How to Make the Best Out of Your IT Discovery Tool
IT discovery allows businesses to stay on top of their game by providing them with an overview of the current state of their IT infrastructure, identifying vulnerabilities and gaps in security, and suggesting ways to improve their overall security posture.
IBM’s 2024 Cost of a Data Breach Report found the global average breach cost reached $4.88 million, with security teams citing incomplete asset visibility as a key factor in extended breach detection timelines. Implementing a structured IT discovery process directly reduces this exposure.
Because IT discovery is an important part of your business ecosystem, it is imperative that you derive the best out of your IT discovery tool. Here are a few steps in the right direction:
Outline a discovery process
Successful IT discovery starts by implementing an effective discovery process so that all your IT assets are properly counted. Identify the environments to be discovered (i.e., data centers, edge, cloud, and their IP networks) and devise the best approach to discover each based on the capabilities of the discovery tool(s) selected. Now’s a good time to determine the frequency for scheduled scans, which may affect how the discovery solution is deployed.
Crawl, walk, run implementation
Start small with just a sampling of asset types at first. Expect some failures initially, so starting small won’t make you feel overwhelmed by too many errors. Chances are very good there’s a simple, common fix (i.e., credential error), so fixing it for a few asset types will mean much more immediate success when you expand the discovery. Next target entire IP subnets to see how the system can handle a bigger load. You may find a few more exceptions to address, but soon after, you’ll be ready to go widespread with discovery.
Improve accuracy by normalizing the data
Normalize discovered data to improve accuracy. Achieve asset normalization with database scripts or normalization software tools.
Manage costs and risks with IT asset lifecycle management
Create a streamlined inventory management process that records the lifecycle status of each IT asset. Your IT administrators can use this asset lifecycle information to determine if an asset is in use, stored, checked out, available for use, or retired. By tracking the lifecycle of IT assets, your administrators gain visibility into hardware assets that need to be refreshed or software licenses that need to be renewed, giving them crucial information needed for making future IT purchases.
Categorize your IT assets correctly
It’s essential to categorize your IT assets based on lifecycle stage, usage, roles, and even level of risk. Then place them in one of two categories: Managed and Unmanaged. Managed devices obviously receive the most attention, and unmanaged devices should have the lowest level of trust.
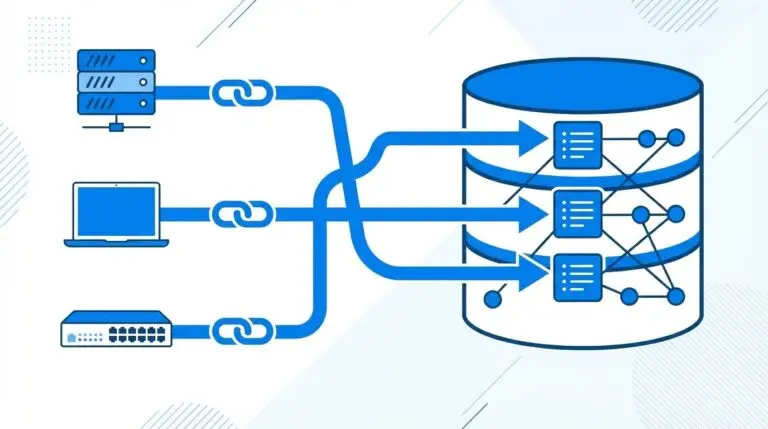
Chart out an asset mapping strategy
The first step in any asset mapping strategy is to gather information about your current IT environment. You should map out your network and storage systems, as well as all of your applications and their dependencies. After this, you should determine how each application is utilized by different departments or teams.
Once you have identified all of these assets, it’s time to look at ways to improve them. This may mean upgrading software licenses or hardware components, or even adding new servers for improved performance.
You should consult with experts in IT discovery before making any major changes because they will be able to offer valuable insights into how best to approach these tasks.
Dos and don’ts of IT discovery tool setup
- The first thing you should do is identify your discovery use cases so you know what general features to look for and questions to ask. Then, create a list of asset types you have to discover and how much information you expect to get about each.
- Chances are, no single method of discovery will meet all your needs, so the discovery solution must be flexible. Be careful to avoid the use of disparate system-specific tools. These will create silos of information and increase the level of effort to maintain.
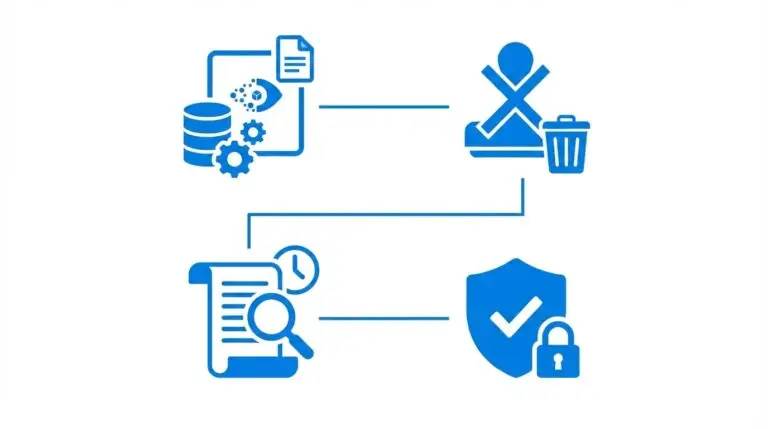
- Automatic and repeatable discovery is imperative. So, focus on tools that offer a lot of automation and require very little manual intervention and processes. Anything that relies on too many manual processes will lead to stale, untrustworthy data. This will ultimately lead to the abandonment of the entire discovery initiative. Once properly configured, scheduled scans and business rule automation will produce results that you can leverage across the organization. IT asset discovery automation is faster, cheaper, and much more accurate than manual approaches.
- Make sure that any tool you choose is easy to access and navigate so that people across the organization can benefit from the data without the need for extensive training in advance.
- Finally, do your best to uncover any organizational limitations upfront (i.e., security/network). Flexibility is key.
Get in touch to explore your IT discovery needs
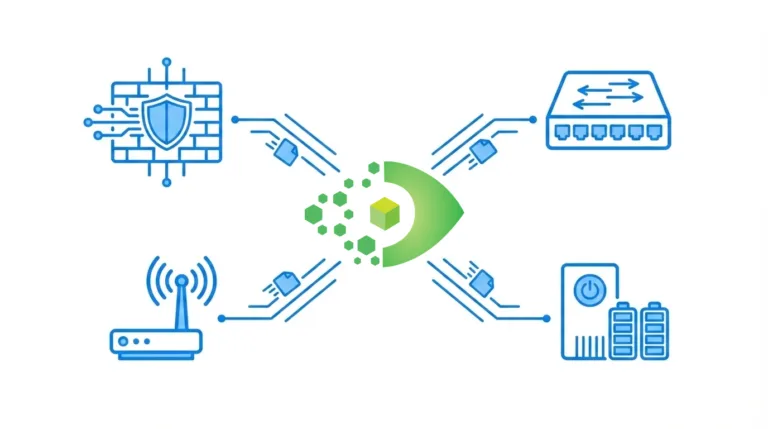
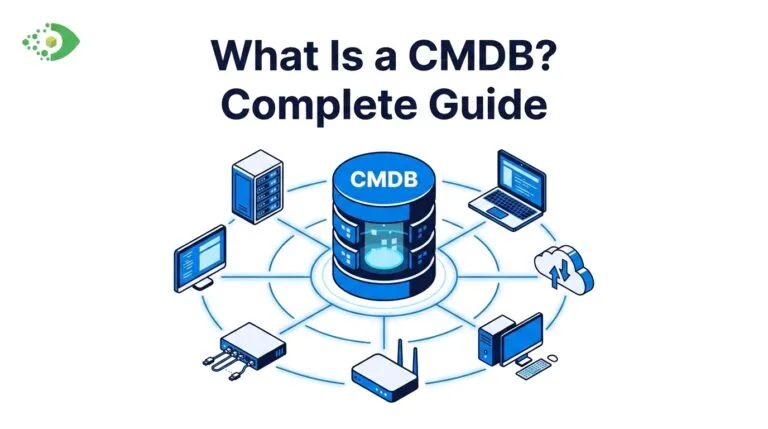
Virima IT discovery offers the broadest discovery techniques, leveraging agentless, agent-based, and API for complete discovery of data center, network, edge, and cloud assets. So whether your goal is to build a robust IT inventory, implement a cost-saving and risk-reducing ITAM program, or finally build the one true source of record in a CMDB to be leveraged across all your ITSM processes, Virima has you covered.
Schedule a Demo at virima.com to learn more about Virima’s robust IT discovery, ITAM, CMDB, and service mapping solutions.