Understanding Risk Assessment vs Impact Analysis in IT Change Management
In the enterprise IT change management process, many people confuse risk assessment with impact assessment. This confusion is a common and costly mistake.
A change might seem well-planned, tested, and approved. However, the organization can still create problems if it misunderstands what could go wrong or what would be affected.
Consider a routine server upgrade. The team approves the change plan, establishes rollback steps, and executes the plan as scheduled.
Then, a downstream service delivery fails, business users are surprised, and revenue-generating applications go offline. The issue was not execution. It was an incomplete understanding.
This happens when people treat risk assessment and impact analysis as interchangeable rather than complementary disciplines.
Why this matters
Industry research reinforces the scale of this problem. Studies show that about 70% of organizational change efforts do not reach their goals. This often happens because of poor planning and a lack of risk awareness (Social).
Only 32% of leaders are good at driving lasting change. This shows how hard it is to match technical changes with business readiness (Gartner, 2025).
At the core of mature IT operations is a clear understanding of risk assessment and impact analysis. These are not just theories; they are two different ways to make decisions. Both contribute to safe and predictable change.
TL;DR
- Risk assessment vs impact analysis is not a semantic debate—it is a decision-quality issue.
- Risk assessment evaluates what might go wrong and how likely failure is. Impact analysis determines what will be affected if a change succeeds or fails.
- Organizations that use accurate CMDB data and see service management ITSM dependencies can reduce outages from changes.
- This improves confidence in the CAB and aligns technical work with business results.
What is risk assessment?
Risk assessment is the process of finding possible threats linked to a change. It involves estimating how likely these threats are and judging how serious their effects could be. It answers a forward-looking question:
What could go wrong, and how likely is it to happen?
Within the broader discussion of risk assessment vs impact analysis, this discipline focuses on uncertainty and prevention before execution begins.
Key components of risk assessment
Risk identification
Effective change risk assessment surfaces risks across multiple dimensions:
- Technical: configuration errors, compatibility failures
- Security: vulnerabilities introduced or exposed
- Operational: skill gaps, timing conflicts, resource constraints
- External: vendor or third-party dependencies


Risk analysis
Once risks are identified, each one is evaluated using two core measures:
- Likelihood: the probability that the risk will occur during or after the change
- Severity: the scale of impact if the risk does materialize
Likelihood considers factors such as past change outcomes, environmental complexity, and the maturity of existing controls. Severity reflects the potential impact consequences, including service outages, data loss, security exposure, or SLA breaches.
These two measures are combined into a risk score, typically by multiplying likelihood and severity. The resulting score allows teams to compare risks objectively and focus attention where it matters most.
High-scoring risks demand mitigation planning, while lower-scoring risks may require monitoring rather than action.
Risk evaluation and treatment
After scoring, risks are reviewed and categorized based on organizational tolerance and business criticality:
- Accept: Low-priority risks that fall within acceptable thresholds and do not justify additional controls
- Mitigate: Risks that require action to reduce likelihood or severity, such as additional testing, configuration validation, or rollback preparation
- Avoid: Risks significant enough to warrant redesigning or postponing the change altogether
- Transfer: Risks that can be shifted to third parties through vendor responsibility, support contracts, or insurance coverage
This step ensures that risk decisions are intentional, consistent, and aligned with business priorities—rather than left to individual judgment or time pressure.
What risk assessment provides
Risk assessment delivers:
- A prioritized list of potential failure scenarios
- Insight into where mitigation effort matters most
- Inputs for testing strategy, rollback design, and approval gating
It is predictive by nature and focuses on preventing failure.
Example: Risk assessment for a database upgrade
Change: Upgrade a production Oracle database from 12c to 19c.
| Risk | Likelihood | Severity | Score |
| Application incompatibility | 7 | 8 | 56 |
| Data corruption | 2 | 10 | 20 |
| Extended downtime | 5 | 7 | 35 |
Before approving the change, the team looks at what could go wrong and how serious each issue would be.
Each potential problem is scored using two questions:
- How likely is this to happen? (Likelihood, scored from 1 to 10)
- How bad would it be if it did happen? (Severity, scored from 1 to 10)
These two numbers are multiplied to produce a risk score, which helps prioritize attention.
Application incompatibility — Score 56
This risk means some applications may not work correctly with the new database version. The likelihood is high (7) because application compatibility issues are common during major upgrades. The severity is also high (8) because affected applications could stop working. The resulting score of 56 signals that this risk needs strong mitigation, such as testing in a staging environment before the upgrade.
Data corruption — Score 20
This risk refers to the possibility of data being damaged during the upgrade. The likelihood is low (2) because modern upgrade tools are reliable. However, the severity is critical (10) because data loss would have serious consequences. Even with a lower overall score, this risk still requires safeguards, such as full backups and validation checks.
Extended downtime — Score 35
This risk involves the upgrade taking longer than planned, which would keep systems offline. The likelihood is moderate (5), and the severity is high (7) because prolonged downtime disrupts users and services. The score of 35 indicates that the team should prepare rollback plans and ensure support resources are available during the change window.
What this example shows
This example illustrates how risk assessment does not rely on guesswork. It uses simple scoring to compare different types of risks and decide where preparation and mitigation efforts should be focused before the change is approved.
What is impact analysis?
Impact analysis, often referred to as change impact analysis, determines what managing systems, services, users, and business processes will be affected by a change or by its failure. It answers:
If something goes wrong (or even if it goes right), what and who will be affected?
In the context of risk assessment vs impact analysis, impact analysis focuses on consequence rather than probability.
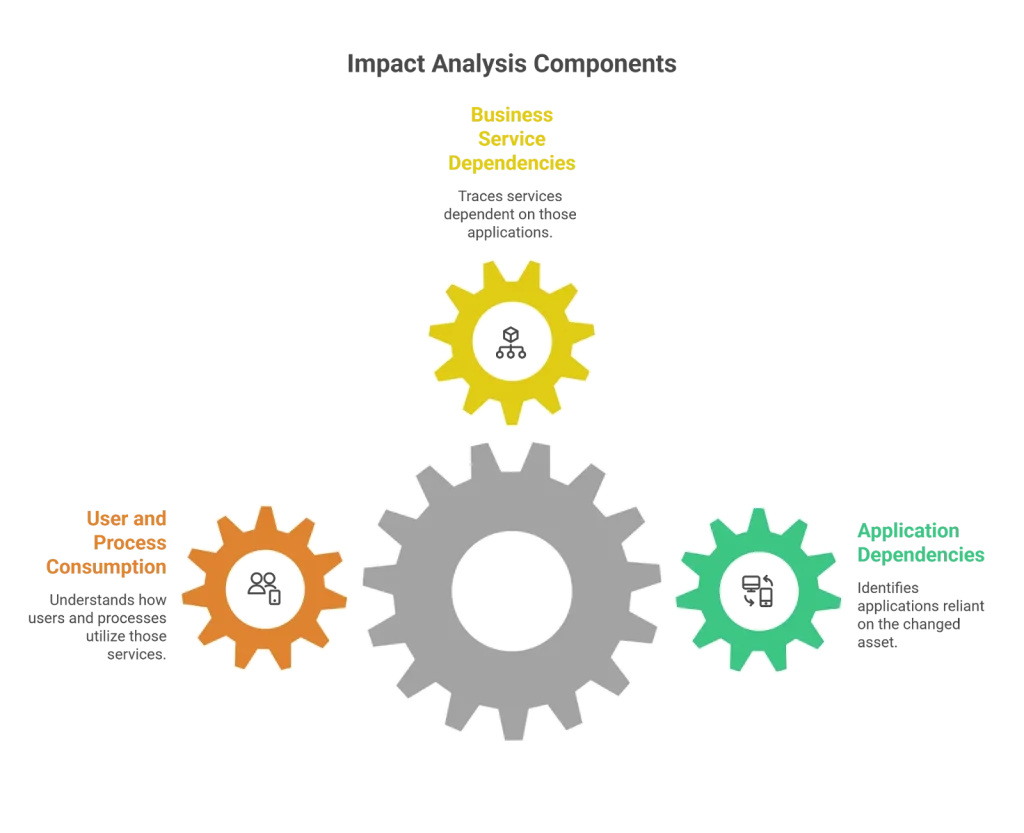
Key components of impact analysis
Dependency mapping
Impact analysis begins with understanding relationships:
- Applications dependent on the changed asset
- Business services are dependent on those applications
- Users and people processes consuming those services
This level of insight requires a trusted CMDB.
Scope of impact
Impact analysis evaluates how far the effects of a change can spread across the environment. This is done by examining impact across multiple layers, not just the component being modified.
- Direct impact: This is the immediate effect on the Configuration Item (CI) being changed. For example, a server or database may be temporarily unavailable during a patch or upgrade.
- Upstream impact: These are the applications or services that depend on the CI. If the CI is unavailable or behaves unexpectedly, dependent services may also fail or degrade.
- Downstream impact: This includes the underlying infrastructure that supports the CI, such as storage, network components, or shared platforms. Changes can introduce stress or configuration conflicts in these supporting layers.
- Business impact: This layer translates technical disruption into business terms. It considers which users are affected, whether revenue-generating services are disrupted, and if SLAs or compliance commitments are at risk.
Looking at impact across these layers ensures that teams understand not just what is being changed, but who and what will feel the effects of that change.
Impact severity classification
Impacts are typically classified as high, medium, or low based on business criticality.
What impact analysis provides
Impact analysis produces:
- A list of affected CIs and services
- Business context for disruption
- Guidance on scheduling, communication, and rollback readiness
It defines blast radius, not likelihood.
Example: Impact analysis for the same database upgrade
- Database runs on Server ABC
- Three applications depend on it
- Two revenue-impacting business services rely on those applications
- Estimated exposure: 5,000 users and $50,000 per hour
The change being planned is the same database upgrade, but this time the focus is not on what could go wrong. The focus is on what would be affected if the database is taken offline or if the upgrade fails.
The database runs on a specific server (Server ABC). That database supports three different applications. Those applications, in turn, support two business services that directly generate revenue.
Because of these dependencies, any downtime of the database would affect all three applications and disrupt the two business services. The impact is not limited to IT systems; it extends to approximately 5,000 users and an estimated $50,000 in revenue per hour.
This level of visibility allows the team to make smarter, informed decisions. The change can be scheduled during a low-traffic period to reduce business disruption, and stakeholder engagement can be informed in advance so there are no surprises.
What this example shows
This example demonstrates how impact analysis turns technical changes into the business context. Instead of guessing who might be affected, teams can clearly see the scope of disruption and plan timing, communication, and support accordingly.
Risk assessment vs impact analysis: key differences
Side-by-side comparison
| Aspect | Risk Assessment | Impact Analysis |
| Core question | What could go wrong? | What will be affected? |
| Focus | Likelihood and severity | Dependencies and scope |
| Primary output | Risk scores and mitigations | Affected services and users |
| Data sources | History, vulnerabilities | CMDB, service maps |
| Purpose | Prevent failure | Prepare for consequences |
Understanding risk assessment vs impact analysis clarifies why both are required for complete decision-making.
How they work together
- Risk assessment without impact analysis leads to poor communication and underestimated business exposure.
- Impact analysis without risk assessment leads to over-cautious or under-mitigated changes.
Together, they enable informed approval, intelligent scheduling, and confident execution.
How Virima enables both risk assessment and impact analysis
Virima equips teams with the context, data accuracy, and visual insights needed to do both risk assessment and CMDB impact analysis with confidence.
Trusted, near real-time CMDB as a foundation
At the heart of Virima’s approach is a continuously updated Configuration Management Database (CMDB) that reflects the real world, not outdated spreadsheets.
Virima’s automated discovery engine scans networks, cloud environments, and endpoints to find assets and track their configuration changes over time, building a CMDB that is both accurate and audit-ready. Because this data is continuously validated, teams can trust that their risk and impact analyses start from a reliable source of truth.
Security context through vulnerability overlays
Extending beyond basic inventory, Virima integrates vulnerability intelligence, including lookups from the NIST National Vulnerability Database directly into service maps. These overlays reveal which assets have known vulnerabilities and how they relate to applications and services.
When performing change risk assessment, this added context helps teams spot security exposure early and prioritize mitigation based not just on likelihood and severity, but also on known vulnerability status.
Historical change data improves risk prediction
Virima captures rich history from past change events, both successful and failed, and ties that back into the CMDB and service maps. This historical perspective allows analysts to spot patterns: which types of changes have historically caused issues, which assets are more failure-prone, and what mitigation steps proved effective.
In this way, risk assessment becomes more predictable and grounded in data rather than intuition.
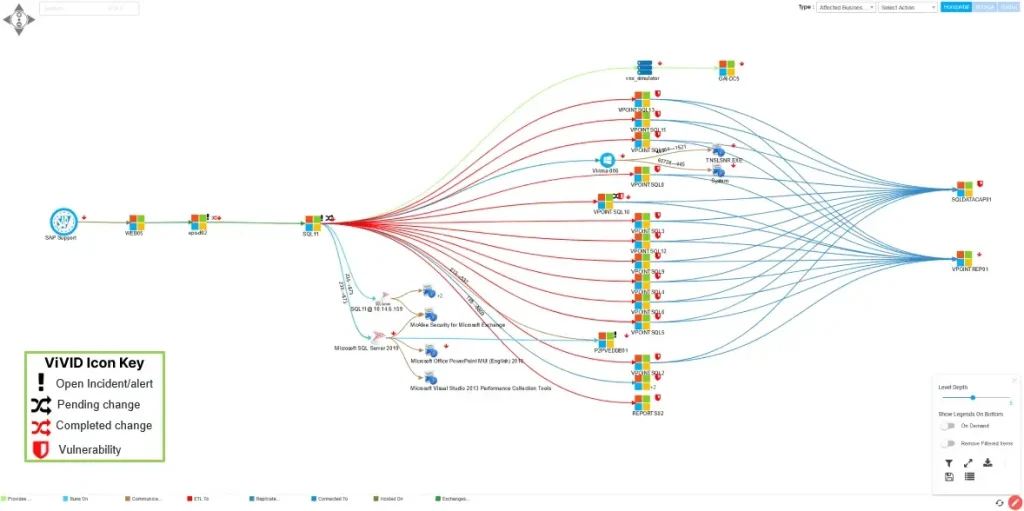
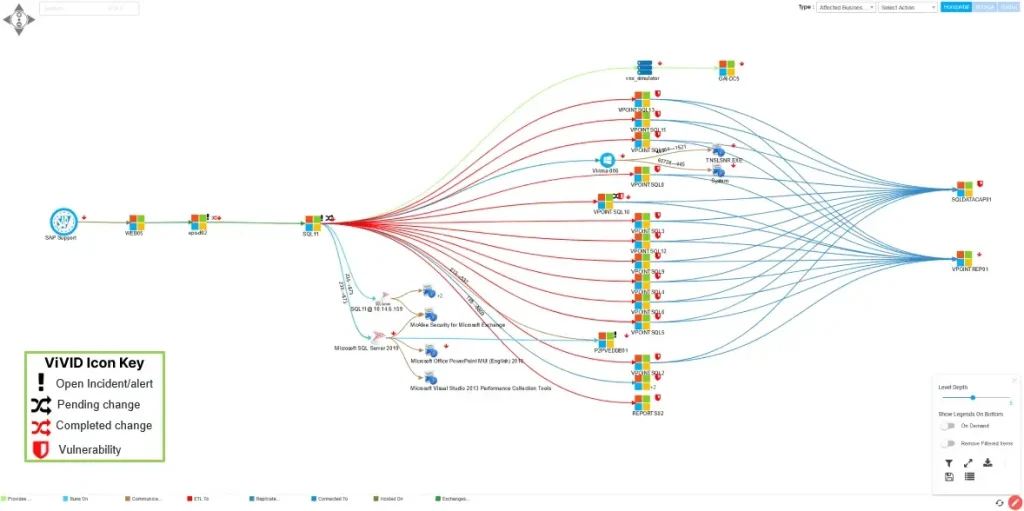
ViVID™ with Service Mapping for precise impact analysis
The Virima Visual Impact Display brings the CMDB to life by overlaying live ITSM data on service dependency maps.
While service maps show how systems, applications, and business services are connected, ViVID adds real-time context by layering incident, change, and vulnerability data directly onto those relationships.
Instead of inferring impact from static connections, teams can clearly see which assets and services are currently affected or at risk before a change is approved. This makes impact analysis faster, more accurate, and grounded in operational reality.
Embedded in ITSM workflows
Virima’s insights are not siloed; they integrate directly with common ITSM platforms like ServiceNow, Jira Service Management, Ivanti, and others. Change analysts and approvers can see risk scores and impact maps right within the tools they already use for change requests and approvals. This ensures that risk assessment and CMDB impact analysis become part of everyday workflows rather than separate exercises.
Continuous discovery keeps analysis current
Both risk and impact assessments depend on accurate data. Virima’s continuous IT discovery ensures that the CMDB and service maps reflect the current infrastructure state, new devices, changed configurations, cloud assets, and updated relationships so that every analysis is based on up-to-date information rather than assumptions or stale records.
In short, Virima doesn’t just store configuration data; it continuously discovers, validates, and visualizes it, turning raw inventory into actionable context. That’s what enables project teams to accurately assess both what could go wrong (risk) and what will be affected (impact) before a change is approved or executed.
Best practices for risk assessment and impact analysis
- Embed both disciplines into every change workflow
- Maintain accurate CMDB and validated service maps
- Use historical outcomes to refine risk scoring
- Communicate impact in business operations terms
- Continuously review failed or degraded changes
Common pitfalls in risk assessment and impact analysis
- Treating high risk and high impact as the same
- Skipping either analysis due to time pressure
- Relying on stale dependency data
- Ignoring low-likelihood but high-severity risks
Each pitfall reflects missing context, not missing tools.
Risk assessment vs impact analysis: Two questions that every change must answer
Risk assessment vs impact analysis represents two sides of the same decision. One anticipates failure. The other prepares the organization for consequences. When combined and powered by accurate CMDB data and service mapping, they transform IT change management tools from reactive execution into confident governance.
Schedule a demo to see how Virima enables automated risk assessment and impact analysis for real enterprise changes.
Explore Virima’s change management use case to know more about how Virima can help you.
Frequently Asked Questions
Is risk assessment vs impact analysis the same thing?
No. Risk assessment predicts failure probability. Impact analysis defines consequence.
Can a change be low risk but high impact?
Yes. Low likelihood does not mean low in minimizing disruption.
When should both be performed?
Before change approval, as mandatory steps.
Why is CMDB impact analysis critical?
Because dependency visibility determines blast radius accuracy.
How do mature teams operationalize both?
By embedding automated analysis into ITSM workflows.