CMDB and Vulnerability Management: How to Automatically Link CVEs to Affected IT Assets
Virima 6.1.1 — Published by Virima, Inc.
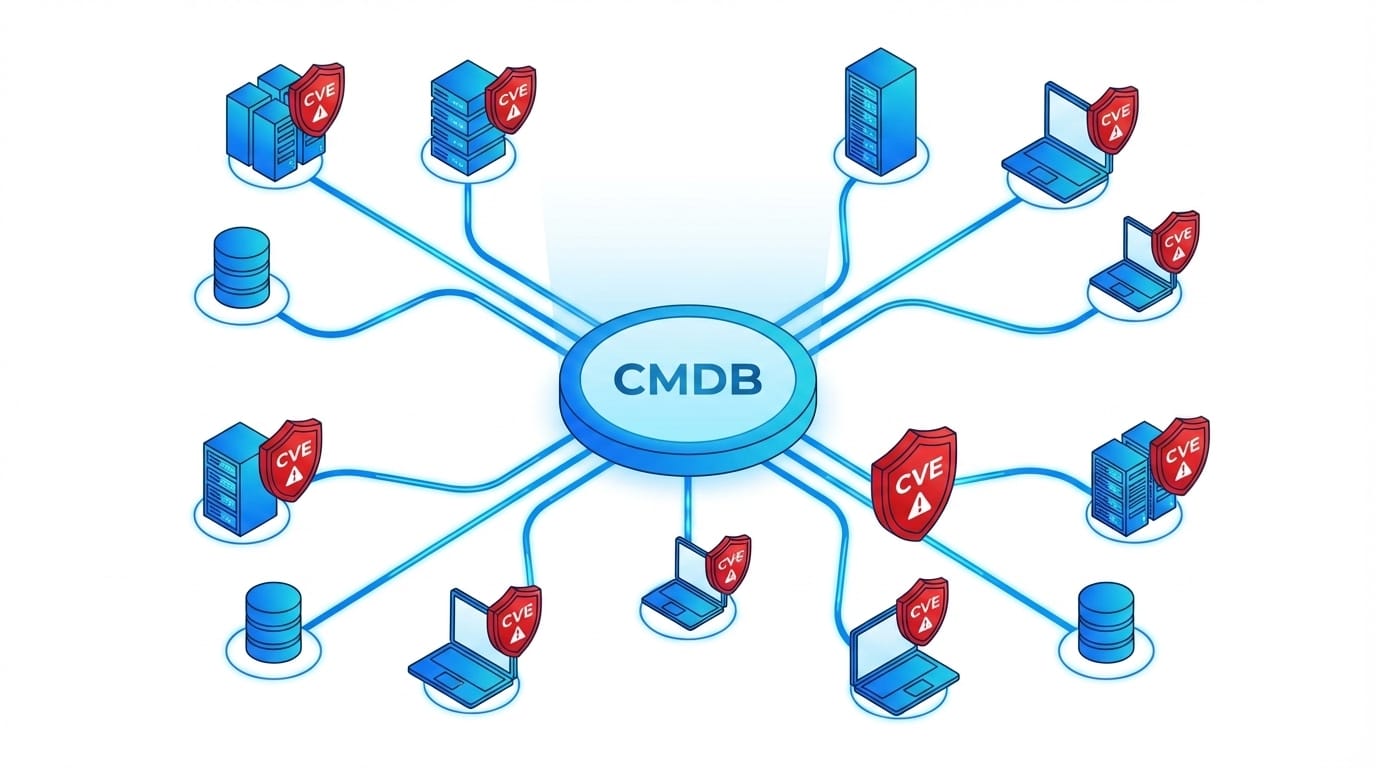
Vulnerability management is broken for most enterprise IT teams — and the reason is not a shortage of scanning tools. The gap is between what the scanner finds and what the team actually knows about the asset behind the CVE. A scanner identifies that a version of OpenSSL running somewhere in the environment has a critical vulnerability. But without knowing which CI owns that installation, what service depends on that CI, and whether that service touches production or a dev sandbox, the security team cannot determine the actual business risk.
This disconnect — between vulnerability data and asset context — is the root cause of alert fatigue, misallocated remediation effort, and compliance audit failures. When CVEs are not linked to specific configuration items in the CMDB, every vulnerability looks equally urgent (or equally ambiguous). Teams spend engineering cycles patching low-risk assets while genuinely critical exposures sit unaddressed.
According to the NIST National Vulnerability Database, tens of thousands of new CVEs are published each year — a volume that makes manual vulnerability-to-asset mapping operationally unsustainable without automated CI linkage at the CMDB layer.
Virima 6.1.1 closes this gap. Discovery data automatically checks for known Common Platform Enumerations (CPEs) and correlates them with CVEs from the NIST National Vulnerability Database, then links each vulnerability directly to the affected CI in the CMDB. Security teams get a complete, asset-aware vulnerability picture — and the remediation context they need to act on it.
Why Vulnerability Management Needs CMDB Data
Standalone vulnerability scanners output a list of findings. They identify software versions, match them against known exploit databases, and assign CVSS severity scores. What they do not provide is business context.
CMDB data answers the questions a scanner cannot:
- Which CI is affected? Not just which IP address or hostname, but the full CI record — owner, location, hardware specs, software installed, relationships to other CIs.
- What service does this CI support? A vulnerable server supporting a tier-1 customer-facing application carries different risk than a test workstation with the same CVE.
- Who owns remediation? The CMDB identifies the CI owner and the team responsible for that asset, removing the “who patches this?” ambiguity that delays remediation.
- What change history exists? CMDB records show recent changes to the CI, helping distinguish between newly introduced vulnerabilities and long-standing exposures.
Without CMDB context, vulnerability prioritization is arbitrary. With it, security teams apply a risk-based model that reflects actual business exposure.
Virima 6.1.1 provides both: continuous IT discovery that populates and maintains the CMDB, and integrated vulnerability management that maps every CVE to a CI the moment a match is found.
How NIST NVD Integration Works in Virima
The National Vulnerability Database (NVD), maintained by NIST, is the authoritative public repository of Common Vulnerabilities and Exposures (CVEs). It uses the Common Platform Enumeration (CPE) standard to identify affected software and hardware versions.
Virima 6.1.1 integrates with the NIST NVD as part of the core discovery workflow — at no additional cost. Here is how the process works:
Step 1: Discovery identifies installed software and versions.
Virima’s agentless and agent-based discovery scans the environment and records every software installation — name, version, vendor — as part of the CI record in the CMDB.
Step 2: CPE matching runs against the NVD.
For each software version discovered, Virima checks against the CPE dictionary in the NIST NVD to find exact or fuzzy matches.
Step 3: CVE correlation surfaces known vulnerabilities.
Where a CPE match exists, Virima retrieves all CVEs associated with that software version — including CVSS scores, severity ratings, and remediation references.
Step 4: CI linkage is created in the CMDB.
Each identified CVE is directly linked to the CI that runs the affected software. The link is not a separate report or export — it is a live relationship in the CMDB, visible from the CI record itself.
This four-step cycle runs on schedule (configurable) so vulnerability data stays current as the environment changes. New software discovered in the next scan cycle automatically goes through the same CPE-CVE correlation workflow.
The inclusion of NIST NVD integration at no extra charge is significant. Many vulnerability management platforms charge separately for database subscriptions or API access. In Virima 6.1.1, NVD correlation is part of the discovery capability.
Multi-Level Vulnerability Drill-Down
One of the most operationally useful features in Virima’s vulnerability management is the multi-level drill-down. Security and IT operations teams navigate from a high-level software summary all the way to a specific CVE in a specific CI — without switching tools or exporting to a spreadsheet.
The drill-down works across three levels:
Level 1: Software
The top level shows all software titles in the environment that have at least one known vulnerability. Teams see the software name, the number of CVEs associated with it, and the highest severity rating present.
Level 2: Version
Selecting a software title shows each version of that software discovered across the environment, with the specific CVEs that apply to each version. Different versions of the same software often carry different CVE profiles — this level makes those differences visible immediately.
Level 3: CVE
Selecting a specific version surfaces the individual CVEs, with full detail: CVE ID, CVSS score, CVSS vector, description of the vulnerability, affected CIs, and remediation references. This is where the CI link becomes directly actionable — the team sees exactly which assets run the affected version and can initiate remediation from the same view.
This structure eliminates the manual pivot tables and cross-referencing that scanner-only approaches require. The data is pre-joined at the CI level.
Severity Categorization and Prioritization
Virima categorizes vulnerabilities by severity using CVSS scores, following standard severity bands:
| CVSS Score Range | Severity |
|---|---|
| 9.0 – 10.0 | Critical |
| 7.0 – 8.9 | High |
| 4.0 – 6.9 | Medium |
| 0.1 – 3.9 | Low |
CVSS score provides the baseline — but CMDB asset data provides the multiplier.
A Critical CVSS score on a CI that sits in an isolated dev environment with no production dependencies carries lower actual business risk than a Medium CVSS score on a CI that is a dependency of the company’s core billing system.
Virima’s approach combines:
- CVSS severity (from the NIST NVD CVE record)
- Asset criticality (from the CMDB — business importance, ownership, tier classification)
- Service context (from ViVID Service Maps — what services depend on this CI?)
The output is a prioritized vulnerability queue where remediation effort aligns to actual business risk, not just scanner output.
Using ViVID Service Maps to Prioritize Remediation
ViVID is Virima’s automated service mapping capability. It builds and maintains visual, dependency-aware maps of IT services — showing which CIs support which services, and how those services relate to business functions.
When vulnerability data overlays on a ViVID Service Map, the result is a risk-in-context view that no standalone scanner produces:
- Which vulnerable CIs sit on business-critical service maps? A CVE affecting a CI that underpins a revenue-generating service requires immediate attention, regardless of CVSS score alone.
- What is the blast radius if this CI is compromised or taken offline for patching? ViVID shows the downstream dependency chain — other CIs and services that would be affected.
- Are there compensating controls in place? If the vulnerable CI sits behind a network segment with additional security controls, the effective risk is lower. The service map makes that topology visible to the remediation team.
Remediation teams use the ViVID overlay to build a sequenced patch plan: starting with vulnerable CIs on critical service maps, then working through lower-tier services. This approach produces measurable risk reduction with every remediation cycle, rather than random CVE closure that may not reduce actual exposure.
Scheduled Vulnerability Assessments
Vulnerability data is only as current as the last scan. In fast-moving environments — where new software is deployed, versions are updated, and infrastructure changes daily — stale vulnerability data creates a false sense of security.
Virima 6.1.1 supports scheduled vulnerability assessments that run on a configurable cadence:
- Discovery scans run on schedule and capture the current state of every CI in scope.
- CPE/CVE correlation runs automatically after each discovery cycle, updating the vulnerability data for any newly discovered or changed software.
- CI linkages update automatically when new CVEs are published in the NIST NVD or when CI software configurations change.
Security teams configure assessment schedules to meet compliance requirements — weekly scans for certain asset classes, daily for critical infrastructure, monthly for low-risk environments. The schedule runs unattended, and the CMDB reflects the updated state after each cycle.
This eliminates the “we ran the scan six weeks ago” problem that causes compliance gaps and audit findings.
Vulnerability Reporting for Auditors and Stakeholders
Security and GRC teams need evidence. Vulnerability reports in Virima 6.1.1 are built on live CMDB data, which means they reflect the actual state of the environment at the time of report generation — not a static export from weeks prior.
Reports available in Virima cover:
- Vulnerability summary by severity — count of Critical, High, Medium, and Low CVEs across the environment
- Vulnerable assets by business unit or location — scoped views for compliance reporting
- Remediation progress tracking — CVEs opened vs. closed over time, with CI-level detail
- Aging vulnerabilities — CVEs that remain open beyond defined thresholds, for SLA compliance
- Service-level risk reports — vulnerable CIs mapped to the business services they support
These reports give auditors the traceability they require: a CVE, the specific CI affected, the software version that caused the exposure, and the remediation action taken. Everything traces back to the CMDB record.
CMDB Vulnerability Management vs. Standalone Vulnerability Scanners
| Capability | Standalone Scanner | Virima CMDB + Vulnerability Management |
|---|---|---|
| CVE identification | Yes | Yes |
| CI-level asset linkage | No | Yes |
| Service dependency context | No | Yes (ViVID) |
| Asset criticality in prioritization | No | Yes |
| CMDB auto-update on new CVEs | No | Yes |
| Included NVD integration | Varies | Yes, at no extra cost |
| Scheduled assessments | Yes | Yes |
| Audit-ready reports with CI traceability | No | Yes |
Standalone scanners serve a purpose — they find vulnerabilities. But without CMDB integration, every finding requires manual research to determine the affected CI, its owner, its service context, and its remediation priority. That manual work is expensive, slow, and error-prone.
Virima CMDB vulnerability management eliminates that manual layer. The CI context is already there, because the CMDB is the source of truth for every asset in the environment.
Conclusion
Vulnerability management works when it runs on top of accurate, current asset data. The combination of Virima’s IT discovery, CMDB, NIST NVD integration, and ViVID Service Maps gives security and IT operations teams what standalone scanners cannot: CVEs linked to CIs, CIs linked to services, and services linked to business criticality.
The result is a remediation program that targets actual business risk — not just CVSS numbers.
Ready to see CMDB-integrated vulnerability management in action?
Schedule a Demo at virima.com
Frequently Asked Questions
Does Virima perform active vulnerability scanning?
Virima’s discovery engine captures installed software versions and correlates them against the NIST NVD to surface CVEs. For environments that require active exploit-based scanning, Virima’s CVE data complements the output from dedicated scanners by adding CI and service context to every finding.
How often does Virima update its CVE data from the NIST NVD?
CVE correlation runs with each discovery cycle, on the schedule configured by the IT team. New CVEs published to the NIST NVD are picked up in the next correlation run, ensuring vulnerability data stays current as new exploits are disclosed.
Can Virima’s vulnerability data integrate with external ticketing or ITSM tools?
Yes. Virima integrates with ServiceNow, Jira, Ivanti, HaloITSM, Hornbill, Xurrent, and TeamDynamix. Vulnerability findings linked to CIs feed into remediation workflows in whichever ITSM platform the team uses.