handle this depreciation and physical lifecycle well, but bridging the gap into configuration management, where CI relationships and service dependencies matter, typically requires a dedicated CMDB and discovery platform.
What is configuration management?
Configuration management sounds like it overlaps with asset management, and in some ways it does. But the focus is different. Configuration management cares about how service assets are used and set up, not about their costs, contracts, or ownership.
Here is what configuration management tracks for each service asset:
- Usage type: Is this a personal device or an infrastructure component?
- Connected assets: What else is it linked to?
- Supported services: Which business services depend on it?
- Relationships: How does it connect to other Configuration Items (CIs)?
- Technical configuration: OS, patches, memory, storage, network settings
Configuration management is a technical practice
ITAM is primarily a business process. Configuration management, by contrast, is a technical and engineering practice. From an ITSM perspective, two aspects matter most:
- Service configuration: Which assets make up an operational service, and how they connect
- Item-level configuration: The technical setup of each item, including its operating system, patch level, memory, and disk capacity
Both feed into effective IT operations, just in different ways. Service configuration helps teams figure out where to focus. When a CI goes down, operators need to know which services it supports and how much redundancy exists before they can gauge the real impact.
Key configuration management activities:
- Identifying configuration items in the CMS
Configuration management maps out the components of an application or system, how those components relate to each other, and how they are set up to work together. It goes beyond tracking what exists. It also tracks what changes.
- Controlling changes to assets
Change management is a core piece of configuration management. It means identifying and controlling every change to assets, along with the supporting processes, documentation, and configurations that go with them. This discipline reaches beyond IT systems alone. It applies to any asset that needs structured management across processes and projects.
- Assessing change impact on services
Configuration management makes sure system changes get properly authorized, documented, tested, and applied. That includes setting baselines for CIs, defining their expected configurations, and watching for drift. The payoff is safer, more predictable changes across the environment.
- Simplifying dependency identification
A well-maintained CMDB holds everything you need to know about an asset: where it is, what state it is in, who owns it, and when it was last updated. It enforces consistency by configuring each asset once with predefined rules, rather than manually setting up each asset for every use case.
Without configuration management, security gaps and root cause analysis get much harder. When something breaks, you are stuck wondering whether the failure is the hardware, the patch level, or the application. Configuration management is what keeps operations consistent.
Traditional platforms like BMC IT asset management have historically separated these functions, which is one reason modern unified solutions are gaining traction.
| How does automated discovery improve configuration management? Modern ITSM platforms have made configuration management far more practical through automated IT discovery and service mapping. Automated discovery populates the CMDB with accurate, current data about every asset it finds. That frees IT teams to spend their time on data quality and building the financial and management records that discovery cannot generate on its own. |
What is service asset and configuration management (SACM)?
ITIL defines Service Asset and Configuration Management (SACM) as the practice that formally brings asset management and configuration management under one roof. SACM starts from a simple premise: these are not competing disciplines. There are two views of the same data.
SACM makes sure accurate information about assets and CIs, including how they relate to each other, is available wherever and whenever teams need it. That feeds directly into incident resolution, change management, and capacity planning. Organizations that get SACM right stop running ITAM and CM in separate silos and start treating them as two halves of one lifecycle.
Asset and configuration management in practice today
Thinking about this as “asset management vs. configuration management” misses the point. The tools available today combine both into a single, unified lifecycle.
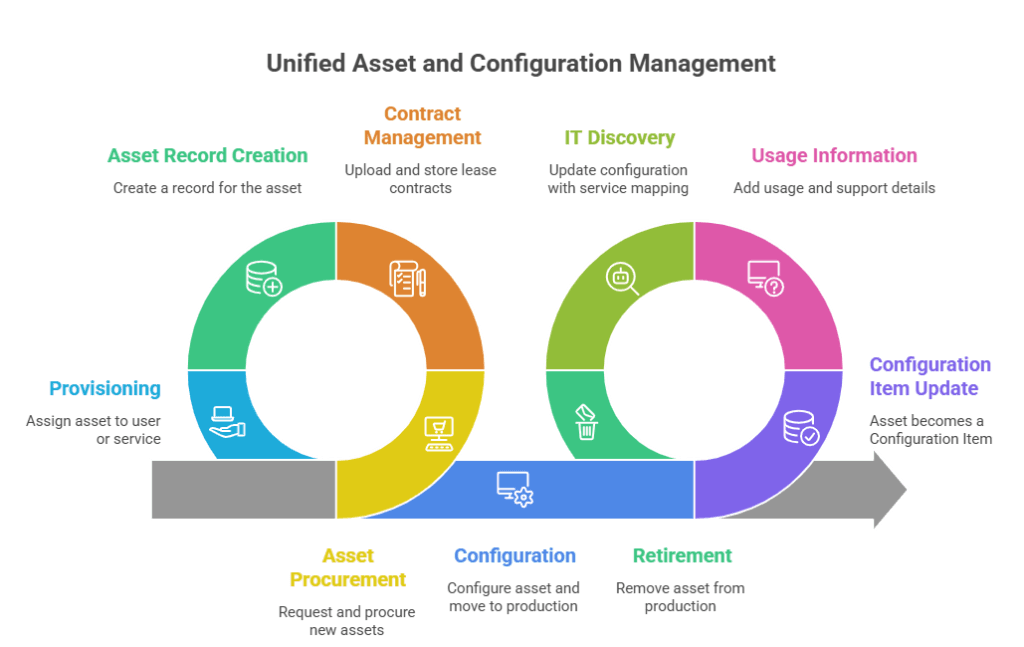
Here is how the integrated asset and configuration management process works in practice:
- An asset is requested and procured
- If leased, contracts get uploaded and stored in the contract management system
- The asset record is created
- The asset is provisioned to a user or assigned to a service
- The asset is configured and moved into production, governed by change control
- The asset record gets updated, and the item becomes a Configuration Item as well
- Usage and support information is added to the record
- IT discovery finds the asset and updates its configuration record with service mapping data
- When repair history or planned retirement warrants it, the item comes out of production
- The record shows it is no longer in use
- ITAM and ITIL procedures handle the financial retirement
- The record is updated to reflect that the asset has been retired
- Discovery no longer detects the asset
Different teams own the financial side and the configuration side, but they are working with the same record. That is what lets organizations manage every item from procurement through retirement with minimal manual effort.
Managing virtual and cloud assets
Virtual environments add another layer. Each virtual instance is typically treated as an asset. But environments that spin up and shut down automatically need their own rules for managing service capacity.
Once those rules are in place, the asset and configuration management platform handles adjustments on its own. Integration with cloud management tools makes this level of lifecycle management possible for virtual and cloud environments.
You need both, not one or the other
Asset management and configuration management are two sides of the same coin. One owns the financial picture, while the other owns usage and configuration. Running one without the other leaves gaps that are difficult to close after the fact. According to reports, 20-30% of IT budgets are wasted on unused or underutilized assets when visibility and control are disconnected
Running one without the other creates gaps that become configuration management database cmdb service management itsm increasingly difficult to close over time.
What tools do you need for asset and configuration management?
Getting asset and configuration management right takes tools that cover discovery, CMDB, service mapping, and lifecycle management in one platform. The toolset you choose should be able to:
- Automate IT discovery across on-premises, cloud, and hybrid environments
- Maintain an accurate CMDB with CI relationships and dependency data
- Map services visually so teams can assess change impact before making changes
- Track the full asset lifecycle from procurement through retirement
- Integrate with your ITSM platform to connect asset data with incident, change, and request workflows
Incorporating Asset Request and Form Management into this unified toolset ensures that the lifecycle begins with a governed intake process rather than ad hoc procurement. Some organizations build their initial asset register using open source IT asset management tools, which handle basic inventory and location tracking well but may lack the automated discovery and configuration management integration needed as the environment grows.
How Virima unifies asset and configuration management
Virima brings asset management and configuration management together in one platform. Virima ITAM, powered by Virima IT Discovery, CMDB, and ViVID™ (Virima Visual Impact Display) service mapping, supports the full asset lifecycle from procurement through retirement. Discovery systems engineer configuration management cm and CMDB automation handle the configuration tracking, while configurable status workflows manage each asset through stages like requested, ordered, development, production, and decommissioned.
Virima integrates with ITSM platforms, including ServiceNow, Jira Service Management, Ivanti, Xurrent, HaloITSM, and Cherwell, so asset and configuration data flows directly into your existing workflows.
With hundreds of extendable discovery probes covering on-premises, AWS, and Azure environments, Virima keeps infrastructure data current configuration management tool through recurring scheduled scans and agent-based monitoring. Configuration changes are reflected in the CMDB and ViVID™ service maps as scans complete, giving IT teams a continuously updated view of their environment.
Use Virima to track hardware and software asset age, identify license compliance gaps, flag security vulnerabilities through Cybersecurity Asset Management, and keep your CMDB accurate across on-premises and cloud environments.
Schedule a demo to see how Virima unifies asset and configuration management for your organization.