Application Dependency Mapping vs Service Mapping: What’s the Difference?
Why these two terms keep getting confused
Ask five IT operations professionals to define application dependency mapping and service mapping, and you will probably get five different answers — some of which describe the same thing.
That is not a knowledge gap. It is a terminology problem the industry has never quite resolved. Vendors use the terms interchangeably. ITIL treats them as adjacent concepts without drawing a hard line. And plenty of tools attempt to do both under a single label, which muddies things further.
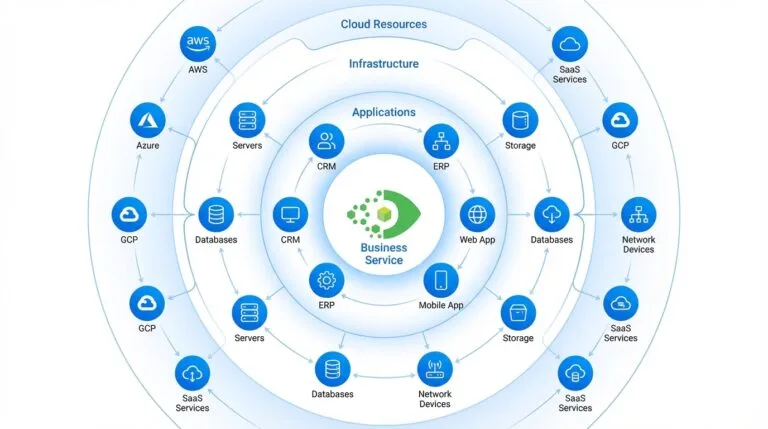
For IT Operations Managers and Directors running hybrid environments, the distinction is not academic. A single business service might span on-premises infrastructure, cloud workloads, SaaS platforms, and containerized applications. Get it wrong and your incident response is working from an incomplete picture. Change approvals go out without blast radius data. Your CMDB fills up with relationships that look right but do not reflect how services actually behave at runtime.
The rest of this article draws a clear line between the two and explains why the full operational picture requires both working together.
What is application dependency mapping?
Application dependency mapping (ADM) is the process of identifying and documenting how an application’s components interact with each other and with the infrastructure they run on.
Think of it as a technical inventory of connections. ADM answers one core question: what talks to what, at the component level?
What ADM shows you
ADM captures relationships between:
- Application modules, libraries, and services within a single application stack
- APIs and integration points between applications
- Databases, message queues, and caching layers that applications depend on
- Network ports, protocols, and communication paths
- Underlying compute, storage, and network infrastructure components
The output is a dependency map — a structured record of how components connect, what they call, and what they rely on to function. This data lives at the configuration item (CI) level in your CMDB, describing individual components and their direct relationships.
When ADM matters most
ADM is most valuable during the build and change phases of the IT lifecycle:
- Architecture decisions: Before you redesign or replace a component, you need to know what depends on it and what it depends on.
- Change management: A proposed change to a database instance or middleware layer needs dependency data to assess risk accurately.
- Security risk assessment: Knowing which components carry known vulnerabilities and what they connect to starts with accurate dependency mapping.
- Migration planning: Moving workloads to a new environment without ADM is guesswork. You need to know every dependency before anything moves.
ADM gives your teams the component-level ground truth they need to make informed decisions before something is deployed or changed.
What is service mapping?
Service mapping takes dependency data and organizes it around business services. Where ADM answers “what connects to what,” service mapping answers “how does this business service depend on the infrastructure beneath it, and what breaks if a specific component fails?”
It is an operational view. A service map traces the path from a named business service (your customer-facing payment portal, your internal HR system) down through every application component, middleware layer, server, network device, and cloud resource keeping it alive.
What service mapping shows you
A service map shows:
- The end-to-end dependency chain from business service to underlying infrastructure
- Which CIs are in scope for a given service
- The blast radius of a failure or change — which services are affected if a specific CI goes down or is modified
- Ownership and accountability at each layer of the service
- Change history and vulnerability exposure across the service’s dependency chain
This is not a static diagram. Effective service mapping reflects live, discovery-sourced ground truth — the actual state of your environment at runtime, not what someone documented six months ago.
When service mapping matters most
Service mapping is most valuable during the operate phase of the IT lifecycle:
- Incident response: When an alert fires, you need to know immediately which business services are affected, who owns them, and what the full scope of impact looks like. Service mapping gives you that context without manual investigation.
- Change approvals: Before approving a change, you need to see which services sit above the CI being modified. Service mapping shows you the blast radius before you approve or reject.
- Audit readiness: Demonstrating that you understand your service dependencies, and can show the evidence, is a requirement for SOC 2 Type 2, ISO 27001, and similar frameworks.
- SLA management: If you do not know which infrastructure components underpin a service with a defined SLA, you cannot manage that SLA with any real confidence.
The core distinction: component-level vs service-level
Here is the simplest way to hold the distinction:
Application dependency mapping is component-level. It describes the technical relationships between individual CIs — what calls what, what depends on what, at the granular level of ports, processes, and software components.
Service mapping is service-level. It organizes those component relationships into a business-meaningful view, showing how a named service depends on the infrastructure beneath it and what the operational consequences are when something in that chain changes or fails.
ADM provides the raw dependency data. Service mapping puts that data to work for the people responsible for keeping services running and managing risk.
One without the other leaves a gap. ADM without service mapping gives you a detailed technical picture with no business context. Service mapping without accurate, discovery-sourced ADM data gives you a business view built on incomplete or stale foundations. That is more dangerous than having no map at all, because it creates false confidence.
Build phase vs operate phase: a practical framing
A useful way to think about where each capability fits is to map them to the IT lifecycle.
Build phase (design, develop, deploy, change):
- ADM is your primary tool here
- You need to know what a component connects to before you change it, move it, or replace it
- Dependency data feeds change impact assessments, architecture reviews, and migration plans
- Security teams use ADM data to trace vulnerability exposure across the component graph
Operate phase (monitor, respond, manage, audit):
- Service mapping is your primary tool here
- When an incident occurs, you need a service-level view of impact, not a raw list of CI relationships
- Change approvals need blast radius context, not just a dependency list
- Audit evidence requires a clear, traceable line from business service to underlying infrastructure
In practice, these phases overlap. A change that starts in the build phase has operational consequences that play out in the operate phase. Both capabilities need to draw from the same underlying data source: your CMDB. And that data needs to reflect the live state of your environment, not a snapshot from the last discovery cycle.
Why you need both — not one or the both
The teams that get the most value from dependency and service data treat ADM and service mapping as complementary, not competing. Here is what that looks like in practice:
- Automated discovery runs continuously, capturing live dependency data across your hybrid environment using agentless scans, optional agents, and API integrations
- That data populates your CMDB with accurate, discovery-sourced ground truth at the CI level (ADM)
- Service mapping organizes those CI relationships into service-level views that reflect current runtime state
- When an incident fires, your operations team sees the affected service, the dependency chain, the blast radius, and ownership without manual investigation
- When a change is proposed, the approver sees which services sit above the affected CI and what the risk exposure is
- When an auditor asks for service dependency documentation, you can produce it from the same continuously updated source that drives your day-to-day operations
This is not a theoretical architecture. It is the operational model mature IT organizations are building right now: to reduce MTTR, prevent failed changes, and maintain audit-ready visibility across hybrid environments.
Looking ahead, AI-assisted operations will only amplify this need. Any automation that triggers remediation must know the blast radius before it acts, which requires both ADM (what connects to what) and service mapping (which services are affected) working from the same live, governed data.
How Virima delivers both in one platform
Virima delivers trusted runtime truth for agentic IT — live, explainable, discovery-sourced ground truth across assets, services, dependencies, ownership, change history, and blast radius. For teams that need both ADM and service mapping, Virima provides both in a single platform built on automated multi-source discovery and an always-accurate CMDB.
Automated discovery
Virima’s discovery engine runs recurring scheduled scans across your hybrid environment using agentless scans, optional agents, and API integrations. It captures dependency relationships at the component level as they exist right now, not as they were documented at last quarter’s architecture review. This is the discovery-sourced ground truth that makes both ADM and service mapping reliable.
Always-accurate CMDB
Virima’s CMDB stores and normalizes that discovery data, maintaining accurate CI records and relationships across your entire estate. It is the single source of truth that feeds both dependency mapping and service mapping with consistent, governed data.
Service mapping at the business-service level
Virima’s service mapping organizes CI-level dependency data into service-level views. It shows how business services depend on underlying infrastructure, and what the blast radius is when something in that chain changes or fails.
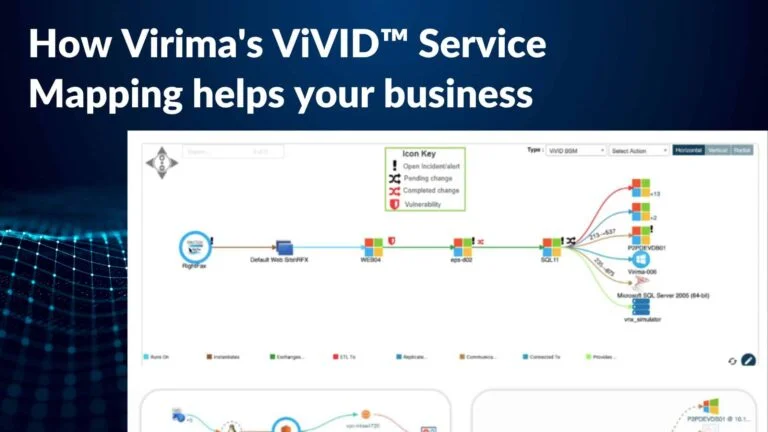
ViVID™: live operational overlays on every service map
Virima Visual Impact Display (ViVID™) brings these views to life. It overlays open incidents, recent changes, pending changes, and known vulnerabilities directly onto your service maps. You see the service, the dependency chain, the affected CIs, and the operational events on each one in a single live view. Each status is mapped to the specific CI it applies to, not shown as a generic alert.
Because all of this draws from the same discovery-sourced data layer, you are not maintaining two separate systems with two separate data models. ADM and service mapping are two views of the same continuously updated infrastructure intelligence.
Quick comparison: ADM vs service mapping
| Dimension | Application Dependency Mapping | Service Mapping |
|---|---|---|
| Primary question | What connects to what? | How does this service depend on infrastructure? |
| Level of view | Component / CI level | Business service level |
| Primary lifecycle phase | Build, change, migrate | Operate, respond, audit |
| Key use cases | Change impact, architecture, security risk, migration | Incident response, change approval, SLA management, audit |
| Output | Dependency graph of CIs and relationships | Service-to-infrastructure dependency map with blast radius |
| Who uses it most | Architects, engineers, security teams, config managers | IT ops, service desk, change managers, auditors |
| Risk when missing | Blind spots in change risk and security exposure | Slow incident response, inaccurate change approvals, audit gaps |
Start With Trusted Runtime Truth
The difference between application dependency mapping and service mapping is not just semantic. It is the difference between knowing what connects to what and knowing what breaks (and for whom) when something in that chain changes.
Both capabilities are necessary. Neither works well without accurate, live, discovery-sourced data underneath them. As IT operations teams take on more automation, and as audit, security, and compliance requirements tighten, the quality of that underlying data is not a nice-to-have. It is the foundation everything else depends on.
Virima gives you both ADM and service mapping in one platform — built on recurring multi-source discovery and an always-accurate CMDB, with ViVID™ overlaying live trusted runtime truth onto every service map so your team can see exactly what exists, what’s connected, and what will break before they act.
Read more in our whitepaper Discovery and Service Mapping: how they create value for IT, or request a demo at virima.com.
FAQs
Q: Is application dependency mapping the same as service mapping? No. Application dependency mapping operates at the component level, documenting how individual application components, services, and infrastructure elements connect to each other. Service mapping operates at the business service level, showing how a named service depends on the full underlying stack and what breaks when a component in that chain fails. They are related, but they serve different purposes.
Q: Do I need both ADM and service mapping, or can I get by with one? You need both for a complete operational picture. ADM without service mapping gives you detailed technical data with no business context. Service mapping without accurate ADM data gives you a business view built on shaky foundations. The two capabilities work best when they draw from the same live, discovery-sourced CMDB data.
Q: What is blast radius in the context of service mapping? Blast radius describes the scope of impact when a specific CI fails or is changed. A service map shows which business services sit above a given CI, so you can assess how far a failure or change would propagate before you act. This is essential for change approvals and incident triage.
Q: How does automated discovery relate to application dependency mapping? Automated discovery is what keeps ADM accurate and current. Without continuous discovery, dependency maps go stale quickly, especially in hybrid environments where workloads shift frequently. Discovery captures the live state of component relationships and feeds that data into your CMDB, which is the foundation for both ADM and service mapping.
Q: Can service mapping work without a CMDB? Not reliably. Service mapping depends on accurate, normalized CI data to build trustworthy service-to-infrastructure views. Without a CMDB as the underlying data store, service maps are typically built manually or from point-in-time snapshots, both of which degrade quickly and create the kind of false confidence that leads to missed blast radius during incidents and change approvals.
Q: How does service mapping support audit readiness? Service mapping provides traceable, documented evidence of how business services depend on underlying infrastructure. For frameworks like SOC 2 Type 2 and ISO 27001, auditors want to see that you understand your service dependencies and can back that up with current, accurate data. A service map built on discovery-sourced ground truth satisfies that requirement far more effectively than manually maintained documentation.
Q: What is the difference between a dependency map and a service map in a CMDB? A dependency map in a CMDB describes relationships between individual CIs — for example, an application server depends on a specific database instance. A service map organizes those CI relationships around a business service, showing the full dependency chain from the service down to every CI that supports it, including ownership, change history, and vulnerability exposure at each layer.
Q: How is service mapping different from network mapping? Network mapping shows physical and logical network topology: switches, routers, subnets, and the connections between them. Service mapping shows how a business service depends on every component beneath it, which includes network devices but also application layers, databases, cloud services, and middleware. A network map answers “how is the network laid out?” A service map answers “what breaks the payroll service if this component fails?” The two are complementary. Network mapping is one input into a complete service map, not a substitute for one.