What Is an IT Risk Register and How Does Virima Connect Risk to Change Management and Projects?
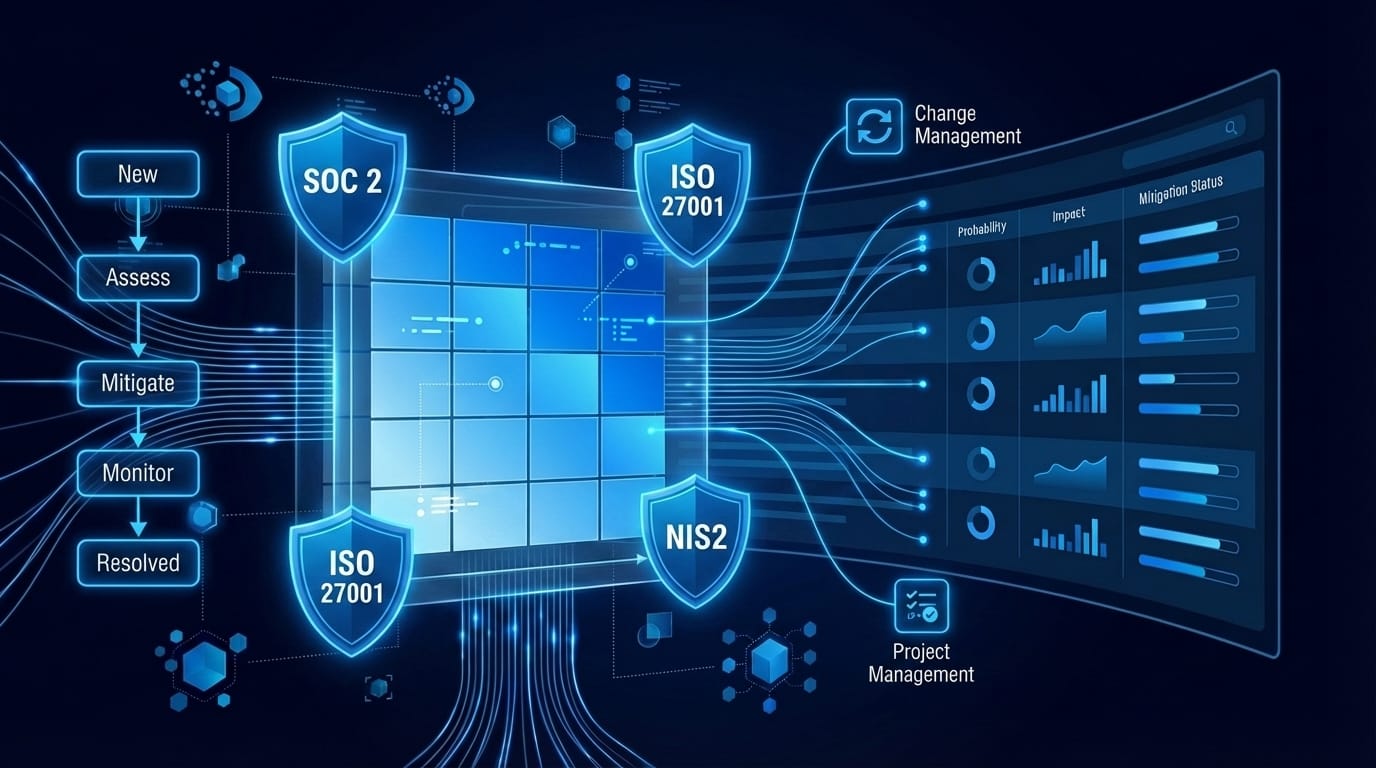
Virima’s IT risk register provides a centralized, structured record of all technology risks — serving as a risk register for IT project environments — integrated with change management and project management to support GRC compliance across SOC 2, ISO 27001, NIS2, and GDPR.
1. What is an IT risk register?
An IT risk register is a centralized, structured repository that documents every identified technology risk, ensuring all critical details are included in a risk register rather than scattered across informal sources, facing an organization, along with key information about each risk’s probability, potential impact, planned response, ownership, and current status. Rather than keeping risk awareness informal — in spreadsheets, meeting notes, or individual memory — a risk register creates an official, maintained record that produces auditable evidence of structured risk management.
A well-maintained risk register answers six questions for every documented risk, helping teams prioritize risk based on likelihood and impact: what is the risk, how likely is it to occur, how severe are the consequences if it does, what is the plan to respond, who owns the response, and what is the current state. These answers, maintained consistently, transform informal awareness into a structured process that supports informed decisions at both operational and executive levels, that satisfies audit requirements, and supports executive decision-making.
2. What information does a risk register record for each risk?
Virima’s Risk Register module supports teams in creating a risk register by recording the following fields for each risk:
- Name — a concise identifier for the risk
- Date — when the risk was identified
- Description — a clear narrative of the risk, its conditions, and potential consequences
- Risk Type — Customer, External, Management, Organizational, or Technical
- Probability — Very Low, Low, Medium, High, Very High, Issue, or Blocker
- Impact Level — Very Low through Very High
- Mitigation Strategy — Avoid, Mitigate, Accept, or Transfer
- Owner — the individual responsible for the response, clearly defining risks owners for accountability and follow-through
- Status — New, Planning, Action, Pending, Resolved, Deferred, or Deleted
- Trigger — the condition or event that would activate the risk
- Trend — Static, Decreasing, or Increasing (updated at each review)
- Source — where the risk was identified (audit, security assessment, project planning, incident review, etc.)
Virima’s Admin-configurable Risk Calculator applies consistent risk scoring by evaluating probability and impact, enabling standardized prioritization across all entries, based on its probability and impact values, producing a numeric composite score that enables consistent prioritization across all risks in the register.
3. How does Virima connect risk records to change management?
Virima 6.1.1 allows risk records to be associated directly with Change records within the same ITSM platform. When a change advisory board reviews a proposed change, the relevant pre-identified risks are visible in the change record — not stored separately in a risk tool that may not be consulted during the approval process.
The risk-to-change linkage creates two operational benefits. First, risk information is part of the change approval workflow, so reviewers see it without having to look elsewhere. Second, when a change is completed, the associated risk records can be updated to reflect whether risks occur, were mitigated by the change, or require continued monitoring. to reflect whether the risk materialized, was mitigated by the change, or requires continued monitoring.
This tight coupling between CMDB-driven change management and risk tracking is what separates structured programs from reactive ones. The entire risk history for a given change is accessible in one place.
4. Can Virima’s risk register link to project management records?
Yes. In Virima 6.1.1, risk records can be associated with Project records in addition to Change records. Technology projects — infrastructure migrations, new system deployments, application upgrades — carry inherent risks that should remain visible throughout the project lifecycle.
Associating risk records with a project in Virima keeps those risks visible during project milestone reviews, ensures they are reassessed as the project progresses, and creates a complete post-project risk history. This integration supports the risk-in-project-management requirements of ISO 27001 Annex A 5.8, which requires information security to be integrated into project management methodology.
5. How does Virima support GRC compliance with the risk register?
Virima’s Risk Register supports governance, risk, and compliance (GRC) requirements across multiple regulatory frameworks:
SOC 2
The AICPA Trust Services Criteria require documented risk assessment and response. Virima’s risk register — with probability assessments, mitigation strategies, owner assignment, and lifecycle history — provides the evidence base for SOC 2 CC3 (Risk Assessment) controls.
ISO 27001
ISO/IEC 27001:2022 Clauses 6.1.2 and 6.1.3 require a formal risk assessment process and documented risk treatment plan. Virima’s risk register fields map directly to these requirements.
NIS2 Directive
NIS2 requires organizations to implement and document cybersecurity risk management measures. Virima provides the structured documentation and audit trail NIS2 compliance reviews require.
GDPR
Data protection risks — including those addressed in Data Protection Impact Assessments — can be managed within Virima’s risk register framework, categorized by risk type and linked to relevant change and project records. Organizations looking to strengthen this posture further can explore how ITAM supports risk management as a complementary discipline.
In each case, the audit evidence is retrievable from Virima: timestamped records, owner accountability, documented response strategies, and complete lifecycle history from identification through resolution.
6. What are the risk lifecycle statuses in Virima?
Virima 6.1.1 tracks each risk through the following status stages:
- New — identified and entered, not yet assessed or assigned
- Planning — assessed, strategy selected, response plan in development
- Action — response plan actively being executed
- Pending — response waiting on a third party or external dependency
- Resolved — mitigation fully executed; risk eliminated or reduced to an acceptable level
- Deferred — response deliberately postponed; risk remains in the register for future review
- Deleted — entered in error or no longer applicable; record retained for history
Each status transition is timestamped and associated with the owner, creating a complete lifecycle history for every risk record. This history is the audit trail that regulators require to verify that identified risks received structured attention.
7. Can the risk register in Virima generate audit reports?
Virima’s risk register supports GRC audit documentation by maintaining complete, timestamped records for every risk entry. Each record contains the full history of status changes, owner assignments, probability and impact assessments, mitigation strategy documentation, and trend assessments over time.
For IT audit purposes, IT teams can access risk records by type, status, owner, or associated change and project records. The complete lifecycle history — from New through Resolved or Deferred — provides auditors with the evidence chain required to verify that risk management is a structured, ongoing process rather than a point-in-time activity.
Organizations undergoing SOC 2, ISO 27001, or NIS2 audits can use Virima’s risk register records as primary evidence for risk assessment controls, supplemented by the associated change and project records that demonstrate risk management is integrated into operational workflows.
Ready to build your IT risk register in Virima? Schedule a Demo at virima.com.