CMDB TCO Analysis: The Real Cost of Inaccurate Data
CMDB inaccuracy is well understood in IT operations circles. In the boardroom, it almost never shows up as a line …
Oracle & MySQL CMDB Discovery: The Complete Guide
Application performance drops without warning. Users report slowness. Dashboards show healthy servers and stable network traffic. Yet logs reveal repeated …
Storage and HCI Topology Discovery in Virima 6.1
Storage underpins everything, yet without proper storage and HCI Topology Discovery, it remains the most opaque layer in modern …
How to Prioritize Vulnerability Remediation Using CMDB Asset Criticality and Service Maps
Learn how to use CMDB asset criticality and ViVID service maps to build a vulnerability remediation priority queue that targets …
Does Virima Include Vulnerability Management? How NIST NVD Integration Works with CMDB
Does Virima Include Vulnerability Management? How NIST NVD Integration Works with CMDB
Virima 6.1.1 — Published by Virima, Inc.
Virima …
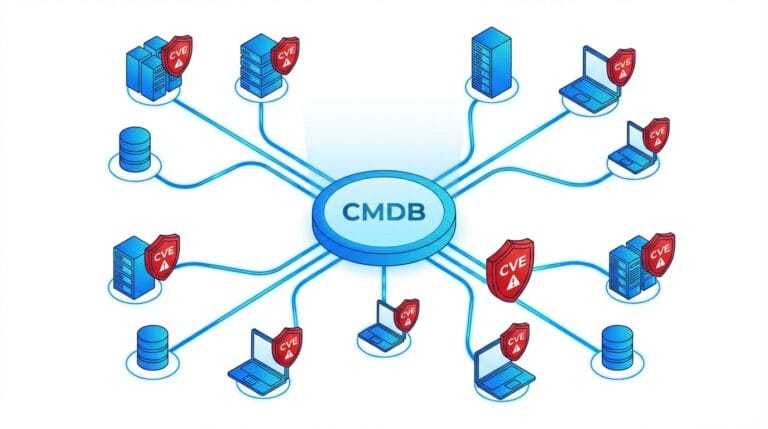
CMDB and Vulnerability Management: How to Automatically Link CVEs to Affected IT Assets
Virima 6.1.1 — Published by Virima, Inc.
Vulnerability management is broken for most enterprise IT teams — and the reason …