The role of CMDB compliance in IT security and risk management
Managing IT security without a CMDB compliance strategy means operating with blind spots across your entire infrastructure, and 57% of businesses don’t fully know where all their IT assets are, which creates hidden openings for attackers. Your environment spans hundreds, sometimes thousands, of interconnected devices, applications, and services. A Configuration Management Database (CMDB) maps those assets, including configuration items CIs, and their relationships in one place.
When that map is inaccurate or incomplete, vulnerabilities go undetected. Unauthorized assets sit on the network. Audit evidence falls apart.
Why CMDB compliance matters?
A compliant CMDB acts as a single source of truth for every IT asset: hardware, software, configurations, and dependencies. For security and compliance teams, that visibility is foundational. Without it, you’re working from outdated inventory, and auditors will find the gaps before your team does.
CMDB compliance strengthens your security posture in several ways— especially when vulnerability severity is rising; 38% of discovered vulnerabilities in 2025 were rated High or Critical.
- Faster incident response: A compliant CMDB gives responders a clear picture of affected systems and downstream dependencies, cutting triage time during security incidents.
- Stronger risk management: Tracking configuration changes and mapping vulnerabilities to specific CIs helps your team prioritize remediation based on actual business exposure.
- Controlled change management: Accurate dependency data means change advisory boards review requests against current service maps, not stale records.
- Optimized resource allocation: Reliable asset data prevents duplicate spend, identifies underused resources, and supports capacity planning.
- Audit-ready evidence: A compliant CMDB provides the documentation regulators expect: a complete, current inventory of assets, their configurations, and their relationships.
Key requirements for CMDB compliance
Maintaining CMDB compliance depends on four pillars:
- Data accuracy: Every CI in the CMDB must reflect its current configuration. Manual updates decay fast. Automated discovery on recurring schedules is the only reliable way to keep data current, ensuring data remains accurate and audit-ready.
- Data completeness: The CMDB should include all assets: on-prem servers, network devices, cloud resources, and virtual infrastructure. Gaps in coverage are gaps in compliance.
- Data governance: Define clear processes for who can create, modify, or retire CIs. Without governance, CMDB data degrades from multiple uncontrolled inputs.
- Data security: Protect CMDB data with role-based access controls. The CMDB contains your complete infrastructure blueprint. Unauthorized access is a security risk in itself.
How does CMDB compliance support regulatory audits?
Regulatory frameworks like SOX, PCI-DSS, and HIPAA require you to control your IT assets and systems. A compliant CMDB helps you do this with clear and updated records. It shows what assets you have, how they are set up, and who made changes. It also shows how your services connect to each other.
During an audit, assessors check if you know what is on your network. They also check if your systems follow approved settings. In addition, they look for proof that every change followed a clear process. Because of this, you need accurate and complete data.
With a compliant CMDB, you can quickly show all this information. As a result, you save time and avoid last-minute stress. Instead of searching for records, you can easily share the right evidence. This makes your audit process much smoother and faster.
What compliance frameworks require a CMDB?
No framework asks for a “CMDB” by name. However, many require the controls a CMDB provides. For example, SOX Section 404 requires you to document IT controls for financial systems. Similarly, PCI-DSS Requirement 2 asks you to keep a list of all system components. Also, HIPAA § 164.312 requires access controls and audit logs for sensitive health data.
In addition, ISO/IEC 27001 Annex A.8 requires you to maintain an asset inventory. Because of this, you need a clear and updated record of your IT environment. A CMDB helps you keep all this information in one place. As a result, you can manage these requirements more easily and at scale.
The risks of CMDB non-compliance
Neglecting CMDB compliance creates compounding risk:
- Unidentified security exposures: Inaccurate or incomplete CMDB data creates blind spots. Outdated software on forgotten servers, unmanaged cloud instances, or shadow IT devices: these are the assets auditors find and attackers exploit.
- Delayed incident response: When a security incident hits, your team needs to know immediately which services are affected and what depends on what. A non-compliant CMDB forces manual investigation at exactly the moment speed matters most.
- Audit failures: Regulatory audits without a compliant CMDB mean scrambling to reconstruct inventory and change history under pressure. The result: non-compliance findings, fines, and reputational damage.
How do you measure CMDB data accuracy?
You can check CMDB accuracy using three key measures.
- First, track the CI completeness rate, the percentage of all assets listed in your CMDB.
- Second, check data freshness, how recently each CI was validated by an automated scan.
- Third, measure relationship accuracy to determine how correctly dependencies between assets match your real infrastructure.
Most mature organizations aim for over 95% completeness. They also check critical assets daily and review relationships at least every three months. By tracking these measures, you can trust your CMDB and respond faster during audits or incidents.
How Virima strengthens CMDB compliance
Virima provides the discovery, mapping, and data integrity capabilities that make CMDB compliance sustainable, not a one-time cleanup that decays within months.
Automated discovery and inventory
Virima’s IT discovery engine finds assets across your infrastructure. It uses both agentless and agent-based methods. This includes on-prem servers, network devices, cloud instances, storage, and applications. Discovery runs on a schedule, so your CMDB stays up to date without manual work.
Some details, like asset ownership, lifecycle status, business criticality, and SLA assignments, cannot be found by scanning. Virima’s Autonomic Social Discovery fills this gap. It asks the right people questions and updates CI records automatically.
By combining technical scanning and social discovery, Virima ensures your CMDB is complete. Automated scans alone miss context, and manual processes cannot scale efficiently.
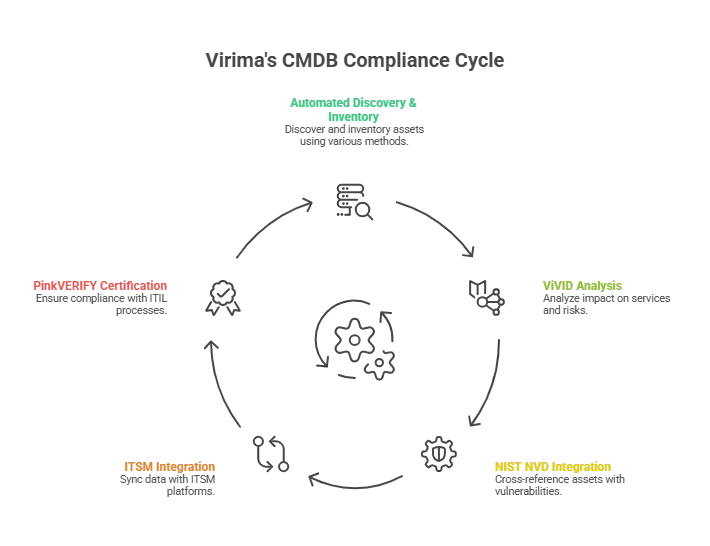
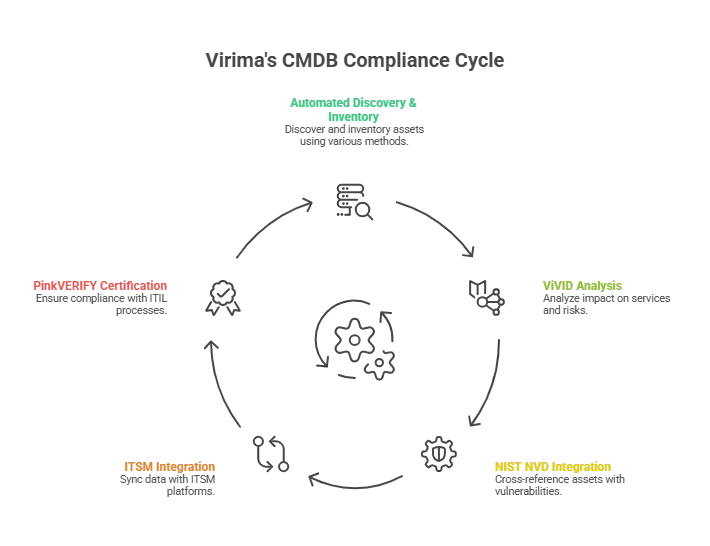
ViVID: Visual impact analysis for compliance
ViVID adds a visual layer to your service maps. It combines ITSM incident and change data, NIST NVD vulnerability information, and monitoring alerts. This shows not only what your infrastructure looks like, but also where risks and changes are happening.
For compliance teams, ViVID answers the key auditor question: “What is the impact?” If a vulnerability affects a server, ViVID shows which services rely on it. It also highlights which business processes are at risk and where you should focus remediation first.
NIST NVD integration: Vulnerability context at no extra cost
Virima cross-references discovered assets against the NIST National Vulnerability Database, surfacing known vulnerabilities tied to specific CIs in your CMDB. This integration comes at no additional cost, giving your team current vulnerability context without bolting on a separate tool.
Combined with ViVID’s visual overlays, you can see which vulnerabilities affect which services and prioritize remediation based on actual business exposure, not just CVSS scores in isolation.
ITSM integration for CMDB compliance workflows
Virima integrates with seven ITSM platforms: ServiceNow, Jira Service Management, Ivanti, HaloITSM, Cherwell, Xurrent, and Hornbill. It keeps CI data flowing both ways with ServiceNow, Jira, Ivanti, HaloITSM, and Cherwell.
Data discovered by Virima automatically updates your ITSM workflows. Likewise, changes made in your ITSM platform sync back to Virima’s CMDB. This integration stops data drift and keeps your CMDB accurate. It also ensures discovery and service management always stay aligned.
Why CMDB compliance is a security prerequisite, not a checkbox
CMDB compliance isn’t a one-time project. It’s the foundation that IT security, risk management, and regulatory readiness depend on. Without accurate, complete, and governed CMDB data, vulnerability management is guesswork, incident response is slower than it should be, and audits become damage control.
Virima’s combination of agentless and agent-based IT discovery, Autonomic Social Discovery for non-discoverable attributes, ViVID visual impact overlays, NIST NVD integration, IT Asset Management for lifecycle governance, and seven ITSM integrations delivers the CMDB accuracy and completeness that compliance demands, without the licensing complexity of rebuilding inside a single-vendor ITSM stack.
Ready to see how Virima supports your CMDB compliance requirements? Schedule a demo to see automated discovery and ViVID in action.






