How to Prioritize Vulnerability Remediation Using CMDB Asset Criticality and Service Maps
Learn how to use CMDB asset criticality and ViVID service maps to build a vulnerability remediation priority queue that targets real business risk — not just CVSS severity ratings.
Here is a problem every security team recognizes: the vulnerability scanner returns 4,000 findings. Eight hundred of them are rated Critical or High. The team has capacity to remediate 50 vulnerabilities this sprint. Which 50?
According to IBM’s 2024 Cost of a Data Breach Report, the average breach now costs $4.88 million globally — and exploited vulnerabilities in software account for 15% of initial attack vectors, making prioritization accuracy a direct cost-reduction lever. CVSS scores alone do not provide that accuracy. A CVSS 9.8 on a decommissioned test server that is isolated from production is not the same risk as a CVSS 7.2 on a database server that sits at the core of a customer-billing service. Treating them identically — because the scanner output does not distinguish between them — is how remediation programs waste engineering capacity and leave genuine exposures unaddressed.
The answer requires CMDB data and service context. When you know which CI is affected, what service that CI supports, and how critical that service is to the business, you can build a remediation priority queue that reflects actual risk — not just numeric severity. Virima 6.1.1 provides the CMDB, the service maps, and the CVE linkage that make this possible.
What Is Asset Criticality and Why It Changes Vulnerability Priority
Asset criticality is a classification applied to a CI in the CMDB that reflects how important that asset is to business operations. Criticality typically combines factors including:
- Service tier — does this CI support a production service, a development environment, or an internal tool?
- Data sensitivity — does this CI store or process regulated data (PII, PCI, PHI)?
- Dependency depth — how many other CIs and services depend on this CI’s availability?
- Recovery complexity — how difficult and time-consuming is it to restore this CI if it fails or is taken offline for patching?
A CI with high asset criticality amplifies the effective risk of any vulnerability on it. A CI with low asset criticality dampens it.
This changes the remediation calculus completely. CVSS-only prioritization produces a flat list sorted by severity score. Criticality-weighted prioritization produces a list sorted by actual business impact — which is what remediation programs should optimize for.
In Virima 6.1.1, asset criticality is a property of the CI record in the CMDB. It feeds directly into vulnerability reporting and remediation queue construction.
How CMDB Service Maps Show Asset Criticality in Context
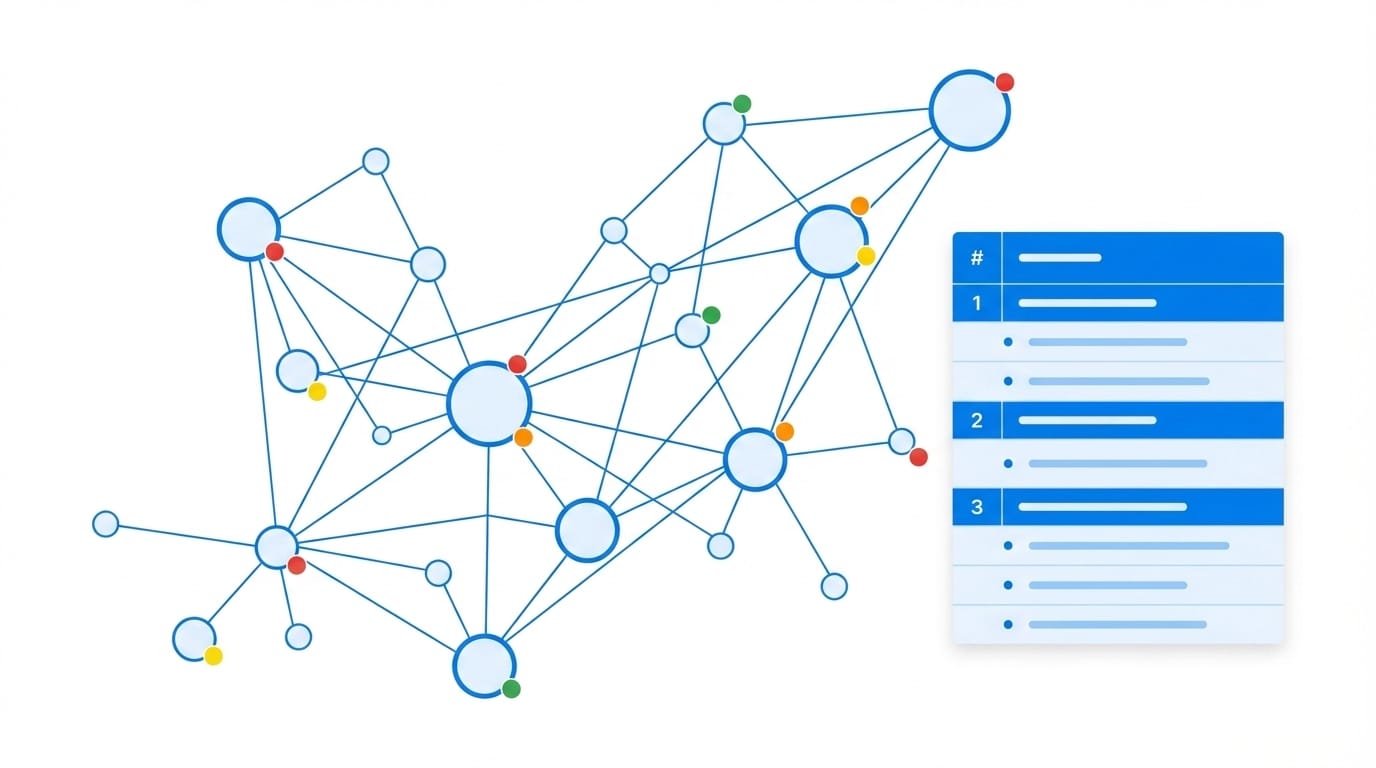
A CI’s criticality classification is informative on its own, but it becomes far more powerful when combined with service map context. Virima’s ViVID Service Mapping builds automated, dependency-aware maps of every IT service — showing exactly which CIs sit on which service maps, and how those services relate to each other.
ViVID service maps answer questions that static CMDB attributes cannot:
- Which CIs are on the critical path of a tier-1 service? These are the assets whose compromise or downtime would cascade into a service outage. Any vulnerability on these CIs is highest priority.
- Which CIs have no downstream dependencies? A vulnerable CI that supports no other services and hosts no regulated data is a lower remediation priority, regardless of CVSS score.
- What is the blast radius of a given vulnerability? If a CI is compromised, ViVID shows which other CIs and services would be affected — giving the team a clear picture of the potential damage scope before committing to a patch schedule.
Service maps also surface lateral risk: a CI might not be inherently critical, but if it connects to a critical CI through a trusted network path, its vulnerability becomes a pivot risk. ViVID makes those connections visible.
Combining CVE Severity with Service Map Context in Virima
Virima 6.1.1 overlays CVE data directly onto ViVID Service Maps. This is not a report you run separately — it is a live view that shows vulnerable CIs within the context of the services they support.
When a new CVE is correlated to a CI (via NIST NVD integration and CPE matching), the following data is immediately available:
- CVE ID and CVSS score — the severity baseline
- Affected CI — the specific configuration item running the vulnerable software version
- CI asset criticality — from the CMDB record
- Service map position — where this CI sits in the ViVID service dependency map
- Downstream dependencies — other CIs and services that depend on the affected CI
Combined, these data points allow the security team to calculate an effective remediation priority that accounts for severity, criticality, and service context simultaneously.
The result: a CVE with CVSS 6.5 on a CI that is the sole dependency of a tier-1 revenue service rises above a CVSS 9.0 on an isolated test server. Virima makes that ranking explicit and defensible — not a judgment call, but a data-driven output.
Step-by-Step: How to Build a Vulnerability Remediation Priority Queue Using Virima
Step 1: Run a discovery scan and CVE correlation.
Virima’s discovery engine identifies all software versions across the environment and automatically correlates them against the NIST NVD. Every CVE match is linked to the affected CI in the CMDB.
Step 2: Filter by CVSS severity threshold.
Start with Critical and High CVEs (CVSS 7.0+). This narrows the working list to findings that warrant immediate attention based on severity alone.
Step 3: Apply asset criticality overlay.
Within the Critical and High CVE list, sort by CI asset criticality. CIs classified as business-critical rise to the top. CIs in non-production or isolated environments move down.
Step 4: Cross-reference with ViVID Service Maps.
For the top-ranked CIs, open the ViVID service map. Confirm which service maps the affected CI sits on and review downstream dependencies. CIs on tier-1 service maps with broad downstream impact receive highest remediation priority.
Step 5: Assign remediation ownership from the CMDB.
Each CI record contains ownership information. Assign remediation tasks directly to CI owners, with the CVE, affected software version, and service map context included in the assignment.
Step 6: Track remediation progress against the priority queue.
As vulnerabilities are patched, the CMDB updates. The remediation priority queue reflects current state after each discovery cycle, so the team always works from a current list.
How This Reduces Remediation Noise and Focuses Engineering Time
A CVSS-only remediation program generates constant noise. Every Critical finding demands immediate attention — even when most Criticals in the environment sit on assets with no meaningful business exposure. Engineers burn cycles patching low-impact assets while high-impact vulnerabilities age.
Virima’s CMDB-and-service-map approach cuts that noise by applying a relevance filter. The team still sees all vulnerabilities. But the priority queue surfaces the ones that genuinely matter to the business — and the context to explain why.
Measurable outcomes from this approach include:
- Reduced time-to-patch for high-business-risk CVEs — because they surface at the top of the queue, not buried in a flat severity list
- Fewer remediation cycles wasted on low-impact findings — engineering time concentrates where risk reduction is highest
- Defensible audit trails — every remediation decision traces back to CMDB data and service map context, not manual judgment
- Better sprint planning for security and ops teams — the priority queue maps to actual business risk, making it easier to scope remediation work per sprint
Conclusion
CVSS scores are a starting point, not a remediation strategy. Genuine vulnerability prioritization requires knowing which assets are affected, how critical those assets are to the business, and what would happen to services and dependencies if those assets were compromised.
Virima 6.1.1 provides that context automatically — through CMDB asset criticality, NIST NVD CVE linkage, and ViVID Service Maps working together. The result is a remediation program that targets the vulnerabilities that actually threaten the business, in the order that reduces risk fastest.
Frequently Asked Questions
Can Virima integrate with a dedicated vulnerability scanner to enrich its findings with CMDB data?
Yes. Virima can ingest vulnerability findings from external scanners and enrich them with CMDB CI context, asset criticality, and ViVID service map data. This allows teams using dedicated scanners to benefit from CMDB-backed prioritization without replacing their existing scanning tools.
How does Virima handle vulnerabilities on assets that are shared across multiple services?
When a CI appears on multiple ViVID service maps, Virima applies the highest criticality tier across all associated services. A CI shared between a tier-1 and a tier-2 service is treated as a tier-1 asset for vulnerability prioritization purposes.
Does the priority queue update automatically as new CVEs are disclosed?
Yes. Each scheduled discovery and CVE correlation cycle updates the vulnerability data for all CIs in scope. New CVEs disclosed in the NIST NVD appear in the next correlation run and are automatically assigned to affected CIs — so the priority queue reflects current threat intelligence without manual intervention.