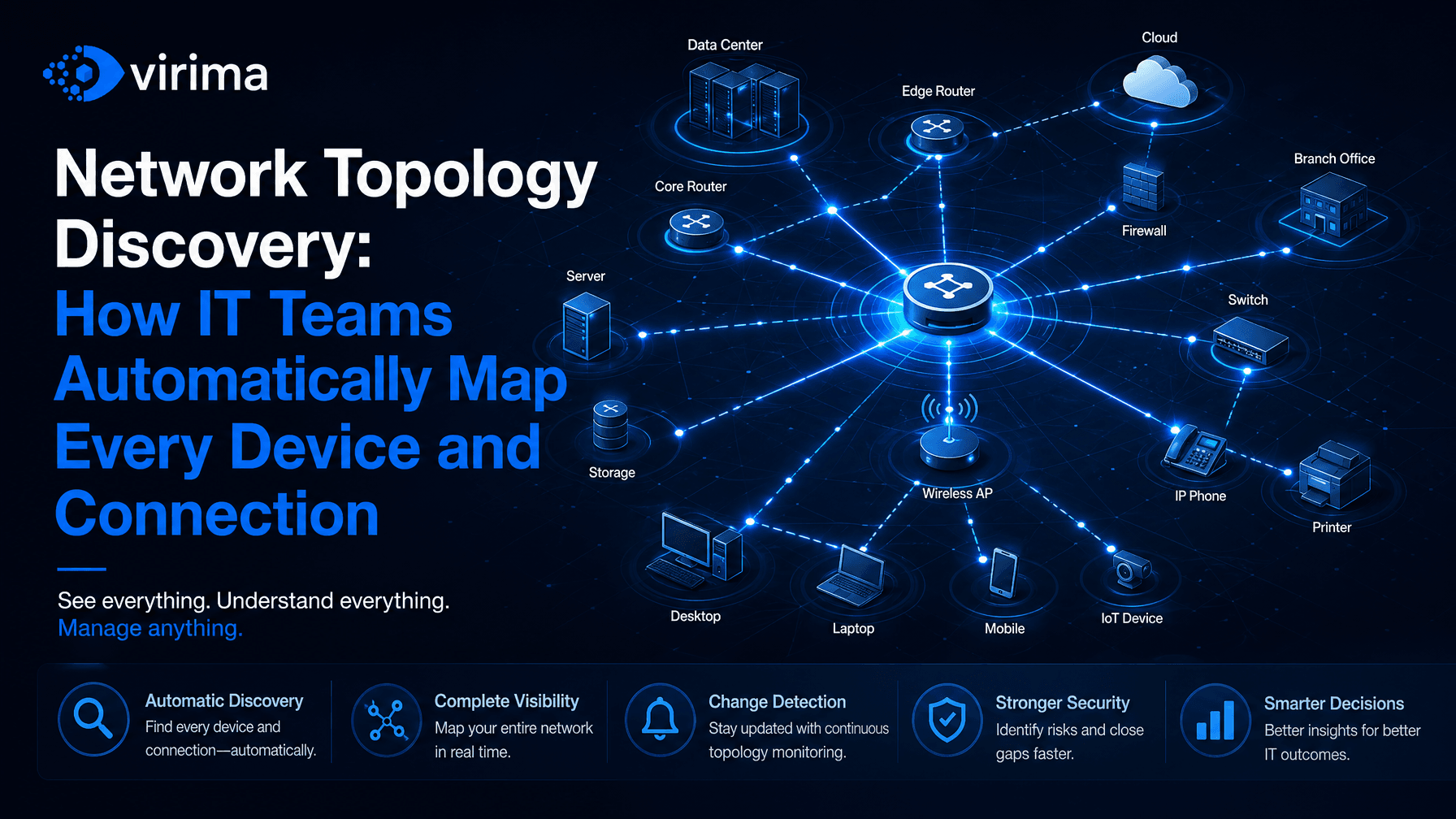
Network Topology Discovery: How IT Teams Automatically Map Every Device and Connection
The Problem With Manual Network Maps
Your network diagram was accurate the day someone drew it. That was probably six months ago, maybe longer. Since then, three servers got decommissioned, two cloud workloads spun up, a dozen remote laptops joined the environment, and a contractor plugged in a switch nobody logged.
The diagram still looks clean. The network is not.
This is the core problem with manual network topology documentation: it goes stale the moment you finish it. IT Ops Managers and Directors at mid-to-large hybrid enterprises spend real hours maintaining diagrams that no longer reflect reality, then make real decisions on top of that fiction. Incident response slows. Change risk climbs. Blast radius becomes a guess.
Automated network topology discovery solves this by replacing the manual process with continuous, authoritative discovery that reflects what is actually running on your network right now — what exists, how it’s connected, what changed, what could break, and who owns it.
What Network Topology Discovery Actually Means
Network topology discovery is the process of automatically identifying every device, connection, and relationship on your network and building an accurate, up-to-date map of how they all fit together.
That means finding routers, switches, firewalls, servers, endpoints, virtual machines, containers, cloud instances, and the network paths between them. It means knowing which devices communicate with which, which services depend on which infrastructure, and which assets carry the most operational risk if they go down.
Done well, network topology discovery gives you:
- A complete inventory of every connected device, including ones you didn’t know existed
- A live picture of network paths and communication patterns
- Dependency chains that show how a failure in one place propagates to others
- Ownership and change history attached to every asset
- Vulnerability context tied to specific devices and their network position
This is not a map for the sake of having a map. It’s the foundation for faster incident response, safer change management, and policy-aware automation — the runtime truth your team and any AI agent acting in your environment need to make safe decisions.
Static Diagrams vs. Live Discovered Topology Maps
Most IT teams still rely on some combination of Visio diagrams, spreadsheets, and tribal knowledge. These are static artifacts — snapshots of the network at a point in time that require manual effort to update and are wrong almost immediately.
A live discovered topology map is different in every way that matters.
| Dimension | Static Diagram | Live Discovered Topology Map |
|---|---|---|
| Accuracy | Accurate at creation, stale immediately | Continuously refreshed from live discovery |
| Coverage | Only what someone documented | Everything discovery finds, including shadow IT |
| Dependencies | Manually drawn | Automatically derived from real traffic and config data |
| Change history | Manual updates or none | Tracked automatically with timestamps |
| Blast radius | Estimated by a person | Calculated from actual dependency chains |
| AI readiness | Not usable by AI agents | Structured, explainable, policy-aware context |
The difference matters most when something goes wrong. During an incident, you don’t have time to wonder whether your diagram is current. You need discovery-sourced ground truth that tells you exactly what’s connected, what depends on what, and what the downstream impact of a failure or change will be.
Why Hybrid IT Makes Network Topology Discovery Harder
Hybrid IT environments are the norm for mid-to-large enterprises. You’re managing on-premises data centers, multiple cloud providers, remote endpoints, and increasingly complex edge infrastructure — each with different discovery requirements, and no single protocol that covers all of them.
On-Premises Infrastructure
On-premises discovery typically combines SNMP, WMI, SSH, and network scanning to identify devices and pull configuration data. The challenge is coverage. Older devices may not respond to modern protocols. Network segmentation can block discovery agents. And relying on a single discovery method means you’ll miss things.
Authoritative on-premises discovery requires multi-protocol support, the flexibility to use both agent-based and agentless methods depending on the device type, and reconciliation logic that handles conflicting data from different sources.
Cloud Environments
Cloud infrastructure doesn’t respond to traditional network scans — you discover it through APIs. AWS, Azure, and GCP each expose different data models, and cloud topology shifts constantly as workloads scale, containers start and stop, and serverless functions execute.
Effective cloud topology discovery means pulling live data from cloud provider APIs, normalizing it into a consistent model, and connecting it to your on-premises topology so you see one complete picture instead of two separate maps.
Remote and Distributed Endpoints
Remote endpoints are the hardest to discover reliably. They aren’t always on the corporate network. They may connect through VPNs with inconsistent uptime, belong to contractors or third parties, and are often the entry point for security incidents.
Discovering them reliably requires a lightweight discovery agent that reports back even when the device is off-network, paired with reconciliation logic that prevents duplicate records when the same device shows up under different network conditions.
How Automated Network Topology Discovery Works
Automated discovery replaces the manual process with a continuous, scheduled, or event-triggered scan cycle that pulls data from every layer of your environment.
Here’s what that looks like in practice:
- Seed the discovery scope. You define IP ranges, cloud accounts, and domain scopes. Discovery starts from known anchors and expands outward.
- Multi-protocol scanning. The discovery engine runs SNMP, WMI, SSH, ICMP, NetFlow, and cloud APIs in parallel. Each protocol surfaces different data. Together, they build a complete picture.
- Agent-based discovery for deep coverage. For endpoints and servers where you need configuration-level detail, lightweight agents report hardware, software, running processes, and network connections directly.
- Relationship mapping. Discovery doesn’t just find devices — it maps the connections between them. Which switch port does each server connect to? Which application talks to which database? Which cloud load balancer fronts which compute instances?
- Normalization and deduplication. Raw discovery data is noisy. The same device may appear under multiple IP addresses, hostnames, or MAC addresses. Reconciliation logic resolves conflicts at the attribute level and writes a single authoritative record.
- Scheduled refresh. Discovery runs on recurring scheduled cycles configured to match the pace of your environment — hourly, daily, or weekly depending on the infrastructure layer. Each cycle detects new assets, changed attributes, and updated relationships, and writes findings directly to the CMDB.
The result is a live, explainable topology map that mirrors your actual environment — not a snapshot from last quarter.
For the complete picture of how every discovery protocol contributes to CMDB accuracy, see our network device discovery guide
From Discovery to Service Map: Introducing ViVID™
Discovering devices and connections is the first step. Making that data operationally useful is the next one.
Virima’s ViVID™ (Virima Visual Impact Display) takes the output of live network topology discovery and renders it as dynamic service maps showing assets, dependencies, ownership, and blast radius in a single view. You can see how a specific server connects to the services that depend on it, which downstream systems would be affected by a failure or change, and who owns each component.
This isn’t a static diagram you maintain by hand. ViVID™ maps update automatically as discovery refreshes the underlying CMDB. When a new device appears, it shows up in the map. When a dependency changes, the map reflects it. When a vulnerability is detected on a specific asset, you can see its position in the service dependency chain and understand the real risk — not just the theoretical one.
For IT Ops Directors managing incident response, that means arriving at a major incident with an accurate picture of the environment, not a six-month-old Visio file. For change managers, it means assessing blast radius before approving a change, not after causing an outage.
Explore Virima’s IT discovery capabilities and see how ViVID™ service maps surface live topology context for every asset.
What Good Discovery-Sourced Ground Truth Looks Like
Not all discovery outputs are equal. A list of IP addresses isn’t the same as discovery-sourced ground truth. Four things separate a useful topology map from a basic scan result:
Source traceability. Every asset and every attribute traces back to its discovery source, the protocol that found it, and the timestamp it was last verified. When two sources disagree about a server’s hostname or owner, you can see exactly where each value came from.
Reconciliation at the attribute level. Raw discovery data contains duplicates, conflicts, and gaps. Authoritative reconciliation resolves these at the attribute level, picking the most authoritative value for each field instead of letting one source overwrite another wholesale.
Freshness you can trust. Continuous discovery reflects what’s actually running now, not a quarterly snapshot. Schedules adjust to the pace of change in each environment — minutes for cloud and containers, hours or days for stable on-prem.
Impact you can act on. Every asset is connected to the services and people it affects. Given any device or group of devices, you can trace the downstream impact chain and identify which services, users, and SLAs are at risk.
When AI agents or automation workflows act on topology data, they need that data to be explainable. Structured, sourced, and traceable — not a black box. In agentic IT environments, policy guards every action, and the guardrails are only as good as the runtime truth feeding them.
This is the foundation Virima’s trusted runtime truth layer is built on — discovery-sourced context that lets humans move faster and AI agents act safely.
Common Network Topology Discovery Mistakes to Avoid
Even teams that invest in automated discovery often undercut their results with avoidable mistakes:
Scanning too infrequently. A weekly scan misses devices that appear and disappear between cycles. In dynamic cloud and container environments, topology can change in minutes. Your discovery schedule needs to match the pace of change in your environment.
Relying on a single discovery method. SNMP finds network devices. WMI finds Windows systems. SSH finds Linux. Cloud APIs find cloud resources. Run only one method and you get partial coverage with false confidence.
Ignoring reconciliation. Without normalization and conflict resolution, your topology map becomes as unreliable as the manual diagram you were trying to replace. Reconciliation is what turns raw scan output into authoritative ground truth.
Treating discovery as a one-time project. Network topology discovery isn’t something you complete — it’s a continuous process. Teams that treat it as a project end up back where they started within months.
Disconnecting topology from operations. A topology map that lives in a separate tool, disconnected from your ITSM, CMDB, and incident management workflows, doesn’t change how your team operates. Discovery data needs to feed the systems your team already uses.
FAQs
How do I discover network topology automatically?
Automated network topology discovery uses multi-protocol scanning (SNMP, WMI, SSH, cloud APIs) combined with agent-based collection on endpoints and servers. A discovery engine scans your defined scope, maps relationships between devices, normalizes the results, and continuously refreshes the topology map as your environment changes. Platforms like Virima automate this process end to end and feed the results into service maps and CMDB records.
What protocols are used for network topology discovery?
Effective network topology discovery uses several protocols in parallel because no single one covers every device class. SNMP discovers routers, switches, and managed network gear. WMI handles Windows servers and endpoints. SSH covers Linux and Unix systems. ICMP and ARP confirm reachability and surface MAC-to-IP mappings. NetFlow and sFlow reveal traffic patterns and live communication paths. Cloud APIs (AWS, Azure, GCP) discover cloud-native resources that don’t respond to traditional scans. Mature platforms run these in parallel and reconcile the outputs into a single authoritative record per asset.
What is the difference between network topology discovery and network monitoring?
Network monitoring tracks the health and performance of known devices in real time. Network topology discovery finds and maps all devices and their relationships, including ones you didn’t know existed. Monitoring tells you when something is broken. Discovery tells you what’s there, how it connects, and what depends on it. You need both, but discovery is the foundation.
What are the best network topology mapping tools for hybrid IT?
Effective network topology mapping tools for hybrid IT need multi-protocol discovery (not just SNMP), cloud API integration for AWS, Azure, and GCP, agent-based collection for remote endpoints, and relationship mapping that connects on-premises and cloud assets into a single topology view. Virima covers all of these and feeds discovered topology into live service maps via ViVID™. Other tools in this space include SolarWinds, ManageEngine, and Lansweeper, though coverage depth and relationship mapping capabilities vary significantly between them.
How often should network topology discovery run?
It depends on how fast your environment changes. For stable on-premises infrastructure, daily or weekly scans may be sufficient. For cloud environments and containerized workloads, you need near-continuous discovery triggered by change events. The goal is to keep your topology map current enough that you can trust it during an incident or before approving a change.
Can network topology discovery find shadow IT and unmanaged devices?
Yes — and it’s one of its most important functions. Automated discovery scans your IP ranges and cloud accounts regardless of whether a device is in your CMDB or asset register. Anything that responds to a discovery protocol gets found — unmanaged switches, personal devices, unauthorized cloud instances, and other assets that manual documentation would never surface.
How does network topology discovery support incident response?
During an incident, you need to know what’s connected to the affected system, what services depend on it, and what the blast radius of a failure or remediation action will be. A live discovered topology map gives you that context immediately, without asking someone to pull up a diagram or query multiple tools. This reduces mean time to resolution and prevents remediation actions from causing secondary outages.
How does network topology discovery support security and vulnerability management?
Network topology discovery is the foundation for accurate vulnerability management because you can’t patch what you don’t know exists. Continuous discovery surfaces shadow IT, unmanaged endpoints, and unauthorized cloud instances — the same blind spots auditors find and attackers exploit. Once an asset is discovered, its network position and dependencies become security context: which segment it sits in, what it can reach, what depends on it. When a vulnerability is reported against that asset, you can see its real blast radius instead of treating every CVE as equally urgent.
How does network topology discovery connect to CMDB accuracy?
Discovery is the primary feed for CMDB accuracy. Without continuous discovery, CMDB records go stale as devices are added, changed, and decommissioned. Automated topology discovery reconciles discovered data against existing CMDB records, flags discrepancies, and updates records based on what’s actually running in the environment — keeping your CMDB grounded in discovery-sourced truth rather than manual entries.
Conclusion
Manual network diagrams give you a false sense of control. Automated network topology discovery gives you actual control, because it reflects what’s really there.
For IT Ops Managers and Directors running hybrid environments, the gap between what your documentation says and what your network actually looks like is where incidents get worse, changes cause outages, and AI agents make unsafe decisions.
Continuous, multi-protocol discovery closes that gap. It gives your team live, explainable, policy-aware context about every device, connection, and dependency in your environment. And when that discovery feeds into service maps like ViVID™, it becomes operationally useful — not just technically interesting.
If your topology map is more than a week old, it’s already wrong. Start with authoritative discovery. Move faster. Act safely.
Explore the discovery and ViVID™ service mapping features directly to see how Virima delivers trusted runtime truth for agentic IT.