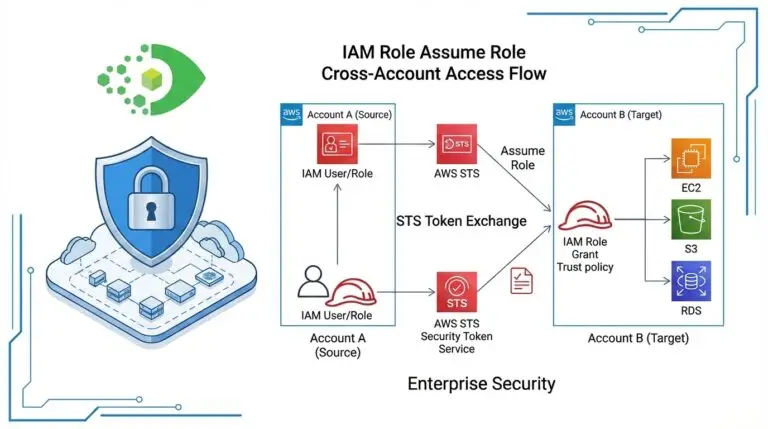
AWS Assume Role for CMDB Discovery: Why Cross-Account Access Control Matters for Security
TLDR
Using static AWS Access Key ID and Secret Access Key for CMDB discovery is a security risk. AWS Assume …
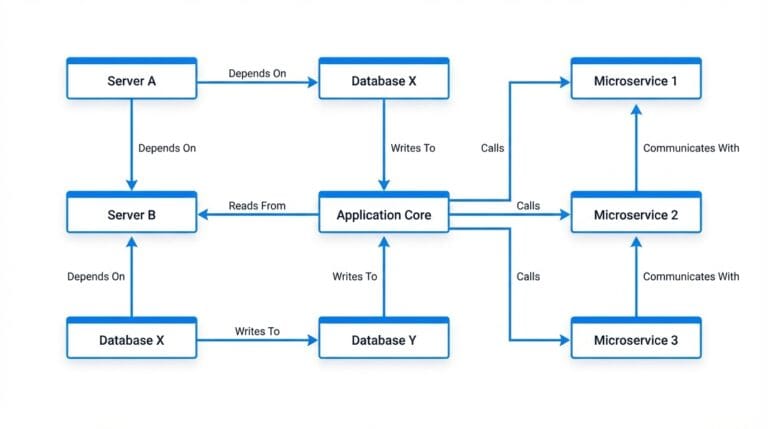
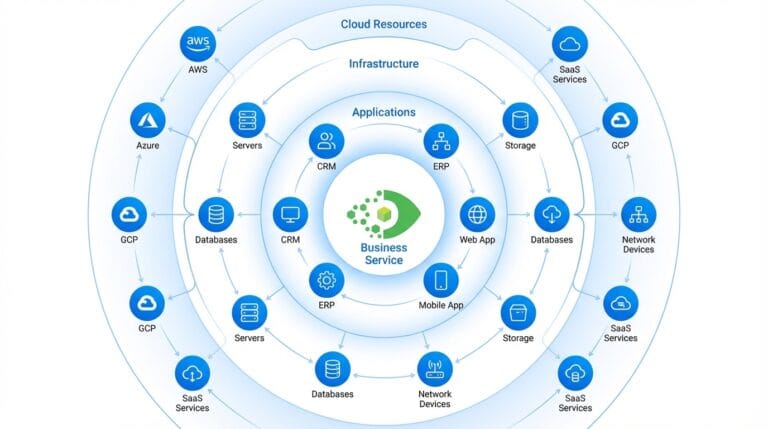
What Is ViVID Service Mapping? How Virima Visualizes IT Service Dependencies
ViVID (Visual Impact Display) is Virima’s service mapping and visualization engine, available in Virima 6.1.1. It converts the relationship data …
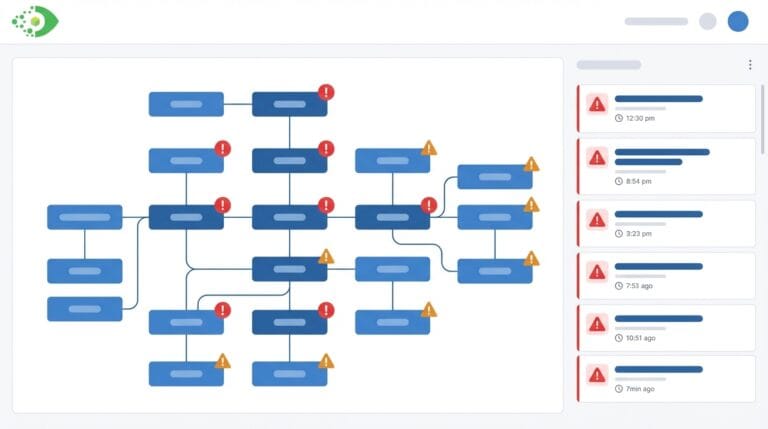
How to Overlay ITSM Incidents and Vulnerabilities onto Your IT Service Map for Faster Root Cause Analysis
…Root cause analysis (RCA) is one of IT operations’ most time-critical activities, and one of its most poorly supported. When
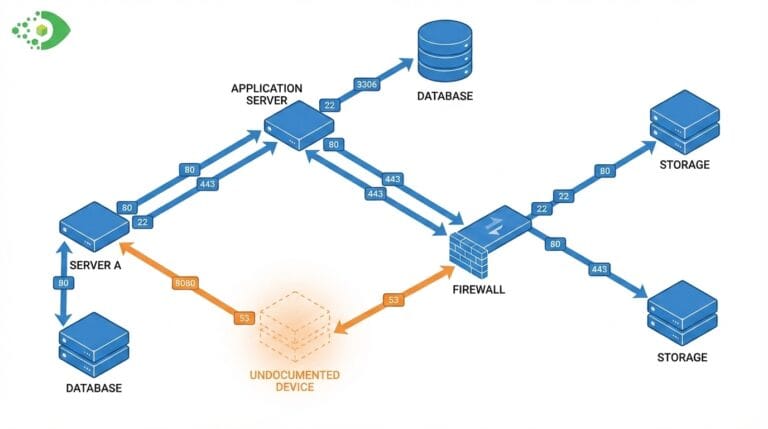
Communication Views in CMDB: How to See Host-to-Host Traffic Flows, Ghost Machines, and Open Ports
A CMDB tells you what devices you know about and how you have documented their relationships. It does not tell …
How to Discover and Map Pure Storage FlashArray in Your CMDB
TLDR
Pure Storage FlashArray arrays rarely appear in CMDBs because most discovery tools treat storage as out-of-scope. Automated SSH or …
5 Early Resolutions for Better IT Management in 2019 (Part 2)
Because it’s never too soon to think about improving IT – Part 2 of 2
It’s December, which means you …