How to Track, Report, and Audit Decommissioned IT Assets in Your CMDB
TLDR
- Ghost assets, devices, and software no longer in service but still in asset records, inflate licensing counts, distort audits, and create security exposure
- “Decommissioned” in a CMDB means the CI is retired from service but retained as a historical record, not deleted
- Business rules automate decommission transitions based on confidence levels, last-seen dates, or discovery absence thresholds
- Decommissioned CIs support audit-ready reporting filtered by asset class, date range, and decommission reason
- Software asset decommissioning carries its own compliance requirements around license key reclaim and SAM reconciliation
Introduction
Every IT environment has them: servers powered off months ago that still appear in asset reports. Laptops returned during offboarding that never got updated in the CMDB. Software products whose license keys remain allocated to devices that no longer exist. These are ghost assets, and they impose real costs on enterprise IT operations.
A 2025 survey by WanAware found that ghost assets drain up to 25% of IT budgets, a figure capturing direct costs (unnecessary software renewals, maintenance contracts for retired hardware) and indirect costs (audit findings, compliance failures, and incident response time wasted on phantom CIs). ITAM Coaches – Ghost Assets Are Costing You 25% of Your IT Budget
The root cause is almost always the same: the decommission process is inconsistent or informal. IT teams physically retire devices but do not update the CMDB. Software gets uninstalled, but license allocations persist. The CMDB grows stale, and each stale record becomes a liability at the next audit.
Structured decommission tracking, built into the CMDB lifecycle with automated transitions, dedicated reporting, and a clear policy for when to decommission versus delete, converts a perennial operational weakness into a defensible, documented process.
The Ghost Asset Problem: What It Costs You
Software Licensing Exposure
When the CMDB shows software allocated to a device that no longer exists, software asset management (SAM) tools count that allocation as active entitlement consumption. License renewal decisions, compliance self-assessments, and true-up calculations all work off that inflated number. Organizations routinely pay for hundreds of licenses they do not need because their CMDB still shows an inflated installed base. A mature IT asset management practice catches these discrepancies before they compound. Teqtivity – Ghost Assets: The Hidden Costs of Untracked IT Equipment
Audit Gaps and Compliance Findings
IT audits under ISO 27001, SOC 2, CMMC, and internal security review frameworks routinely scrutinize the CMDB for accuracy. Auditors look for evidence that the CMDB reflects actual operational reality. Finding records for decommissioned devices with no documented decommission date, no retirement reason, and no chain of custody creates findings that require remediation.
Security Exposure
CMDB records for decommissioned devices sometimes remain linked to active service accounts, network access rules, or vulnerability scan targets. Security teams waste remediation time chasing vulnerabilities on devices that no longer exist, or fail to notice when a device is quietly reactivated and reuses credentials tied to a “decommissioned” record. Cybersecurity asset management practices mitigate this by maintaining a validated, current asset inventory.
Decommissioned vs. Deleted: Why the Distinction Matters
This is one of the most important distinctions in CMDB lifecycle management, and one of the most frequently misunderstood.
Deleting a CI removes the record from the CMDB entirely. As far as future queries are concerned, the CI never existed. There is no audit trail, no decommission date, and no record of what the device was or when it went out of service.
Decommissioning a CI changes its operational status to “retired” or “decommissioned” while preserving the full record. The CI remains visible in the CMDB with its complete history: discovery data, relationships to other CIs, service associations, ownership records, and the date and reason it was decommissioned.
The audit value of a decommissioned record is substantial. When an auditor asks, “What servers were decommissioned in Q4 2025 and what software was installed on them?” a delete-based approach returns nothing. A decommission-based approach returns a complete, timestamped report.
For compliance frameworks that require evidence of proper asset disposal (data destruction, hardware disposition), the decommissioned CI record provides the anchor for that evidence chain. Deleted records leave no anchor.
The practical guideline: Decommission CIs when real assets retire from service. Delete CI records only for entries created in error (duplicates, test entries, import mistakes) where the CI never represented a real asset.
For the foundational behavior behind these transitions — what specifically happens to each CI when its underlying asset retires, which relationships persist, which fields are preserved, and what stays in the historical record — read our CMDB asset lifecycle best practices guide.
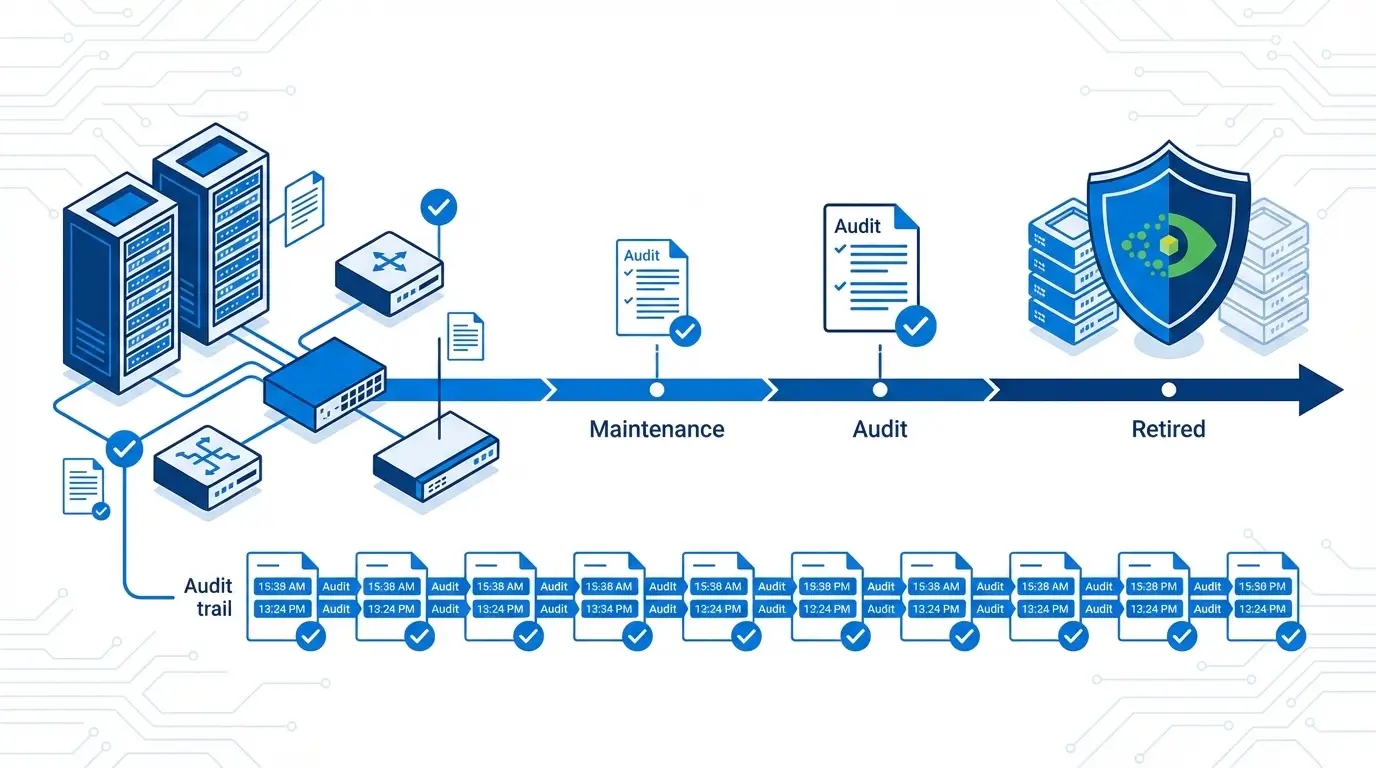
The CI Lifecycle: From Discovery to Decommissioning
A well-governed CMDB CI follows a lifecycle with defined stage transitions:
- Discovered: CI detected by discovery scan; record created automatically
- Active: CI confirmed operational, in service, and under management
- Maintenance: CI temporarily out of service but expected to return (planned downtime, repair)
- Decommissioned: CI permanently retired from service; record retained for history and audit
- Deleted: Record removed (reserved for error-created CIs only)
Stage transitions are the governance control points. “Active to Decommissioned” is the transition that most organizations leave informal, relying on someone to manually update the CMDB record after a device goes offline. That informality is why ghost assets proliferate.
Automating the “Active to Decommissioned” transition, based on objective criteria rather than manual action, removes the dependency on someone remembering to update a record.
Automating Decommission with Business Rules
Business rules in a CMDB apply condition-based logic to CI lifecycle transitions. For decommissioning, the relevant conditions include:
Last-Seen Date Threshold
If a CI has not appeared in any discovery scan for a configurable number of consecutive days, the business rule flags it as a decommission candidate. Thresholds vary by CI class and organizational policy: servers typically use 30 days, endpoints 60 days, and network devices 14 days. The last-seen date is a discovery-native signal that requires no manual input.
Confidence Level Decline
Discovery tools assign confidence scores to CI records based on how recently and completely the device was discovered through service mapping and dependency tracking. A CI whose confidence level drops below a defined threshold because discovery is no longer finding it is a strong decommission signal. Confidence-based rules catch devices that disappear gradually (powered down in stages, moved to isolated segments) rather than abruptly.
Human Approval Step
Automated rules surface decommission candidates; a human confirms the transition with a documented reason. The combination of automation (to catch what manual processes miss) and human approval (to prevent false positives from marking active CIs as decommissioned due to temporary discovery gaps) creates a balanced and auditable workflow.
Integration with Offboarding Workflows
Devices returned during employee offboarding can trigger CMDB decommission workflows through integration with HR systems or ITSM platforms, linking the HR lifecycle event to the asset lifecycle change automatically and eliminating a common gap in the decommission process.
Decommissioned Asset Reporting: Generating Audit-Ready Output
A decommissioned assets report serves multiple purposes: operational cleanup tracking, audit evidence, license reconciliation, and disposal documentation.
Effective decommissioning reporting includes:
- Date range filter: Show all CIs decommissioned between two dates (e.g., all Q1 2026 retirements for quarterly review)
- CI class filter: Isolate servers, endpoints, network devices, or software separately for focused review
- Decommission reason: Document why each CI was retired (end of life, hardware failure, lease return, consolidation project)
- Associated software assets: For each decommissioned hardware CI, list the software that was installed and identify the license keys available for reclaim
- Linked relationships: Show what services, applications, or other CIs the decommissioned device was connected to, for service map cleanup
Virima 6.1.1 introduced a dedicated Decommissioned Assets view and report capability, allowing IT teams to filter decommissioned CIs by date range, CI class, and decommission status, and export results in an audit-ready format. This removes the manual aggregation work previously required to compile decommission evidence for audits or executive reviews.
Software Asset Decommissioning: The Licensing Compliance Angle
Hardware decommissioning and software asset decommissioning are related but distinct processes. When a server is decommissioned, the software running on it should trigger a separate SAM reconciliation workflow:
- Identify all software installed on the decommissioning CI: Pull the software installation records linked to the retiring device
- Reclaim license keys: Return license keys to the available pool in the SAM tool rather than leaving them allocated to a retired device
- Update maintenance contracts: Flag maintenance renewals for software on decommissioned devices for review before auto-renewal
- Retain license key records: Even after software decommissioning, retain the historical record of what license key was allocated to which device and when it was released, for audit purposes
Organizations that decommission the hardware CI without addressing the associated software records find their license positions overstated at audit time, or discover they have been auto-renewing maintenance contracts for software on hardware that no longer exists.
How Virima Supports Decommission Tracking and Compliance
Virima’s CMDB and ITAM platform supports structured decommission workflows through discovery-driven automation and dedicated reporting:
- Confidence-based decommission candidates: CIs that drop below a configurable confidence threshold appear in a decommission review queue for administrator action
- Last-seen date tracking: Every CI record tracks when it was last observed in a discovery scan, providing an objective, non-manual decommission signal
- Dedicated Decommissioned Assets view: Introduced in Virima 6.1.1, this view surfaces all decommissioned CIs with decommission date, reason, and associated asset data for audit and reporting
- Software asset integration: Software installations link to parent hardware CIs, so hardware decommissioning surfaces associated software records for SAM reconciliation
For a broader view of how CMDB governance supports IT compliance, read ServiceNow CMDB Governance Best Practices.
Conclusion
Decommissioned asset tracking is a compliance necessity, not an administrative convenience. Ghost assets inflate licensing costs, expose audit gaps, and create security risks that accumulate silently until the next audit surfaces them.
The structured approach, defining the decommission lifecycle, automating transitions through business rules, retaining records as decommissioned rather than deleting them, and generating audit-ready reports on demand, converts this perennial operational weakness into a defensible and documented process.
Ready to see how Virima manages the IT asset lifecycle from discovery to decommission? Schedule a Demo at virima.com
Sources: Teqtivity – Ghost Assets: The Hidden Costs of Untracked IT Equipment | GB Advisors – Ensuring Data Reliability: Proven Techniques to Cleanse and Govern Your CMDB | ZenAdmin – IT Asset Retrieval and Decommissioning Best Practices