Strengthen IT Governance with Virima and Ivanti
Without IT governance and risk management, you get security breaches, data loss, regulatory penalties, and direct financial damage. Leave those …
EMA reveals why real-time discovery and CMDB maturity are key to ServiceOps success. Download the EMA Report!
First dependency map in under 60 minutes — powered by discovery that keeps your CMDB accurate. Request Free Trial.


Without IT governance and risk management, you get security breaches, data loss, regulatory penalties, and direct financial damage. Leave those …




Unpatched servers, shadow IT, and unknown dependencies — these are the gaps that show up in IT audit findings and …


In a complex IT environment, IT visibility is what separates teams that react from teams that stay ahead. It gives …
Managing IT security without a CMDB compliance strategy means operating with blind spots across your entire infrastructure, and 57% of …
Your IT environment is growing faster than you can track. New servers spin up, and cloud systems keep increasing. Also, …
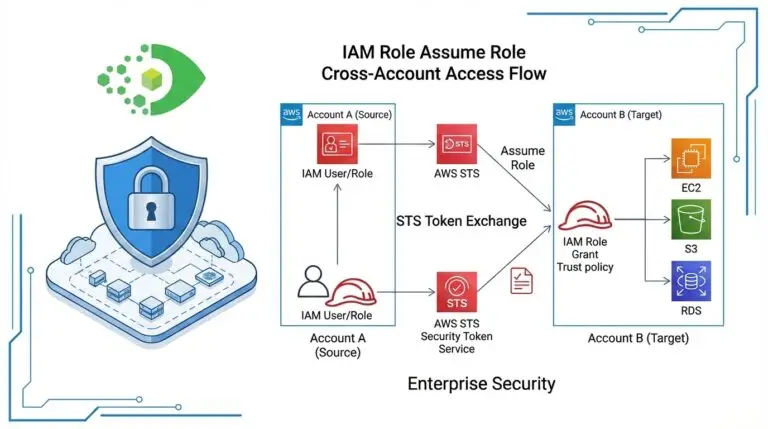
Using static AWS Access Key ID and Secret Access Key for CMDB discovery is a security risk. AWS Assume …


Gartner’s IT Infrastructure, Operations & Cloud Strategies (IOCS) Conference has always been a useful barometer for where IT operations priorities …

