ITAM vs ITSM: How Virima Turbocharges Both
Organizations depend on two core IT disciplines to keep operations running: IT Asset Management (ITAM) and IT Service Management (ITSM). According to the 2025 State of ITSM report, organizations using modern ITSM capabilities resolve incidents up to 17.8% faster on average, highlighting how process maturity directly impacts operational performance.
Most teams treat them as separate functions. But ITAM and ITSM are more connected than they appear, and the organizations that integrate them well consistently outperform those that don’t.
What is the difference between ITAM and ITSM?
ITAM tracks what you own: every piece of hardware, software license, cloud instance, and endpoint across your environment. ITSM manages what you deliver: the services, workflows, and support processes your IT team provides to the business.
ITAM answers “what do we have?” and ITSM answers “how do we support it?” Both rely on accurate data to function well, and both suffer when that data is stale or incomplete. Organizations with strong ITAM programs see faster incident resolution, smoother change management, and fewer compliance surprises on the ITSM side.
IT Asset Management (ITAM): Taking control of your IT inventory
IT Asset Management covers the full lifecycle of IT assets, from procurement and deployment through maintenance to retirement. The goal: know exactly what assets you have, where they are, what state they’re in, and what they cost.
This includes hardware, software, cloud resources, and mobile devices. When you have that complete picture, every downstream IT process gets easier.
An effective ITAM strategy covers several key process areas:
Discovery and inventory
This is the foundation. IT discovery tools scan your network and deploy agents to identify and document every IT asset in the environment. Without accurate discovery, your asset inventory starts decaying from day one.
This becomes even more critical in modern environments where 77% of enterprises operate hybrid IT infrastructures, making manual tracking nearly impossible.
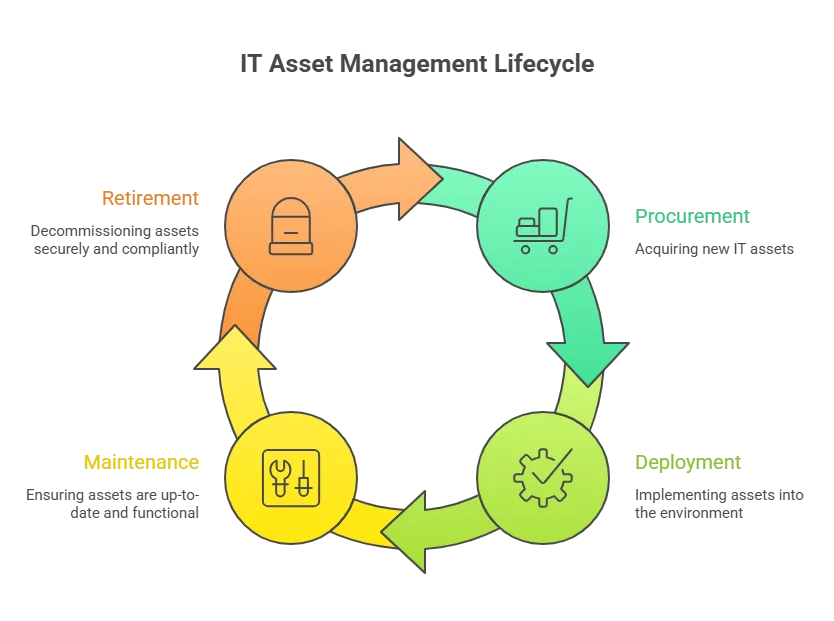
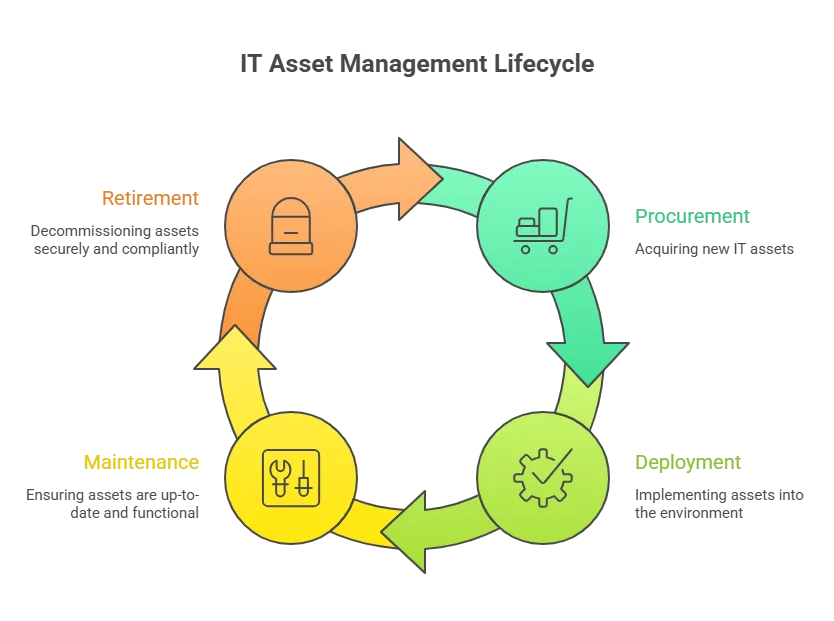
Software license management
Tracking software licenses keeps you compliant with vendor agreements and helps you avoid costly audits. Good ITAM tools show you which licenses are in use, which are sitting idle, and where you’re over- or under-licensed.
Asset tracking and reporting
ITAM goes beyond identifying assets. It tracks them through their full lifecycle: location, status, configuration, and ownership. That data feeds into reports that surface utilization trends, cost patterns, and risk areas.
Service request management
While typically an ITSM process, service request management also ties into ITAM. When users request new hardware, software installs, or asset reconfigurations through a service portal, ITAM data ensures the IT team knows what’s available and can fulfill requests accurately.
Asset maintenance and upgrades
Regular maintenance keeps IT assets running well. ITAM processes trigger timely software updates, hardware maintenance, and upgrades based on schedules or performance thresholds.
Asset retirement and disposal
Every asset eventually reaches end-of-life. ITAM ensures retired assets are disposed of securely and in compliance with regulations, protecting against data leaks and audit findings.
A well-run ITAM program delivers clear results:
- Lower IT costs: better asset visibility means fewer redundant purchases and higher utilization rates.
- Stronger security posture: license compliance tracking reduces software vulnerabilities and audit exposure.
- Better decisions: asset utilization and cost data drive smarter IT investment choices.
- Faster ITSM fulfillment: accurate asset data helps service desk teams resolve requests without guessing what’s available.
IT Service Management (ITSM): Streamlining IT service delivery
ITSM focuses on delivering IT services to users through structured, repeatable processes. The goal: make sure IT services align with business needs and are delivered efficiently.
Here’s how the key ITSM processes work in practice:
Service request management
This process gives users a standard way to request IT services through a self-service portal, email, or phone. Requests get logged, categorized, prioritized, and routed to the right team for action.
Incident management
When something breaks, incident management kicks in. The focus is on identifying, diagnosing, and resolving disruptions to restore normal operations as fast as possible with minimal user impact. Modern ITSM teams are improving here, with top-performing organizations reducing resolution times by up to 54% using automation and AI-driven workflows.
Problem management
Incidents are symptoms. Problem management digs deeper to find the root cause and prevent repeat failures. By analyzing trends in incident data, it identifies systemic issues and drives permanent fixes.
Change management
Changes to infrastructure, applications, or processes are inevitable. Change management ensures those changes are planned, tested, and reviewed in a controlled way, reducing the risk of service disruptions.
Service catalog management
The service catalog is the single reference for all IT services offered. It gives users clarity on what’s available, what the SLAs are, and how to request each service.
Service Level Management (SLM)
SLAs define the agreed service levels IT commits to. SLM processes make sure those commitments are documented, tracked, and met, creating accountability between IT and the business.
Continuous service improvement (CSI) ties it all together. CSI means regularly reviewing and improving ITSM processes so they keep pace with changing business needs and user expectations.
A strong ITSM program delivers:
- Consistent service quality: standardized processes mean reliable, repeatable IT delivery.
- Higher user satisfaction: users know what services exist and how to get them.
- Lower delivery costs: automation and streamlined workflows cut waste and speed up fulfillment.
- Better visibility and control: a centralized view of services and assets supports faster, smarter decisions.
ITAM vs ITSM: Where the two disciplines connect
ITAM and ITSM serve different functions, but they share a critical dependency: accurate, current data about IT assets and their relationships. When these two disciplines work together, the operational gains are real.
The CMDB: Shared foundation for both disciplines
Both ITAM and ITSM depend on a centralized CMDB, a single source of truth for all configuration items, their attributes, and their relationships. When the CMDB is accurate, incident teams can trace failures to root causes faster.
Change advisory boards can assess the blast radius before approving changes. Asset managers can tie costs to the services those assets support.
When is the CMDB stale? Every process built on top of it slows down.
Streamlined service request management
ITAM data on hardware, software, and user licenses integrates directly with ITSM service request workflows. When a user requests a new laptop, the service desk can instantly see what’s in stock, what’s allocated, and what needs procurement, no manual lookup required.
Enhanced change management
ITAM data on asset configurations and dependencies directly informs change management. When your change advisory board reviews a proposed change, they need to know what depends on the affected CIs. Accurate asset and dependency data turns change impact assessment from guesswork into a data-driven process.
Virima: Turbocharging both ITAM and ITSM
Virima is built to solve the exact problem that weakens both ITAM and ITSM: incomplete, inaccurate, or stale data about your IT environment. Here’s how Virima connects the dots across both disciplines:
Complete IT discovery with agentless and agent-based scanning
Virima’s IT discovery uses both agentless and agent-based scanning to find and inventory every asset in your environment: hardware, software, cloud instances, and non-IT assets. Discovery runs on recurring scheduled scans, so your asset inventory stays current once scanning is configured; no ongoing manual imports required.
With 140+ extendable probes covering on-premises infrastructure, AWS, and Azure, Virima provides broad coverage across data center, edge, cloud, and virtual assets, including devices and cloud resources that may not appear in your existing inventory.
Virima’s cloud discovery extends across AWS, Azure, and GCP environments. For AWS and Azure, API integrations import cloud objects directly into the CMDB for the same dependency mapping and ViVID™ overlay treatment as on-premises assets.
Service mapping and ViVID™ impact overlays
Virima’s service mapping builds a complete picture of how your IT assets connect to each other and to the business services they support. On top of those maps, Virima Visual Impact Display (ViVID™) overlays ITSM incidents, change requests, event management alerts, and NIST NVD vulnerability data, giving your teams a single view of assets, dependencies, and active risks.
This is where ITAM and ITSM data visually converge. When an incident fires, your team can see the affected CI, its upstream and downstream dependencies, any open change requests touching the same area, and known vulnerabilities, all on one map.
Seven ITSM integrations with bi-directional sync
Virima integrates with seven major ITSM platforms: ServiceNow, Jira Service Management, Ivanti, HaloITSM, Cherwell, Xurrent, and Hornbill. For ServiceNow, Ivanti, and Cherwell, bi-directional CMDB sync is fully documented. Jira Service Management and HaloITSM also support sync with Virima’s discovery and CMDB data.
CIs discovered by Virima can be synced to your ITSM platform directly, and granular business rules let you automate the promotion process so updates flow between systems without manual intervention.
For platforms with bi-directional sync, your ITSM teams work with current asset data without manual imports or reconciliation. Xurrent and Hornbill integrations enrich their CMDB and ITSM processes with Virima’s discovery and ViVID™ service mapping capabilities.
| How do you choose between separate ITAM and ITSM tools vs. a unified platform? Many organizations start with standalone ITAM and ITSM tools, then discover the integration gap the hard way: during a failed audit or a major incident where nobody could trace the root cause because asset data lived in a different system. The key question is data flow. If your ITAM tool can’t feed accurate, current CI data into your ITSM workflows in near-real-time, you’re maintaining two disconnected systems. Virima bridges this gap by acting as the discovery and CMDB layer that feeds directly into your existing ITSM platform through configurable sync. You don’t have to replace your ITSM tool. You make it work better by giving it accurate data. |
Vulnerability management with NIST NVD at no extra cost
Virima integrates with the NIST National Vulnerability Database at no additional cost. Known vulnerabilities are automatically mapped to the affected CIs in your environment, and ViVID™ overlays this data onto your service maps.
Your security and ops teams can prioritize remediation using Virima’s Service Value Rating (SVR), which ties each asset’s criticality to the business services it supports — so prioritization reflects actual business impact, not just CVSS scores.
Autonomic Social Discovery™ for non-discoverable data
Not everything about a CI can be found by scanning. Ownership, business criticality, lifecycle status, SLA assignments, and compliance policies require human knowledge.
Virima’s Autonomic Social Discovery™ automates the gathering of these non-discoverable attributes by routing targeted questions to the right people at the right time, keeping your CMDB complete without relying on manual data entry.
PinkVERIFY ITIL 4 certified
Virima is PinkVERIFY certified across six processes: Service Asset and Configuration Management, Change Management, Incident Management, Problem Management, Request Management, and Knowledge Management.
This isn’t a badge on a slide deck. It means Virima’s workflows align with ITIL 4 best practices out of the box, and your ITSM processes can trust the data Virima provides.
SOC 2 Type II compliant
Virima holds SOC 2 Type II certification, confirming that data handling, security controls, and operational processes meet independent audit standards. For organizations in regulated industries, this removes a procurement barrier.
| What ITIL processes connect ITAM and ITSM?ITIL defines several processes that explicitly bridge ITAM and ITSM. Service Asset and Configuration Management (SACM) is the most direct. It governs how CIs are identified, recorded, and maintained in the CMDB, which both ITAM and ITSM depend on.Change management relies on accurate asset and dependency data from ITAM to assess impact. Incident and problem management use CI data to trace root causes. Request fulfillment uses asset availability data to confirm what can be provisioned. When these processes share a single source of truth, an accurate, automatically maintained CMDB, the handoffs between ITAM and ITSM stop being manual and start being reliable. |
How Virima delivers measurable gains across ITAM and ITSM
Faster incident resolution
Accurate CI data and visual dependency maps mean incident teams identify root causes faster. When your ops team can see, on a single ViVID™ map, which assets are affected, what depends on them, and what vulnerabilities are in play, MTTR drops measurably.
Smoother service request fulfillment
Integration between Virima and your ITSM platform means the service desk works with current asset data, what’s available, what’s allocated, and what needs procurement. Requests get fulfilled on accurate data, not stale spreadsheets.
Lower operational costs
Virima surfaces redundant software licenses, underutilized hardware, and unmanaged devices across your environment, the spending most organizations don’t realize they have.
Combined with NIST NVD integration that catches vulnerabilities before they become incidents, Virima reduces both waste and unplanned downtime.
Complete visibility from a single platform
Virima provides a single source of truth across ITAM and ITSM: every asset, every relationship, every integration, every vulnerability, kept current through recurring discovery scans and direct ITSM integration.
Discovery data and ViVID™ overlays give both operational and strategic teams the visibility they need without switching between tools.
Data-driven decision-making
When your CMDB is accurate and your ITSM data is integrated, IT leaders can make informed decisions about capacity planning, vendor consolidation, infrastructure investment, and service improvements.
The data lives in a system that reflects your environment as it is today, not in a quarterly report that’s already outdated.
Unite ITAM and ITSM under one accurate data layer
The gap between ITAM and ITSM isn’t a strategy problem. It’s a data problem. When asset data is stale, incomplete, or siloed in a tool your ITSM platform can’t read, every process built on that data underperforms.
Virima closes that gap. Automated discovery keeps your CMDB current. ITSM integration keeps your service desk working with accurate, synced data. ViVID™ overlays connect assets, dependencies, incidents, and vulnerabilities in one visual layer. And Autonomic Social Discovery™ fills in the human-knowledge gaps that scanning alone can’t reach.
Ready to see how it works in your environment? Schedule a demo with Virima today.
FAQ
How does poor asset data affect IT service delivery?
Inaccurate or incomplete asset data creates a ripple effect across ITSM workflows. Incident teams waste time tracking down which server runs which application. Change managers approve changes without knowing what depends on the affected CI.
License audits catch your team off guard because nobody knew three departments were running the same software without proper licenses.
The cost isn’t just time. It’s unplanned downtime, failed changes, SLA breaches, and audit penalties. This is why organizations that invest in automated discovery and CMDB accuracy see measurable improvements in MTTR, change success rates, and audit readiness.
How does ITAM data improve incident management?
When a production server fails at 2 AM, the incident team’s first question is “what’s affected?” With accurate ITAM data feeding the CMDB, they can immediately see which applications run on that server, which business services depend on those applications, and which users will be impacted.
Without that data, the team is making phone calls, checking spreadsheets, and guessing. The difference between a 30-minute resolution and a 3-hour outage often comes down to whether the dependency data was accurate and current.