Open Infrastructure Mapping Tools for Smarter Enterprise IT Management
Picture an outage bridge where the only “map” is a Visio diagram last updated two quarters ago. The network team sees link flaps. App owners see timeouts. Security wants to know whether the affected segment touches regulated data. Nobody can answer the one question that matters: what depends on what, right now. That moment is why “open infrastructure mapping tools” keep showing up in enterprise searches.
The first instinct in mid-to-large organizations is often to start with free or open-source tooling to regain visibility without committing to a platform too early.
This guide clarifies what infrastructure mapping is, why it matters in hybrid environments, and how to evaluate open-source and enterprise solutions. It is especially for regulated sectors where audit readiness, traceability, and access control are part of the job.
The tooling list includes both open favorites and enterprise options, plus decision guidance for choosing the right approach.
What is infrastructure mapping, and why does it matter?
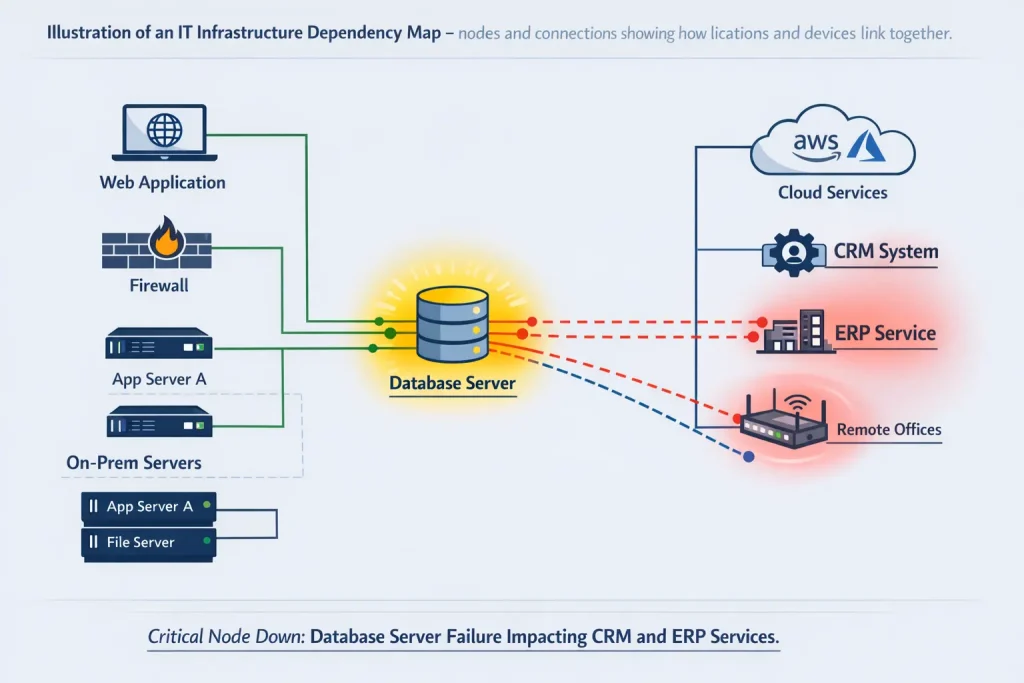
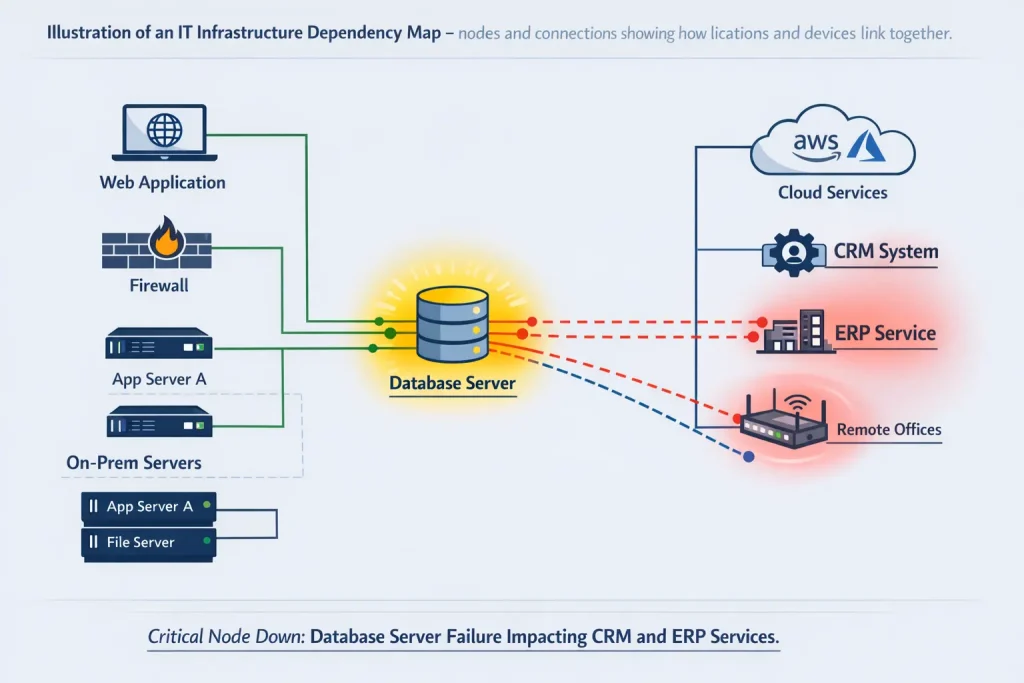
Infrastructure mapping is the process of discovering and visualizing IT assets and their connections, showing how devices and services are physically and logically linked.
This is commonly framed as a “visual representation” of network infrastructure and connections.
In enterprise operations, mapping is not a “nice-to-have diagram.” It is a risk-reduction mechanism:
- Visibility: A current map reduces blind spots and highlights what exists and how it connects, which is critical when environments sprawl across data centers and the cloud.
- Faster troubleshooting: Dependency context turns an alert storm into a prioritized blast-radius view (what’s impacted, what’s upstream/downstream).
- Planning & optimization: Migrations, refresh cycles, and cloud cost initiatives move faster when dependencies are explicit.
- Change impact analysis: Change approvals get safer when impacted services and downstream dependencies are visible.
- Compliance & audits: Regulated environments frequently require defensible evidence of system inventories and interconnections; mapping supports audit readiness by reducing undocumented components and relationships.
Transition point: Manual mapping rarely survives hybrid change velocity. That is where infrastructure mapping tools, open-source utilities through enterprise platforms, enter the conversation.
Challenges of mapping complex infrastructure (and the rise of open-source tools)
Modern infrastructure is defined by change:
- Hybrid and multi-cloud footprints
- Frequent provisioning/deprovisioning of workloads
- Shared services and third-party dependencies
- Layered ownership across teams and vendors
Manual documentation (Visio, spreadsheets) becomes outdated the moment a new instance is deployed or a switch is replaced.
This drives adoption of automated mapping tools and explains why open-source infrastructure mapping tools often become the starting line: budget-friendly, flexible, and powerful in the hands of a skilled team.
Open tools can be excellent, but trade-offs tend to emerge around scale, support, integration, and governance. Those trade-offs matter most in regulated sectors, where tooling must not become a new compliance gap.
Top open-source infrastructure mapping tools (free solutions)
Open-source tools typically excel at parts of the mapping problem: discovery, topology, monitoring, and documentation. Strong outcomes come from pairing tools intentionally.
Tool #1 – Nmap (Network Mapper): Discovery king
Nmap is widely used for network discovery and security auditing. It identifies hosts, open ports, and service fingerprints, often acting as the “discovery layer” behind a mapping workflow.
Example use-case: A hospital network monitoring team runs an overnight scan across a /16 segment and discovers an unmanaged device on your network on clinical VLANs. The output becomes the starting point for controlled remediation and map accuracy improvement.
Best for: Fast discovery, security-driven inventory validation, feeding downstream tooling
Limitations: Not a mapping UI; visualization requires additional tooling
Tool #2 – Netdisco: Network inventory & topology tracker
Netdisco is a web-based network management tool suited for small to very large networks, collecting IP/MAC data into a database via SNMP (and other device interfaces).
Competitor analyses highlight topology discovery patterns using protocols like SNMP, CDP, and LLDP, which are useful for building switch-port and adjacency context.
Best for: LAN topology, switch-port mapping, MAC/IP correlation
Limitations: Network-centric; limited application/service dependency context
Tool #3 – OpenNMS Horizon: monitoring + topology visualization
OpenNMS can display topology maps and discover node connections via link discovery protocols accessible through SNMP (for example, via Enhanced Linkd / Enlinkd).
Example use-case: A university uses OpenNMS to track campus network segments; when a core switch fails, topology context accelerates identification of impacted buildings and services.
Best for: Monitoring-centric environments needing topology context
Limitations: Configuration-heavy; service mapping typically requires additional modeling
Tool #4 – Zabbix: Infrastructure Monitoring with Basic Mapping
Zabbix is frequently used for monitoring at scale; many teams pair its monitoring data with separate topology visualization to improve operational context.
Best for: Metrics + alerting backbone
Limitations: Mapping is not the primary capability; dependency/service mapping is limited
Tool #5 – NetBox: Network Source of Truth (Documentation + Modeling)
Net Box shines as a structured system for IPAM/DCIM and network mapping tools solution modeling. It improves documentation rigor and reduces diagram drift, but depends on disciplined updates and/or automation integrations.
Best for: Network documentation maturity, modeling standards
Limitations: Not “auto-mapping” by default; discovery is typically integrated externally
Tool #6 – iTop (open-core): CMDB foundation
iTop can provide CMDB structure and ITIL-aligned relationships, often used as a system-of-record layer when teams want stronger governance.
Best for: CMDB structure and process alignment
Limitations: Discovery and dynamic dependency mapping generally require companion tools
Tool #7 – Wireshark: Packet-level reality check
Wires Hark is not a mapping tool, but it helps validate traffic relationships and unexpected connections, which often reveal hidden dependencies and security exposures.
Best for: Deep troubleshooting, verifying true dependencies
Limitations: Not scalable as an enterprise mapping system
Tool #8 – Diagramming tools (Lucidchart): Manual map presentation
Lucidchart is a diagramming tool often used to document infrastructure and share clean visuals across stakeholders.
It works best when fed by validated discovery outputs; otherwise, it becomes another manual artifact that drifts.
Best for: Executive-ready diagrams once data is known
Limitations: Manual upkeep; not automated mapping
Pro tip: Open-source mapping succeeds when tools are combined intentionally—e.g., Nmap for discovery + Netdisco for topology + NetBox/iTop for governed documentation. The hidden cost is integration and maintenance effort, which becomes the limiting factor at scale.
Leading commercial infrastructure mapping solutions (and why they matter)
Open infrastructure mapping tools are valuable. Many enterprises still evaluate commercial platforms because they reduce operational friction in three ways: faster deployment, support/SLAs, and pre-built integrations with CMDB/ITSM and cloud APIs.
Common enterprise options include:
- Virima – designed to connect mapping to operational context: service and application dependency mapping, and dynamic visuals via Virima Visual Impact Display (ViVID™) that can include infrastructure dependencies plus business services and related records.
- Auvik – automated network management discovery and topology visualization, positioning network mapping solution as an always-updated operational view.
- SolarWinds Network Topology Mapper (NTM) – frequently used in enterprises already standardized on SolarWinds tooling (tooling details vary by deployment).
- Device42 / Faddom – frequently discussed for discovery and dependency mapping workflows (vendor scope varies).
The value of enterprise tools is not “more dashboards.” It’s a more usable context, especially when mapping must be defensible for audits, tied to change records, and consumable by multiple stakeholders.
Open vs. commercial tools – how to choose the right approach
This decision is rarely about license price alone. It is about risk tolerance, operating model, and governance requirements.
Open-source vs commercial tools comparison (at-a-glance)
| Factor | Open-Source Tools | Commercial Tools |
| Initial cost | $0 license cost | Subscription/license fees |
| Maintenance effort | High (in-house setup, upgrades, integrations) | Low/Moderate (vendor handles platform upkeep; team configures) |
| Scalability | Varies (some scale well; tuning required) | Built for enterprise scale and performance testing |
| Support | Community support; no guaranteed SLA | Vendor support + SLAs; professional services available |
| Integration | Typically stronger RBAC, audit logging, and enterprise controls | Pre-built integrations (CMDB, ITSM, cloud, identity, etc.) |
| Security & compliance | Deployment must be secured; key features vary by tool | Typically stronger RBAC, audit logging, enterprise controls |
Decision guidance that holds up in regulated sectors:
- Open-source works well for discovery pilots and focused topology visibility.
- Commercial platforms become compelling when mapping must be continuously accurate, auditable, and integrated into change, incident, and CMDB workflows.
Best practices for implementing infrastructure mapping
1) Define scope and operational purpose
Mapping initiatives fail when “map everything” becomes the goal. Mature programs start with critical services: customer-facing platforms, revenue paths, and regulated data flows.
2) Establish an asset baseline
Run discovery and validate results with owners. Baselines must include “unknowns” (unmanaged devices, shadow assets) because those are often audit and security risks.
3) Choose tools strategically (and accept multi-tool reality)
Open-source stacks can work, but require defined data flows: where discovery lives, where the “source of truth” lives, and how updates propagate.
4) Validate the map like production data
Maps influence decisions. Accuracy matters. A short validation workshop with network devices, servers, apps, and security stakeholders prevents false confidence.
5) Operationalize continuous updates
Maps drift unless tied to a change in velocity. Continuous IT discovery and relationship reconciliation is the maturity line.
This is where platforms such as Virima are often introduced when mapping must remain aligned with operational workflows.
Virima Service Mapping provides automated service maps and dependency mapping, with ViVID™ designed to visualize dependencies alongside context such as business services (and related operational records where applicable), supporting decision-making rather than static documentation.
Compliance, security, and infrastructure maps (not optional in regulated IT)
Infrastructure maps can support audit readiness by providing evidence of what exists and how systems connect. But the mapping tool itself also becomes part of the control surface.
Controls that matter:
- Role-based access to mapping views and discovery credentials
- Audit trails for changes to relationships and CMDB records
- Secure storage and access policies for exported maps and inventories
Open-source caution: Security posture depends on deployment discipline. Access to a complete network performance map is sensitive; governance gaps can create risk even while improving visibility.
Navigating the mapping journey
Infrastructure mapping is not documentation work. It is operational risk management.
Open tools provide powerful building blocks, especially for discovery and topology. Enterprise platforms become valuable when mapping needs to remain continuously accurate, governed, and integrated into IT operations and compliance workflows.
Virima fits naturally when the problem shifts from “getting a map” to “maintaining trusted context”: automated service mapping features and dependency visibility through ViVID™ are built to support decision-making across incident response, change, and audit readiness, not just visualization.
For organizations ready to move from ad-hoc mapping to a continuous, audit-ready service context, schedule a Virima walkthrough to see how automated discovery + service mapping + ViVID™ can reduce blind spots and accelerate infrastructure decisions in hybrid environments.
Frequently Asked Questions (FAQs)
Are open infrastructure mapping tools secure enough for financial or healthcare environments?
They can be, but require careful deployment, access control configuration, and often additional tooling to meet audit requirements.
What breaks first as environments scale?
Dependency accuracy. Without automated reconciliation, maps drift, undermining incident response and compliance confidence.
Can open tools integrate with ITSM or CMDB systems?
Some can, but integration is often custom or manual. Native, governed synchronization is limited.
When should teams consider moving beyond open tools?
When downtime risk, audit pressure, or operational scale demands consistent service-level visibility and historical traceability.