Top 10 ITSM Change Management Best Practices
Technology moves fast. Keeping IT services stable during constant change sets strong teams apart from those stuck firefighting every Monday morning. In other words, how you manage change decides how smoothly your systems run. Without a clear process, even small updates can cause big problems.
So, how do you stay in control? You need a disciplined change management process. It helps you plan, review, and roll out changes with confidence. As a result, you can improve systems without breaking what already works.
In this guide, you’ll explore 10 ITSM change management best practices based on ITIL frameworks. More importantly, you’ll learn how to apply them in real-world situations. This way, you can make smarter changes with less risk and fewer surprises.
What is ITSM change management?
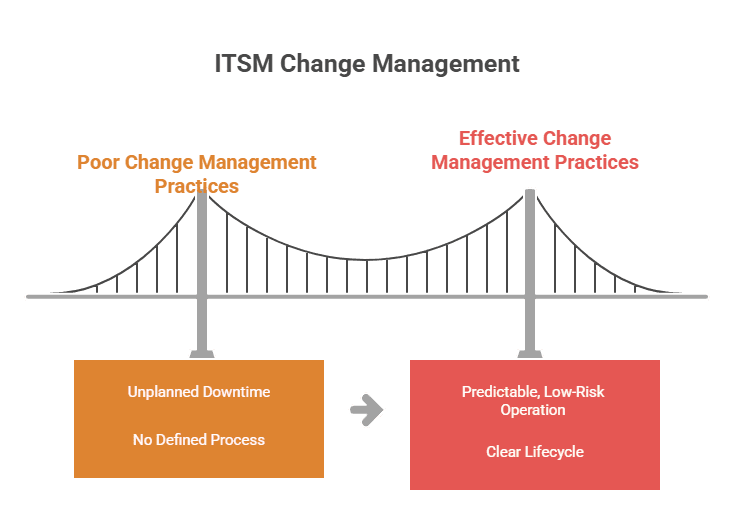
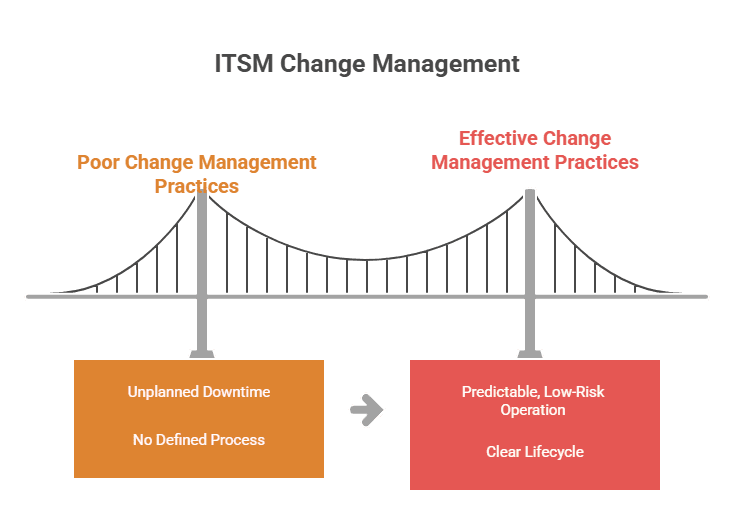
ITSM change management is a structured process for controlling modifications to the project management of IT systems, services, and infrastructure. It covers everything from minor configuration tweaks to full platform migrations. The goal is simple: implement changes that improve IT services while minimizing disruptions, risks, and unplanned downtime.
According to Gartner, 80% of unplanned downtime is caused by people and process issues, including poor change management practices. That is why a defined process is critical. Every change follows a clear lifecycle: request, assessment, approval, implementation, and review. Nothing moves forward without proper evaluation.
When done well, ITSM change management best practices turn what was once a major source of outages into a predictable, low-risk operation.
How does change management differ from change enablement in ITIL 4?
ITIL 4 renamed “change management” to “change enablement.” The shift reflects a change in philosophy. Traditional change management often acted as a gatekeeper, slowing deployments with heavy approval processes. Change enablement focuses on making changes happen faster and safer by matching oversight to risk.
The core activities stay the same: logging changes, assessing impact, getting approvals, and reviewing outcomes. What changes is the mindset. ITIL 4 pushes teams to automate low-risk changes and save the heavyweight review processes for changes that genuinely need them.
What are the three types of changes in ITIL?
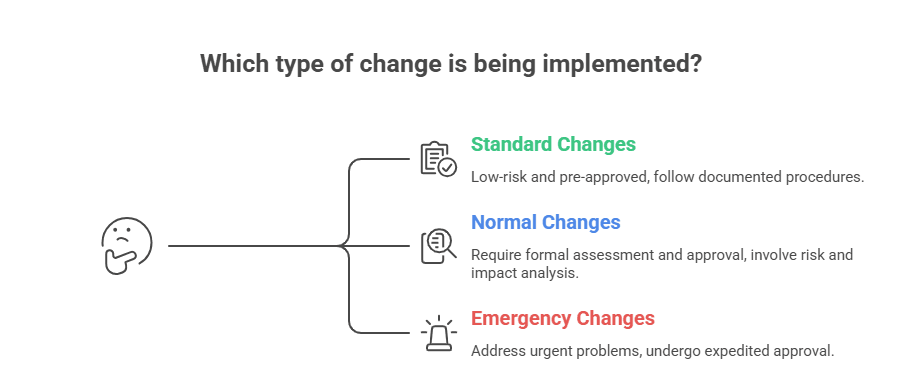
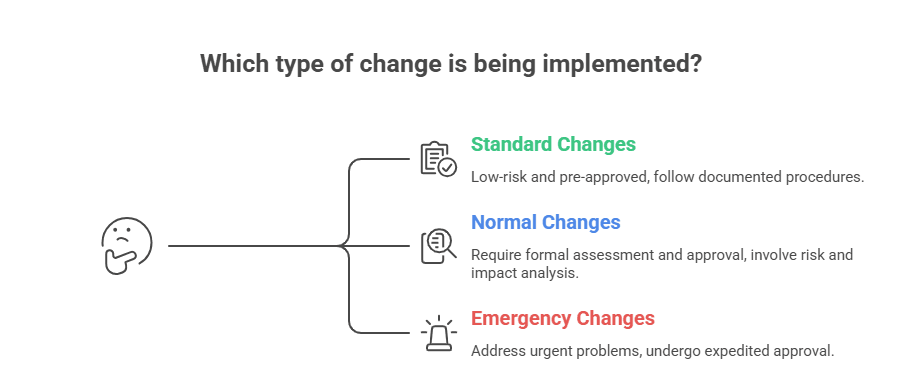
ITIL defines three change categories. Each follows a different approval path:
- Standard changes are low-risk and pre-approved. They follow a documented procedure every time. Think password resets, routine patching, or adding a user to a distribution list. These skip the approval queue entirely because the risk profile is already understood and accepted.
- Normal changes need formal assessment and approval before anyone touches production. Upgrading a database server, migrating a workload to the cloud, or deploying a new application — these all qualify. The Change Advisory Board (CAB) or a designated change authority reviews the risk, impact, and rollback plan before giving the green light.
- Emergency changes address urgent problems like security breaches or critical system failures. They go through an expedited approval process and get a full post-implementation review once the immediate crisis is resolved.
Getting these categories right prevents unnecessary bottlenecks on routine work while keeping proper controls around the changes that actually carry risk.
10 ITSM change management best practices
Now, let’s look at ten ITSM change management best practices that help teams reduce risk and maintain service stability.
1. Document every change and maintain traceability
Every change should leave a paper trail. Record what changed, who requested it, who approved it, when it happened, and why.
ITIL change management best practices call for standardized methods to log, evaluate, prioritize, and review each change. Record every modification to configuration items (CIs) in your CMDB and ensure your configuration management process keeps pace. This traceability answers three questions that come up during every troubleshooting session and every audit:
- Who made the change?
- When was it made?
- What exactly was modified?
Without that documentation, diagnosing change-related incidents turns into guesswork. And guesswork at 2 AM during a production outage is not where you want to be.
2. Break changes into smaller, manageable steps
Large, monolithic changes carry disproportionate risk. A single deployment that touches five systems at once creates five potential failure points, and if something breaks, isolating the cause takes far longer.
Break changes into smaller phases instead. Each phase gets its own testing cycle, approval, and rollback plan. If something goes wrong in phase two, you roll back phase two, not the entire deployment. This is one of those ITSM change management best practices that sounds obvious but gets ignored constantly under deadline pressure.
3. Foster transparency and stakeholder involvement
Change management falls apart when it operates in isolation. Involve stakeholders early, not just for rubber-stamp approval, but for genuine input on timing, dependencies, and risks they can see from their side of the organization.
Share change calendars so teams can flag conflicts before they become problems. Include business stakeholders in planning when changes touch customer-facing services. Run open discussions about upcoming changes in team standups or CAB meetings. When people contribute to change decisions, they own the outcome. That ownership reduces resistance and catches blind spots that the change team alone would miss.
What is the role of a Change Advisory Board (CAB)?
A CAB is a group of stakeholders, typically IT leads, service owners, security representatives, and business stakeholders, who review and approve normal and major changes. They assess risk, evaluate potential impact, and decide whether a change is ready for deployment.
The role of the CAB is evolving. Many organizations now reserve CAB review for high-risk or high-impact changes only. Standard and pre-approved changes bypass the CAB entirely. This keeps the change management process lean, where it can afford to be, while still maintaining serious oversight for changes that could cause real damage.
4. Set clear Service Level Agreements (SLAs)
SLAs define the performance standards your IT services must meet. They are your measuring stick for whether a change helped or hurt.
An effective SLA should specify service availability targets (for example, 99.9% uptime), response and resolution time commitments, escalation procedures when targets are missed, and reporting mechanisms for tracking performance.
Every change plan should reference the SLAs it could affect. If a change risks dropping below an SLA target, that risk needs to be flagged, mitigated, or explicitly accepted before the change proceeds. Too many teams treat SLAs as something the service desk worries about. In reality, SLAs should be front and center during change planning.
5. Prioritize security during change implementation
Every change is a potential attack surface. Enforce strict access controls, authentication, and encryption throughout the change process. Nobody should be able to push a change to production without proper authorization, and every step should be auditable.
Pair this with a well-maintained service catalog that documents all IT offerings, their owners, and their security requirements. When teams know exactly what services exist and who owns them, they make better decisions about which changes need additional security review versus which can proceed through the standard path.
6. Measure service level performance after changes
Track the impact of every significant change on service metrics. Monitor uptime, response time, cost efficiency, and customer satisfaction before and after each deployment.
This data tells you whether your changes are improving services or quietly degrading them. If a pattern emerges, say, changes to a specific system consistently cause latency spikes, you can adjust your process to add extra testing or staged rollouts for that system. Without this feedback loop, you are flying blind.
What is change impact analysis in ITSM?
Change impact analysis maps every system, service, and user that a proposed change could affect. It is one of the most critical steps in the change lifecycle. Skip it, and you are gambling on cascading failures across dependent services.
Effective impact analysis depends on accurate dependency data from your CMDB and service maps, visibility into the blast radius of the proposed change, and scenario modeling to assess what happens if the change fails and needs a rollback.
Virima’sViVID™ (Virima Visual Impact Display) helps change managers see the blast radius visually. By overlaying recent change data on service maps, teams can spot dependency risks and plan rollback strategies before anything gets deployed. This is where change impact analysis stops being a checkbox exercise and starts actually preventing outages.
7. Automate change workflows
Manual change processes are slow and mistake-prone. Automate the repetitive parts: ticket routing, approval notifications, status updates, and deployment triggers.
Automation generates change requests as tickets routed to the right approvers, eliminates manual handoffs that introduce delays, and frees up team capacity for higher-value work like risk analysis and planning. The goal is not to remove humans from the process but to stop wasting their time on tasks that ITSM change management software handles better.
Integrating your ITSM platform with IT discovery and IT Asset Management tools takes this further. When change tickets automatically pull CI data and dependency maps, approvers can make informed decisions without hunting for information across multiple systems.
8. Build a risk management plan for every change
Every change carries risk. The question is never whether risk exists, but how much and what kind.
ITIL best practices require a formal risk assessment before any change proceeds. Evaluate technical risk (compatibility, performance, and configuration drift), business risk (downtime, revenue impact, and SLA breach), and rollback risk (can the change be reversed cleanly if it fails?).
Map change impacts to specific CIs and services in your CMDB. When risk is quantified and tied to real infrastructure data rather than assumptions, approval decisions happen faster and hold up better under scrutiny. The teams that skip this step are the same ones writing post-mortems every quarter.
9. Conduct post-implementation reviews (PIRs)
After every significant change, run a post-implementation review. This is where the real learning happens.
A good PIR answers whether the change delivered the expected improvement, whether there were unexpected incidents or side effects, and what the team would do differently next time. Feed those insights back into your change management process so each cycle gets tighter. PIRs are also a good checkpoint for updating your CMDB with any configuration changes that happened during implementation.
The teams that treat PIRs as optional are the ones that keep making the same mistakes.
10. Track KPIs and continuously improve
You cannot improve what you do not measure. Track these change management KPIs:
- Change success rate—percentage of changes completed without incidents
- Change failure rate—percentage requiring rollback or rework
- Emergency change rate—percentage handled as emergencies (a climbing rate here is a red flag that planning and testing processes are breaking down)
- MTTR after change-related incidents—how quickly teams restore service when a change causes issues
- CSAT—end-user perception of service stability through changes
Review these regularly. If your emergency change rate keeps climbing, throwing more people at the problem will not fix it. Your planning process needs work. If MTTR is high, look at your dependency mapping and rollback procedures. Applying ITSM change management best practices means using this data to find and fix the weak links.
How Virima supports ITSM change management
Good change management depends on accurate infrastructure data, clear dependency visibility, and tight integration with your ITSM workflows. Virima provides all three.
Integration with ITSM platforms
Virima integrates with ServiceNow, Jira Service Management, Ivanti, HaloITSM, Cherwell, Xurrent, and Hornbill. Discovery data, CI relationships, and service maps feed directly into your existing change workflows. Change managers and CAB members get infrastructure context without switching tools or chasing exports from other systems.
Service mapping and dependency visualization
Virima’s service mapping automates the discovery and mapping of IT components and their dependencies. Before approving a change, IT teams can see exactly which services, applications, and infrastructure components depend on the CIs being modified. Impact analysis becomes a data-driven exercise instead of a best-guess conversation.
ViVID™ for change impact analysis
ViVID™ (Virima Visual Impact Display) overlays recent change data, incident history, and vulnerability information onto live service dependency maps. Change managers can pinpoint root causes faster during incidents and assess the blast radius of proposed changes before deployment. This accelerates MTTR and gives the CAB real data to work with during risk assessment.
IT discovery and CMDB
Virima’s IT discovery uses agentless and agent-based methods with hundreds of out-of-the-box, extendable probes to scan infrastructure across on-premises, AWS, and Azure environments. Discovery data feeds directly into the CMDB, keeping CI records accurate and current. After a change is deployed, discovery scans can validate that changes were executed as intended and detect configuration drift, so your CMDB reflects what is actually running in production.
Virima’s CMDB is backed by PinkVERIFY ITIL 4 certification for Service Asset and Configuration Management (SACM), so the underlying processes meet verified ITIL standards. Every reliable change impact analysis starts with a CMDB you can actually trust.
NIST NVD integration
Virima integrates with the NIST National Vulnerability Database (NVD) at no extra cost. During change planning, teams can cross-reference proposed changes against known vulnerabilities to make sure changes do not introduce or expose security risks.
Flexible API and codeless integrations
Virima’s flexible APIs and codeless integration options connect to existing IT toolsets without custom development. This keeps data flowing across your change management toolchain so every tool in the chain works from the same infrastructure data.
Smarter changes start with better visibility
The change management process does not have to be the bottleneck that slows IT down. With the right ITSM change management best practices and accurate infrastructure intelligence, changes become a driver of improvement rather than a source of weekend outages.
Virima gives IT teams the discovery data, dependency maps, and ITSM integration they need to plan, approve, and deploy changes with confidence. Schedule a demo to see how Virima supports your change management process from planning through post-implementation review.






