What is the best Active Directory monitoring tool for security?
Active Directory controls identity, authentication, and access. Therefore, when it changes unexpectedly, risk increases immediately. In today’s hybrid environments, that risk expands even faster. As a result, selecting the right Active Directory monitoring tool becomes essential for both security and compliance.
However, many organizations still rely on manual log reviews and isolated scripts. Consequently, suspicious changes go unnoticed. Meanwhile, replication failures create login issues. In addition, dormant accounts often remain active longer than intended.
Therefore, effective Active Directory Monitoring and Management must combine detection, auditing, and health visibility. In other words, monitoring alone is not enough. Instead, structured governance is required.
TL;DR
- Active Directory monitoring detects suspicious activity and risky changes in real time.
- AD auditing preserves defensible history for compliance and investigations.
- AD health monitoring ensures replication, DNS, and Domain Controllers remain stable.
- Hybrid environments require unified monitoring across on-prem AD and Entra ID.
- Integration with CMDB, SIEM, and ITSM improves prioritization and response.
Who this guide is for
This guide is designed for:
- IT Operations Managers in regulated industries
- Infrastructure Leads managing hybrid AD environments
- Teams preparing for SOX, HIPAA, or PCI audits
- Organizations evaluating an Active Directory management tool
If AD security, uptime, or compliance creates pressure, this guide is relevant.
What is the difference between AD monitoring, AD auditing, and AD health monitoring?
Before evaluating tools, definitions must be precise. Otherwise, concept drift occurs. Consequently, teams misalign expectations.
| Category | Purpose | Focus | Example Question | Primary Outcome |
| AD Monitoring | Real-time detection | Changes and activity | Who added a Domain Admin at 2am? | Immediate alert and response |
| AD Auditing | Historical record | Compliance evidence | When was this group membership changed? | Defensible audit trail |
| AD Health Monitoring | Infrastructure stability | Replication and DC health | Is replication failing between sites? | Prevent outages |
AD monitoring (real-time detection)
Active directory monitoring focuses on live visibility.
It answers:
- Who changed a group membership?
- Why was an account enabled at midnight?
- Where are failed logins coming from?
It provides alerts and immediate awareness.
AD auditing (historical proof)
AD auditing focuses on recorded history.
It answers:
- When was this privileged role assigned?
- How long did that account remain active?
- Who approved the change?
Auditing supports compliance and investigations. It preserves defensible evidence.
AD health monitoring (infrastructure stability)
AD health monitoring focuses on system reliability.
It answers:
- Are Domain Controllers online?
- Is replication functioning?
- Are DNS and SYSVOL operating correctly?
Health monitoring prevents outages before users notice login failures.
Therefore, an effective active directory monitoring tool should address all three areas.
What events should you monitor in Active Directory?
Effective Active Directory monitoring starts with clarity. Without a defined scope, alert noise increases quickly. Consequently, teams experience fatigue rather than insight.
Authentication events
Monitor:
- Failed logons
- Account lockouts
- Unusual login locations
- Repeated password resets
These signals often indicate credential misuse. Therefore, they should trigger structured review.
Change events
Monitor:
- Domain Admin group changes
- GPO modifications
- Account enable or disable events
- Password resets
- Delegated permission updates
For example, if a Domain Admin is added at midnight, that change should trigger immediate escalation. Otherwise, exposure increases silently.
Directory health signals
Monitor:
- Replication failures
- Domain Controller downtime
- DNS errors
- DFS-R or SYSVOL issues
Replication failures, in particular, often precede widespread login disruption. Therefore, early detection prevents outages.
Privileged identity controls
Monitor:
- Service accounts
- Break-glass accounts
- Delegated admin roles
- High-privilege groups
Dormant privileged accounts represent hidden risk. Consequently, regular review becomes essential.
Minimum baseline configuration
At a minimum:
- Enable advanced auditing policies
- Centralize logs
- Define alert severity tiers
- Assign response ownership
Without this foundation, monitoring remains reactive.
How do you monitor Active Directory effectively?
Effective monitoring requires structure. Tools help. However, process determines success.
Use this four-stage model:
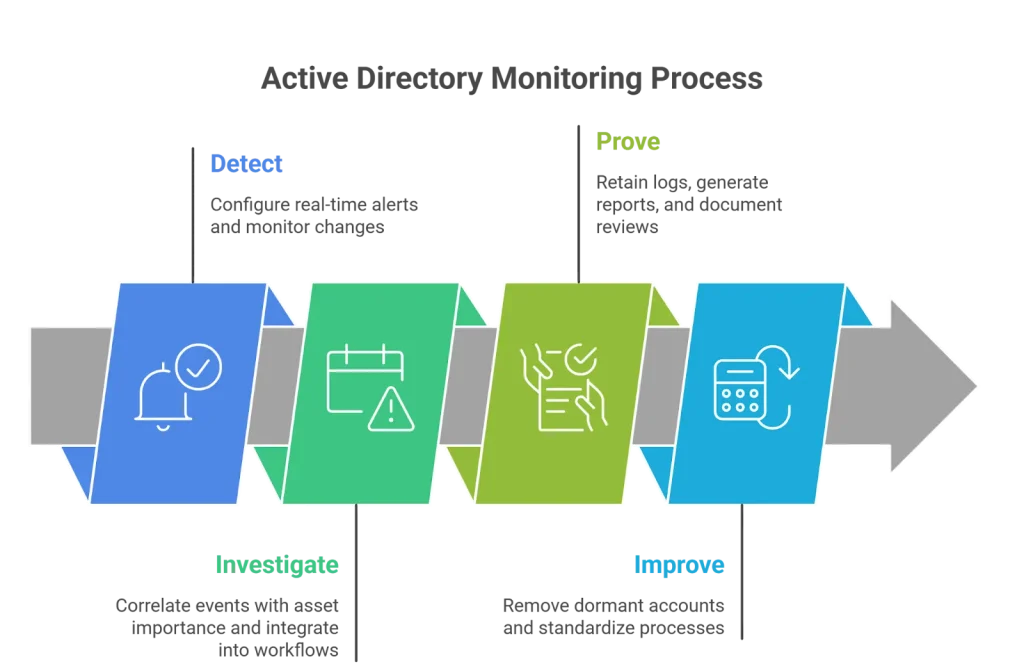
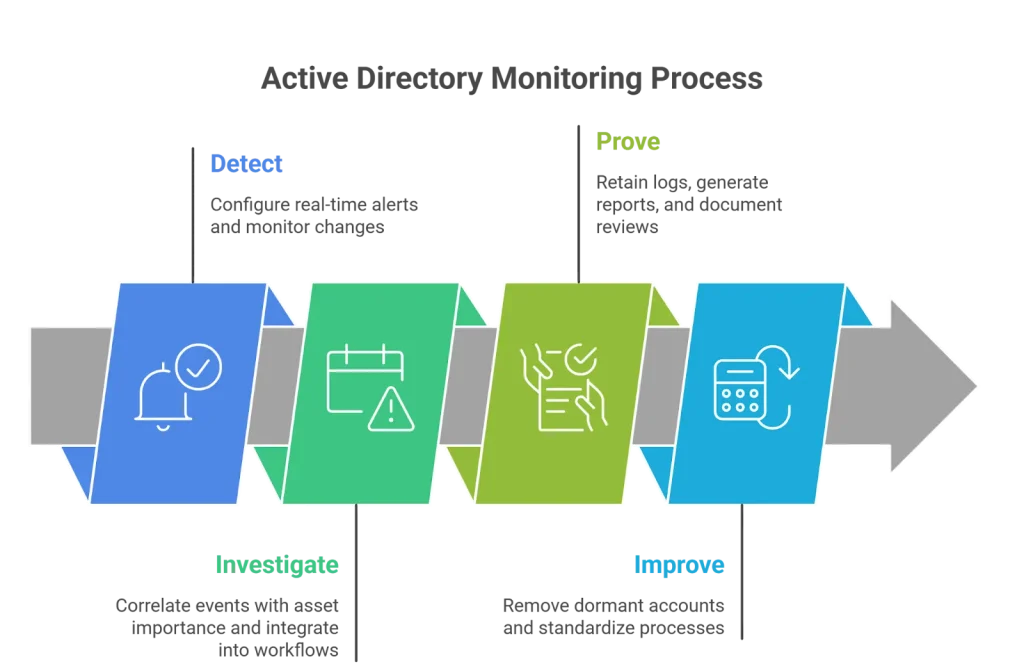
1. Detect
First, configure real-time alerts. Then, monitor privileged changes. In addition, track replication health.
Keep alerts focused. Otherwise, noise overwhelms the signal.
2. Investigate
Next, correlate AD events with asset importance. For example, a change on a Tier-0 server carries more risk than the same change elsewhere.
Meanwhile, integrate alerts into ITSM workflows. As a result, the response becomes structured rather than ad hoc.
3. Prove
Then, retain logs according to compliance rules. In addition, generate structured change history reports. Moreover, document privileged access reviews.
Auditors expect consistent evidence. Therefore, reporting automation matters.
4. Improve
Finally, reduce long-term exposure. Remove dormant accounts. Standardize role assignments. Automate onboarding workflows.
Monitoring without improvement only creates recurring alerts.
Quick wins
Quick wins create immediate improvement without a large investment. In many cases, small operational adjustments reduce significant risk.
Alert immediately on Domain Admin changes
Domain Admin changes represent one of the highest-risk events in Active Directory. Therefore, alerts for these changes should be real-time.
Specifically, configure alerts for:
- New members added to Domain Admins
- Removal of existing members
- Changes to Enterprise Admin roles
In addition, assign clear ownership for these alerts. As a result, the team structures escalation rather than handling it informally.
Review disabled accounts monthly
Disabled accounts often accumulate quietly. However, they may still retain group memberships or legacy permissions.
Therefore, conduct a monthly review to:
- Confirm accounts are no longer needed
- Remove unnecessary group access
- Validate deprovisioning workflows
Over time, this reduces dormant access risk significantly.
Monitor replication daily
Replication health directly impacts authentication reliability. However, replication issues often go unnoticed until users complain.
Therefore, monitor:
- Replication latency
- Failed replication attempts
- Domain Controller synchronization status
Daily checks prevent broader outages. Consequently, service stability improves.
Audit privileged group membership quarterly
Privileged groups require periodic review. Otherwise, access creep develops.
Each quarter:
- Export group membership lists
- Validate business justification
- Remove unnecessary elevated access
This simple cadence strengthens compliance posture and reduces insider risk.
Small improvements, when applied consistently, reduce major exposure over time. In other words, discipline matters more than complexity.
Common pitfalls
Even strong monitoring programs fail when basic issues remain unresolved. Therefore, avoiding common mistakes is just as important as implementing tools.
Excessive alert volume
Too many alerts create fatigue. As a result, critical signals may be ignored.
To reduce noise:
- Filter low-risk events
- Tier alerts by severity
- Assign response SLAs
Focused alerting improves response speed and confidence.
Monitoring on-prem AD but ignoring Entra ID
Many organizations monitor traditional AD closely. However, they overlook Entra ID roles and cloud authentication.
This creates a blind spot. Consequently, privileged role changes in the cloud may go undetected.
Therefore, hybrid monitoring must include:
- Entra ID role assignments
- Conditional access changes
- Cloud-only account activity
Unified visibility reduces risk across environments.
Short log retention
Compliance mandates often require extended log retention. However, some environments store logs for only a short period.
As a result, historical investigations make user logins difficult. Audit defensibility weakens.
Therefore, define clear retention policies aligned with regulatory requirements.
Manual review without automation
Manual log review consumes time. Moreover, it introduces human error.
Without automation:
- Alerts may be missed
- Reports may be incomplete
- Reviews may be inconsistent
Automation, when configured properly, improves consistency and frees up operational bandwidth.
These pitfalls weaken monitoring effectiveness gradually. However, when addressed early, monitoring maturity increases steadily.
Active Directory monitoring tool selection checklist
When evaluating an active directory management tool, assess:
- Alert fidelity (low false positives)
- Hybrid coverage (on-prem + Entra ID)
- Reporting depth
- Log retention flexibility
- Integration with SIEM, ITSM, and CMDB
- Role-based access control
- Ease of deployment
- Scalability
Decision-stage buyers should validate alert quality before finalizing selection.
Implementation steps
To deploy effective Active Directory monitoring:
- Define monitoring scope and compliance requirements.
- Enable advanced auditing.
- Centralize logs.
- Configure alert tiers.
- Integrate with ITSM or SIEM.
- Test alert response workflows.
- Document retention policies.
Structured rollout prevents alert overload.
Audit evidence pack
Auditors typically request:
- Group membership change history
- Privileged access review documentation
- Account lifecycle evidence
- Log retention policies
- Replication health reports
A mature active directory monitoring tool should generate these reports without manual effort.
Red flags
- No monitoring of Entra ID privileged roles
- No alerting for Domain Admin changes
- No documented retention policy
- Replication failures discovered by user complaints
These signals elevated operational risk.
Several active directory monitoring tools exist. However, not all tools solve the same problem. Therefore, selection should depend on integration depth, hybrid coverage, and compliance requirements.
In addition, consider whether you need monitoring only, or full Active Directory Monitoring and Management. Tools vary widely in that regard.
Below is a focused comparison aligned to mid-market, regulated environments.
1. Virima
Best for: Unified Active Directory Monitoring and Management integrated with IT asset visibility and governance workflows.
Virima goes beyond basic alerting. Instead, it connects AD events to a broader IT context.
Strengths:
- Near real-time AD change monitoring
- CMDB integration for asset criticality context
- Unified visibility across on-prem AD and Entra ID, including role assignments, conditional access changes, and cloud-only account activity, mapped to the same CMDB asset records
- Compliance-ready audit reporting
- ITSM workflow integration with ServiceNow, Jira Service Management, Ivanti, and others, alerts can generate tickets automatically with asset context and assigned ownership
- ViVID™ visual dependency mapping connects AD changes to downstream service impact, so a privileged change on a Tier-0 server surfaces which services and assets are affected, not just that the change occurred
For example, a privileged change on a Tier-0 server can be prioritized higher than the same change on a non-critical asset. As a result, the response becomes risk-based rather than generic.
Ideal when: AD visibility must align with broader IT governance, compliance reporting, and asset intelligence.
2. ManageEngine ADAudit Plus
Best for: Organizations focused primarily on AD change auditing and compliance reporting.
ManageEngine ADAudit Plus offers strong reporting capabilities. In particular, it provides detailed visibility into user and group changes.
Strengths:
- Pre-built compliance reports
- Detailed change tracking
- User activity monitoring
- Alerting for key events
However, integration depth may require additional configuration. Therefore, evaluate microsoft active directory how it connects to your existing ITSM and CMDB tools.
Ideal when: The primary goal is audit reporting and change visibility without broader IT context integration.
3. Netwrix Auditor
Best for: Compliance-heavy environments requiring strong historical logging.
Netwrix Auditor focuses deeply on audit trails and documentation. As a result, it is often selected in regulated industries.
Strengths:
- Comprehensive change history
- Strong compliance documentation support
- Alerting for sensitive events
- Privileged activity reporting
However, it may emphasize auditing more than operational workflow integration. As a result, regulated industries often select it.
Ideal when: Historical audit defensibility is the dominant priority.
4. SolarWinds Access Rights Manager
Best for: Organizations focused on permissions analysis and access visibility.
SolarWinds Access Rights Manager specializes in analyzing user permissions and group memberships.
Strengths:
- Clear visibility into effective permissions
- Access review support
- Role and group analysis
- Delegation insight
However, it may require additional tools for full hybrid monitoring or workflow automation. Therefore, consider how it fits within your broader monitoring ecosystem.
Ideal when: Access review and permission transparency are primary concerns.
How to compare these tools effectively
Instead of focusing only on feature lists, ask structured evaluation questions:
- Does the tool support hybrid AD environments?
- Can it correlate AD events with asset criticality?
- Does it generate compliance-ready reports automatically?
- Can alerts integrate into ITSM workflows?
- Is the alert noise manageable?
Because each environment differs, the “best” active directory monitoring tool depends on operational maturity and integration needs.
Ultimately, tools that combine monitoring, auditing, and contextual Azure AD integration tend to reduce long-term risk more effectively.
Are there any software solutions that integrate an active directory monitoring tool with other IT management tools?
Yes. However, not all integrations are equal. Some tools simply forward alerts. In contrast, others create a real operational context.
Modern platforms should integrate AD monitoring with:
- CMDB systems
- ITSM platforms
- Asset discovery tools
- SIEM solutions
However, the real value appears when integration drives prioritization and workflow automation.
Why CMDB integration matters for active directory monitoring tool
Active Directory changes do not carry equal risk. For example, a privileged change on a Tier-0 Domain Controller is far more critical than the same change on a test system.
Without CMDB context, alerts look identical. As a result, teams must investigate manually.
Virima integrates AD monitoring directly with CMDB and asset intelligence. Every AD event inherits service context, asset criticality, and dependency mapping through ViVID™, Virima’s Visual Impact Display, so teams can see not just what changed, but what that change puts at risk.
Alerts become risk-weighted rather than generic, and the blast radius user creation of a privileged change becomes visible before an incident ticket is ever opened.
Why ITSM integration matters active directory monitoring tool
Detection alone does not resolve incidents. Instead, events must trigger structured response.
Virima integrates with ITSM platforms to:
- Automatically generate tickets from high-severity AD alerts
- Assign ownership based on predefined rules
- Track remediation workflows
- Preserve response history for audit windows server purposes
As a result, monitoring connects directly to action.
For example, if a Domain Admin group membership user account changes unexpectedly, the system can:
- Generate an alert
- Create an ITSM ticket
- Assign the correct owner
- Track investigation steps
- Archive closure evidence
Therefore, detection flows seamlessly into investigation and documentation.
Integration beyond basic alert forwarding
Some tools simply export logs to a SIEM. While that provides visibility, it does not automatically add asset or workflow context.
In contrast, Virima’s integrations align:
- Active directory monitoring
- CMDB-based asset classification
- ITSM remediation workflows
- Compliance organizational units reporting
Because these layers connect, AD monitoring becomes part of broader IT governance.
From alerts to operational intelligence in an active directory monitoring tool
Integration transforms isolated events into structured insight.
Instead of asking, “What changed?” teams can ask:
- What changed?
- On which critical asset?
- Who owns remediation?
- Was it resolved within SLA?
As a result, AD monitoring supports uptime, compliance, and accountability simultaneously.
Ultimately, integration depth determines access to sensitive data and long-term value. Tools that connect monitoring to CMDB and ITSM workflows reduce risk faster and with less manual effort.
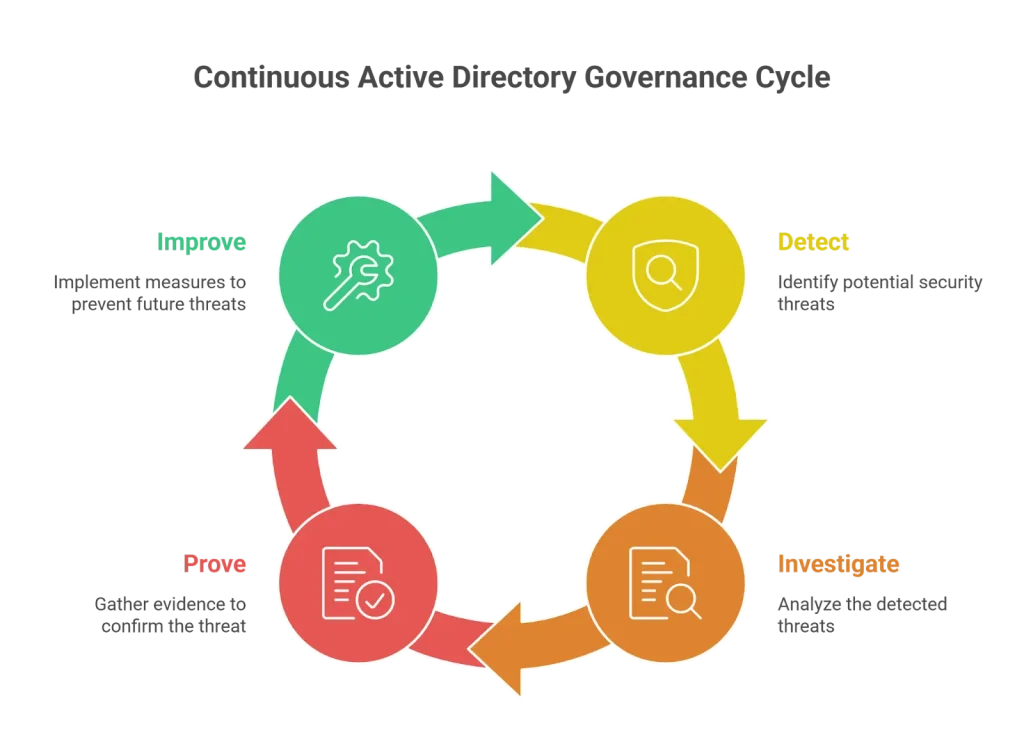
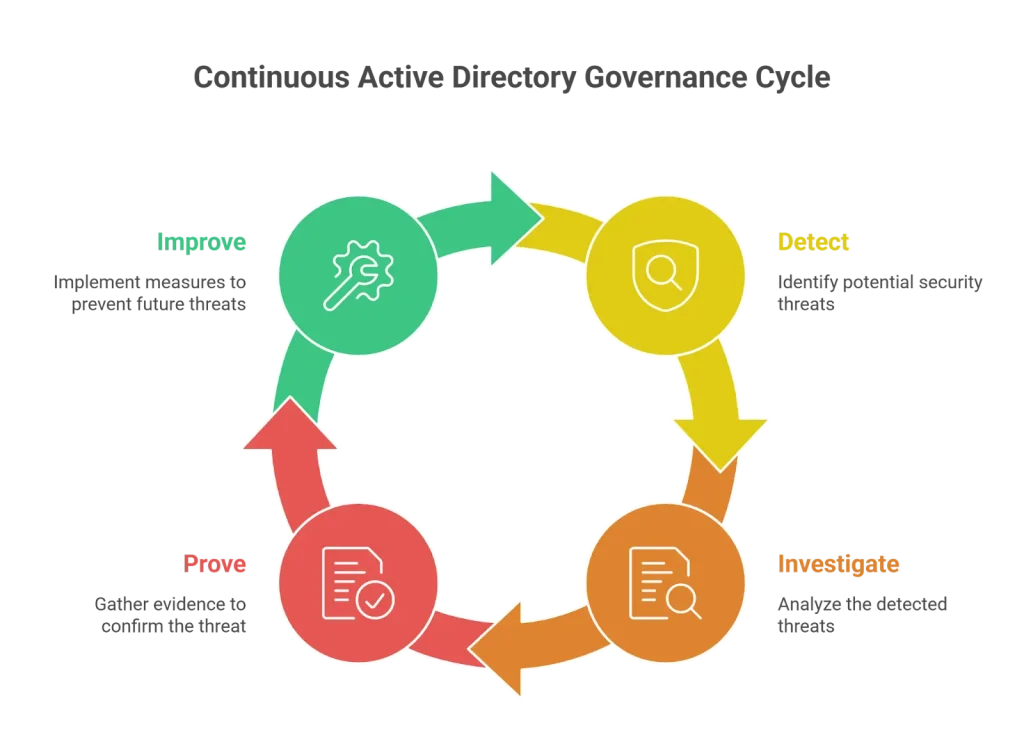
Continuous Active Directory governance
Forward-looking organizations do not treat AD as static. Instead, they maintain continuous oversight.
They:
- Tier alerts by severity
- Assign active directory service owners
- Define response SLAs
- Review privileged access regularly
- Correlate AD events with asset impact
Over time, Detect → Investigate → Prove → Improve becomes a steady governance cycle.
Strengthening Active Directory monitoring and management
Active Directory remains central to enterprise security and uptime. However, fragmented monitoring leaves visibility gaps.
If unauthorized changes, login disruptions, or compliance reporting create pressure, it may be time to reassess.
Organizations must detect changes in real time. At the same time, they must preserve audit history. In addition, they must protect directory health. When these elements operate together, risk decreases significantly.
Moreover, hybrid environments add complexity. On-prem AD and Entra ID must be monitored together. Otherwise, blind spots appear. Consequently, integration becomes essential.
Virima aligns:
- Active directory monitoring
- Asset criticality context
- IT service workflows
- Compliance-ready reporting
- Hybrid AD visibility
As a result, organizations move from reactive log review to structured governance.
Instead of reacting to logs, teams gain clear prioritization. Instead of scrambling before audits, evidence remains organized. Instead of manual correlation, context is built in.
If you are evaluating an Active Directory monitoring tool, a structured talk can help. It should cover integration depth, hybrid coverage, and workflow automation. This can clarify the right next step.
Explore how Virima connects monitoring, asset intelligence, and service workflows into a unified governance framework. Schedule a demo today!
FAQs
What are the best tools for Active Directory monitoring?
The best tools depend on the environment size and integration needs. Platforms that integrate AD monitoring with broader IT management systems often provide stronger long-term value.
How can I set up effective Active Directory monitoring in my organization?
Start by enabling advanced auditing, centralizing logs, defining alert tiers, and integrating with ITSM or SIEM. Then document retention policies and automate privileged reviews.
Are there any software solutions that integrate Active Directory monitoring with other IT management tools?
Yes. Several platforms integrate AD monitoring with CMDB, ITSM, and SIEM systems. Integration improves prioritization and response.
What are the best tools for Active Directory monitoring?
People commonly evaluate tools such as Virima, ManageEngine ADAudit Plus, Netwrix Auditor, and SolarWinds Access Rights Manager. Selection should focus on hybrid support and integration capabilities.
How can I set up effective Active Directory monitoring in my organization?
Effective monitoring requires structured scope definition, alert configuration, integration with workflows, and continuous improvement.






