Virima and ORDR: CMDB Context for Security Visibility
It begins with a security alert.
ORDR detects a device on your network behaving outside its normal baseline. It’s reaching unfamiliar systems. Traffic patterns have changed. The behavior looks risky.
Security can see the signal clearly. With global cybercrime costs projected to reach $10.5 trillion annually by 2025, visibility without context can be financially devastating.
But then operations steps in with the harder questions. Who owns this device? What business service depends on it? Is it part of a regulated workflow? Was a change window approved?
Isolating it might stop a threat — or it might disrupt payroll, ERP, a critical customer application, or even an integrated order management system that supports revenue operations.
So the response slows down. Not because detection failed, but because context is missing.
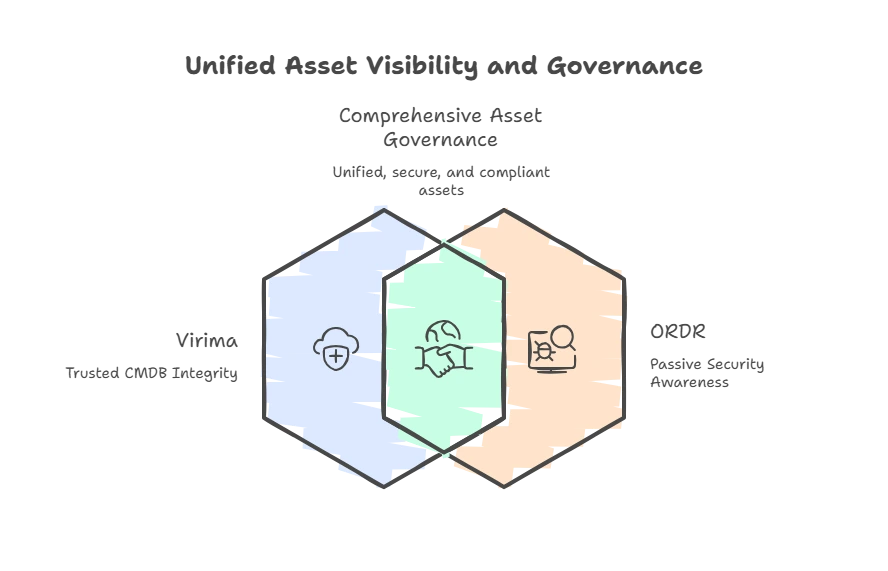
This is the gap many enterprises face. ORDR delivers real-time visibility and behavioral insight. Virima delivers ownership, service mapping, and governance clarity.
ORDR shows what is happening.
Virima shows what it affects.
Together, they turn security signals into confident, coordinated action.
Different design centres lead to complementary strengths
To understand why Virima and ORDR work better together, you first need to see why they were built differently. Each tool solves a different problem, and its key features reflect those different priorities from the very beginning. So, they focus on different priorities from the start.
We built ORDR to deliver fast security. It asks a simple question: what is on your network right now, and is it acting as it should? Therefore, it focuses on fast, passive monitoring and behavior analysis.
Because security decisions cannot wait, ORDR designed for real-time network security monitoring, gives you answers in real time, strengthening your enterprise security posture in a landscape where Microsoft processes 78 trillion security signals per day, making speed and clarity essential.
We built Virima to ensure operational accuracy. It asks a different question: what are these assets, who owns them, and what do they support? It also checks if your records are reliable enough to guide decisions.
So, Virima focuses on CMDB accuracy, service mapping, and clear ownership. It helps you trust your data and prove it in audits. Because governance decisions have long-term impact, you need records that stay accurate even after the incident ends.
The overlap between these two designs is small. However, that is not a weakness. In fact, it is the reason they work so well together.
Where ORDR’s visibility ends, Virima’s context begins. Then, where Virima’s records need proof from live network data, ORDR provides that signal. Because of this, each platform strengthens the other and increases your overall value.
Why the Discovery purpose matters more than Discovery technique
The most common comparison between Virima and ORDR is discovery. At first glance, both platforms discover devices. But that matters more than ever because two out of three organizations say their external attack surface expanded in the past 12 months, increasing the number of “unknowns” teams must account for. So, it may seem like they do the same thing.
However, they solve very different problems with discovery. ORDR discovers devices to quickly spot risk and unusual behavior. In contrast, Virima discovers assets to build trusted records and clear ownership.
Once you understand this difference, you stop seeing them as alternatives. Instead, you see how each one supports a different step in your decision process.
1. How Virima’s discovery model supports CMDB integrity
Virima uses multiple discovery (both agent based and agentless) methods to build a trusted, reconciled view of your environment. Using credentialed scans, APIs, and agent-based or agentless methods, it gathers infrastructure data across cloud and on-premises.
In AWS and Azure, Virima uses APIs to discover compute, storage, and databases, including resources that network scans miss.
This matters for security as much as operations. Cloud resources that spin up outside formal provisioning processes, a new S3 bucket, an unregistered VM, and an untagged database can go weeks without appearing in your CMDB. When they do appear in ORDR’s network traffic, Virima gives you somewhere to anchor them: a record, an owner, a service relationship.
On-premises, agents collect detailed host data, hardware, software, services, patches, and configurations, while agentless methods cover devices without agents.
Most importantly, Virima reconciles everything into a single authoritative CMDB record, ensuring that insights coming from platforms like ORDR integrate cleanly with your existing ITSM workflows and governance processes. It removes duplicates, assigns ownership, and links assets to the services they support.
This reconciliation keeps ViVID™ accurate and reliable. Service maps stay current, supporting change management software, impact analysis, compliance, and audits — where correctness matters more than raw speed.
2. How ORDR’s passive discovery expands security awareness
ORDR discovers devices by watching network traffic. It uses SPAN and TAP feeds, packet inspection, and flow analysis.
That visibility matters because research shows 69% of ransomware attacks started with a malicious email, and compromised endpoints often become the launch point for abnormal internal traffic. It does not need agents, credentials, or prior records. Instead, it learns about devices from how they behave on the network.
This is a powerful capability that Virima does not try to copy. It matters most for devices that are hard to govern. For example, think about building systems, facility controllers, printers, AV equipment, and shadow IT devices.
You often cannot install agents on these systems. You also cannot scan them with credentials, and they may never appear in ITSM tools. However, they still communicate on the network. Because they send traffic, ORDR can see and profile them.
ORDR answers a simple question: What is actually on the wire right now — a capability that defines effective order software built for continuous order including security monitoring. In contrast, Virima asks: What can you see and verify through managed paths? Both answers matter, and you need them together.
The devices that ORDR finds, but Virima does not yet manage, often carry the highest risk. They can create hidden compliance gaps and unknown exposure. Therefore, once ORDR surfaces them, you should bring them into your governance framework with Virima.
Unmanaged devices introduce visibility without ownership
ORDR excels at discovering devices with no operational record — facilities controllers, conference room systems, and unmanaged contractor endpoints. If it communicates on the network, ORDR can see it.
But discovery is only the first step. Once an unknown device is flagged, governance questions immediately follow:
| Who owns this device? What service does it support or threaten? What is its lifecycle status? Should it be isolated, enrolled, or escalated? |
Without a trusted system of record, these questions stall — especially in environments where teams must track orders, financial systems, or regulated workflows with precision. Findings pile up. Ownership remains unclear. Risk stays open.
This is where Virima adds control, bridging the gap between raw including order security detection and structured operational ownership within your order software ecosystem.
When an ORDR-discovered device enters Virima, you can:
| Assign clear ownership Define lifecycle status Link it to business services Visualize impact through ViVID™ dependency mapping |
Instead of debating in email threads, teams see service impact immediately — and act with clarity.
Behavioural risk signals versus service impact understanding
How ORDR identifies behavioural risk patterns
ORDR builds a communication baseline for every device it sees, reinforcing its role as a network security platform purpose-built for adaptive behavioral threat analytics.
It learns what normal looks like, such as who the device talks to and how often. It also tracks which protocols it uses and in what pattern. When behavior changes, ORDR flags it right away.
Because of this, ORDR can detect lateral movement early. It can spot protocol misuse and even find a new device within minutes of connection. So, you gain fast visibility into unusual activity.
In short, ORDR answers a clear question: Is this device doing something it should not? That is a security question, and it demands speed and pattern recognition. We built ORDR for that purpose, and even the most accurate CMDB cannot replace it.
How Virima determines service impact and dependency
- Virima approaches risk from a different direction. When you assess a flagged device or a planned change, ViVID™ gives you a clear dependency context. As a result, you can turn a security alert into a confident operational decision.
- ViVID™ maps assets in the context of the business services they support, both upstream and downstream. Quarantining a device immediately reveals what services will be affected, including ERP modules or inventory management platforms that rely on upstream infrastructure.
- Patching a middleware server highlights which enterprise applications depend on it and the level of risk within the change window.
- When an unmanaged endpoint appears near a core ERP system, ViVID™ visualizes the exposure path in clear business terms — not just technical connections. So, in order fulfillment, you do not just see network links. Instead, you see the real business impact, including downstream effects on customer service platforms and revenue systems.
- Virima answers a key question: What does it mean if something goes wrong here? This is an operations and governance question, not just a security one. So, for inventory tracking, you need accurate data, clear relationships, and a strong service context to answer it well.
- Here is the difference that matters most. ORDR tells you a device is dangerous. In contrast, Virima tells you what will break if you act on that danger.
- Therefore, you need both answers before you make a safe remediation decision. This is especially true in regulated environments, where an unplanned outage can cost as much as the incident itself.
Timing differences reflect decision-making requirements, not platform maturity
Many misunderstand the Virima–ORDR relationship by calling ORDR “real-time” and Virima “slow.” That framing misses the point.
ORDR delivers near real-time visibility and real-time updates because security decisions cannot wait. When a device appears or behavior changes, you need insight within minutes.
Virima, however, supports governance decisions that cannot afford errors. Teams must verify CMDB records used for change management, audits, and impact analysis. Acting on unvalidated data can create long-term operational risk.
If Virima updated records directly from raw network traffic, it would introduce noise and instability. Instead, it reconciles and validates data before updating the CMDB.
Reconciliation is not delayed — it is what makes the data trustworthy.
Think of it this way:
- ORDR operates on a security SLA — speed and detection.
- Virima operates on a governance SLA — accuracy and accountability — which is essential for environments running automated order management and other mission-critical workflows.
Both are correct. Each supports a different kind of decision.
Business context enables meaningful risk prioritisation
Without operational context, every alert feels urgent. An unknown device in a dev VLAN can appear just as critical as one near your ERP system. So teams rely on risk scores alone — but risk without service context is incomplete.
Virima changes prioritization by adding asset criticality, ownership, and lifecycle status to each record, ensuring order processing security findings from ORDR align with real business priorities instead of existing in isolation from your order software governance layer.
When ORDR generates multiple findings, the order management system oms you can immediately see which ones impact compliance-bound or business-critical services.
ViVID™ makes this visible through live service mapping. You see order volume, which assets sit upstream of regulated applications and which exist in low-risk segments.
Ownership clarity removes confusion. Each finding has a named accountable owner.
The result: Faster triage, smarter prioritization, and shorter risk exposure — with decisions that stand up in audits and ultimately boost customer satisfaction.
Integration multiplies value across security and operations
The value of Virima and ORDR together is architectural, not just technical, especially in environments where business-critical platforms such as ERP systems, customer service applications, and financial workflows depend on stable, governed infrastructure.
ORDR detects devices and behavioral risk. Virima provides the system of record, ownership, service context, criticality, and change history. When ORDR surfaces a finding, Virima explains what it means and what could break if you act.
For teams already running ITSM platforms, this context flows directly into existing workflows. Virima integrates with ServiceNow, Jira Service Management, Ivanti, HaloITSM, and Cherwell so when ORDR surfaces a finding, ownership and impact data can be passed directly into the ticketing or change management workflow your team already uses. No manual handoff. No copy-paste between tools.
With an accurate CMDB, alerts arrive with context. Teams spend less time interpreting signals and more time resolving them — which is critical when the global median attacker dwell time was 10 days in 2023, leaving little room for slow ownership and impact analysis.
The integration strengthens both platforms:
- ORDR-discovered devices improve Virima’s service maps
- Virima adds business criticality and ownership to ORDR findings
Risk is no longer measured by network behavior alone, but by real business impact.
The result is faster incident response, clearer change decisions, audit-ready governance, and measurable cost savings through reduced downtime and investigation effort, turning ORDR’s behavioral signals into tracked, owned, and service-mapped move faster operational decisions.
A foundation-first strategy for operationally mature organisations
When evaluating Virima and ORDR, sequence matters as much as selection.
Step 1: Build the operational foundation
Start with Virima:
- Discovery and CMDB tools population
- Clear ownership assignment
- ViVID™ service mapping
This creates a reliable operational layer that strengthens ITSM, change management plan audits, compliance reporting, and incident response, not just security integration.
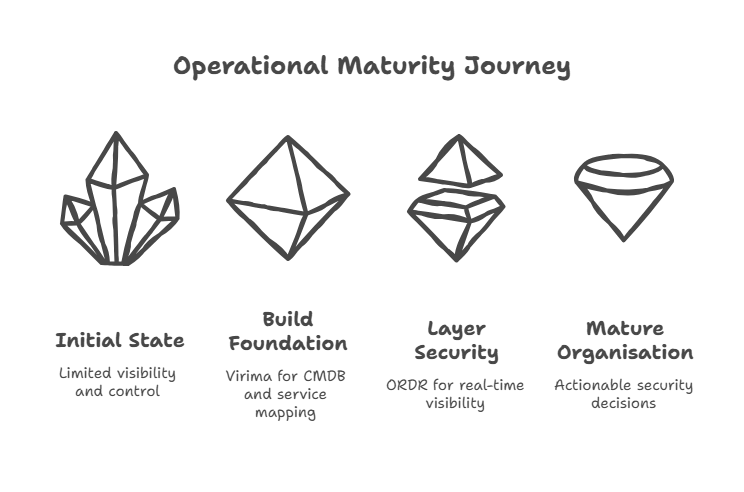
Step 2: Layer in real-time security visibility
Once your CMDB benefits are accurate and trusted, ORDR becomes far more powerful:
- New devices are evaluated against known service dependencies
- Behavioral changes linked to the change history
- Risk prioritization reflects business criticality
Without strong CMDB management, alerts lack context and create noise — limiting the effectiveness of even the most advanced order software or well-funded order management software security initiative.
With a reliable foundation, ORDR delivers faster, clearer, actionable outcomes—helping teams spend less time investigating and more time resolving.
Why Virima anchors security visibility to business reality
ORDR is a powerful security platform. It uses passive network monitoring and behavioral analysis to detect unmanaged devices and unusual activity in real time. Virima does not try to replicate that capability.
Instead, Virima ensures ORDR’s alerts lead to accountable action.
Without operational context, findings can remain unassigned and unresolved. Virima adds ownership, lifecycle status, service dependencies, and governance clarity — turning signals into tracked decisions.
ViVID™ service mapping connects device-level alerts to business impact. Teams can identify customer orders identify affected services before isolating or patching a system.
In simple terms, ORDR shows what is happening on the network. Virima shows what it means for the business.
Together, they close the gap between detection and response. That operational context lives in ViVID™ Virima’s visual dependency mapping team members layer. When a security purchase orders alert points to a device, ViVID™ shows which business services sit upstream and downstream of it, which teams own those services, and what breaks if you isolate or patch the asset. It turns a network signal into a mapped, owned, information include sactionable decision.
Explore how Virima supports security through operational clarity
If security alerts lack actionable confidence for operations, the issue is missing context—not detection. More alerts will not solve the problem. Instead, you need clearer asset data and service insight.
Virima addresses this challenge directly. It uses agentless and agent-based discovery to build accurate CMDB software records. Then, ViVID™ service mapping shows how assets support real business services. order management solutions. Because of this, security signals from platforms like ORDR become actionable, not confusing.
So, whether you are building your operational foundation or strengthening your security stack, start by reviewing your asset records. Ask what your current data stock levels truly support. Then, learn how Virima builds the foundation that turns security visibility into confident action.
Book a free demo to see how it works in your environment.
Frequently asked questions
1. Does Virima replace ORDR?
No. Virima does not replace ORDR. ORDR provides real-time network visibility and behavioral threat detection, purpose-built for continuous network security monitoring.
Virima provides CMDB components and accuracy, automatic mapping, and ownership governance. Together, they strengthen security and operational decision-making.
2. What does Virima do that ORDR does not?
Virima consolidates data into a CMDB (CMDB definition), assigns ownership, maps services via ViVID™, and supports change and audit governance. ORDR(1.6K) does not provide full-service dependency mapping or governance workflows.
3. Is Virima real-time like ORDR?
Virima focuses on verified and reconciled data to ensure long-term accuracy. ORDR provides near real-time behavioral monitoring. They support different decision timelines: security speed versus governance accuracy.
4. Which should be implemented first: Virima or ORDR?
For operational maturity, start with Virima to establish accurate asset records, ownership, and a service mapping tool. Then layer ORDR for real-time security visibility. This approach ensures teams contextualize and act on alerts effectively.






