What Happens to CIs When IT Assets Are Decommissioned? A CMDB Best Practices Guide
TLDR
- Decommissioning a CI changes its lifecycle status to retired without removing the record or its history
- Deleting a CI removes all history; decommissioning preserves the full audit trail
- CIs move to “Decommissioned” status through manual transition, automated business rules, or integration triggers
- Linked records (software installs, relationships, service associations) remain visible on decommissioned CIs for audit purposes
- Decommissioned CI records form the evidence base for disposal documentation, license reclaim, and compliance reviews
Introduction
When a server goes offline, a laptop gets returned, or a network switch gets pulled from a rack, the CI in your CMDB does not automatically follow it into retirement. Without a defined decommission process, those records stay in your CMDB as active CIs indefinitely. They become ghost assets: inflating inventory, distorting software license counts, and generating compliance findings at the next audit.
This guide answers the most common questions IT managers and CMDB administrators ask about CI decommissioning, from what the term means in a CMDB context to how decommissioned records support audit and compliance requirements. Each question has a direct, practical answer.
What Does Decommissioned Mean in a CMDB?
In a CMDB, “decommissioned” is a lifecycle status that marks a CI as permanently retired from active service. The CI record remains in the database with its full history intact; it no longer appears in active asset counts or operational reports unless explicitly filtered in.
This status is distinct from “maintenance” (temporarily offline but expected to return) and from deletion (record permanently removed). Decommissioned CIs sit in a preserved, queryable state: visible for historical review and audit purposes, but excluded from live operational reporting by default.
The decommission status typically captures: decommission date, reason for retirement, the team member who approved the transition, and any linked disposal or data destruction records. This metadata is what makes the record useful long after the physical asset is gone.
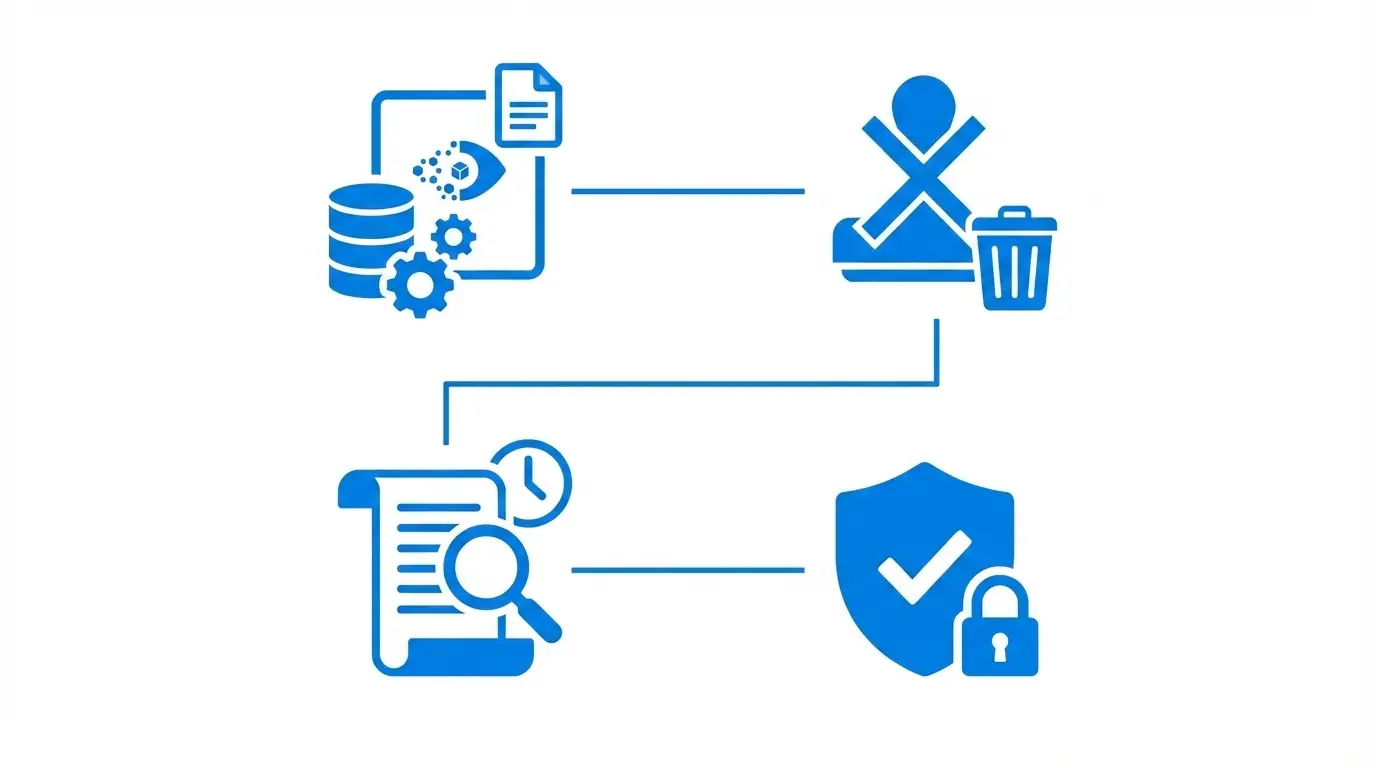
Should You Delete or Decommission a CI in CMDB?
Decommission the CI. Reserve deletion for CI records created in error, such as duplicates, test entries, or import mistakes that never represented a real asset.
When you delete a CI, you permanently remove it from the CMDB. There is no history, no decommission date, no record of what software was installed, and no way to answer an auditor’s question about that asset in the future.
When you decommission a CI, you retain the full record under a clear retirement status. Auditors, security teams, and SAM analysts can still query it. License keys on the device can be formally reclaimed. Relationships to services or other CIs remain visible for investigation.
The rule of thumb: If the CI ever represented a real device or software instance in your environment, decommission it. If it never should have been created, delete it. Storage capacity is not the constraint. Audit defensibility is. For a primer on maintaining CMDB accuracy throughout the asset lifecycle, see our dedicated guide.
How Do You Mark a CI as Decommissioned in CMDB?
There are three paths to marking a CI as decommissioned:
Manual transition: An administrator or ITAM team member directly changes the CI’s lifecycle status field from “Active” to “Decommissioned,” entering a decommission date and reason. This is the baseline process but is prone to being skipped when teams are busy.
Business rule automation: The CMDB applies a rule that flags CIs for decommission review when IT discovery has not observed them for a defined period (e.g., 30 days for servers) or when their confidence level drops below a threshold. A reviewer approves the transition, which triggers the status change and stamps the record with a date and reason.
Integration trigger: An external event, such as an HR offboarding request, a hardware disposal ticket in the ITSM platform, or a physical audit, triggers the CMDB decommission workflow through an integration or API call, linking the operational event to the asset lifecycle change.
Best practice combines automated flagging (to catch what manual processes miss) with a human approval step (to prevent false positives from temporary discovery gaps marking active devices as decommissioned).
How Do You Report on Decommissioned IT Assets?
A decommissioned assets report serves multiple use cases simultaneously: audit evidence, license reconciliation, disposal documentation, and operational cleanup tracking. Effective reports include:
Audit evidence: Filter by decommission date range (e.g., all CIs decommissioned in calendar year 2025), CI class, and decommission reason. Export as a dated, attributable report for IT audit submission.
License reconciliation: List all software installed on CIs decommissioned within a given period, with associated license keys and SAM records, to identify licenses available for reallocation or maintenance contracts eligible for non-renewal.
Disposal documentation: Cross-reference decommissioned CIs with hardware disposal records to confirm that every retired device has a corresponding disposition record for data destruction compliance.
Relationship cleanup: Identify services and other CIs that were linked to decommissioned devices, so service maps and dependency documentation can be updated.
Virima 6.1.1 introduced a dedicated Decommissioned Assets report and view that allows IT teams to filter decommissioned CIs by date range, CI class, and status, and export results directly. This removes the manual aggregation previously required to compile decommission evidence across multiple data sources.
What Happens to Linked Records When a CI Is Decommissioned?
Linked records remain intact when a CI is decommissioned. Relationships to other CIs, service associations, software installation records, user assignments, and contract links are not automatically removed or orphaned.
This is a deliberate design principle with clear rationale:
- Relationship history: Shows which services depended on the retired device, useful for post-incident reviews, capacity planning retrospectives, and service mapping cleanup
- Software audit trail: Documents exactly what software was installed on the device at decommission time, supporting SAM reconciliation and providing disposal evidence for software-side audits
- Compliance chain: Provides an unbroken evidence chain from when the device was active through its retirement, satisfying auditors who need to trace asset history
IT teams should review linked records as part of the decommission workflow, specifically to reclaim software license keys and update service dependency maps. The linked records themselves should remain visible until all dependent compliance or audit retention requirements are satisfied.
How Does CMDB Decommissioning Support IT Audit and Compliance?
CMDB decommissioning directly addresses requirements common across ISO 27001, SOC 2 Type II, CMMC, and internal IT governance frameworks. According to NIST’s Cybersecurity Framework 2.0 (published February 2024), asset lifecycle management — including secure retirement and disposal tracking — is a foundational governance capability that organizations must demonstrate to achieve effective cyber risk management posture.
Asset inventory accuracy: Auditors verify that the CMDB reflects the actual operational asset base. Decommissioned records with documented transition dates demonstrate that the organization maintains lifecycle discipline, not just a static inventory snapshot. A CMDB with properly decommissioned records shows governance maturity; one with ghost assets shows control gaps.
Data disposal evidence: Frameworks requiring evidence of secure data destruction (NIST SP 800-88, GDPR Article 17) depend on knowing which devices were retired, when, and how. The decommissioned CI record provides the anchor for that evidence chain and links to any associated disposal documentation.
Software license compliance: Software audit processes from publishers and independent auditors compare installed base to entitlements. Decommissioned CIs with documented software records support accurate license position reporting and demonstrate proper license reclaim at retirement, reducing true-up liability.
Change management audit trail: Every CI lifecycle transition, including decommission, belongs in the change record with an approver, date, and reason. This creates the auditable change trail that ITSM and configuration management frameworks require for asset disposition decisions.
What Is the Difference Between a Decommissioned Asset and a Deleted CI?
| Decommissioned CI | Deleted CI | |
|---|---|---|
| Record exists in CMDB | Yes, with “Decommissioned” status | No |
| Full attribute history retained | Yes | No |
| Queryable for reports | Yes | No |
| Audit trail available | Yes | No |
| Linked records accessible | Yes | No |
| Decommission date recorded | Yes | N/A |
| Appropriate use case | Real-world asset retired from service | Record created in error |
The practical consequence of deletion versus decommission is most visible at audit time. A deleted CI leaves a gap in the asset record. A decommissioned CI leaves a documented retirement with provenance and history. In any compliance review, documentation of retirement is an asset; absence of documentation is a liability.
When in doubt, decommission. For a broader look at CMDB best practices that support governance maturity, see our in-depth guide.
CMDB Decommissioning Best Practices: Summary
- Define a decommission policy that specifies triggering criteria (last-seen threshold, confidence level drop, manual request) and the required approval workflow
- Automate decommission flagging using discovery data so the process does not rely on manual updates from overloaded IT staff
- Retain decommissioned records until all compliance retention requirements for that asset class are satisfied
- Reclaim software licenses as part of every hardware decommission workflow, not as a separate downstream process
- Generate dated reports after each decommission cycle for audit readiness, not just before audits
- Audit CI identifier fields periodically to prevent decommissioned device identifiers (hostnames, IP addresses) from being reassigned to new devices, which causes identity conflicts in subsequent discovery runs
Virima’s CMDB platform supports all of these practices through discovery-driven confidence tracking, a dedicated Decommissioned Assets view (introduced in Virima 6.1.1), and integrated ITAM records that link hardware CIs to their associated software assets and license keys for complete lifecycle visibility.
For an operational guide to tracking and reporting on decommissioned assets, read How to Track, Report, and Audit Decommissioned IT Assets in Your CMDB.
Ready to Manage Your Full IT Asset Lifecycle?
From discovery through decommissioning, Virima gives IT teams the visibility and automation they need to maintain an accurate, audit-ready CMDB.
Sources: Teqtivity — Ghost Assets: The Hidden Costs of Untracked IT Equipment | ZenAdmin — 14 Best Practices for IT Asset Retrieval and Decommissioning | GB Advisors — Ensuring Data Reliability: Proven Techniques to Cleanse and Govern Your CMDB | NIST Cybersecurity Framework 2.0