Trusted Runtime Truth for Agentic IT

Why “Good Data” Is No Longer Enough
AI in IT Is Only as Safe as the
Truth It Runs On
Every IT team and every AI agent working in your environment needs to answer the same questions before taking action:
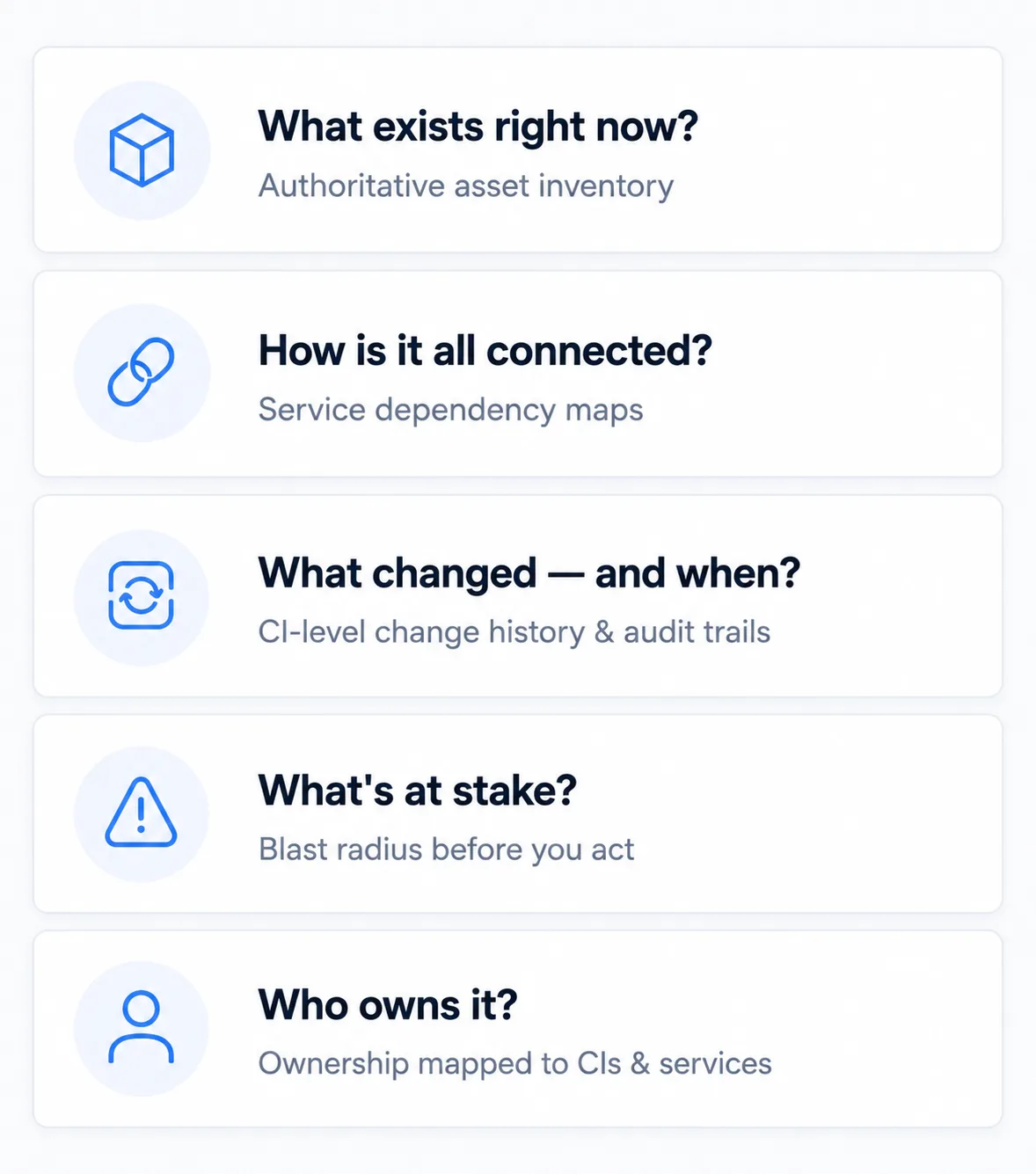
What exists in this environment right now? How are these assets and services connected? What changed — and when? What’s at stake if we proceed? Who owns this and what are the boundaries?
Most IT stacks cannot answer all five. They have workflow history. They have ticket data. Some have dashboards. But they lack discovery-sourced truth — authoritative, reconciled across sources — not what was last manually entered or even discovered just last week.
When AI agents operate on stale, fragmented, or ungoverned data, the results are failed changes, undetected blast radius, and automation that introduces risk instead of reducing it.
Good data is table stakes. Trusted Runtime Truth — live, explainable, and governed — is what Virima delivers.
Category Definition
What Is Trusted Runtime Truth?
It is the operational context layer that uniquely combines machine-driven accuracy with human context — giving IT platforms and AI agents a governed, explainable picture of your environment: assets, services, dependencies, ownership, change history, and blast radius. All sourced from authoritative, reconciled multi-source discovery.
It is not a dashboard. It is not a workflow log. It is not a point-in-time snapshot loaded manually into a spreadsheet. It is the live, accurate truth that makes every IT decision and every automated action safer and faster.
Five questions your CMDB alone cannot answer:

What exists right now?
An authoritative inventory across cloud, on-prem, remote, and virtual — with source attribution and confidence scores

How is it all connected?
Service dependency maps tied to named business services, built from your asset and infrastructure data

What changed — and when?
Change history at the CI level, with audit trails that support compliance and impact review

What could break?
Blast radius analysis before a change is approved — so teams avoid change-induced outages

Who owns it?
Ownership and accountability mapped to every CI and service, so AI agents and humans know who to engage
60min
Time to First Map
100%
Attribute authority
0
Duplicates
One scan discovers your assets, populates your CMDB with high-authority data, and maps every dependency and relationship — streamlined from start to finish.
Three Pillars of Trusted Runtime Truth
How Virima Delivers Trusted Runtime Truth
1. Discover with Authority
Trusted Runtime Truth starts with authoritative discovery. Virima reconciles data from multiple sources — agentless credential-based discovery, agent-based discovery, passive discovery, cloud APIs, and third-party security agents and endpoint management tools already deployed in your environment, and direct integrations — into a single, deduplicated operational record.
Every CI carries source attribution and confidence scores — where the data came from, how reliable it is, and how conflicts between sources were resolved. This is not visibility. This is discovery-sourced truth that teams and AI agents can act on with confidence.
- • Hardware, software, certificates, virtual machines, and cloud assets discovered across your entire hybrid estate
- • Agentless and agent-based discovery — the right approach for every environment and endpoint type
- • Source attribution and confidence scores on every CI record so you know where your data came from and how reliable it is
- • Software inventory with version and license footprint at every scan
- •Scheduled and on-demand discovery ensures data freshness
2. Understand in Context
Discovery alone is not enough. Runtime Truth means connecting every asset to its services, its dependencies, its change history, its known vulnerabilities, and its blast radius — so teams understand impact before they act. This is where machine-driven discovery and human-defined service context meet.
Virima’s ViVID™ service mapping layer builds application-to-infrastructure dependency maps from machine-learned dependencies and relationships, staying current as your environment changes. Every change to the underlying CI record is reflected in the map — without manual maintenance.
- •Service dependency maps built from machine-learned dependencies and relationships, tied to its services
- • Impact path tracing from a failing CI to the affected business service
- • ViVID™ surfaces ITSM incidents, changes, and vulnerability exposure as overlays on every map
- • Multi-tier architecture mapping from server to application to database layers
- • Blast radius scoping before change windows open
3. Govern Every Action
True governance requires strict data controls and provenance. Virima enforces this with defensible data sourcing, change tracking and auditability, and role-based access controls — so every human and AI action is backed by truth.
Every CI record is traceable to its discovery source. Every change is logged, every relationship is auditable, and every action is backed by data you can stand behind.
- •Full audit trail and change history logging on all CI records
- • Role-based access controls (RBAC) with granular permissions by team and function
- • CMDB health scoring that tracks accuracy, completeness, and data staleness over time
- • Asset lifecycle management from deployment to decommission
- • Change risk assessment that flags at-risk services before change windows open
Truth Travels With You
Trusted Runtime Truth only works if it flows to the platforms your teams already use. Virima is purpose-built to integrate with your IT platforms — not to replace your stack, but to become the authoritative context layer beneath it.
Whether your team runs ServiceNow, Jira, Ivanti, Halo, Xurrent, Hornbill, or TeamDynamix, the truth travels with you. Virima syncs discovered CIs, relationships, and service context into those platforms bi-directionally — without vendor lock-in.
Your IT operations are not trapped inside one platform’s view of reality. They are grounded in discovery-sourced truth that works across the entire stack.
ITSM Platforms
Cloud & Infrastructure
Identity, Security & Endpoint
See your environment like never before
Built for IT Leaders Who Cannot Afford to Guess
Who Is Trusted Runtime Truth For?
Strategic Decision Makers
- • Audit-ready compliance without the fire drill
- • A trusted foundation for AI and automation initiatives
- • Platform-independent context that isn’t locked inside one vendor’s ecosystem
Infrastructure & Operations Leaders
- • Approve changes knowing what’s downstream, not hoping for the best
- • Faster root cause analysis — less time in war rooms, more time preventing the next one
- • Fewer Sev-1s caused by changes no one saw coming
IT Service & Asset Management Teams
- • Stop reconciling records manually — your CMDB keeps itself current
- • Fewer audit surprises with accurate software and license data
- • Spend time improving service delivery, not maintaining spreadsheets
Technical Influencers
- • Stop debating which data source to trust during an incident
- • Troubleshoot faster with data you don’t have to second-guess
- • Automate with confidence knowing the inputs are accurate
What Industry Analysts and Customers Say
Trusted by IT Teams Who Need
Truth, Not Guesswork

EMA Research
Finally, a CMDB that Delivers on its Promise
“We use VIRIMA as our CMDB software to gather information from all our network devices such as servers, desktops, and laptops. The Discovery part of the software is very intuitive and works perfectly. We use it to manage and track assets.”
Christopher Rodriguez
IT Asset Manager in Healthcare and Biotech
Visibility Auditors Trust
“Auditors demand clear evidence of data flow and system communications. With ViVID™, we have complete visibility into every connection, helping us strengthen business continuity, prioritize critical services, and deliver the transparency auditors value.”
Robert Hanson
IT Manager and Director
at a US-based Bank
FREQUENTLY ASKED QUESTIONS
Common Questions
01. What is Trusted Runtime Truth in IT?
02.What is the difference between workflow context and Trusted Runtime Truth?
03. How does Virima deliver Trusted Runtime Truth?
(1) Discover with authority — multi-source, multi-protocol IT discovery with attribute-level reconciliation.
(2) Understand in context — ViVID™ service mapping with dependency visualization, blast radius, and ownership overlays
(3) Govern every action — explainability, auditability, secure discovery, and role-based access controls so every action is backed by verifiable data.
04. Which IT platforms does Virima work with?
Move faster. Act safely.
Get live, explainable runtime truth across your entire estate — without platform lock-in.