IT Discovery: A Complete Guide for IT Teams
Let’s begin with the three major concerns plaguing IT organizations today
- Evolving fast enough to keep up with the changing customer and technology demands
- Keeping existing services stable while facing interruptions and risks
- Staying ahead of cyber threats, securing data, and minimizing disruptions
The concerns aren’t exclusive to any single IT organization, and that’s why having comprehensive visibility into IT components is so essential. According to Flexera’s 2024 State of IT report, 82% of organizations cite managing the cost and usage of their IT assets as a top challenge — reflecting how widespread visibility gaps remain across the industry.
Viewing and understanding the interconnections and dependencies of these components can be the key determinant of successful service management practices. With developing cyber threats, being aware of your conditions with IT discovery is no longer just an option; it’s crucial.
What is IT discovery?
In simple terms, IT discovery is a process of monitoring systems to get a comprehensive view of the IT infrastructure of an organization, including applications, systems, and workloads. IT discovery helps you locate trouble areas, uncover lost or forgotten data assets, and provide critical information about the health of your IT components.
The IT discovery process involves tagging all the active and inactive assets present in your network, including hardware assets like laptops, smartphones, tablets, and all software assets. While many enterprises are slowly making it a habit to rely on advanced IT Asset Management (ITAM) platforms and tools to make the IT discovery process easier, there’s still hesitancy and reliance on manual tracking. Industry surveys consistently show that a significant share of organizations still track IT assets in spreadsheets — and those that do spend substantially more time on audit preparation and compliance remediation than those using automated platforms. According to IBM’s 2024 Cost of a Data Breach Report, the average breach took 194 days to identify — a figure that drops significantly for organizations with mature, automated asset visibility.
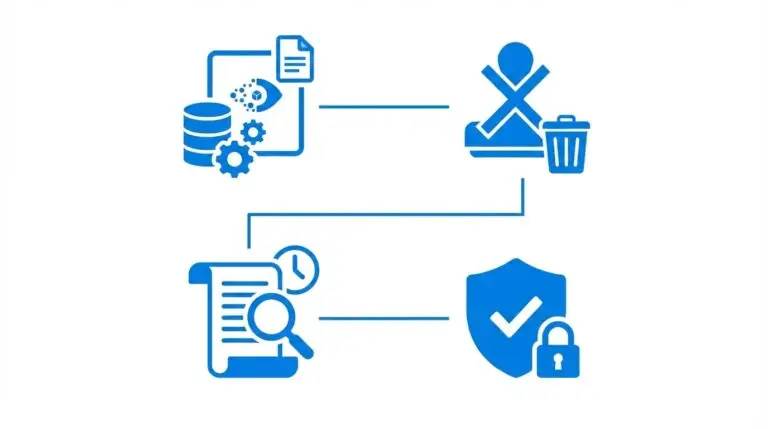
Data security, one of the most sensitive issues, is often overlooked by many organizations. IT discovery and asset management can be highly empowering in keeping data safe and sending out alerts in case of breaches. IT discovery helps you keep track of what resources you have, where they are, and what steps you need to follow to safeguard them. By identifying the IT assets owned by your organization and tracking hardware configurations and installed software on a continuous basis, IT discovery can play an essential role in making sure potential vulnerabilities are identified and prioritized for mitigation.
The modern IT discovery process eliminates the need to manually catalog all your IT assets before or after they have been deployed. With seamless, automated discovery technology, virtually all of your IT hardware and software assets are easily discovered, cataloged, and continuously tracked for configuration changes.
Some examples of physical assets IT Discovery tools can find:
- Desktop computers and laptops
- Servers
- Network and storage devices
- Tablets
- Printers
- VoIP handsets
Non-physical assets include:
- Virtual servers
- Cloud resources
- Software/applications
- OS patches
- Processes and services
- Websites
- Database servers
- Middleware
- Containers
Until recently, the IT discovery process concentrated primarily on physical assets or installed software. With the COVID-19 pandemic making virtual operations almost inevitable for organizations today, and with so much infrastructure and functionality now operating in virtual realms — either cloud or SaaS — the modern IT discovery systems include the capability to discover and monitor SaaS and cloud infrastructure.
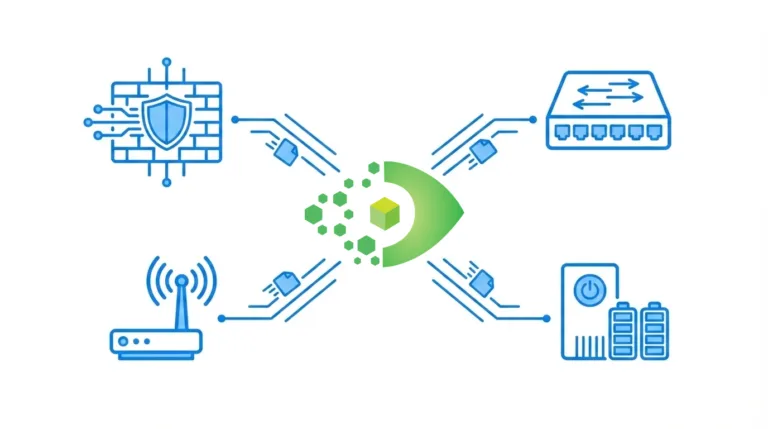
The urgency of going virtual also made the availability of real-time data mandatory for most organizations. With features like Network Discovery, which intelligently scans your organization’s network to find the assets and store the configurations of discovered devices, such as routers, switches, printers, and more. The Network Discovery feature lets you quickly find and identify the connected devices on your network and monitor your IT landscape with automated network scans.
The modern IT discovery tools also help you keep a close eye on your cloud infrastructures, cloud applications, and virtual servers and databases. Cloud asset management keeps track of every aspect of your cloud environment, including tracking your cloud asset inventory.
With features like discovery and dependency mapping, you can identify and document external dependencies of software applications like networks, storage, servers, and applications. You can also understand their interdependencies and how they affect each other. Then there’s the problem of Shadow IT, which refers to the IT components that are managed outside your organization’s control and without the knowledge of your IT department.
According to Gartner, shadow IT now accounts for 30–40% of total enterprise technology spending in large organizations — a figure that has accelerated with the rapid adoption of cloud and SaaS platforms. In such a situation, Shadow IT discovery becomes essential to identify cloud and SaaS application usage by incorporating firewall or proxy logs, and to provide risk assessment for those discovered applications.
Why do organizations need IT discovery?
To sum up, the answer to this question is that a good IT discovery tool saves you unnecessary costs and helps you mitigate risks.
IT discovery helps you get a comprehensive view and status of your IT components. It empowers your organization with baseline information that can be extended to provide support for IT service management (ITSM) practices, such as:
Asset and configuration management
IT asset management, or ITAM, is essential for keeping track of your IT assets. Asset management is crucial for your organization as it helps you evaluate when to make changes to your IT components and identify which changes to make. The two main activities of ITAM can be summed up as:
- Keeping tabs on the financial value of each asset, which entails how much value the asset is adding to the company
- Determining the right time to upgrade/retire/expire assets due to depreciation
- The problem is that these activities can be highly cumbersome, and therefore, many organizations struggle and often fail in their ITAM efforts.
- Apart from asset management, configuration management is also essential for enterprises. Enterprise assets are often deployed in complex environments, and these assets have configurations or interface dependencies that need to be detected, managed, and controlled so that your IT environment behaves the way it is supposed to.
- Configuration management is important because any change in configurations can significantly impact the performance, security, and functionality of the supported applications and the underlying IT assets.
- The requirements of the production environment can be very different from the infrastructure configured to run tests.
Your IT team must ensure that these configurations are managed correctly, which is also not an easy task.
The solution? A reliable IT discovery tool that supports asset and configuration management. Let us walk you through the details.
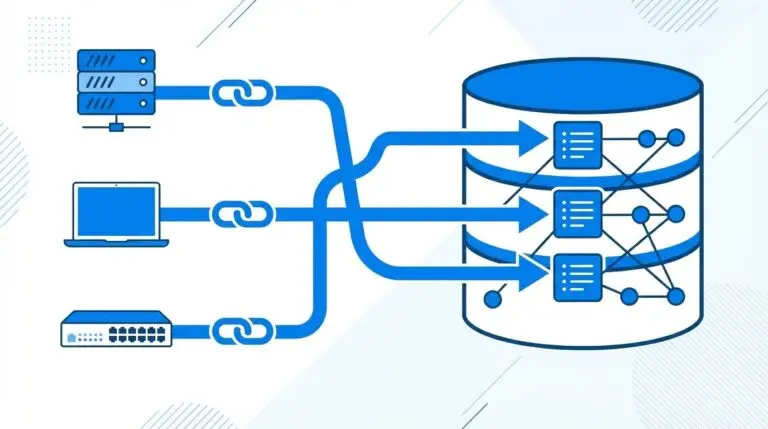
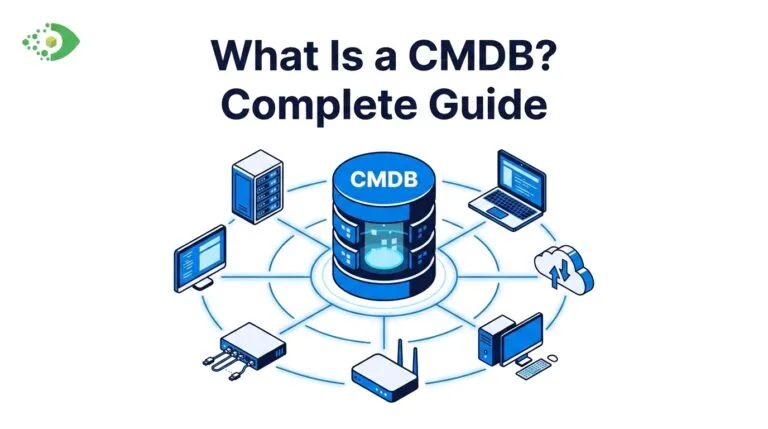
Asset and configuration management provides trustworthy and up-to-date details about your IT infrastructure to support IT service delivery and support. A reliable IT discovery tool automatically populates the Configuration Management Database (CMDB) and clearly defines the relationships between configuration items (CIs). IT discovery tools help you go beyond conventional asset management by keeping technical information on CI’s baseline, statuses, ownership, and location details.
It also helps you discover the devices that are using unlicensed software or have been improperly configured, which can result in high costs for your organization.
Change management
Change management in ITSM refers to a process that assesses and approves or rejects a proposed change and manages the change through its development and deployment.
These changes aren’t always planned. Most of the time, these changes occur as unanticipated consequences of a service interruption. A small change in the infrastructure can often escalate across your IT environment and affect multiple users due to the technology dependencies in a complex IT infrastructure environment. The types of changes in an IT environment include
- Standard changes that refer to low-risk, pre-authorized tasks
- Normal changes that can be intermediary or high-risk changes
- Urgent changes that may lead to high-risk consequences if not handled promptly
The change management process often involves countless meetings to verify the relevant data and dependencies, overlooking or completely missing crucial data points. The most essential factors for successful change management require awareness, IT Agility, and, more importantly, accuracy. A reliable IT discovery tool can be instrumental in providing these accurate data points.
When your IT teams review changes to determine the potential effects on other services and components, they can leverage the critical insights provided by IT discovery data to:
- Prevent unforeseen incidents
- Find dependencies that will require contributions from other stakeholders in making the change successful
- Determine which users will be impacted if a network/storage/server component is taken down
- Properly plan changes to minimize downtime
- Find the best maintenance window to reduce the end-user impact
- Identify the best resources to make the change effective
Once discovery data enters the CMDB from multiple sources, the reconciliation layer determines what the CMDB actually believes when sources disagree — see our guide on multi-source CMDB reconciliation for why the default model fails
Information security
With remote work being the norm in the new normal, business is regularly conducted in the cloud with file sharing and storage. This brings a huge challenge for the enterprises as they need to constantly know precisely where their assets are and where the sensitive or regulatory data resides.
With the growing interconnectivity between business processes, data is dispersed through several systems, databases, shared files, and applications, which makes security, authentication, and discretion a herculean task for enterprises.
A scheduled automated scan can reveal compliance issues with security policies (endpoint protection, patches, or antivirus) and license issues.
IT discovery is also essential for detecting access points when itemizing a network for penetration testing.
Disaster recovery
Disaster recovery (DR) involves designing IT technologies and best practices to prevent or minimize data loss and business disruption resulting from cataclysmic events like major equipment failures and power outages, cyberattacks, emergencies, criminal or military attacks, and natural disasters.
The first step to creating an effective and comprehensive IT disaster recovery plan is business impact analysis, which requires accurate, always up-to-date IT inventory data. The DR managers in organizations usually look to find that data in a single source of truth, typically a CMDB. The DR team needs to know the status in real-time to plan for continuity. That’s where IT discovery comes into the picture.
IT discovery helps your DR teams to observe the current state and identify critical dependencies that need to be accounted for in case of a disruptive event. DR teams can also use the data collected from IT discovery to recognize assets that lack the proper failover and mitigate the potential risk, therefore preventing a possible service disruption.
In cases of major disruptions where an organization might have to restore its services in a different IT environment, information from IT discovery can prove to be a vital resource in rebuilding IT services and components from scratch.
Release and deployment
The terms release and deployment are used interchangeably in service management to refer to various updates that are made in applications, including feature enhancements, security updates, bug fixes, and performance improvements.
IT discovery can help your IT team plan releases and gain visibility into whether dependencies, such as libraries and OS versions, can be established in advance and validated before new or updated software components are installed in the IT environment. It can further be used for post-verification checks after deployment and to ensure the changes are properly documented.
IT discovery challenges
Before the pandemic, many organizations had transitioned a lot of data center assets to the cloud, which may have reduced the number of physical assets to manage, but it also made it easy to spin up new environments quickly, often with less oversight than if installed within a data center. Cloud architects may claim to have a handle on what’s in the cloud, but the same can’t always be said for IT service management and IT Sec teams. Many traditional IT discovery tools just don’t have the reach to include cloud assets.
Compounding the challenges for many IT discovery tools is the pandemic’s “new normal,” which rapidly and irreversibly increased the number of work-from-home users. This means a lot of end-use compute devices, arguably the most vulnerable to security breaches, rarely, if ever, connect to the network. This also poses a monumental task for traditional IT discovery tools.
Virima IT discovery
A strong, reliable IT discovery tool like Virima can be leveraged to get visibility into the blind spots caused by dispersed corporate networks, which extend onto the cloud and into employees’ personal workspaces. Virima IT discovery can be leveraged for data center, edge, cloud, and even work-from-anywhere environments. It helps you continuously discover thousands of IT assets and maintain an accurate inventory of cloud infrastructure with multiple environments and providers.
Virima IT discovery can be deployed easily by downloading the app to a server you control and configuring the scan parameters. You can choose to run immediate scans or set a schedule to get asset discovery and dependency modeling results within a few hours, instead of weeks.
Since strong foundational IT security is crucial, Virima IT discovery is certified by AICPA SOC 2 Type 1 audited controls so that your data is transmitted securely, and only authorized devices are given access. Virima IT discovery is an IP-based, agentless tool that is easy to install and configure with automated ‘set-and-forget’ scheduling and an intelligent design that won’t flood the network with “scan storms” or affect device performance while providing comprehensive scan details that show where the IT discovery tool succeeded, where it failed, and why.
The other approaches to IT discovery involve:
Common Information Model (CIM)
The Common Information Model (CIM) provides a common standard of management information for networks, applications, systems, and services, and permits vendor extensions. CIM can be used in many ways and integrated with other management models.
Windows Management Infrastructure (MI)
Windows MI features are based on CIM and represent the latest version of Windows Management Instrumentation (WMI). It is compatible with the previous versions of WMI and provides a host of features and benefits that make designing and developing providers and clients a breeze.
Cloud discovery
This approach can be used by enterprises to collect comprehensive data about all cloud instances spanning applications, containers, databases, and related services. Cloud discovery offers a single, consolidated view of various cloud platforms and services within an enterprise.
Agent-based approach
Enterprises can deploy universal discovery agents on client or server machines to collect asset inventory information. These agents collect the required information about the assets and share it with the proxy server. The proxy server then consolidates the data and sends the information to the centralized server. This approach provides greater visibility for supporting, monitoring, and troubleshooting efforts. But the agent-based approach adds to the costs with installation, updating, and management, which, although automated, still require significant administration effort.
Agentless approach
The agentless approach doesn’t require the installation of agents for discovery. Instead, a proxy server remotely accesses and pulls information from other devices. This solution requires less manpower and depends on native, already installed OS or standard agents like SNMP, WMI, TELNET, SSH, NETBIOS, and more.
Configuring IT discovery to find network devices in subnets and VLANs
IT discovery client agents include a network discovery component called LANProbe. LANProbe gets automatically installed once the client agent is deployed on a Windows PC. Client agents help discover only network devices in the agent’s local subnet by default. Without a client agent, if there are devices in a subnet or VLAN, they won’t be discovered.
Continuous asset discovery and inventory
Continuous asset discovery and inventory help you stay on top of every cyber threat with improved asset awareness of other systems and tools. IT discovery continuously analyzes assets and traffic flows to determine asset criticality and cyber risks. It continuously examines the enterprise to discover, identify, and categorize all assets, including apps, devices, and services: managed and unmanaged, on-prem and cloud, and fixed and mobile.
Device discovery and monitoring using SNMP
Device discovery leverages SNMP to find third-party devices on the network map. SNMP traps can then be collected for these SNMP-discovered devices. Alerts for issues or notable incidents with these devices are shown on the map. This helps you in monitoring third-party devices in real-time.
IT discovery best practices and benefits
If your IT discovery and inventory management processes are not correctly defined and executed, asset data will be inaccurate. Therefore, you must ensure that you have the right tools and processes in place so that every asset is discovered and properly tracked by inventory management tools.
A few best practices to ensure that your IT discovery works efficiently.
- Deploy the discovery agent on every Windows and Mac OS endpoint device within the organization for better visibility into every device. The scanner provides high-level management, while the agent provides comprehensive details of hardware and software for every device.
- Deploy the discovery scanner on one or more subnets and ensure it has access to all the subnets from which you want to collect asset data. It ensures complete asset management.
- Single versus multiple deployments – It’s crucial for efficient asset management to reach all subnets. Router integration will be required if you have multiple connected subnets. You can pull information from multiple subnets through a single deployment by using router integration.
- Subnet load – Only considering the number of devices connected to each subnet is not enough. The load of processes needs to be considered to determine whether to deploy the scanner on each subnet or if one deployment for multiple connected subnets is sufficient.
IT asset discovery and inventory management: best practices
Identify the right discovery tools
To discover and track IT assets effectively, your IT asset managers must use tools like network discovery software and bar code scanners. Make use of the network solutions already installed on the network, especially the security tools that have discovery capabilities.
Outline a discovery process
Define and implement a discovery process so that all your IT assets are properly counted.
Improve accuracy by normalizing the data
Normalize discovered data to improve accuracy. Achieve asset normalization with database scripts or normalization software tools.
Manage costs and risks with IT asset lifecycle management
Create a streamlined inventory management process that records the lifecycle status of each IT asset. Your IT administrators can use this asset lifecycle information to determine if an asset is in use, stored, checked out, available for use, or retired. By tracking the lifecycle of IT assets, your administrators gain visibility into hardware assets that need to be refreshed or software licenses that need to be renewed, giving them crucial information needed for making future IT purchases.
Categorize your IT assets correctly
It’s essential to categorize your IT assets based on the risk associated with them and then place them in one of the two categories: Managed and Unmanaged.
IT assets with proprietary data, like laptops, servers, mobile devices, and desktops, should be placed in the managed category.
The assets that support operational requirements but do not contain sensitive data, such as printers (without hard drives), hubs, and monitors, should be categorized as unmanaged.
Chart out an asset mapping strategy
Map IT assets to relevant information like
- Owners
- Contracts
- Projects
- Locations
- Cost centers or departments
- CMDB
- Compliance definitions
With the right asset mapping, your IT asset administrators will be able to pull meaningful IT asset reports with relevant and actionable insights into security risks and overall IT asset operational costs.
Cloud migration discovery and assessment
With cloud migration discovery and assessment, you can assess its resources and IT environment to determine if it can be migrated to the cloud. The assessment involves carrying out an evaluation to make the migration process easier and adding a cloud environment that follows the best practices.
Types of discovery
There are many kinds of IT discovery, like
Network discovery
This process allows computers and devices to find one another when operating on the same network. It is the first step system administrators take while mapping and monitoring their network infrastructure.
Cloud discovery
Cloud discovery empowers IT departments of organizations to collect detailed information about their cloud-based infrastructure. It uncovers resources in major cloud service providers and collects the logical data centers associated with the account and subaccounts.
CI discovery
Automated IT discovery helps in automatically populating the CMDB. These discovery products create CIs and relationships from the discovered data when they discover IT hardware and software.
Serverless discovery
Serverless discovery is dependent on infrastructure patterns to discover CIs on a host. This type of discovery skips the scanning and classification phases. There are two kinds of serverless discovery: standard and host-based. Both types need an infrastructure pattern.
Agentless discovery
As explained earlier, agentless discovery does not need the installation of dedicated agents on the servers to be discovered. This type of discovery depends on the native OS or standard agents that are already installed. See our comparison of agent-based vs agentless discovery to determine which approach best fits your environment.
Shadow IT discovery
Shadow IT discovery is for your Shadow IT assets, in which your team first catalogs all applications used in your organization. The feature first runs in the observation mode, where all applications are analyzed.
Your team can then use the report to review the applications found and classify them as approved or unapproved.
ICMP discovery
It is also known as router discovery, which uses Internet Control Message Protocol (ICMP) router advertisements and router solicitation messages to permit a host to discover the addresses of operational routers on the subnet. The routers must be discovered first by the host before they can send IP datagrams outside their subnet. A host can discover the addresses of operational routers on the subnet with ICMP discovery.
Subnet discovery
Subnet discovery is usually automated, where it scans selected routers for IPv4 subnets and their IP addresses and imports them into IPAM. This type of discovery removes the need for manual entry or the importing of IP address spreadsheets.
NMAP discovery
The NMAP host discovery process refers to network hosts’ accounts to collect information about them to build an attack plan in penetration testing. During host discovery, NMAP looks up operating systems, ports, and running services using TCP and UDP protocols.
SNMP discovery
This type of IT discovery helps to find the network resources. It makes use of predefined discovery formulas, collection formulas, and metrics. It can also process the user-defined formulas for fast SNMP device onboarding.
IP discovery
IP discovery refers to the process of scanning your network for IP devices through one or several methods, like SNMP, ICMP, or neighborhood scanning.
Inventory discovery
Inventory discovery also includes Infrastructure discovery and determines which devices are in your network, and collects information about each of them. It also serves as the base for the other modules of discovery.
Passive asset discovery
Passive asset discovery enables companies to generate assets using not just live broadcast syslog data but also historical data. Having a passive discovery methodology gives your IT team the ability to pull in asset data from alternative data sources, such as archived syslog messages.
Get in touch to explore your IT discovery needs
Looking for more information on IT discovery and ITAM? Schedule a Demo at Virima.com to speak with the experts at Virima and see how our IT discovery, ITAM, CMDB, and service mapping solutions work together to give your team complete infrastructure visibility.